
A Windows security update released in January and now fully enforced this month is causing Windows users to experience 0x0000011b errors when printing to network printers.
In January 2021, Microsoft released a security update to fix a 'Windows Print Spooler Spoofing Vulnerability' tracked as CVE-2021-1678.
"A security bypass vulnerability exists in the way the Printer Remote Procedure Call (RPC) binding handles authentication for the remote Winspool interface," explains a support bulletin about the vulnerability.
When the security update was released, it did not automatically protect devices from the vulnerability. However, it did add a new Registry key that admins could use to increase the RPC authentication level used for network printing to mitigate the vulnerability.
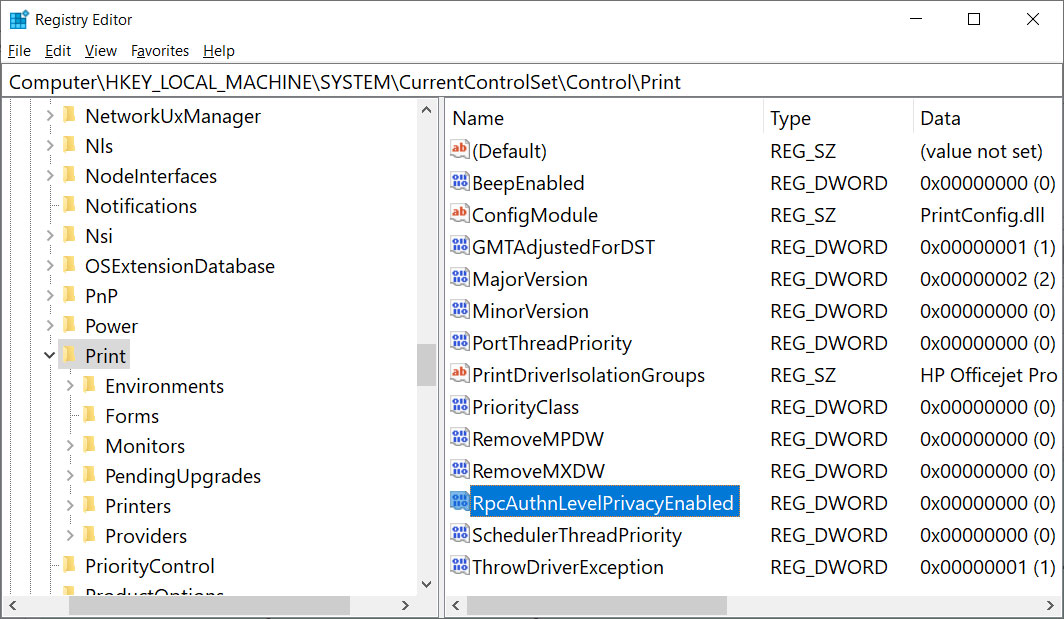
In other words, this security update did not fix any vulnerability unless a Windows administrator created the following Registry key:
[HKEY_LOCAL_MACHINE\System\CurrentControlSet\Control\Print]
"RpcAuthnLevelPrivacyEnabled"=dword:00000001
However, in this month's September 14th Patch Tuesday security updates, Microsoft automatically enabled this setting by default for every Windows device even if that Registry setting was not created.
Once this mitigation was enabled by default, Windows users began experiencing 0x0000011b errors when printing to network printers.
This printing error is mainly seen in small business and home networks that can't take advantage of a Kerberos setup on a Windows domain.
Uninstalling September's Windows security updates will fix the problem, but now the devices will be vulnerable to two vulnerabilities, PrintNightmare and MSHTML, actively exploited by threat actors.
A better method is to disable the mitigation for CVE-2021-1678 until Microsoft comes out with new guidance, as that vulnerability is not actively exploited.
How to fix the 0x0000011b printing errors
To fix the recent 0x0000011b printing errors without removing the current Windows Updates (KB5005565), you can instead disable the CVE-2021-1678 mitigation enabled by default this month.
To do that, open the Windows Registry Editor and navigate to the HKEY_LOCAL_MACHINE\System\CurrentControlSet\Control\Print key, create a new DWORD-32 bit value named RpcAuthnLevelPrivacyEnabled, and set it to 0, as shown in the Registry file below.
Windows Registry Editor Version 5.00
[HKEY_LOCAL_MACHINE\System\CurrentControlSet\Control\Print]
"RpcAuthnLevelPrivacyEnabled"=dword:00000000
To make it easier to add this change, you can use the fix-0x0000011b.reg Registry file to add it for you.
Download this file on both your print server and your Windows devices connecting to it, double-click on it, and allow the data to be merged.
Once you disable this mitigation, you will no longer be protected from the vulnerability, but it will hopefully allow you to print again.
If this does not solve your problem, use the enable-RpcAuthnLevel.reg to go back to the Windows defaults.


Comments
joshwenke - 2 years ago
I like the design of the registry key box. Nice!
forum11 - 2 years ago
So among other issues with the handling of this security fix, MS had *eight months* to catch the failure before throwing the switch and still didn't catch it. They clearly need to beef up their internal testing efforts and stop leaving so much to the general public.
Also, at this point with all the recent fumbling of printing related fixes, I imagine I'm watching MS perform in a circus act, chasing a printer around the ring while calliope music plays.
bond007x - 2 years ago
forum11 - I was thinking the same sentiments. It seems as if MS has conducted little/no QA and have let us end-users become the testers! Perhaps the QA lab has completely moved offsite distributed across employees' home systems due to C19? Not sure what's up ...I've been a beta tester for MS for years, but these serious problems keep creating more issues at a rate unlike any time before. Love MS, but they need to get it together!
zRISC - 2 years ago
Interesting.
in my case, since we use LPR and LPD windows services, we are stopping sharing printers via SMB and then adding the via LPR queue.
I_Rogue - 2 years ago
Thanks! I was just about to uninstall the misery that was the update. Micro$oft really needs to be better. #understatement
nyilasrobert - 2 years ago
Thanks for the info. That was good until I modified the registry key, an i got other error 0X00004005. I cannot connect to the printer. (HP 2015).
keezyman - 2 years ago
you don't have to edit any registry, just install https://download.bleepingcomputer.com/reg/fix-0x0000011b.reg and you are ready to go
keezyman - 2 years ago
it worked wonders for me, just had to install it on the systems that has the printer on it and boom ! they are printing.>!! thanks man
Zeone - 2 years ago
Thank you so much.
It worked. (should be applied
on host machine / server)
emusat - 2 years ago
Best way around it that I found is to install the printer manually using a local port. No registry changes needed, and doesn't bypass any security patches put in place by Microsoft. Created a video on it: https://youtu.be/QwnOh69dlM8
tw0ja5tara - 2 years ago
Praise the Lord, this is a good solution !!! and good tip "Zeone". (should be applied on host machine / server)
Byron_abc - 2 years ago
This issue had been driving me nuts for days. Lawrence Abrams thank you so much!
Byron_abc - 2 years ago
Just installed Windows Malicious Software Removal Tool x64 - v5.94 (KB890830) and it looks like I'm back to square one. Any ideas?
mohamadmaklad - 2 years ago
May God Reward You in Heaven
God Bless You Bro
Mudd47 - 2 years ago
Fantastic! I've read different "help-guides" from Microsoft and others for some days now, not on solution has solved the problem - but yours did!
I dit it this way: Change registry on server, change registry on client, remove printer, add printer.
My test shows that the first step, change registry on server, is th only one nessecary. Now this could be different for others, of course. I'm grateful for your tip, it stopped my hair from getting grayer :)
huckroy - 2 years ago
Fixed it for mw thanks
PeterM42 - 2 years ago
Still awaiting for a Microsoft fix, so THANK YOU for yours - much appreciated.
jk74b - 2 years ago
thnx for the posting of the fix! I did implement the fix on my W10 21h2 install and my WS22 but still I get the same error; any suggestions? thnx upfront!
Lconnie - 2 years ago
Thank you, thank you, thank you! It was driving me nuts and finding you had done the registry fix for me was icing on the cake. You just made this 80+ year old woman very happy.
manchox - 1 year ago
Hello, thank you, working for me...! fix-0x0000011b.reg
Thank you Totally