
Click Studios, the company behind the Passwordstate enterprise password manager, notified customers that attackers compromised the app's update mechanism to deliver malware in a supply-chain attack after breaching its networks.
Passwordstate is an on-premises password management solution used by over 370,000 security and IT professionals at 29,000 companies worldwide, as the company claims.
Its customer list includes companies (many of them in the Fortune 500 rankings) from a wide range of industry verticals, including government, defense, finance, aerospace, retail, automotive, healthcare, legal, and media.
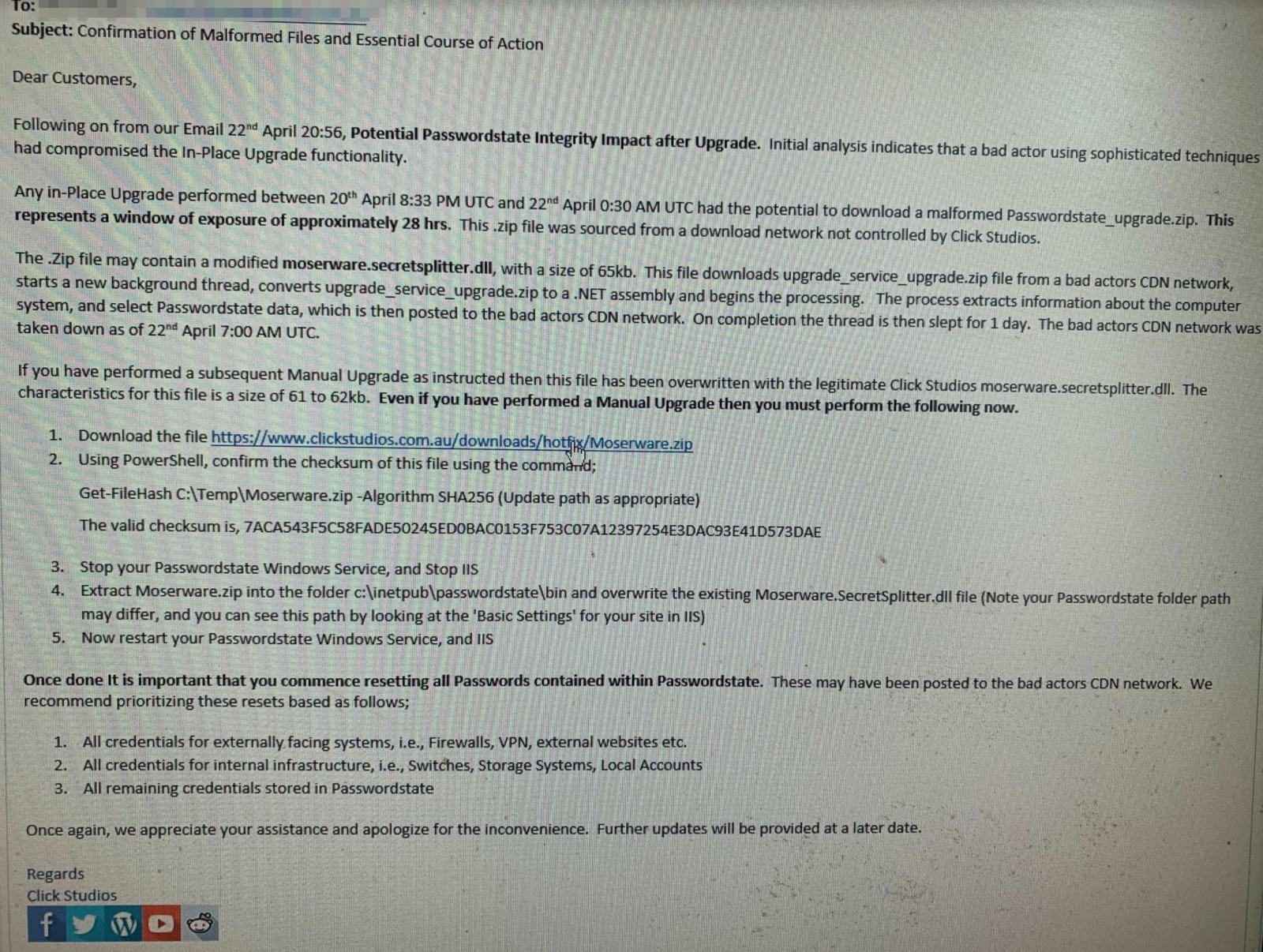
According to a notification email regarding the supply-chain attack sent to customers, malicious upgrades were potentially downloaded by customers between April 20 and April 22.
"Initial analysis indicates that bad actor using sophisticated techniques had compromised the In-Place Upgrade functionality," Click Studios told customers in an email with the "Confirmation of Malformed Files and Essential Course of Action" title.
"Any in-Place Upgrade performed between 20th April 8:33 PM UTC and 22nd April 0:30 AM UTC had the potential to download a malformed Passwordstate_upgrade.zip [..] sourced from a download network not controlled by Click Studios," the company added.
Malware harvested system info, Passworrdstate data
Once deployed, the malware (dubbed Moserpass) would collect system information and Passwordstate data, which later gets sent to attacker-controlled servers.
"The attackers crudely added a 'Loader' code section, just an extra 4KB from an older version" to Passwordstate's original code, said J. A. Guerrero-Saade, SentinelOne Principal Threat Researcher.
"At a glance, the Loader has functionality to pull a next stage payload from the C2 above. There's also code to parse the 'PasswordState' vault's global settings (Proxy UserName/Password, etc)."
"The process extracts information about the computer system, and selects Passwordstate data, which is then posted to the bad actors CDN network," Click Studios added in a security advisory published on Saturday.
After uploading the collected data, the malware will sleep for 1 day and restart the harvesting and uploading process.
Analysis of compromised data indicates the following information is posted back:
- Computer Name, User Name, Domain Name, Current Process Name, Current Process Id, All running Processes name and ID, All running services name, display name and status, Passwordstate instance’s Proxy Server Address, Username and Password
The following fields in Passwordstate instance’s password table is posted back:
- Title, UserName, Description, GenericField1, GenericField2, GenericField3, Notes, URL, Password
The Domain Name and Host name aren’t extracted as part of this. Although the encryption key and database connection string are used to process data via hooking into the Passwordstate Service process, there is no evidence of encryption keys or database connection strings being posted to the bad actor CDN network.
The CDN servers used in the attack are no longer reachable as they were taken down since starting with April 22nd 7:00 AM UTC.
Customers advised to reset all stored passwords
The company published a second advisory on Sunday, saying that "only customers that performed In-Place Upgrades between the times stated above are believed to be affected and may have had their Passwordstate password records harvested."
"To be clear, Click Studios CDN Network was not compromised. The initial compromise pointed the In-Place Upgrade functionality to a CDN network not controlled by Click Studios," the company added.
However, there's also good news for customers who had their password information encrypted since, in this case, Moserpass wouldn't collect and upload it to the threat actors' servers.
Click Studios advises customers who have upgraded their client during the breach to reset all passwords in their Passwordstate database.
It also recommends prioritizing the password reset as follows:
- all credentials for Internet-exposed systems (firewalls, VPN, external websites, etc.)
- all credentials for internal infrastructure
- all remaining credentials
The company also emailed a hotfix to potentially affected customers to help them remove the Moserpass malware.
Number of affected customers unknown
"The best information we have relating to the number of affected customers is based on the window of opportunity, approximately 28 hours, the nature of the initial compromise and subsequent exploit, and customers provision of requested information," Click Studios added.
"At this stage the number of affected customers appears to be very low. However, this may change as more customers supply the requested information."
Indicators of compromise (IOCs) including a hash of the malicious loader and one of the command-and-control server addresses were shared earlier by cybersecurity firm CSIS Security Group A/S after analyzing one of the rogue DLL deployed in this supply-chain attack.
Cybersecurity firm CrowdStrike also released analysis of the Moserpass malicious code delivered in the Passwordstate supply chain attack.
Update: Changed the malware's name to Moserpass.
Update: Added additional info from Click Studios' security advisories/updates.


Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now