Forrester: CISO Budgets Not Immune to Cuts
Security Boulevard
AUGUST 30, 2022
Still, a new report from Forrester Research warned that CISOs mustn’t. The post Forrester: CISO Budgets Not Immune to Cuts appeared first on Security Boulevard.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Security Boulevard
AUGUST 30, 2022
Still, a new report from Forrester Research warned that CISOs mustn’t. The post Forrester: CISO Budgets Not Immune to Cuts appeared first on Security Boulevard.

CSO Magazine
MARCH 28, 2023
As the role of the CISO continues to grow in importance and gain more responsibility, many cybersecurity practitioners may wonder if they have what it takes to be successful in the role. Technical expertise and experience are obviously huge assets. They know how to make quick decisions and drive change in the organization.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
NetSpi Executives
FEBRUARY 21, 2024
Like many technologies that came before it, AI is advancing faster than security standards can keep up with. For a comprehensive view of security in ML models, access our white paper, “ The CISO’s Guide to Securing AI/ML Models.” How transparent is the model architecture?

CyberSecurity Insiders
JUNE 11, 2023
Zero Trust is a cybersecurity framework that can greatly support Chief Information Security Officers (CISOs) and Chief Technology Officers (CTOs) in their roles of securing organizational systems and data. This approach significantly reduces the risk of lateral movement and unauthorized access within the network.

The Last Watchdog
OCTOBER 23, 2023
Splunk’s inability to migrate to a modern cloud-native architecture makes it difficult to take advantage of these cost-saving benefits or implement advanced data science use cases critical for threat detection. Influxes of data ingestion and the flat architecture of data lakes have led to difficulties in extracting value from repositories.

Jane Frankland
OCTOBER 31, 2023
However, new research from e2e-assure has revealed that few organisations are taking full advantage of security technologies available today. Having surveyed over 500 CISOs and ITDMs responsible for cybersecurity on the challenges faced with SOCs, their insights are not to be missed. Remember 2021?

SecureWorld News
OCTOBER 5, 2023
Having helped build out many SecureWorld conferences, I have come to realize—likely to no one's surprise—that the best cybersecurity leaders indeed have some technical prowess, but it is their soft skills that make them exceptional leaders. That's a soft skill that even the most adept CISOs are still trying to master.

The Last Watchdog
JANUARY 8, 2023
Business initiatives demand faster, more efficient outcomes and technology responds. When it comes down to it, C-level goals and CISO initiatives are not all that misaligned. About the essayist: Chris Reffkin is chief information security officer at cybersecurity software and services provider Fortra.

SC Magazine
APRIL 30, 2021
Touhill brings a rich and diverse background to the role, having spent years protecting military computer networks as an Air Force brigadier general and later serving as director of the National Cybersecurity and Communications Integrations Center at the Department of Homeland Security. I lived it. I’m absolutely thrilled.
Notice Bored
AUGUST 5, 2022
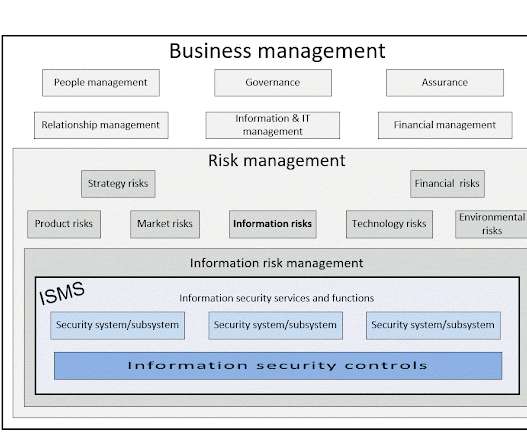
Other slides in the deck appear to equate ' security posture ' to vulnerability management and software/systems patching - a rather narrow/specific technical concern for metrics suggested to senior management, although arguably it is a major factor in cybersecurity - or to security strategy.

CyberSecurity Insiders
NOVEMBER 16, 2021
In 2020, we saw cybersecurity move from a technical problem to become a business enabler. In 2022, we will see 5G go from new technology to a business enabler bringing previously unimaginable use cases because of its high bandwidth and lower latency. 5G began its disruptive charge in 2021, and this will continue to accelerate in 2022.

McAfee
NOVEMBER 3, 2020
There are new and expanding opportunities for women’s participation in cybersecurity globally as women are present in greater numbers in leadership. Forrester also predicts that the number of women CISOs at Fortune 500 companies will rise to 20 percent in 2019 , compared with 13 percent in 2017. government clients.

Security Boulevard
SEPTEMBER 19, 2022
Sunsetting legacy Cybersecurity Process for Better Optimization and Security Modernization. The idea of “if it isn’t broken, don’t fix it” should not apply to cybersecurity. The cost of sunsetting security products, legacy applications, and legacy technology imposes a financial strain on every organization.

CyberSecurity Insiders
NOVEMBER 8, 2021
As the AT&T Cybersecurity team endeavors to help organizations transition to SASE frameworks, it’s picking up accolades not only from valued AT&T customers but also the broader cybersecurity community. SASE helps future-proof cybersecurity architecture by decoupling security control from the data center.

CyberSecurity Insiders
FEBRUARY 28, 2023
John Masserini, of Tag Cyber, will explore practical approaches to advancing zero trust along with his fellow panelists: Kevin Dana, VP of Information Technology for World Wide Technology; Marcos Christodonte II, Global CISO for CDW; and Allen Jeter, Director of IT for Chainalysis. You can view the full agenda here.

SecureWorld News
OCTOBER 19, 2023
Global inflation can have, and is having, a significant impact on cybersecurity. As prices rise, organizations may be tempted to cut back on cybersecurity spending, making them more vulnerable to cyberattacks. Additionally, inflation can make it more difficult for organizations to keep up with the latest cybersecurity threats.
Security Boulevard
JANUARY 9, 2024
Many next-generation technologies became deployed parallel to existing solutions, including zero-trust architecture ( ZTNA ), extended detection and response ( XDR ), and cloud-based multi-factor authentication. Assessing Duplication of Security Controls. Importance of Assessing Duplication of Security Controls.

IT Security Guru
SEPTEMBER 25, 2023
The IT Security Guru caught up with Tarnveer Singh a CISO and finalist in the Security Serious Unsung Heroes Awards 2023 for his thoughts on how to get more professionals involved in the cybersecurity industry: There are many ways we can inspire new cybersecurity professionals to join our industry.

CyberSecurity Insiders
OCTOBER 7, 2021
. & HYDERABAD, India–( BUSINESS WIRE )–Analytics Insight has named ‘ The 10 Most Influential CISOs to Watch in 2021 ’ in its October magazine issue. The magazine issue recognizes ten futuristic CISOs who are reimagining the business world and adopting new ways of working. He holds a Ph.D

Cisco Security
OCTOBER 18, 2021
About 15 years ago, the idiom began to be applied to cybersecurity, where the risk management continuum values the investment in protection to mitigate the negative consequences of a cyber incident. Achieving “Left of Boom” cybersecurity is a journey on which every CISO should be embarked. Some “Left of Boom” Processes.

SecureWorld News
JUNE 2, 2022
In Q&A format, they share about their professional journeys, unique experiences, and hopes for the future of cybersecurity—along with some personal anecdotes. He is active in CIO Roundtables, CISO Chicago, the Chicago Life Sciences Consortium, and the Technology Leaders' Association. Get to know Glenn Kapetansky.

Security Boulevard
JANUARY 24, 2023
Why Will CyberSecurity Become the Least of your Concern? Cybersecurity attacks, including phishing, vishing, smishing, and everything else “ishing,” continues to rise and become even more of a problem for organizations and individuals. BTW: — Cybersecurity breaches also make headlines, too.

SC Magazine
MAY 18, 2021
A visitor photographs a symbol of a cloud at the Deutsche Telekom stand the day before the CeBIT technology trade fair. It’s about how you can do your business mission” in a different environment, with its own requirements for protecting data, Vickers said during his talk at the RSA Show’s Cloud Security Alliance CISO Summit.

SecureWorld News
MAY 16, 2023
Seven small coastal towns in Massachusetts have formed a partnership to better tackle their IT and cybersecurity needs in the region. The city has a more established IT setup, including a full-time IT director, which many of the smaller towns lack, according to this Government Technology article. This is a great approach.
Cisco Security
JANUARY 12, 2022
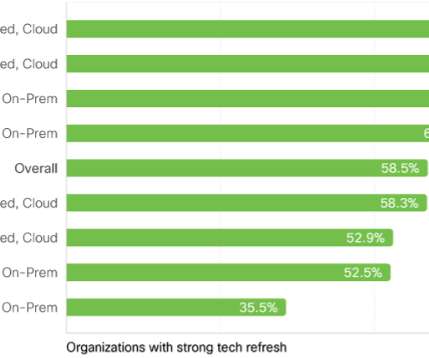
One of the five main findings in our newly published Security Outcomes Study, Volume 2 , was the clear benefit in having a proactive strategy of refreshing business-critical technologies. How often should a technology refresh take place? As you could guess, this level of technology debt is a drag on security teams.

Cisco Security
JULY 21, 2021
Today, the Cisco Investments team released their 2021 CISO Survival Guide to Emerging Trends in the Startup Ecosystem. There is a wealth of insightful information for CISOs in this report. Because Zero Trust and XDR are integrated architectural outcomes, the majority of CISOs are anchoring their SASE strategies here.

SecureWorld News
SEPTEMBER 7, 2023
Quantum computing poses a potential threat to current cybersecurity practices, which are based on encryption algorithms that can be broken by quantum computers. As for the panel presentation at SecureWorld Denver , it features Edgar Acosta, Experienced Cybersecurity Professional (former CISO at DCP Midstream ); Craig Hurter, Sr.

SC Magazine
FEBRUARY 8, 2021
Now, those insurers are poised to drive cybersecurity investment by insisting that organizations meet certain criteria to qualify for coverage. Still unclear is whether this will serve the cybersecurity community well, or distort strategies to protect data and networks. A maturing model. billion in premium.

NopSec
SEPTEMBER 23, 2022
Lisa has a passion for connecting business with technology and thrives in transforming disruptive technology into leading solutions. In this episode, Lisa talks with Tim Brown, the CISO at SolarWinds. Tim has held many roles in the cybersecurity space, including Fellow, Chief Architect, Distinguished Engineer and Board Advisor.

SecureWorld News
APRIL 8, 2021
Before you do either of those things—again—consider this: a new computer chip remains unhacked after DARPA and more than 500 cybersecurity researchers tried to break through its security. Undefined semantics are nooks and crannies of the computing architecture—for example the location, format, and content of program code.

Security Boulevard
SEPTEMBER 9, 2022
Grim statistics illustrate the urgent need for strong and strategic cybersecurity efforts under the guidance of a seasoned leader. But hiring a full-time chief information security officer (CISO) is not always possible for organizations – nor is it always needed.

CyberSecurity Insiders
JANUARY 17, 2022
By Tyler Farrar, CISO, Exabeam. In almost every case, technology has played a vital role in facilitating and supporting these changes. It makes sense that security budgets should follow to help protect these increasingly diverse and flexible architectures. appeared first on Cybersecurity Insiders. Leaving The Legacy.

McAfee
AUGUST 23, 2021
Now that we’ve officially kicked off our journey as McAfee Enterprise , a pure-play enterprise cybersecurity company under the new ownership of Symphony Technology Group (STG), we’re celebrating a lot of new firsts and changes. After being in the CISO role for over 12 years, I understand how difficult the role can be.

CyberSecurity Insiders
SEPTEMBER 27, 2021
And it’s jam-packed with cybersecurity talks! Given how critical security is to digital transformation and our ability to innovate, we’ve got a robust line-up of cybersecurity topics – from SASE to zero trust and the technologies you need to help protect your business. Event is FREE! Speaker: Rupesh Chokshi.

McAfee
JULY 1, 2020
Hybrid and multi-cloud architectures can offer government agencies the flexibility, enhanced security and capacity needed to achieve what they need for modernizing now and into the future. Yet many questions remain surrounding the implementation of multi- and hybrid-cloud architectures.

CyberSecurity Insiders
JANUARY 5, 2022
SAN FRANCISCO–( BUSINESS WIRE )–Tetrate, the leading company providing a zero-trust application connectivity platform, announced their third annual conference on Zero Trust Architecture (ZTA) and DevSecOps for Cloud Native Applications in partnership with the U.S. security standards for a distributed architecture: About Tetrate.

CyberSecurity Insiders
NOVEMBER 7, 2022
Over the last 20+ years, the SIEM market has procured substantial growth within the technology industry. billion of total cybersecurity spending and is expected to increase to $6.4 According to Ponemon Institute, the average number of cybersecurity products a company uses is 45. Today, SIEM accounts for approximately $4.4

SecureWorld News
MAY 19, 2020
When David Sherry became Chief Information Security Officer at Princeton University, he says cybersecurity was done well. "I Sherry brought to Princeton his 25 years of technology experience, 12 of which was in higher education as the former CISO at Brown University. How do you assess your current cybersecurity culture?
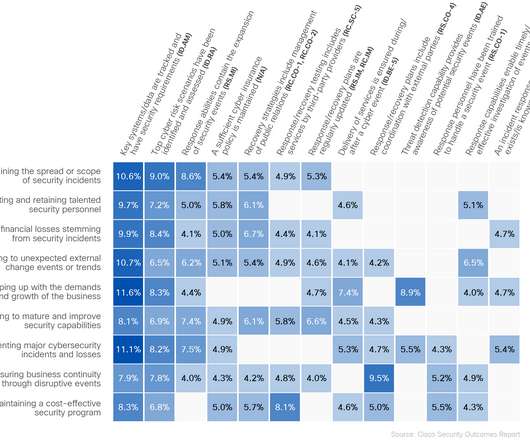
Cisco Security
DECEMBER 6, 2022
Two years ago, we asked the question: What actually works in cybersecurity? Not what everyone’s doing—because there are plenty of cybersecurity reports out there that answer that question—but which data-backed practices lead to the outcomes we want to implement in cybersecurity strategies?

Security Boulevard
AUGUST 29, 2022
Organizations developing a Security operations center(SOC) should consider which strategy they should adopt based on available cybersecurity professional resources: offensive or defensive? Are they experienced cyber warriors or recent additions to the cybersecurity field or resources moving over from traditional IT roles?

eSecurity Planet
DECEMBER 19, 2023
As 2023 draws to an end and cybersecurity budgeting is nearly complete, it helps to consider the year’s events and try to predict next year’s trends. After receiving input from industry experts and doing my own analysis of the year’s driving forces, I identified five major cybersecurity trends. Bottom line: Prepare now based on risk.

SC Magazine
MAY 1, 2021
Each year, a select pool of experts from the cybersecurity community sets hours aside to review hundreds of entries received for the SC Trust and Excellence Awards. Dan Basile is the chief information security officer for the RELLIS campus at the Texas A&M University System and director of Statewide Cybersecurity Services.

Spinone
OCTOBER 19, 2018
Cybersecurity professionals encompass a wide range of job roles including security engineer, cryptographer, ethical hacker, security analyst, vulnerability tester, security consultant, and more. Broadly speaking, cybersecurity professionals are individuals who have been trained to protect data via various different methods.

The Last Watchdog
JULY 30, 2018
Understanding today’s cybersecurity landscape is complex. The painful impact of cyber attacks on businesses is worsening despite advances in technology aimed at protecting enterprises from malicious network traffic, insider threats, malware, denial of service attacks and phishing campaigns. It requires a massive architecture overhaul.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content