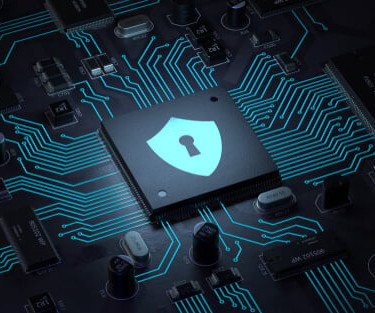
Zenbleed: New Flaw in AMD Zen 2 Processors Puts Encryption Keys and Passwords at Risk
The Hacker News
JULY 25, 2023
A new security vulnerability has been discovered in AMD's Zen 2 architecture-based processors that could be exploited to extract sensitive data such as encryption keys and passwords.








































Let's personalize your content