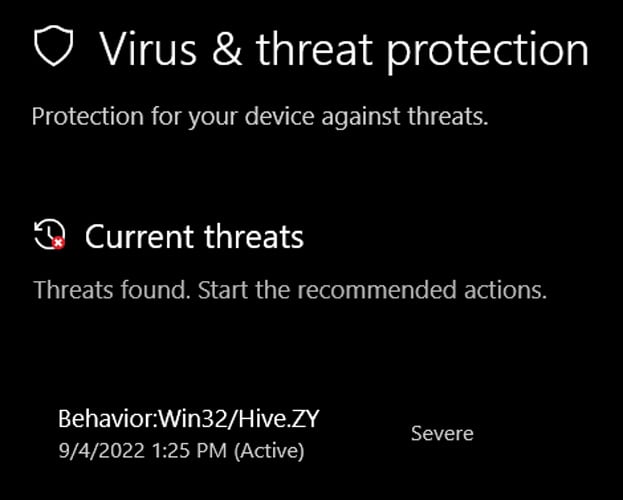
Additional updates to the story are below, including the version of security intelligence updates required to fix Win32/Hive.ZY false positive.
A bad Microsoft Defender signature update mistakenly detects Google Chrome, Microsoft Edge, Discord, and other Electron apps as 'Win32/Hive.ZY' each time the apps are opened in Windows.
The issue started Sunday morning when Microsoft pushed out Defender signature update 1.373.1508.0 to include two new threat detections, including Behavior:Win32/Hive.ZY.
"This generic detection for suspicious behaviors is designed to catch potentially malicious files. If you downloaded a file or received it through email, ensure that it is from a reliable source before opening it," reads the Microsoft detection page for Win32/Hive.ZY.
According to BornCity, the false positive is widespread, with users reporting on BleepingComputer, Twitter, and Reddit that the detections appear each time they open their browser or an Electron app.
Source: Twitter
Even though Microsoft Defender will continuously display these detections when apps are opened, it is important to note that this is a false positive, and your device is mistakenly being detected as infected.
Microsoft has since released two new Microsoft Defender security intelligence updates, the latest being 1.373.1518.0.
While this signature update does not display Win32/Hive.ZY detections in BleepingComputer's tests, other users report that they continue to receive false positives.
To check for new security intelligence updates, Windows users can search for and open Windows Security from the Start Menu, click Virus & threat protection, and then click on Check for updates under Virus & threat protection updates.
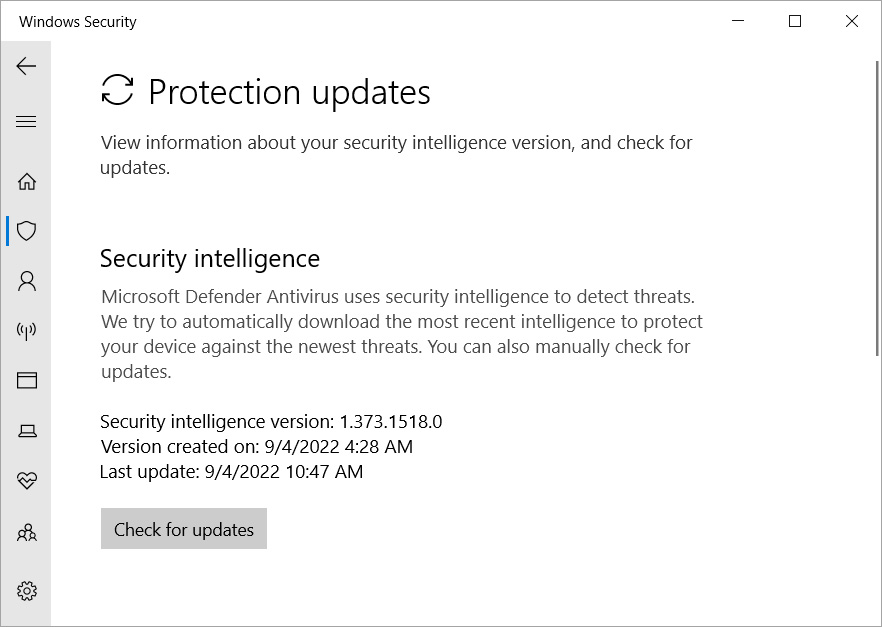
Source: BleepingComputer
While it is usually not required, in this case, it may be helpful to reboot Windows after installing the new security intelligence update to see if it resolves the false positive.
As this issue is widespread and causing panic among Windows users worldwide, we will likely see a new update fixing the problem within a few hours, if not sooner.
At this time, there has been no formal confirmation of the issue from Microsoft.
Update 6:47 PM EST:
Microsoft has released Microsoft Defender security intelligence update version 1.373.1537.0, which from reports, appears to resolve the Win32/Hive.ZY false positive experienced by Windows users today.
You can follow the instructions at the end of this article to update to this version.
Update 9:25 PM EST:
Microsoft shared the following statement with BleepingComputer:
"We have released an update to address this issue and customers using automatic updates for Microsoft Defender do not need to take additional action." - a Microsoft spokesperson.
In addition Microsoft shared that enterprise customers managing their updates should ensure they are using detection build 1.373.1537.0 or newer.


Comments
Winston2021 - 1 year ago
What ACTUALLY went on here?
On the morning of 4 Sep, my PC was powered up and the latest Defender intelligence update was loaded.
I started the Chrome browser and got the Win32/Hive.ZY "false" alarm. Defender indicated that it had been "blocked" and "deleted." However, I closed Chrome, opened it, and every time I did so, the "deleted" extreme threat warning popped up again.
I used Firefox to investigate and found out, ONLY from Microsoft since I could find nothing about this variant from any other source, that the Win32/Hive.ZY alarm was triggered by generic RAT behavior.
I read elsewhere that Chrome based Edge also had the problem, so I started it up for the first time in many months. It presented a screen you'd see on a first install, so I checked and I had the very latest update discussed below. No "false" alarm appeared.
I then read that Chrome Edge version 105.0.1343.27 was released on 3 Sep 2022 and Chrome version 105.0.5195.102 was also released on 3 Sep 2022.
Those updates included ONE fix for this serious security vulnerability:
[$TBD][1358134] High CVE-2022-3075: Insufficient data validation in Mojo. As reported by Anonymous on 2022-08-30
Reported by "Anonymous," huh?
I went back to Chrome and there was no alarm. I checked and I now had the latest Chrome version which I probably didn't have early in the AM when these "false" alarms began. I also checked and there had been no Defender intelligence update.
SO, the "false" alarms on MANY PCs blamed on a flawed Defender update was NOT fixed by a Defender update, but by Chrome and Chrome Edge emergency updates the day before the "false" alarms caused this issue.
Could it be that there was a very widespread active exploit talking place on a large number of PCs due to that Chrome flaw which was defeated by that emergency Chrome update and the Defender warning WASN'T a false alarm? And if that was the case, WHO was exploiting it?
EndangeredPootisBird - 1 year ago
I have so far only seen Defender being triggered by launching applications based on Electron, an actual exploit also wouldnt be executed like this, instead an victim have to navigate to an attacker-controlled website which would then launch the actual exploit in the browser.
Also, FYI, Hive is ransomware.
Winston2021 - 1 year ago
"I have so far only seen Defender being triggered by launching applications based on Electron, an actual exploit also wouldnt be executed like this, instead an victim have to navigate to an attacker-controlled website which would then launch the actual exploit in the browser.
Also, FYI, Hive is ransomware."
1. If the actual exploit was already present, was Chrome exploit dependent, and didn't want to remain active when Chrome wasn't being used, it would behave exactly as it did.
2. Cross pollination of malware code is not uncommon at all. If an exploit is useful (successful) for ransomware, it would also be useful for a RAT and would be heuristically detected as behaving like ransomware.
Because of the fact that the issue was fixed not by a Defender intelligence update, but by a Chrome emergency update before the "false" alarm issue ever occurred when that update finally loaded on my AM-booted system, an update issued the day before due to a serious flaw reported by "anonymous," I'd say the alarm wasn't false. If not, someone needs to explain exactly what happened.
MolassesMan - 1 year ago
If it wasn't fixed by a Defender update, then MS wouldn't have taken responsibility as causing a false positive. The details of the threat detected would have been submitted to MS in mass due to sample submission, which is presumably why they were able to identify it as not actually Hive so quickly. Moreover, this was widely seen in many electron based apps, which haven't all be updated, nor did they have the same issues as in chrome, yet after the definitions update, the false positive report still stopped.
Moreover, that chrome update is only being pushed out over the next few weeks. If there was such a widescale exploit, they would presumably make the fix more urgent.
Winston2021 - 1 year ago
"If it wasn't fixed by a Defender update, then MS wouldn't have taken responsibility as causing a false positive."
They weren't sure. In their forum they told people to NOT just "allow" the behavior to get rid of the alarm. And in my case, it WASN'T fixed by a Defender intelligence update. It was fixed by an update in both Chrome and Edge. Firefox didn't have the problem.
And, BTW, if it had been a "false" alarm, why would Defender be heuristically detecting generic RAT behavior in Chrome code?
"Moreover, that chrome update is only being pushed out over the next few weeks. If there was such a widescale exploit, they would presumably make the fix more urgent."
HOW does one know how widespread an exploit is until something can detect it?
MolassesMan - 1 year ago
"They weren't sure. In their forum they told people to NOT just "allow" the behavior to get rid of the alarm. And in my case, it WASN'T fixed by a Defender intelligence update. It was fixed by an update in both Chrome and Edge. Firefox didn't have the problem."
You said "I checked and I now had the latest Chrome version which I probably didn't have early in the AM when these "false" alarms began." So you don't really know if your chrome update fixed the problem, do you? Also Firefox isn't based on electron, which is what all the applicaitons being false flagged, like Discord, are, so that makes perfect sense.
"And, BTW, if it had been a "false" alarm, why would Defender be heuristically detecting generic RAT behavior in Chrome code?"
First of, it didn't detect RAT behaviour. Hive is ransomware. Second, that is what a false positive is. It gave incorrect information.......
Winston2021 - 1 year ago
MolassesMan
I answered all of your questions above before you posted. Please learn to read before responding.
Winston2021 - 1 year ago
"Moreover, that chrome update is only being pushed out over the next few weeks. If there was such a widescale exploit, they would presumably make the fix more urgent."
WRONG.
CVE-2022-3075: 0-day Google Chrome Vulnerability
BY DO SON · PUBLISHED SEPTEMBER 2, 2022
https://securityonline.info/cve-2022-3075-0-day-google-chrome-vulnerability/
"Google has released an emergency security update to fix this vulnerability, the corresponding version number is Google Chrome 105.0.5195.102."
EndangeredPootisBird - 1 year ago
Theres no other AV thats detecting this supposed "exploit", which is an instant indicator this (was) an false positive.
Lawrence Abrams - 1 year ago
This is a false positive. Why would Microsoft "fix it" if it was correctly detecting an exploit?
cafejose - 1 year ago
How to manually ask for the update does not give the option described in this article. The expected choice at , "click on Check for updates under Virus & threat protection updates" is not present.