New Loader Delivering Spyware via Image Steals Cryptocurrency Info
Dark Reading
JUNE 12, 2023
Sophisticated attackers are lacing malware into PNG image files in order to steal cryptocurrency and business information.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Dark Reading
JUNE 12, 2023
Sophisticated attackers are lacing malware into PNG image files in order to steal cryptocurrency and business information.
Security Affairs
JUNE 27, 2023
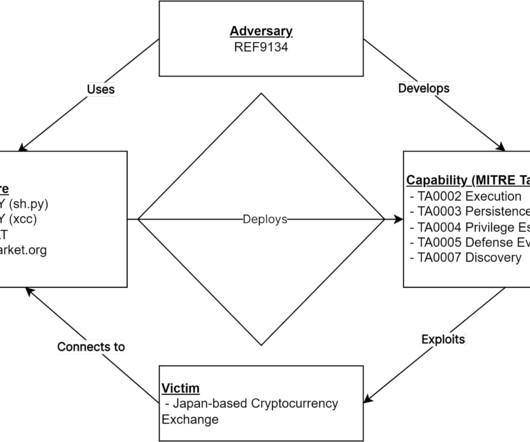
An unnamed Japanese cryptocurrency exchange was the victim of a cyber attack aimed at deploying an Apple macOS backdoor named JokerSpy. Elastic Security Labs researchers provided details about a recently discovered intrusion at an unnamed cryptocurrency exchange, aimed at deploying an Apple macOS backdoor named JokerSpy.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Security Affairs
FEBRUARY 10, 2022
I transcribed a recent interview, here some questions and answers about nation-state hacking, spyware, and cyber warfare. Enjoy” How has spyware changed the rules of cyber security in recent years? Spyware are powerful weapons in the arsenal of governments and cybercrime gangs. Is the Pegasus spyware as a game-changer?
Security Affairs
SEPTEMBER 9, 2022
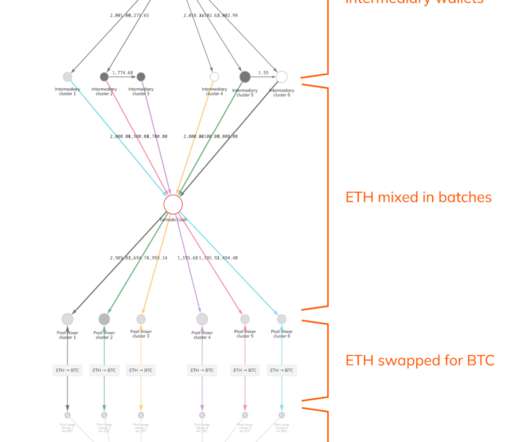
US authorities recovered more than $30 million worth of cryptocurrency stolen by the North Korea-linked Lazarus APT from Axie Infinity. A PDF containing the offer was sent to the employee, once opened the file spyware compromised his system and infiltrate Ronin’s network. ” continues the report. Pierluigi Paganini.

Tech Republic Security
DECEMBER 22, 2023
ESET's latest report highlights the abuse of the ChatGPT name, the rise of the Lumma Stealer malware and the Android SpinOk SDK spyware.

Security Affairs
AUGUST 15, 2020
This behavior allows the malicious code to replace cryptocurrency addresses, and steal credentials for online services (amoCRM, Apple ID, Google, Paypal, SIPMarket, and Yandex) and payment card information from the Apple Store. The post XCSSET Mac spyware spreads via Xcode Projects appeared first on Security Affairs.

Security Affairs
FEBRUARY 6, 2024
A Belarusian and Cypriot national linked with the cryptocurrency exchange BTC-e is facing charges that can lead maximum penalty of 25 years in prison. In 2017, Greek Police arrested the Russian national Alexander Vinnik and they accused the man of running the BTC-e Bitcoin exchange to launder more than US$4bn worth of the cryptocurrency.

Security Affairs
SEPTEMBER 8, 2019
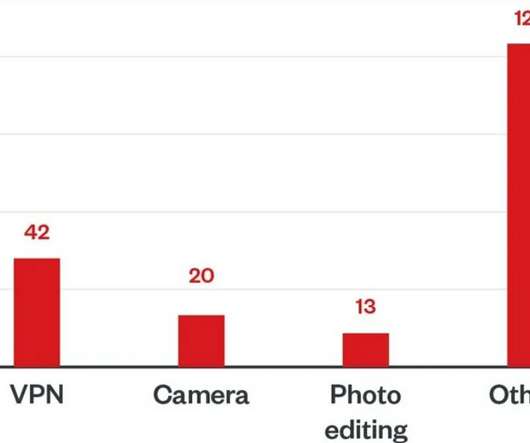
Security experts at Google have removed from Google Play 24 apps because they were infected with a new spyware tracked as “the Joker.” ” Google has removed from Google Play 24 apps because they were infected with a new spyware tracked as “the Joker.” The C&C URL 6.

Schneier on Security
JULY 6, 2020
But it's nasty: In addition to ransomware, ThiefQuest has a whole other set of spyware capabilities that allow it to exfiltrate files from an infected computer, search the system for passwords and cryptocurrency wallet data, and run a robust keylogger to grab passwords, credit card numbers, or other financial information as a user types it in.
Security Affairs
MAY 17, 2022
Experts spotted over 200 Android apps on the Play Store distributing spyware called Facestealer used to steal sensitive data. Trend Micro researchers spotted over 200 Android apps on the Play Store distributing spyware called Facestealer used to steal sensitive data from infected devices.

Graham Cluley
SEPTEMBER 15, 2021
A Walmart press release says it's jumping aboard the cryptocurrency bus - but is it true? Theranos's Elizabeth Holmes goes on trial, and have you updated your Apple gadgets to protect against the latest NSO Group spyware attack?

Security Affairs
NOVEMBER 20, 2018
Security researchers at F-Secure have recently uncovered a small spam campaign aimed at delivering spyware to Mac users that use Exodus wallet. Security experts at F-Secure have recently spotted a small spam campaign aimed at Mac users that use Exodus cryptocurrency wallet. update.zip.” . Pierluigi Paganini.

SecureList
SEPTEMBER 8, 2022
Spyware was blocked on 6% of ICS computers. Percentage of ICS computers on which spyware was blocked. Building Automation leads the ranking of industries based on the percentage of ICS computers on which spyware was blocked (12.9%). Percentage of ICS computers on which spyware was blocked, in selected industries.

Threatpost
SEPTEMBER 27, 2019
The malware harvests data, steals cryptocurrency and drops additional malware, while masquerading as a Fortnite aimbot and more.

Security Affairs
JULY 30, 2018
A new sophisticated version of the AZORult Spyware was spotted in the wild, it was involved in a large email campaign on July 18. Malware researchers at Proofpoint spotted a new version of the AZORult Spyware in the wild, it was involved in a large email campaign on July 18, just 24 hours it appeared in cybercrime forums on the Dark Web.

Security Affairs
JUNE 4, 2023
Xplain hack impacted the Swiss cantonal police and Fedpol Zyxel published guidance for protecting devices from ongoing attacks Kimsuky APT poses as journalists and broadcast writers in its attacks New Linux Ransomware BlackSuit is similar to Royal ransomware CISA adds Progress MOVEit Transfer zero-day to its Known Exploited Vulnerabilities catalog (..)
Security Affairs
FEBRUARY 25, 2024
Iran Crisis Russia-Aligned TAG-70 Targets European Government and Military Mail Servers in New Espionage Campaign U.S.

Security Affairs
JULY 24, 2022
released in Dark Web – malicious shortcut-based attacks are on the rise Tor Browser 11.5 is optimized to automatically bypass censorship A massive cyberattack hit Albania Watch out for the CVE-2022-30136 Windows NFS Remote Code Execution flaw Graff paid a $7.5M released in Dark Web – malicious shortcut-based attacks are on the rise Tor Browser 11.5

SecureWorld News
JULY 11, 2022
Axie Infinity, a video game that utilizes NFTs and Ethereum-based cryptocurrencies, lost $540 million in March of this year after a senior engineer was tricked into opening a PDF of a fake job application, according to a story from The Block. So, what exactly happened with Axie Infinity?

The Last Watchdog
MAY 8, 2019
And earlier this year, three popular “ selfie beauty apps ”– Pro Selfie Beauty Camera, Selfie Beauty Camera Pro and Pretty Beauty Camera 2019 – accessible in Google Play Store were revealed to actually be tools to spread adware and spyware. Adware are unwanted ads that redirect you to sketchy webpages, and spyware collects your data.
Security Affairs
JUNE 11, 2023
Gox exchange and operating BTC-e Japanese Pharmaceutical giant Eisai hit by a ransomware attack Clop ransomware gang was testing MOVEit Transfer bug since 2021 Stealth Soldier backdoor used is targeted espionage attacks in Libya Researchers published PoC exploit code for actively exploited Windows elevation of privilege issue Experts detail a new Kimsuky (..)
Security Affairs
MARCH 4, 2023
stolen credit/debit cards Pegasus spyware used to spy on a Polish mayor Hundreds of thousands of websites hacked as part of redirection campaign MQsTTang, a new backdoor used by Mustang Panda APT against European entities Trusted Platform Module (TPM) 2.0 FiXS, a new ATM malware that is targeting Mexican banks BidenCash leaks 2.1M
Security Affairs
DECEMBER 2, 2023
Researchers devised an attack technique to extract ChatGPT training data Fortune-telling website WeMystic exposes 13M+ user records Expert warns of Turtle macOS ransomware US govt sanctioned North Korea-linked APT Kimsuky Black Basta Ransomware gang accumulated at least $107 million in Bitcoin ransom payments since early 2022 Apple addressed 2 new (..)

SecureList
MARCH 3, 2022
Since H1 2020, we have seen increases in the percentages of ICS computers on which the following types of objects were blocked: Spyware – by a factor of 1.4 — from 5.6% Percentage of ICS computers on which spyware was blocked ( download ). Cryptocurrency miners (Windows executable files) – more than doubled – from 0.9%

SecureList
NOVEMBER 22, 2022
Cryptocurrency targeted attacks. The cryptocurrency business continues to grow, and people continue to invest their money in this market because it’s a digital asset and all transactions occur online. More cryptocurrency-related threats: fake hardware wallets, smart contract attacks, DeFi hacks, and more.

Malwarebytes
MAY 16, 2022
Cryptocurrency values soared in 2021 and, to nobody’s surprise, detections of malware that mines cryptocurrencies increased more than 300 precent. Adware, spyware, and worms all displayed an enormous bounce back in 2021, climbing 200%, and detections of email threats showed a considerable “Covid bounce” too.

Security Affairs
NOVEMBER 14, 2021
Hundreds of thousands of fake warnings of cyberattacks sent from a hacked FBI email server GravityRAT returns disguised as an end-to-end encrypted chat app Intel and AMD address high severity vulnerabilities in products and drivers New evolving Abcbot DDoS botnet targets Linux systems Retail giant Costco discloses data breach, payment card data exposed (..)

Security Affairs
FEBRUARY 13, 2022
US seizes $3.6 to replace Chinese equipment Hackers breached a server of National Games of China days before the event Russian Gamaredon APT is targeting Ukraine since October Israeli surveillance firm QuaDream emerges from the dark Argo CD flaw could allow stealing sensitive data from Kubernetes Apps.

Security Affairs
JANUARY 23, 2022
Pay attention to Log4j attacks, Dutch National Cybersecurity Centre (NCSC) warns Vulnerabilities in Control Web Panel potentially expose Linux Servers to hack US Treasury Department sanctions 4 Ukrainian officials for working with Russian intelligence A bug in McAfee Agent allows running code with Windows SYSTEM privileges Experts warn of anomalous (..)

Security Affairs
MARCH 11, 2019
Experts observed the STOP ransomware installing the Azorult password-stealing Trojan to steal account credentials, cryptocurrency wallets, and more. Experts observed the ransomware also installing the dreaded Azorult password-stealing Trojan on victim’s machine to steal account credentials, cryptocurrency wallets, documents and more.

Security Affairs
JUNE 28, 2020
Every week the best security articles from Security Affairs free for you in your email box. Copyright (C) 2014-2015 Media.net Advertising FZ-LLC All Rights Reserved -->. Copyright (C) 2014 Media.net Advertising FZ-LLC All Rights Reserved -->. Every week the best security articles from Security Affairs free for you in your email box.

Security Affairs
OCTOBER 23, 2018
A new version of the Azorult info-stealer appeared in the wild, it is able to steal more data, including other types of cryptocurrencies. A new version of the Azorult info-stealer appeared in the wild, it is able to steal more data, including other types of cryptocurrencies, and implements new features.

Identity IQ
APRIL 29, 2021
Infecting systems and using them to mine cryptocurrencies like bitcoin. Hackers demand cryptocurrency in exchange for the decryption key that allows you to access your data again. Spyware is software designed to capture your activity and sensitive information without your knowledge or consent. How Does Malware Spread?
Security Affairs
MAY 6, 2023
Twitter confirmed that a security incident publicly exposed Circle tweets FBI seized other domains used by the shadow eBook library Z-Library WordPress Advanced Custom Fields plugin XSS exposes +2M sites to attacks Fortinet fixed two severe issues in FortiADC and FortiOS Pro-Russia group NoName took down multiple France sites, including the French (..)

Webroot
MAY 12, 2021
Since cryptocurrencies were, are and will continue to be impactful technologies, surely NFTs are a topic worth exploring. NFTs use the same blockchain ledger technology to verify uniqueness that cryptocurrencies rely on to prove ownership. “What Bitcoin was to 2011, NFTs are to 2021.”. Perhaps NFTs are a bubble positioned to pop.

Security Affairs
OCTOBER 31, 2021
Hacker accessed medical info at UMass Memorial Health Reading INTERPOL the African Cyberthreat Assessment Report 2021 MITRE and CISA publish the 2021 list of most common hardware weaknesses TrickBot member extradited to US faces up to 60 years in prison ESET found a variant of the Hive ransomware that encrypts Linux and FreeBSD Papua New Guinea ‘s (..)

eSecurity Planet
JUNE 16, 2022
Restoration is offered in exchange for a ransom, usually in cryptocurrencies. Crimeware and spyware. On the other hand, spyware malware can breach a device and access specific functions like webcams, website history, cookies, or even record conversations on a phone. See the Top Rootkit Scanners. Other methods.

SecureWorld News
AUGUST 8, 2022
Cybercriminals often use malware to gain access to a computer or mobile device to deploy viruses, worms, Trojans, ransomware, spyware, and rootkits. It has been sold on underground hacker forums for stealing browser data, user credentials, and cryptocurrency information. AZORult's developers are constantly updating its capabilities.

Security Affairs
APRIL 26, 2020
Copyright (C) 2014-2015 Media.net Advertising FZ-LLC All Rights Reserved -->. Copyright (C) 2014 Media.net Advertising FZ-LLC All Rights Reserved -->. Copyright (C) 2014-2015 Media.net Advertising FZ-LLC All Rights Reserved -->. Copyright (C) 2014 Media.net Advertising FZ-LLC All Rights Reserved -->.

Security Affairs
SEPTEMBER 23, 2018
New XBash malware combines features from ransomware, cryptocurrency miners, botnets, and worms. NSO mobile Pegasus Spyware used in operations in 45 countries. Hackers stole $60 Million worth of cryptocurrencies from Japanese Zaif exchange. Amazon is investigating allegations that its staff is selling customer data.
Security Affairs
JULY 16, 2020
The list of targeted apps includes cryptocurrency wallet applications (i.e. The malware targets 226 applications to steal account credentials, including Gmail, Google Play services, Uber, Amazon, Netflix and Outlook. Coinbase, BitPay, and Coinbase), and banks (i.e. Santander, Barclays, Lloyds, ING, and Wells Fargo).

Security Affairs
AUGUST 4, 2018
Copyright (C) 2014-2015 Media.net Advertising FZ-LLC All Rights Reserved -->. Copyright (C) 2014-2015 Media.net Advertising FZ-LLC All Rights Reserved -->. Copyright (C) 2014 Media.net Advertising FZ-LLC All Rights Reserved -->.
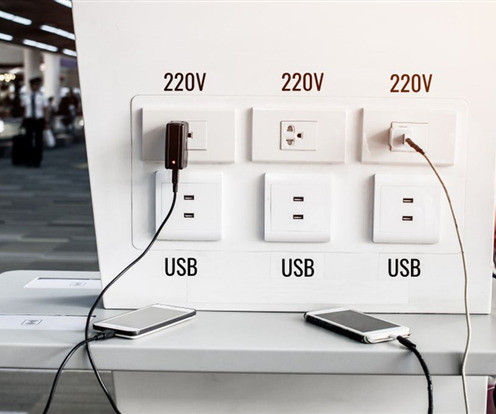
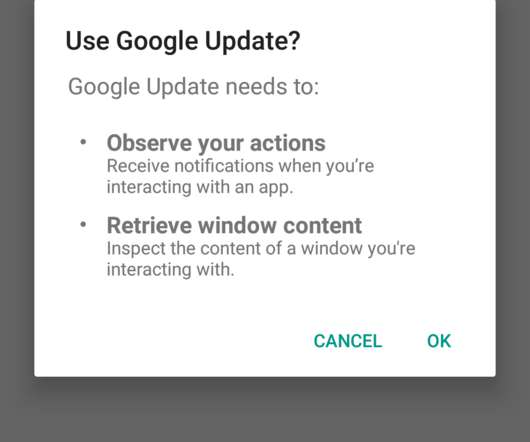
Malwarebytes
APRIL 11, 2023
There are many categories of malware that cybercriminals could install through juice jacking, including adware, cryptominers, ransomware, spyware, or Trojans. While cryptominers mine a mobile phone's CPU/GPU for cryptocurrency and drain its battery, ransomware freezes devices or encrypts files for ransom.

Security Affairs
NOVEMBER 17, 2019
Two men arrested for stealing $550,000 in cryptocurrency with Sim Swapping. WhatsApp flaw CVE-2019-11931 could be exploited to install spyware. New TA2101 threat actor poses as government agencies to distribute malware. The Australian Parliament was hacked earlier this year. Checkra1n, a working iPhone Jailbreak, was released.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content