Who’s Hacking You?
Webroot
MARCH 9, 2021
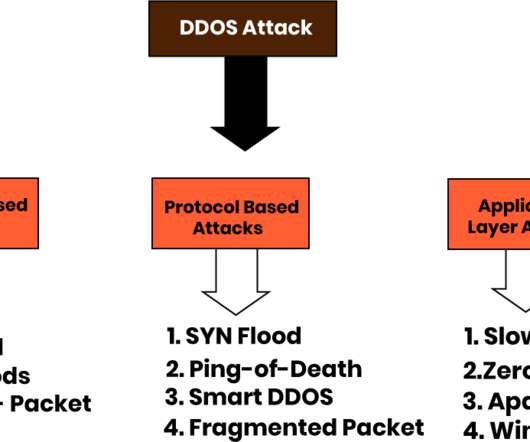
DNS (Domain Name System) is especially vulnerable. One of the most common methods of infiltration includes internet-based attacks, such as Denial of Service (DoS), Distributed Denial of Service (DDoS) and DNS poisoning. However, cybercriminals can also use legal DNS traffic surveillance to their advantage.



































Let's personalize your content