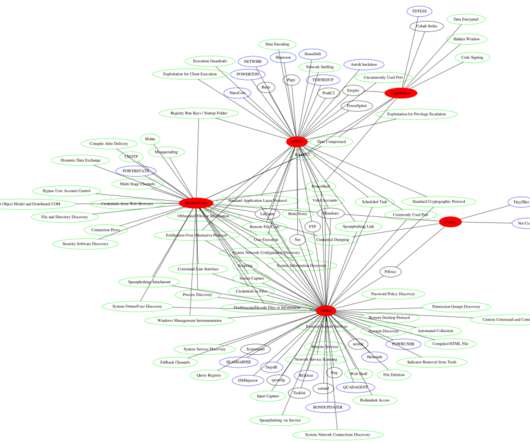
Lyceum APT made the headlines with attacks in Middle East
Security Affairs
AUGUST 27, 2019
reported that Hexane is targeting organizations in the oil and gas industry and telecommunication providers. The malware uses DNS and HTTP-based communication mechanisms. The group also used the ‘Decrypt-RDCMan.ps1,’ that is a password decryption tool included in the PoshC2 framework for penetration testing.













Let's personalize your content