ConnectWise Quietly Patches Flaw That Helps Phishers
Krebs on Security
DECEMBER 1, 2022
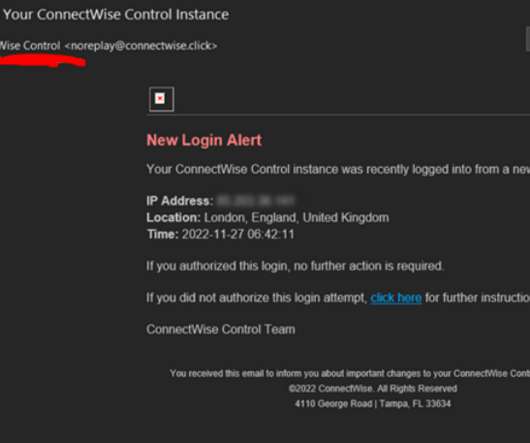
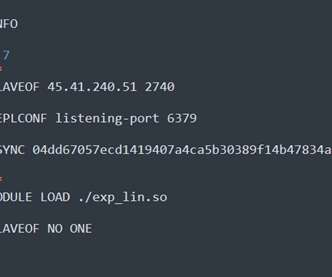
ConnectWise , which offers a self-hosted, remote desktop software application that is widely used by Managed Service Providers (MSPs), is warning about an unusually sophisticated phishing attack that can let attackers take remote control over user systems when recipients click the included link. The warning comes just weeks after the company quietly patched a vulnerability that makes it easier for phishers to launch these attacks.

































Let's personalize your content