The Chinese cyber espionage actor known as Camaro Dragon has been observed leveraging a new strain of self-propagating malware that spreads through compromised USB drives.
"While their primary focus has traditionally been Southeast Asian countries, this latest discovery reveals their global reach and highlights the alarming role USB drives play in spreading malware," Check Point said in new research shared with The Hacker News.
The cybersecurity company, which found evidence of USB malware infections in Myanmar, South Korea, Great Britain, India, and Russia, said the findings are the result of a cyber incident that it investigated at an unnamed European hospital in early 2023.
The probe found that the entity was not directly targeted by the adversary but rather suffered a breach via an employee's USB drive, which became infected when it was plugged into a colleague's computer at a conference in Asia.
"Consequently, upon returning to the healthcare institution in Europe, the employee inadvertently introduced the infected USB drive, which led to spread of the infection to the hospital's computer systems," the company said.
Camaro Dragon shares tactical similarities with that of activity clusters tracked as Mustang Panda and LuminousMoth, with the adversarial crew recently linked to a Go-based backdoor called TinyNote and a malicious router firmware implant named HorseShell.
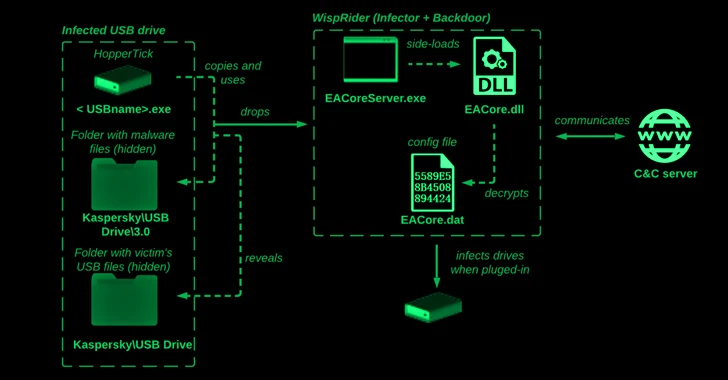
The latest infection chain comprises a Delphi launcher known as HopperTick that's propagated via USB drives and its primary payload dubbed WispRider, which is responsible for infecting the devices when they are attached to a machine.
"When a benign USB thumb drive is inserted into an infected computer, the malware detects a new device inserted into the PC and manipulates its files, creating several hidden folders at the root of the thumb drive," Check Point researchers said.
WispRider, besides infecting the current host if not already, is tasked with communicating with a remote server, compromising any newly connected USB devices, executing arbitrary commands, and performing file operations.
Select variants of WispRider also function as a backdoor with capabilities to bypass an Indonesian antivirus solution called Smadav as well as resort to DLL side-loading by using components from security software like G-DATA Total Security.
Another post-exploitation payload delivered alongside WispRider is a stealer module referred to as disk monitor (HPCustPartUI.dll) that stages files with predefined extensions (i.e., docx, mp3, wav, m4a, wma, aac, cda, and mid) for exfiltration.
This is not the first time Chinese threat actors have been observed taking advantage of USB devices as an infection vector to reach environments far beyond the scope of their primary interests.
In November 2022, Google-owned Mandiant attributed UNC4191, a threat actor with a suspected China nexus, to a set of espionage attacks in the Philippines that lead to the distribution of malware such as MISTCLOAK, DARKDEW, and BLUEHAZE.
A subsequent report from Trend Micro in March 2023 revealed overlaps between UNC4191 and Mustang Panda, connecting the latter to the use of MISTCLOAK and BLUEHAZE in spear-phishing campaigns targeting countries in Southeast Asia.
"The group tends to build its arsenal with similar C&C protocols and capabilities in different programming languages, showing that the actors behind Earth Preta have likely been enhancing their development skills," the company said in a follow-up report published this month.
The nation-state crew has since been spotted expanding its targeting footprint to include Western Asia and Eastern Europe, directing its attacks against governments, telecommunication services, educational institutions, and think-tanks.
It has also utilized new droppers like TONEDROP to deliver implants like TONEINS and TONESHELL as well as employ fake Google Drive sites to distribute MQsTTang (aka QMAGENT), another known Mustang Panda backdoor. Furthermore, code similarities have been identified between MQsTTang and TinyNote (aka MIROGO).
The development is a sign that the threat actors are actively changing their tools, tactics, and procedures (TTPs) to bypass security solutions, while simultaneously relying on a vast collection of custom tools to exfiltrate sensitive data from victim networks.
"The Camaro Dragon APT group continues to employ USB devices as a method for infecting targeted systems, effectively combining this technique with other established tactics," the researchers said.
(The story was updated after publication to highlight additional tactics adopted by the threat actor in recent spear-phishing attacks.)