Injecting a Backdoor into SolarWinds Orion
Schneier on Security
JANUARY 19, 2021
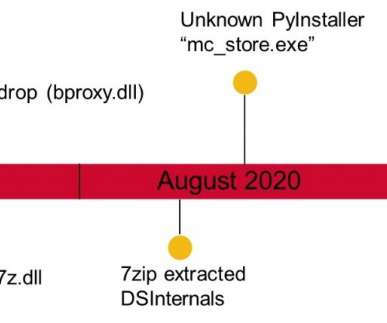
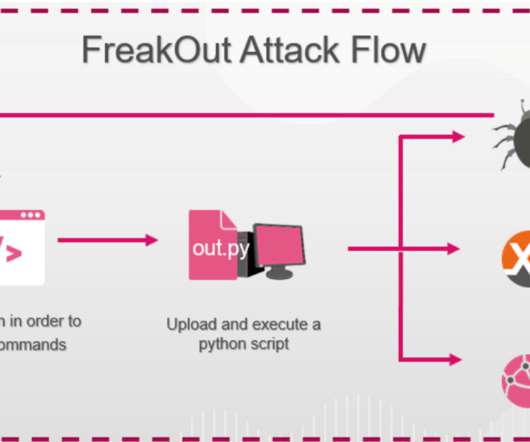
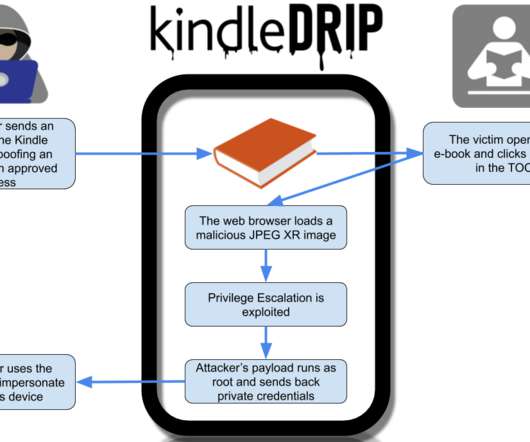
Crowdstrike is reporting on a sophisticated piece of malware that was able to inject malware into the SolarWinds build process: Key Points. SUNSPOT is StellarParticle’s malware used to insert the SUNBURST backdoor into software builds of the SolarWinds Orion IT management product. SUNSPOT monitors running processes for those involved in compilation of the Orion product and replaces one of the source files to include the SUNBURST backdoor code.







































Let's personalize your content