U.S. Secret Service: “Massive Fraud” Against State Unemployment Insurance Programs
Krebs on Security
MAY 16, 2020
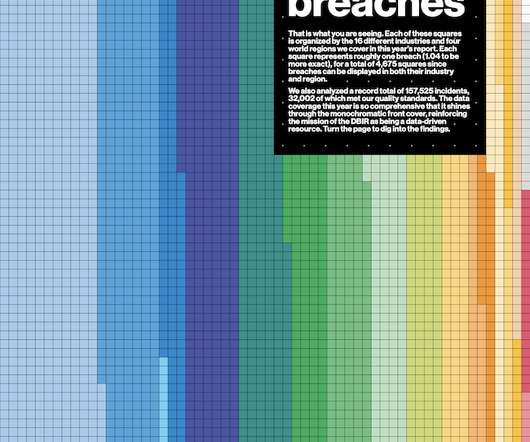
A well-organized Nigerian crime ring is exploiting the COVID-19 crisis by committing large-scale fraud against multiple state unemployment insurance programs, with potential losses in the hundreds of millions of dollars, according to a new alert issued by the U.S. Secret Service. A memo seen by KrebsOnSecurity that the Secret Service circulated to field offices around the United States on Thursday says the ring has been filing unemployment claims in different states using Social Security numbers




































Let's personalize your content