Florence, Ala. Hit By Ransomware 12 Days After Being Alerted by KrebsOnSecurity
Krebs on Security
JUNE 9, 2020
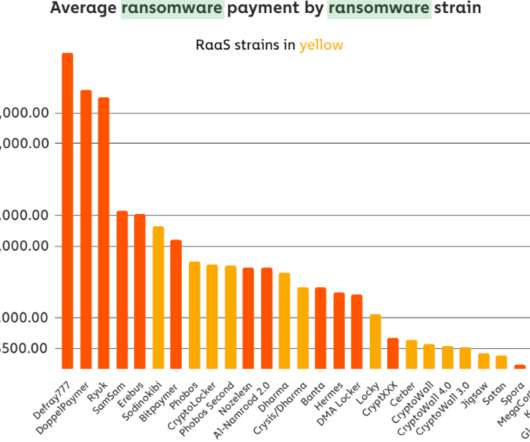
In late May, KrebsOnSecurity alerted numerous officials in Florence, Ala. that their information technology systems had been infiltrated by hackers who specialize in deploying ransomware. Nevertheless, on Friday, June 5, the intruders sprang their attack, deploying ransomware and demanding nearly $300,000 worth of bitcoin. City officials now say they plan to pay the ransom demand, in hopes of keeping the personal data of their citizens off of the Internet.







































Let's personalize your content