Hackers Were Inside Citrix for Five Months
Krebs on Security
FEBRUARY 19, 2020
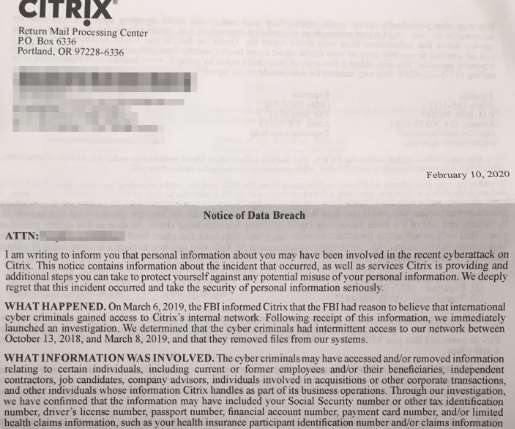
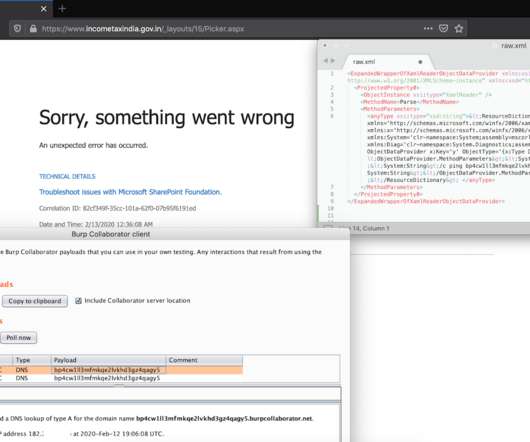
Networking software giant Citrix Systems says malicious hackers were inside its networks for five months between 2018 and 2019, making off with personal and financial data on company employees, contractors, interns, job candidates and their dependents. The disclosure comes almost a year after Citrix acknowledged that digital intruders had broken in by probing its employee accounts for weak passwords.

































Let's personalize your content