Be Very Sparing in Allowing Site Notifications
Krebs on Security
NOVEMBER 17, 2020
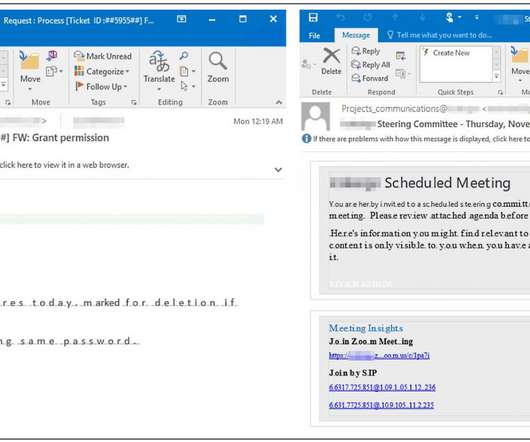
An increasing number of websites are asking visitors to approve “notifications,” browser modifications that periodically display messages on the user’s mobile or desktop device. In many cases these notifications are benign, but several dodgy firms are paying site owners to install their notification scripts and then selling that communications pathway to scammers and online hucksters.

































Let's personalize your content