Phishing attacks target Chase Bank customers
Tech Republic Security
APRIL 27, 2021
Two email campaigns discovered by Armorblox impersonated Chase in an attempt to steal login credentials.

Tech Republic Security
APRIL 27, 2021
Two email campaigns discovered by Armorblox impersonated Chase in an attempt to steal login credentials.

Threatpost
APRIL 29, 2021
The perp faces jail time, but the incident highlights the growing cyber-abuse of QR codes.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Troy Hunt
APRIL 29, 2021
Today I'm very happy to announce the arrival of the 15th government to Have I Been Pwned, Romania. As of now, CERT-RO has access to query all Romanian government domains across HIBP and subscribe them for future notifications when subsequent data breaches affect aliases on those domains. Romania joins a steadily growing number of governments across the globe to have free and unrestricted access to API-based domain searches for their assets in HIBP.

Schneier on Security
APRIL 26, 2021
If you don’t have enough to worry about already, consider a world where AIs are hackers. Hacking is as old as humanity. We are creative problem solvers. We exploit loopholes, manipulate systems, and strive for more influence, power, and wealth. To date, hacking has exclusively been a human activity. Not for long. As I lay out in a report I just published , artificial intelligence will eventually find vulnerabilities in all sorts of social, economic, and political systems, and then exploit

Advertisement
How many people would you trust with your house keys? Chances are, you have a handful of trusted friends and family members who have an emergency copy, but you definitely wouldn’t hand those out too freely. You have stuff that’s worth protecting—and the more people that have access to your belongings, the higher the odds that something will go missing.
Krebs on Security
APRIL 26, 2021
In 2017, KrebsOnSecurity showed how easy it is for identity thieves to undo a consumer’s request to freeze their credit file at Experian , one of the big three consumer credit bureaus in the United States. Last week, KrebsOnSecurity heard from a reader who had his freeze thawed without authorization through Experian’s website, and it reminded me of how truly broken authentication and security remains in the credit bureau space.

Tech Republic Security
APRIL 26, 2021
A former IT pro turned end user explains why blending your work and personal tech was, is and always will be a bad idea for you and your employer.
Cyber Security Informer brings together the best content for cyber security professionals from the widest variety of industry thought leaders.

Schneier on Security
APRIL 30, 2021
Apple just patched a MacOS vulnerability that bypassed malware checks. The flaw is akin to a front entrance that’s barred and bolted effectively, but with a cat door at the bottom that you can easily toss a bomb through. Apple mistakenly assumed that applications will always have certain specific attributes. Owens discovered that if he made an application that was really just a script—code that tells another program what do rather than doing it itself—and didn’t include a standard ap

Security Boulevard
APRIL 29, 2021
Neurodiversity, the term for the range of differences in individual brain function and behavioral traits, with regard to sociability, learning, attention, mood and other mental functions in a non-pathological sense, is important to foster in any industry, but the security space in particular has always welcomed a range of neurodiverse groups. Whether professionals are diagnosed.

Tech Republic Security
APRIL 28, 2021
Palo Alto Networks' cloud-native security suite is getting a bundle of new features to automate VM security and add malware protection to CI/CD workflows, among others.

Bleeping Computer
APRIL 30, 2021
Hackers suspected to work for the Chinese government have used a new malware called PortDoor to infiltrate the systems of an engineering company that designs submarines for the Russian Navy. [.].

Advertiser: Revenera
In a recent study, IDC found that 64% of organizations said they were already using open source in software development with a further 25% planning to in the next year. Most organizations are unaware of just how much open-source code is used and underestimate their dependency on it. As enterprises grow the use of open-source software, they face a new challenge: understanding the scope of open-source software that's being used throughout the organization and the corresponding exposure.

Schneier on Security
APRIL 27, 2021
Moxie Marlinspike has an intriguing blog post about Cellebrite , a tool used by police and others to break into smartphones. Moxie got his hands on one of the devices, which seems to be a pair of Windows software packages and a whole lot of connecting cables. According to Moxie, the software is riddled with vulnerabilities. (The one example he gives is that it uses FFmpeg DLLs from 2012, and have not been patched with the 100+ security updates since then.). …we found that it’s possib

CyberSecurity Insiders
APRIL 28, 2021
Cancer treatment services across the United States have taken a big hit as a cyber attack is said to have disrupted the software services operating in the High-tech radiation machines used to treat the malign disease. Elekta is the company in discussion that was hit by a cyber attack and as it supplies software meant to operate radiation treatment systems, most of the medical treatments were cancelled or postponed across North America.
Tech Republic Security
APRIL 28, 2021
The phishing emails use a Microsoft logo within an HTML table, which is not analyzed by security programs, says Inky.

Graham Cluley
APRIL 28, 2021
Apple has released a brand new update for its macOS Big Sur operating system, and you really should install it. Amongst other fixes, Big Sur 11.3 patches a zero-day vulnerability that could allow an attacker to craft malicious payloads that will not be checked by Gatekeeper, the security check built into Apple's operating system that is supposed to block the execution of software from untrusted sources.

Advertisement
The healthcare industry has massively adopted web tracking tools, including pixels and trackers. Tracking tools on user-authenticated and unauthenticated web pages can access personal health information (PHI) such as IP addresses, medical record numbers, home and email addresses, appointment dates, or other info provided by users on pages and thus can violate HIPAA Rules that govern the Use of Online Tracking Technologies by HIPAA Covered Entities and Business Associates.

Schneier on Security
APRIL 29, 2021
In this entertaining story of French serial criminal Rédoine Faïd and his jailbreaking ways, there’s this bit about cell phone surveillance: After Faïd’s helicopter breakout, 3,000 police officers took part in the manhunt. According to the 2019 documentary La Traque de Rédoine Faïd , detective units scoured records of cell phones used during his escape, isolating a handful of numbers active at the time that went silent shortly thereafter.

Bleeping Computer
APRIL 28, 2021
A recently discovered Linux malware with backdoor capabilities has flown under the radar for years, allowing attackers to harvest and exfiltrate sensitive information from compromised devices. [.].

Tech Republic Security
APRIL 27, 2021
The spyware tries to steal passwords and other sensitive data and accesses your contact list, warns the U.K.'s National Cyber Security Centre.

Security Boulevard
APRIL 27, 2021
Research that’s done on malicious breaches of data presents a unique conundrum for the security professionals who are doing the investigating: should access to sets of breached raw data become available to public users and, if so, how? In light of the pandemic, the acceleration toward location-distributed work has the potential to raise similar questions.

Speaker: Blackberry, OSS Consultants, & Revenera
Software is complex, which makes threats to the software supply chain more real every day. 64% of organizations have been impacted by a software supply chain attack and 60% of data breaches are due to unpatched software vulnerabilities. In the U.S. alone, cyber losses totaled $10.3 billion in 2022. All of these stats beg the question, “Do you know what’s in your software?
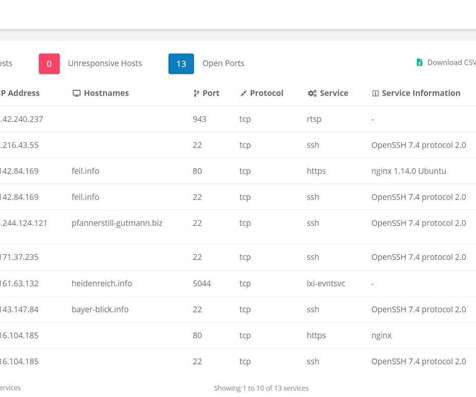
The Hacker News
APRIL 29, 2021
Hackers are scanning the internet for weaknesses all the time, and if you don't want your organization to fall victim, you need to be the first to find these weak spots. In other words, you have to adopt a proactive approach to managing your vulnerabilities, and a crucial first step in achieving this is performing a vulnerability assessment.
Bleeping Computer
APRIL 25, 2021
Emotet, one of the most dangerous email spam botnets in recent history, is being uninstalled today from all infected devices with the help of a malware module delivered in January by law enforcement. [.].

Hot for Security
APRIL 26, 2021
Phishing attacks masquerading as QuickBooks invoices are targeting users of the popular accounting software in an attempt to infect victim’s devices with the infamous Dridex banking Trojan. Spotted by Bitdefender Antispam Lab, this fresh Intuit-themed malspam campaign reels in QuickBooks users with fake payment notifications and invoices. The ongoing phishing campaign began on April 19, targeting QuickBooks users from across the globe.

Security Boulevard
APRIL 28, 2021
All business industries have seen increasing pressure to digitize their services in recent years, particularly over the past 12 months in response to COVID-19. But few industries have felt this pressure more than the financial sector, where customers have grown to expect high-quality digital services, particularly since so many financial organizations are unable to provide.

Advertisement
Within the past few years, ransomware attacks have turned to critical infrastructure, healthcare, and government entities. Attackers have taken advantage of the rapid shift to remote work and new technologies. Add to that hacktivism due to global conflicts and U.S. elections, and an increased focus on AI, and you have the perfect recipe for a knotty and turbulent 2024.

CyberSecurity Insiders
APRIL 28, 2021
This blog was written by an independent guest blogger. On December 8, 2020, Kubernetes released version 1.20—the third and final release of the popular container orchestration platform in 2020. Kubernetes noted in a blog post that the version contained 42 enhancements. Of those enhancements, 16 entered into alpha, while the remainder moved to beta or graduated to stable at 15 and 11, respectively.
Bleeping Computer
APRIL 27, 2021
Millions of email addresses collected by Emotet botnet for malware distribution campaigns have been shared by the Federal Bureau of Investigation (FBI) as part of the agency's effort to clean infected computers. [.].

CSO Magazine
APRIL 29, 2021
The adoption of edge computing and cloud infrastructure over the past decade combined with the recent surge in remote work, have seriously challenged traditional network architectures and security models. Large enterprises have been better able to adapt to this new reality, having access to larger IT budgets and skilled employees, but small and medium-sized businesses are struggling to keep up with the access control, monitoring and threat detection technologies needed to defend their local and

Security Boulevard
APRIL 29, 2021
One of our memes was reposted by The Cyber Security Hub, an infosec community with greater than 1 million (yes, it’s MILLION) followers on LinkedIn. The meme (see below) was on the topic of cybersecurity budgets and it was our tongue-in-cheek way to start a discussion. But we were blown away by the response it …. Read More. The post The Infosec Meme That Touched a Raw Nerve appeared first on Security Boulevard.

Speaker: Erika R. Bales, Esq.
When we talk about “compliance and security," most companies want to ensure that steps are being taken to protect what they value most – people, data, real or personal property, intellectual property, digital assets, or any other number of other things - and it’s more important than ever that safeguards are in place. Let’s step back and focus on the idea that no matter how complicated the compliance and security regime, it should be able to be distilled down to a checklist.

CyberSecurity Insiders
APRIL 30, 2021
Nitro Ransomware, a new variant of file encrypting malware is shaking up the internet by demanding Discord Nitro Gift Cards from victims instead of cryptocurrency. Researchers from MalwareHunterTeam have discovered this activity and discovered that the distributors of this malware are giving only 3 hours to buy the gift card after which the stolen data will leaked to the internet.
Bleeping Computer
APRIL 24, 2021
A recently discovered cryptomining botnet is actively scanning for vulnerable Windows and Linux enterprise servers and infecting them with Monero (XMRig) miner and self-spreader malware payloads. [.].

CSO Magazine
APRIL 27, 2021
Organizations will face significant challenges in purchasing, renewing, and benefitting from cyber insurance policies this year as various factors drive the sector towards a stricter, more specialized position, global specialists in law, risk, and cybersecurity predict. These include the continued evolution and impact of cyberthreats throughout 2020 and the early months of 2021, chiefly in the form of ransomware attacks and wide-ranging supply chain security issues.

Security Boulevard
APRIL 29, 2021
Over six months on, the Schrems II verdict is proving to be a difficult obstacle for many businesses when it comes to data management. Find out why here. The post What is Schrems II and how does it affect your data protection in 2021? appeared first on Security Boulevard.

Speaker: William Hord, Vice President of ERM Services
A well-defined change management process is critical to minimizing the impact that change has on your organization. Leveraging the data that your ERM program already contains is an effective way to help create and manage the overall change management process within your organization. Your ERM program generally assesses and maintains detailed information related to strategy, operations, and the remediation plans needed to mitigate the impact on the organization.
Let's personalize your content