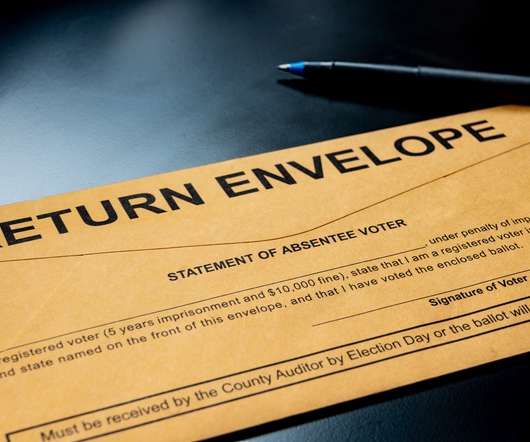
Personal Information of Millions of US Voters Available on Dark Web
Adam Levin
SEPTEMBER 1, 2020
Databases containing the personal information of millions of U.S. voters have appeared on Russian hacking forums. According to Russian news outlet Kommersant , a hacker called Gorka9 has posted the personal information of several million registered voters in Michigan, Arkansas, Connecticut, Florida, and South Carolina.The data includes names, birthdates, gender, mailing addresses, email addresses and polling station numbers.



































Let's personalize your content