Vulnerability management tools discover security flaws in network and cloud environments and prioritize and apply fixes. They go beyond vulnerability scanning tools, creating an overall vulnerability map for businesses with features like risk scores, asset discovery, and reports. We scored industry-leading vulnerability management tools and selected six of the best, analyzing their features, pros, and cons to help you find the right product for your team.
Here are the top six vulnerability management systems:
- Rapid7 InsightVM: Best overall vulnerability management solution
- Tenable Nessus: Best choice for pen testers and other contractors
- Qualys VMDR: Best for organizations with complex environments
- Holm Security: Best tool for improving employee security posture
- Digital Defense Frontline VM: Best for SMB vulnerability testing
- Microsoft Defender: Best tool for extensive Microsoft ecosystems
Featured Partners: Vulnerability Management Software
Top Vulnerability Management Software Compared
The following table briefly compares our top picks, including features like asset categorization and risk scores as well as pricing details:
| Asset Grouping | Risk Scoring | IoT Asset Identification | Pricing Information | |
|---|---|---|---|---|
| Rapid7 InsightVM | ✔️ | ✔️ | ❌ | • $2.19/asset/month for 250 assets |
| Tenable Nessus | ✔️ | ✔️ | ❌ | • Professional plan: $3,590/year • Expert plan: $5,290/year |
| Qualys VMDR | ✔️ | ✔️ | ✔️ | • Priced per asset; requires a quote request |
| Holm Security | ✔️ | ✔️ | ✔️ | • Requires a quote request |
| Digital Defense Frontline VM | ✔️ | ✔️ | ❌ | • Requires a quote request |
| Microsoft Defender | ✔️ | ❌ | ❌ | • $3/user/month for standalone product • $2/user/month for Defender for Endpoint add-on |
Table of Contents

Rapid7 InsightVM
Best Overall Vulnerability Management Solution
Overall Rating: 4.1/5
- Pricing: 5/5
- Core Features: 4.3/5
- Additional Features: 2.3/5
- Ease of Use & Admin: 4.8/5
- Customer Support: 4.5/5
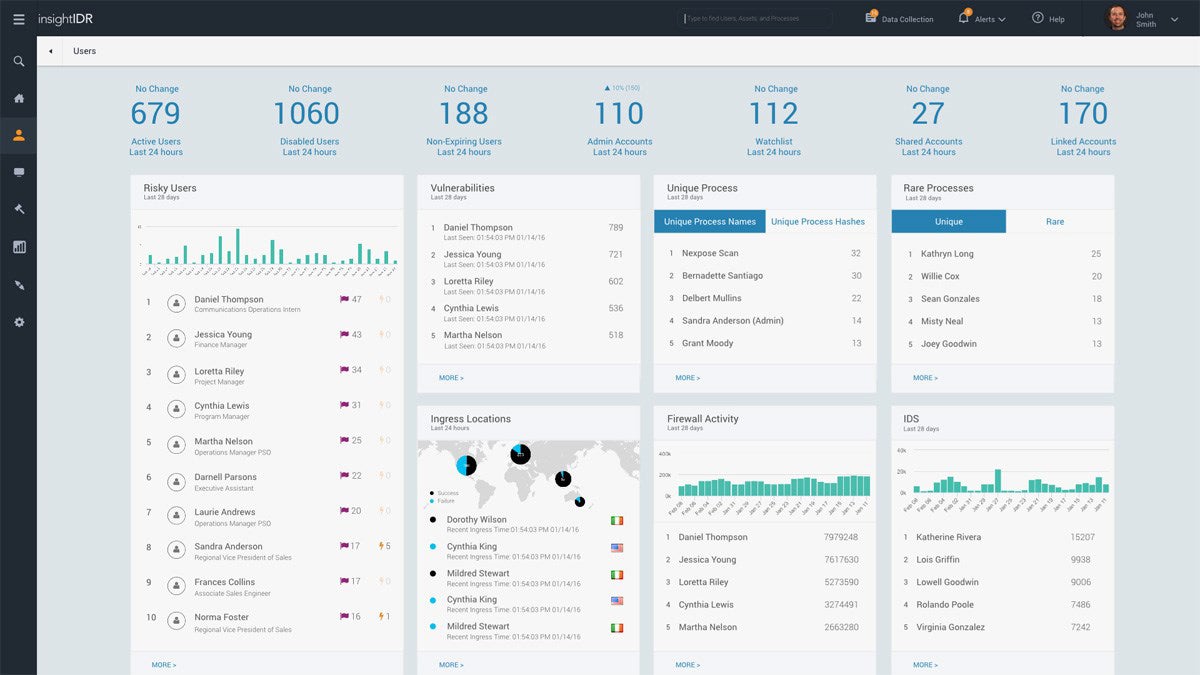
Rapid7 InsightVM is a scalable vulnerability management solution for enterprises of all sizes. One of its most sought-after features is risk prioritization, with step-by-step instructions for effective remediation. Good value and automation make InsightVM particularly useful for SMBs, but organizations with greater expertise can benefit from its risk prioritization capabilities. For those lacking sophisticated security teams, InsightVM is also available as a managed service.
While InsightVM is a strong overall solution for multiple teams, it lacks role-based access controls and doesn’t support IoT assets. Consider Holm Security if you’re looking for a VM solution that offers these features and still serves both SMBs and large teams.
| Pros | Cons |
|---|---|
| Reasonable pricing for smaller enterprises | Lacks patch rollback features |
| Supports vulnerability exceptions if you need to accept a risk | Lacks role-based access control |
| Available as a managed service | No support for identifying IoT assets |
Pricing
- Cost: For 250 assets minimum, Rapid7 costs approximately $2.19/asset/month; for larger increments of assets, the price per asset decreases.
- Free trial: Potential customers can try InsightVM for 30 days.
Key Features
- Real-time risk viewing: Customizable dashboards offer up-to-date vulnerability information.
- Integrated threat feeds: Teams can view the most relevant threats at the moment.
- Third-party integrations: InsightVM integrates with tools like CyberArk, Palo Alto, and McAfee.
- Asset grouping: This helps teams target and report on specific asset groups.
Tenable Nessus
Best Choice for Pen Testers & Other Contractors
Overall Rating: 3.6/5
- Pricing: 3.5/5
- Core Features: 4.2/5
- Additional Features: 3/5
- Ease of Use & Admin: 3.6/5
- Customer Support: 3.8/5
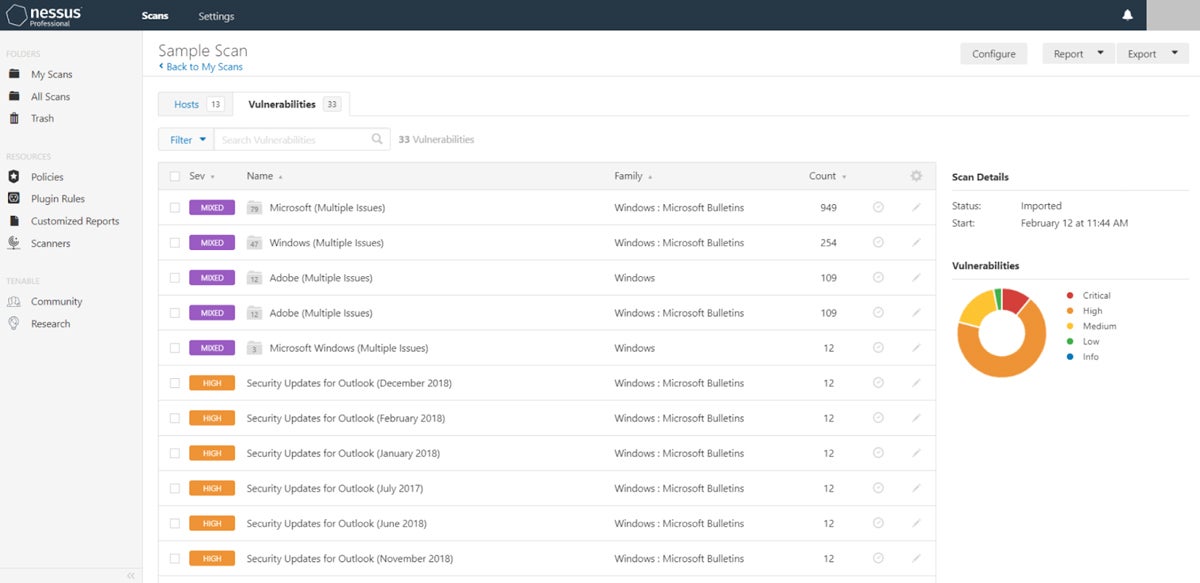
Tenable Nessus is a vulnerability assessment solution for both businesses and security contractors. It offers features like role-based access controls, as well as asset grouping to simplify threat remediation for similar issues. SMBs, developers, pen testers, and consultants will find Nessus Expert most useful, but features like external attack surface scanning have broad appeal. Consider Nessus if your business is focused on security audits and internal compliance efforts.
Because Nessus lacks some advanced VM features, it’s not the best choice for enterprises. If you’re a large business, consider a product like Holm Security, which offers features like IoT asset identification and some patch management functionality.
| Pros | Cons |
|---|---|
| Designed for contractors like pen testers | Might not serve all the needs of large businesses |
| 24/7 advanced support available as an add-on | Nessus Pro and Expert trials are only 7 days |
| Good option for small businesses | Lacks some advanced features like IoT asset identification |
Pricing
Tenable Nessus offers two plans:
- Professional: $3,590/year
- Expert: $5,290/year
Potential buyers should also know the following:
- Support pricing: Advanced customer support requires add-on pricing.
- Free trials: Tenable offers week-long free trials for both plans.
Key Features
- Third-party integrations: Splunk, Fortinet, and Palo Alto are highlights.
- Role-based access controls: Customers can choose to enable these if they like.
- Asset grouping: Asset lists help to logically organize assets by business function.
- Preconfigured templates: Nessus offers over 450 prebuilt vulnerability templates.

Qualys VMDR
Best for Organizations with Complex Environments
Overall Rating: 3.6/5
- Pricing: 3.5/5
- Core Features: 3.9/5
- Additional Features: 2.5/5
- Ease of Use & Admin: 3.5/5
- Customer Support: 4.8/5
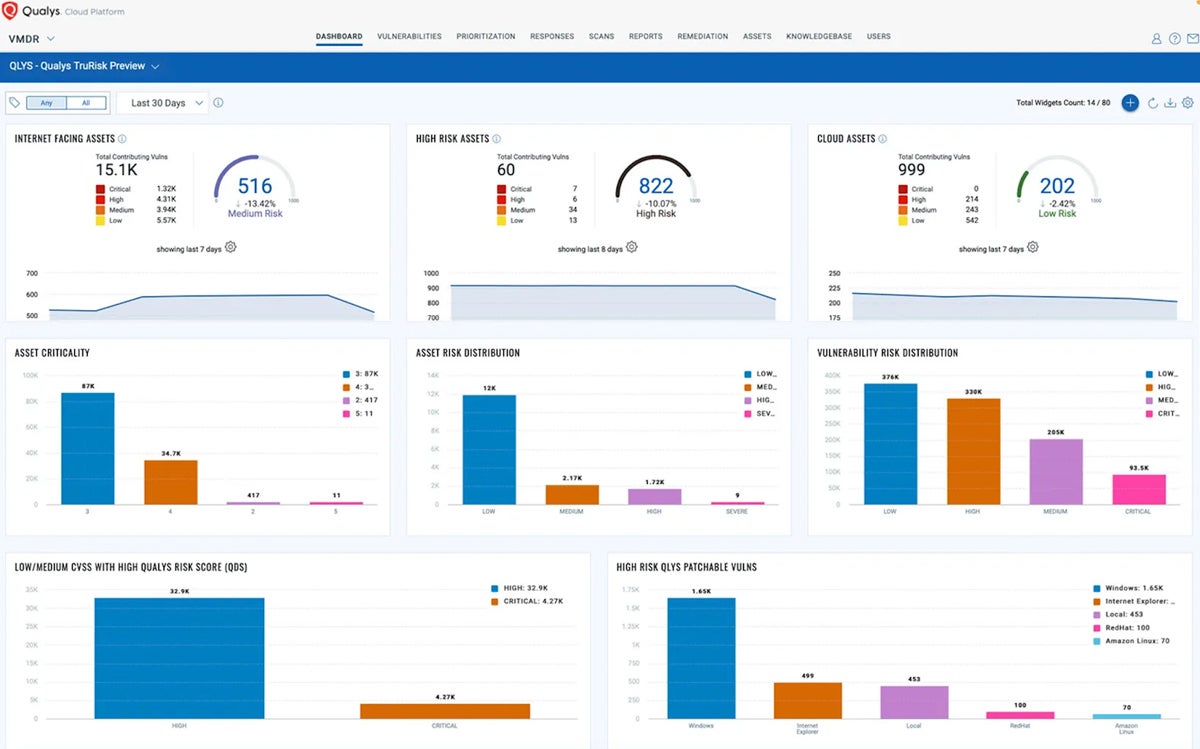
Qualys VMDR 2.0 with TruRisk is an enterprise-grade cyber risk management solution for complex security environments. VMDR uses Center for Internet Security (CIS) benchmarks to find misconfigurations and vulnerabilities in your business’s assets. Consider Qualys if you’re a medium-to-large organization with a security infrastructure that’s already built out. It’s a good solution for complex environments because it can scan IoT devices and operational tech.
Qualys isn’t available as a managed service; if your team needs that, look at Rapid7 instead. It also offers industry benchmarking functionality and transparent pricing, which Qualys lacks.
| Pros | Cons |
|---|---|
| Plenty of customer support options | Limited pricing information |
| Supports a variety of assets, including OT and IoT | No industry benchmarking capabilities |
| Has a strong set of core management features | Not available as a managed service |
Pricing
- Asset-based pricing: Qualys VMDR 2.0 with TruRisk is priced per asset.
- Contact Qualys for details: You can either sign up for a free trial or request a quote from the Qualys sales team.
Key Features
- IoT asset identification: Teams need a complete inventory of their IoT landscape.
- Training videos: A video library with setup instructions helps teams get started with VMDR.
- No-code automation: Teams can design workflow automation for vulnerability remediation tasks.
- Patch management: VMDR automatically finds vulnerabilities and deploys the associated patches.

Holm Security
Best Tool for Improving Employee Security Posture
Overall Rating: 3.2/5
- Pricing: 1.5/5
- Core Features: 4.3/5
- Additional Features: 4.3/5
- Ease of Use & Admin: 1.8/5
- Customer Support: 3.3/5
Holm Security VMP is a next-gen vulnerability management platform that helps detect vulnerabilities across your enterprise network and human assets on a single platform. Among the platform’s standout features is its phishing module, which simulates phishing attacks on employees to identify weaknesses and train teams to better promote security. Holm Security VMP is preferred by SMBs thanks to its value and features like phishing awareness, but its capabilities also apply to large teams.
Holm Security isn’t available as a managed service. If your business wants a powerful VM solution offered as a service, consider Rapid7 instead.
| Pros | Cons |
|---|---|
| Designed for comprehensive business security | Lacks transparent pricing information |
| Offers ticketing, CMDB, and single-sign on integrations | Lacks patch rollback features |
| Good choice for both small and large teams | Not available as a managed service |
Pricing
- Contact Holm Security for pricing: It doesn’t provide pricing publicly, so you’ll need to request a quote from its sales team for detailed pricing information.
Key Features
- Integrations with CI/CD tools: Teams can find vulnerabilities in their business’s codebases.
- Finding IoT assets: Holm Security looks for vulnerabilities in devices across your infrastructure.
- Role-based access controls: These manage teams’ access to important applications.
- Integrations with other security tools: Highlights include Splunk and Microsoft Sentinel.

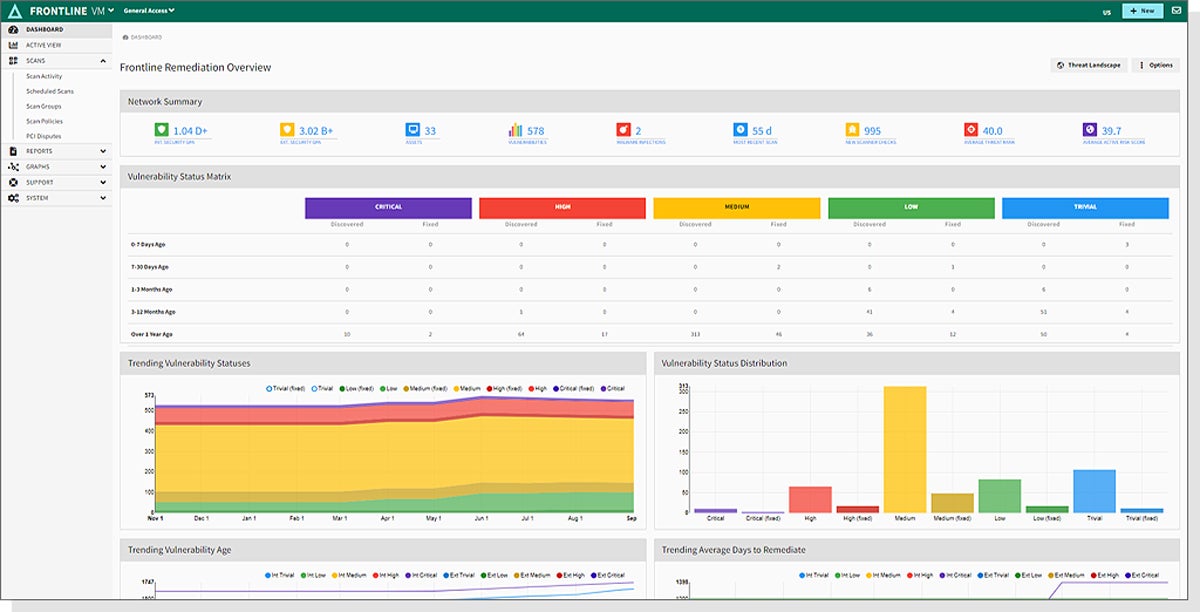
Digital Defense Frontline VM
Best for SMB Vulnerability Testing
Overall Rating: 3.1/5
- Pricing: 1.5/5
- Core Features: 3.3/5
- Additional Features: 3/5
- Ease of Use & Admin: 3.3/5
- Customer Support: 4.5/5
Digital Defense Frontline Vulnerability Manager (Frontline VM) is a comprehensive SaaS VM tool that covers all network assets. Frontline VM is among the most user-friendly tools on this list. It’s well suited to the vulnerability and penetration testing demands of SMBs. That said, Digital Defense’s on-demand service can also meet the needs of a large-scale organization — just keep in mind that you’ll need to source your patch management functionality elsewhere.
Consider Qualys if your business is looking for internal patch management in a vulnerability management product; Qualys is also a good choice for larger teams.
| Pros | Cons |
|---|---|
| Users find Frontline VM easy to use overall | Lacking in patch management or patch rollback features |
| Offered as a managed service | No transparent enterprise pricing |
| Support is available 24/7 via phone and email | Limited documentation and training videos |
Pricing
Contact Digital Defense for pricing information: It doesn’t provide pricing directly, so you’ll need to fill out a quote request for detailed information.
Key Features
- Security integrations: These include vendors like ServiceNow, LogRhythm, and Palo Alto.
- Role-based access controls: Security teams can restrict employee access to sensitive data.
- Risk scores: Scoring comes from either prebuilt or configured risk profiles that take threat rankings into account.
- Network mapping: Businesses can visualize threats across their network devices with filtering and asset relationships.
Microsoft Defender
Best Tool for Extensive Microsoft Ecosystems
Overall Rating: 3/5
- Pricing: 4.5/5
- Core Features: 3/5
- Additional Features: 2.3/5
- Ease of Use & Admin: 2/5
- Customer Support: 3.3/5
Microsoft Defender Vulnerability Management is a VM product that makes sense for existing Microsoft customers, but it can stand on its own, too. Microsoft’s security business is impressive, if its recent MITRE scores are any indication, and it offers features like app blocking. Defender VM also integrates with plenty of other Microsoft products, including Microsoft Sentinel. Consider Defender if you want to build out your Windows security infrastructure.
However, if your team uses a lot of non-Windows tech, you may want to consider a solution like Tenable Nessus, which supports Mac, Linux, and Windows operating systems. Nessus also offers risk scoring, and Defender doesn’t.
| Pros | Cons |
|---|---|
| Users can view vulnerable device reports to find weaknesses | The Vulnerability Management standalone product doesn’t have risk scoring |
| Defender VM integrates with Defender for Endpoint and other Microsoft products | Patch management and patch rollback features aren’t available |
| Free trial lasts 90 days, giving teams plenty of time to make a choice | Defender may be challenging to integrate with non-Windows environments |
Pricing
- $2/user/month add-on pricing: This is applicable to Microsoft Defender for Endpoint Plan 2 and Microsoft 365 E5.
- $3/user/month as a standalone solution: This plan is designed to support EDR products.
Key Features
- Application blocking: Defender is able to block vulnerable programs and alert customers with specific messages about the applications.
- Security assessments: Teams can compare their cybersecurity to industry benchmarks like the National Institute of Standards and Technology (NIST) and CIS.
- Threat intelligence data: Defender provides information on the potential for breaches and which endpoint devices are vulnerable.
- Regular assessments: Defender looks for outdated certificates, insufficient algorithms for digital signatures, and misconfigurations.

Top 5 Features of Vulnerability Management Software
Shortlist the top features your business needs, including monitoring, risk scores, attack surface visualization, automation, and reports, when you’re selecting any cybersecurity solution. Note that few tools provide all of these capabilities. Some have a few, while some offer many.
Continuous Monitoring & Scanning
Potential vulnerabilities can pop up at any time, and vulnerability management systems should be a consistently-active line of defense. Your vulnerability management software should continuously look for potential problems. Zero-day vulnerability management, in particular, needs to rapidly identify issues so your business can mitigate threats before they cost you money.
Risk Scoring
Cataloging and remediating risks can easily become overwhelming if your security team doesn’t know exactly what steps to take. Scoring risks based on their severity helps personnel prioritize remediation tasks. For example, an unpatched zero day is probably a more urgent fix than an employee’s outdated version of Microsoft Word. Risk scoring plays a critical role in ensuring that vulnerability management is successful over time because it helps employees avoid overwhelm.
Attack Surface Visualization
Attack surface visualization is intended to simplify the process of identifying all the places your business could be attacked. It should cover internet-facing and internal assets to give your team a complete picture of its vulnerabilities and the areas that the team needs to protect.
Automated Remediation
Security teams don’t always have time to fix every vulnerability. This is where automation comes in: Remediation strategies should ideally have automatic fixes for at least some vulnerability management tasks. For example, a predesigned patch management workflow might be triggered when a vulnerability scanner detects an unpatched asset. Then your security team knows exactly what to patch.
Customizable Reporting
Often, other teams in your organization need to know what’s going on in the IT department. Reports help security teams provide the most relevant information to company stakeholders, including the executive team. Policy-driven compliance reports are also important, not just current vulnerability stats. Ideally, the reporting feature in a vulnerability management tool should offer both premade templates and customization options so your security team can tailor reports to your business’s needs.
How We Evaluated Vulnerability Management Software
We evaluated a broad selection of vulnerability management products using a product scoring rubric. When we create guides for buyers, we look at available information, including vendor product pages, data sheets, and independent user reviews, as we analyze products to determine those that are best for our audience. We divided this rubric into five categories. Each of the categories had subcriteria with its own weighting, which factored into the total product score. The product received an overall score out of five.
The six products that scored highest made our list; each overall score was based on whether the product met the specific criteria we set for the rubric. The criteria for this rubric included pricing, major vulnerability management features, nice-to-have features, overall ease of use, and technical support availability.
Pricing | 15%
In this category, we evaluated the vendor’s pricing availability, its relative value, and any free product trials.
- Criterion Winner: Rapid7
Core Features | 30%
We looked at the most important features of vulnerability management tools, including asset discovery, risk scoring, patching, and reporting capabilities, and whether these vendors offered them.
- Criterion Winner: Multiple winners
Additional Features | 20%
We scored less common features like RBAC and risk exceptions, as well as integrations with continuous integration and deployment (CI/CD) and other tools.
- Criterion Winner: Holm Security
Ease of Use & Administration | 20%
We considered reviewers’ usability ratings; availability of knowledge bases, documentation, and training videos; and whether the product is available as a managed service.
- Criterion Winner: Rapid7
Customer Support | 15%
We evaluated chat, email, and phone technical support as well as hours of availability.
- Criterion Winner: Qualys
Frequently Asked Questions (FAQs)
What Is the Difference Between Vulnerability Scanning & Vulnerability Management?
Vulnerability management is broader than vulnerability scanning. It’s not just scanning assets and networks but also helping security teams remediate vulnerabilities and improve their overall security posture. Vulnerability management should help your business create a map of sorts to locate common weaknesses in your security infrastructure and make lasting improvements.
What Is the Difference Between Risk Management & Vulnerability Management?
Risk management is a broader enterprise category because it covers all aspects of business risk, including security vulnerabilities but also financial risks and events like natural disasters. A risk management plan should include planning for cybersecurity risks, which may include a vulnerability management strategy.
What Is an Example of a Vulnerability Management KPI?
Vulnerability management key performance indicators (KPI) should be easily measurable metrics that your team aims to hit, such as a specific length of time between a vulnerability being observed and being remediated. The more detailed your KPIs are, the more easily your security team can decide whether your vulnerability management strategy is working and whether it needs to be changed.
Read about creating a vulnerability management policy, including policy best practices, required sections for a policy, and a free policy template.
Bottom Line: Vulnerability Management Is Critical for Security
There are roughly 20,000 new vulnerabilities discovered each year — and many of them are zero-day vulnerabilities that aren’t discovered until they’ve been used in a cyberattack. Plugging those holes takes a lot of time and dedication even for the most secure companies and networks. For everyone else, they need all the help they can get from vulnerability management tools and services.
To find the right vulnerability management tool for your organization, take advantage of any demos or free trials that vendors offer and choose a product that suits your security and IT teams’ expertise. The right VM tool’s ability to prioritize fixes should help your team focus on the vulnerabilities that are most likely to impact your organization.
If your business is considering a managed VM service, read Vulnerability Management as a Service: Ultimate Guide next. This guide covers the top managed VM providers and major steps of the VMaaS process.











