A CISA advisory warns that the Daixin Team ransomware group has put the US healthcare system in its crosshairs for data extortion, and provides tools to fight back.
Daixin Team has actively targeted the US Healthcare and Public Health (HPH) sector since last June, according to a joint advisory issued by the FBI, Cybersecurity and Infrastructure Agency (CISA), and the Department of Health and Human Services (HHS), which provides indicators of compromise (IoCs) and tactics techniques and procedures (TTPs).
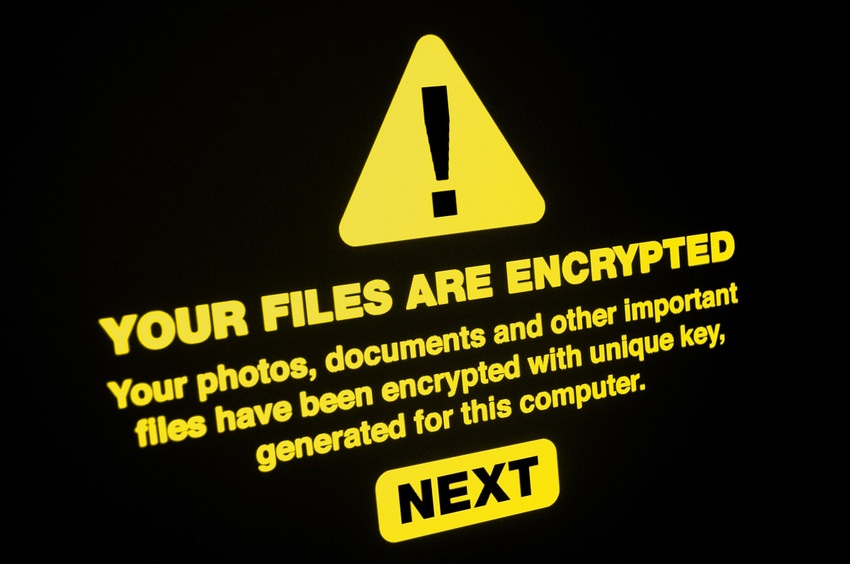
Third-party investigations revealed that the Daixin Team ransomware is based on Babuk Locker source code, targets VMware EXSi servers and encrypts files, the advisory said.
Officials believe the Daixin Team uses phishing campaigns to steal VPN credentials, and exploits.
"Daixin actors gain initial access to victims through virtual private network (VPN) servers. In one confirmed compromise, the actors likely exploited an unpatched vulnerability in the organization’s VPN server," the advisory explained. "In another confirmed compromise, the actors used previously compromised credentials to access a legacy VPN server that did not have multifactor authentication (MFA) enabled."
The FBI reported that as of October, the HPH sector makes up a full 25% of ransomware complaints filed to its Internet Crime Complaint Center, and accounted for the most overall ransomware reports during 2021.
About the Author(s)
You May Also Like
Securing Code in the Age of AI
April 24, 2024Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




