‘Predator’ — Nasty Android Spyware Revealed
Security Boulevard
MAY 30, 2023
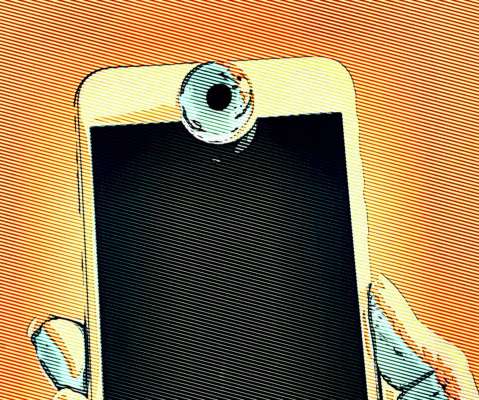
Intellexa mercenary spyware chains five unpatched bugs—plus ‘Alien’ technology The post ‘Predator’ — Nasty Android Spyware Revealed appeared first on Security Boulevard.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Security Boulevard
MAY 30, 2023
Intellexa mercenary spyware chains five unpatched bugs—plus ‘Alien’ technology The post ‘Predator’ — Nasty Android Spyware Revealed appeared first on Security Boulevard.
Security Boulevard
JUNE 22, 2022
It could be via virus malware, phishing, social engineering, fileless malware, etc. So, we’re here to talk about one such common tactic: Spyware. What is spyware and how does it work? The post What is Spyware and How to Protect Against it? The post What is Spyware and How to Protect Against it?
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Security Boulevard
SEPTEMBER 25, 2023
The post More iOS Zero Days, More Mercenary Spyware — This Time: Cytrox Predator appeared first on Security Boulevard. Apple Scrambled to Fix 3 More CVEs: Egyptian opposition presidential candidate Ahmed Eltantawy targeted “by the government.
Security Affairs
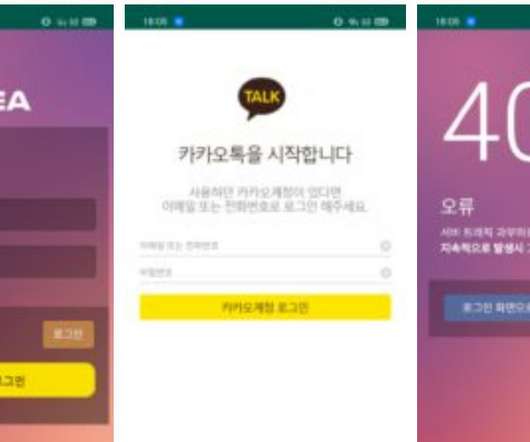
NOVEMBER 10, 2021
South Korean users have been targeted with a new sophisticated Android spyware, tracked as PhoneSpy, as part of an ongoing campaign. Researchers from Zimperium zLabs uncovered an ongoing campaign aimed at infecting the mobile phones of South Korean users with new sophisticated android spyware dubbed PhoneSpy. Zimperium concludes.

Security Boulevard
JUNE 28, 2023
The post Ironic: LetMeSpy Spyware Hackers Were Hacked (by Hackers) appeared first on Security Boulevard. Content warning: Abuse, stalking, controlling behavior, Schadenfreude, irony, doxxing.

Security Boulevard
JULY 29, 2022
The post Solved: Subzero Spyware Secret — Austrian Firm Fingered appeared first on Security Boulevard. DSIRF GmbH codenamed ‘Knotweed’ by Microsoft and RiskIQ.
Malwarebytes
JUNE 29, 2022
Google’s Threat Analysis Group (TAG) has revealed a sophisticated spyware activity involving ISPs (internet service providers) aiding in downloading powerful commercial spyware onto users’ mobile devices. The spyware, dubbed Hermit, is reported to have government clients much like Pegasus.
Security Boulevard
JULY 19, 2023
Adds ‘Mercenary Spyware’ Firms to Ban List appeared first on Security Boulevard. European cousins Intellexa and Cytrox essentially banned by Commerce Dept. Predator/ALIEN not welcome in U.S. The post Biden Admin.
Security Boulevard
MARCH 3, 2021
Another reason is that social engineering lures may be expertly crafted by the attacker after they have been monitoring a victim’s activity for some time, resulting in more effective phishing campaigns with serious security implications. Continue reading Trojan Spyware and BEC Attacks at Sucuri Blog.

Security Boulevard
AUGUST 22, 2022
NSO, notorious producer of the Pegasus nation-state spyware, is struggling. The post NSO Group Fires CEO — and 100 Staff — in Spyware ‘Streamlining’ appeared first on Security Boulevard. So it’s dumped its CEO, Shalev Hulio, and around 100 employees.
Security Affairs
JANUARY 21, 2022
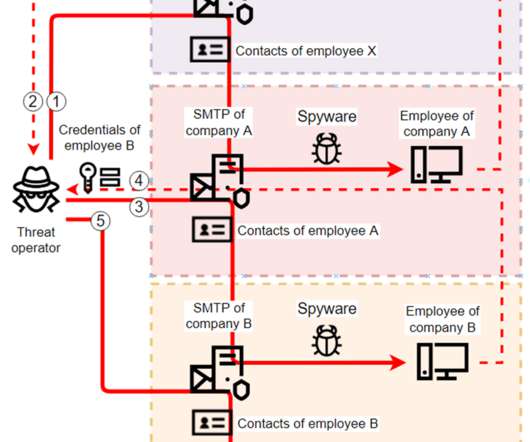
Researchers spotted several spyware campaigns targeting industrial enterprises to steal credentials and conduct financial fraud. Researchers from Kaspersky Lab have uncovered multiple spyware campaigns that target industrial firms to steal email account credentials and carry out fraudulent activities. ” concludes the report.
Security Boulevard
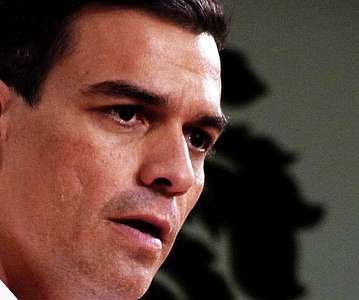
MAY 3, 2022
The notorious spyware, sold by NSO Group “only to governments,” caused large amounts of data to be exfiltrated. Hacked by NSO Pegasus Spyware (or was it?) The prime minister and the defense minister of Spain were infected with Pegasus. The post Spanish Govt. appeared first on Security Boulevard.
Security Affairs
NOVEMBER 26, 2021
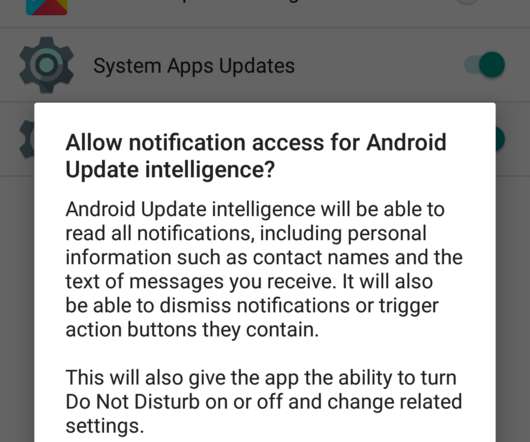
A threat actor, tracked as APT C-23, is using new powerful Android spyware in attacks aimed at targets in the Middle East. The APT C-23 cyberespionage group (also known as GnatSpy, FrozenCell, or VAMP) continues to target entities in the Middle East with enhanced Android spyware masqueraded as seemingly harmless app updates (i.e.

WIRED Threat Level
APRIL 21, 2021
The groups used social engineering techniques on Facebook to direct targets to a wide range of malware, including custom tools.

Hacker's King
MAY 20, 2023
However, if hackers gain access to these tokens through social engineering, phishing attacks, or other means, they can bypass 2FA by directly entering the codes, granting them unauthorized access. Social Engineering: Guarding Against Manipulation Social engineering remains a potent tool in hackers’ arsenal.

The Hacker News
FEBRUARY 2, 2021
Typically spread through social engineering lures, the Windows spyware not only now targets Microsoft's Antimalware Scan Interface (AMSI) in an attempt to defeat endpoint protection software, it also employs a
Security Affairs
APRIL 14, 2024
Crooks manipulate GitHub’s search results to distribute malware BatBadBut flaw allowed an attacker to perform command injection on Windows Roku disclosed a new security breach impacting 576,000 accounts LastPass employee targeted via an audio deepfake call TA547 targets German organizations with Rhadamanthys malware CISA adds D-Link multiple (..)

Security Boulevard
JUNE 23, 2023
Vulns unpatched for FOUR years: ‘Triangulation’ spyware said to use backdoor Apple gave to NSA. The post Apple Fixes 0-Days — Russia Says US Used for Spying appeared first on Security Boulevard.

Malwarebytes
JANUARY 25, 2024
Reconnaissance and social engineering are specific fields where AI can be deployed. Currently only state sponsored groups, professional spyware vendors, and the large criminal operations have access to, and know how to use advanced AI tools to increase the effectivity of their attacks.

Security Affairs
JUNE 4, 2023
Xplain hack impacted the Swiss cantonal police and Fedpol Zyxel published guidance for protecting devices from ongoing attacks Kimsuky APT poses as journalists and broadcast writers in its attacks New Linux Ransomware BlackSuit is similar to Royal ransomware CISA adds Progress MOVEit Transfer zero-day to its Known Exploited Vulnerabilities catalog (..)
CyberSecurity Insiders
MARCH 16, 2023
But after the spread of the Covid-19 pandemic, the focus of hackers has shifted more towards the smart phones with more phishing and social engineering attacks recorded in a 2nd quarter of 2022. All these days, we have seen cyber criminals infiltrating networks and taking down computers.
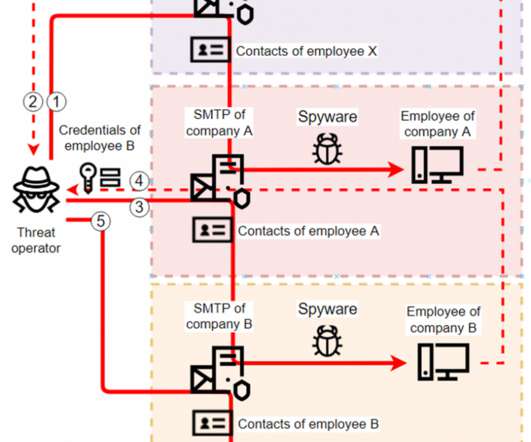
SecureList
JANUARY 19, 2022
Kaspersky ICS CERT has uncovered a number of spyware campaigns targeting industrial enterprises. The attackers use off-the-shelf spyware, but limit the scope and lifetime of each sample to the bare minimum. The attackers use off-the-shelf spyware, but limit the scope and lifetime of each sample to the bare minimum.

SecureWorld News
JULY 11, 2022
The Cybersecurity and Infrastructure Security Agency (CISA) issued a warning in April that the group was targeting cryptocurrency and blockchain companies and that it was using social engineering schemes to gain access to the victim's network. The employee who fell for the social engineering scheme no longer works for Sky Mavis.

Malwarebytes
AUGUST 26, 2021
Researchers from Citizen Lab, an academic research and development lab based in the University of Toronto in Canada, has recently discovered that an exploit affecting iMessage is being used to target Bahraini activists with the Pegasus spyware. The attackers just deploy the exploit. No need for the target to click something.

Security Boulevard
JULY 20, 2021
Yet another zero-day bug in iOS has allowed notorious spyware vendor NSO Group to break into the iPhones of journalists and activists. The post Apple’s Insecure iPhone Lets NSO Hack Journalists (Again) appeared first on Security Boulevard.
Security Affairs
JUNE 11, 2023
Gox exchange and operating BTC-e Japanese Pharmaceutical giant Eisai hit by a ransomware attack Clop ransomware gang was testing MOVEit Transfer bug since 2021 Stealth Soldier backdoor used is targeted espionage attacks in Libya Researchers published PoC exploit code for actively exploited Windows elevation of privilege issue Experts detail a new Kimsuky (..)
Security Affairs
SEPTEMBER 3, 2023
Enjoy a new round of the weekly SecurityAffairs newsletter, including the international press.
eSecurity Planet
FEBRUARY 22, 2022
There is no need for social engineering , as the program can implant backdoors directly without forced consent. NSO Group’s Pegasus software has been routinely in the headlines in recent years for using zero-click attacks to install its spyware. Spyware and Zero-Days: A Troubling Market.
Security Affairs
AUGUST 12, 2020
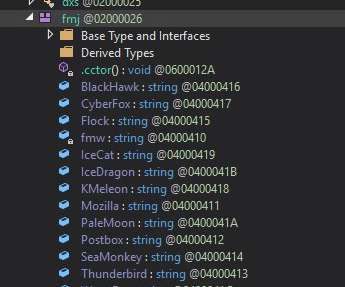
Agent Tesla is a spyware that is used to spy on the victims by collecting keystrokes, system clipboard, screenshots, and credentials from the infected system. To do this, the spyware creates different threads and timer functions in the main function. ” concludes the report that also includes indicators of compromise (IoCs).

ForAllSecure
APRIL 26, 2023
Common Types of Cyber Attacks Common techniques that criminal hackers use to penetrate systems include social engineering, password attacks, malware, and exploitation of software vulnerabilities. It uses psychological manipulation to trick users into making security mistakes or giving away sensitive information.”

Security Affairs
MARCH 25, 2021
Facebook researchers also reported that attackers also targeted iOS devices belonging to Uyghur targets with spyware like PoisonCarp or INSOMNIA. .” The group used the now terminated accounts to send links to the victims that point to malicious websites set up to conduct watering hole attacks.

Security Affairs
NOVEMBER 15, 2023
Admins’ notes on users present in leaked logs may also help malicious actors build a profile and better target users through spearphishing or other social engineering attacks. Notes on users, submitted by admins and customer support agents.

Hot for Security
JUNE 15, 2021
Given the portability and myriad of functionalities, mobile devices are highly susceptible to cyber threats, including malware, spyware and phishing attempts that may compromise that precious piece of tech we keep in our pocket and any information stored on it. Threat actors know that users often behave recklessly with their smart devices.

SecureWorld News
MARCH 29, 2024
This ends up executing sketchy code that installs viruses, ransomware, spyware, or adware behind the victim's back. A mix of social engineering, hacking, and abuse of legitimate services makes this style of online crime incredibly effective. However, that seems to be a misconception because these cyberattacks often overlap.

SecureList
JANUARY 18, 2023
The threat landscape is constantly updated through new malware and spyware, advanced phishing methods, and new social engineering techniques. In addition, the likelihood of the data being used for phishing and social engineering increases. . Kaspersky detects an average of 400,000 malicious files every day.

Identity IQ
MAY 7, 2021
Social Engineering: Cybercriminals are increasingly using sophisticated social engineering tools to trick people into revealing their login credentials. Spyware can be loaded onto your machine to log all your keystrokes. This includes bulk collections of details stolen in data breaches.

SecureWorld News
JULY 27, 2023
Mike Parkin, Senior Technical Engineer at Vulcan Cyber, said: "There's no doubt we're seeing more information stealing malware, but there's been an uptick in cybercriminal activity overall. It's always hard to predict how malware will evolve over time, however, it's a safe bet that attacks on the users themselves will remain a priority.

BH Consulting
OCTOBER 6, 2022
Social engineering techniques, such as phishing, target not the systems but the people using them. After all, it’s called social engineering for a reason. spyware, ransomware).”. The Health Service Executive is warning of fake contact tracing calls. They bypass rational arguments and appeal to our instincts.
Security Affairs
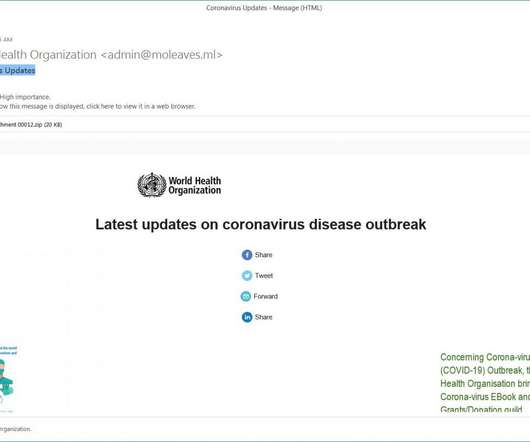
MARCH 8, 2020
FormBook data-stealing malware was used with cyber espionage purposes, like other spyware it is capable of extracting data from HTTP sessions, keystroke logging, stealing clipboard contents. See Using Caution with Email Attachments and Avoiding Social Engineering and Phishing Scams for more information.

Malwarebytes
JULY 16, 2021
General awareness of common social engineering techniques will also help steer you away from panic-based decisions. Pressure to make decisions right away “or else” are also a major red flag. Ad blockers will help reduce the possibility of redirects to scareware and malvertising from bad ads. Double win!
Malwarebytes
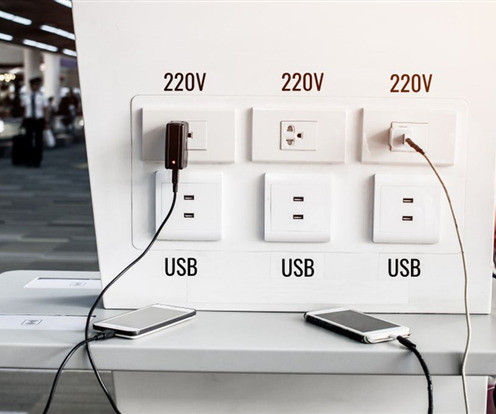
APRIL 11, 2023
Instead, hackers know that our mobile devices store a lot of PII, which can be sold on the dark web for profit or re-used in social engineering campaigns. There are many categories of malware that cybercriminals could install through juice jacking, including adware, cryptominers, ransomware, spyware, or Trojans.

Security Affairs
NOVEMBER 25, 2020
Business Email Compromise (BEC) is a type of email phishing attack that relies on social engineering. Group-IB researchers note that the cybercriminals behind these BEC operations rely exclusively on a variety of publicly available Spyware and Remote Access Trojans (RATs), such as AgentTesla , Loky, AzoRult , Pony, NetWire , etc.

Identity IQ
FEBRUARY 18, 2021
The following vectors represent some of the most common ways a criminal could gain access to your accounts and is also known as an account takeover : Social Engineering. This involves manipulating individuals into sharing confidential information that can be used for fraudulent purposes. A common example is phishing.

Malwarebytes
JUNE 7, 2021
Malicious hackers might use tools like computer viruses, spyware, ransomware, Trojan horses, and more to further their goals. Lastly, be on guard for phishing and social engineering attacks that try to trick you into doing something that’s bad for you, like downloading malware or giving out sensitive information.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content