Where Next for Quantum Computing and Cybersecurity?
Lohrman on Security
JULY 3, 2022
We’ve been hearing about upcoming breakthroughs with quantum computing technology for several years, so what’s the latest from around the world
Lohrman on Security
JULY 3, 2022
We’ve been hearing about upcoming breakthroughs with quantum computing technology for several years, so what’s the latest from around the world

Schneier on Security
JUNE 28, 2022
Thought experiment story of someone of someone who lost everything in a house fire, and now can’t log into anything: But to get into my cloud, I need my password and 2FA.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Lohrman on Security
JUNE 27, 2022
State and local governments need to prepare and respond to a new round of cyber attacks coming from groups claiming to be protesting the Supreme Court overturning Roe v. Wade last Friday

Daniel Miessler
JUNE 28, 2022
It’s common to hear that it’s hard to get into cybersecurity, and that this is a problem. That seems to be true, but it’s informative to ask a simple follow-up: The current cybersecurity jobs gap sits at around 2.7 million people. A problem for who?

Speaker: Karl Camilleri, Cloud Services Product Manager at phoenixNAP
Through a detailed analysis of major attacks and their consequences, Karl Camilleri, Cloud Services Product Manager at phoenixNAP, will discuss the state of ransomware and future predictions, as well as provide best practices for attack prevention and recovery.
Krebs on Security
JUNE 28, 2022
On December 7, 2021, Google announced it was suing two Russian men allegedly responsible for operating the Glupteba botnet, a global malware menace that has infected millions of computers over the past decade.

Troy Hunt
JULY 2, 2022
In a complete departure from the norm, this week's video is the much-requested "cultural differences" one with Charlotte. No tech (other than my occasional plug for the virtues of JavaScript), but lots of experiences from both of us living and working in different parts of the world.
Cyber Security Informer brings together the best content for cyber security professionals from the widest variety of industry thought leaders.
Joseph Steinberg
JUNE 30, 2022
Nearly a decade ago, well before most people had first heard the term “fake news,” I wrote a piece for Forbes unlike any other piece I had ever written before. Since then, I have seen many Internet memes circulate that appear to convey a similar message.

The Last Watchdog
JULY 1, 2022
The pandemic-driven remote working brought about unforeseen challenges that the pre-pandemic corporate world would have never imagined. From transitioning to a work-from-home as a ‘perk’ to a ‘necessity’, the organizations had to realign their operations and do it fast, to keep the ships afloat. Related: Deploying human sensors. Now that the dust seems to have settled on the novelty of remote working, there’s no doubt that remote working- whether organizations like it or not is here to say.
Security Boulevard
JUNE 27, 2022
Myths of Cyber Security : We work online. We live online. As our fast-paced lives get exponentially dependent on digital services, the urgency to protect our information from being misused is crucial. In 2021, Microsoft went down in flames of […].

Schneier on Security
JUNE 30, 2022
Wired is reporting on a new remote-access Trojan that is able to infect at least eighty different targets: So far, researchers from Lumen Technologies’ Black Lotus Labs say they’ve identified at least 80 targets infected by the stealthy malware, including routers made by Cisco, Netgear, Asus, and DrayTek.

Speaker: Ronald Eddings, Cybersecurity Expert and Podcaster
In this webinar, Ronald Eddings, Cybersecurity Expert, will outline the relationship between SaaS apps and IT & security teams, along with several actionable solutions to overcome the new difficulties facing your organization.

Dark Reading
JUNE 28, 2022
The clever, interactive phishing campaign is a sign of increasingly complex social-engineering attacks, researchers warn

Security Affairs
JUNE 28, 2022
Expert discovered a remote memory-corruption vulnerability affecting the latest version of the OpenSSL library. Security expert Guido Vranken discovered a remote memory-corruption vulnerability in the recently released OpenSSL version 3.0.4.

The Last Watchdog
JUNE 28, 2022
Virtual Private Networks – VPNs – remain widely used in enterprise settings. Don’t expect them to disappear anytime soon. This is so, despite the fact that the fundamental design of a VPN runs diametrically opposed to zero trust security principles. I had the chance to visit with David Holmes, network security analyst at Forrester, to learn more about how this dichotomy is playing out as companies accelerate their transition to cloud-centric networking.
CyberSecurity Insiders
JUNE 26, 2022
A Michigan based American bank named Flagstar Bank has sent notification to almost all its customers about a data breach that took place in December last year.

Speaker: P. Andrew Sjogren, Sr. Product Marketing Manager at Very Good Security, Matt Doka, Co-Founder and CTO of Fivestars, and Steve Andrews, President & CEO of the Western Bankers Association
In this webinar, we have a great set of panelists who will take you through how Zero Data strategies can be used as part of a well-rounded compliance and security approach, and get you to market much sooner by also allowing for payment optimization. They’ll share how to grow your business faster and minimize costs for both security and compliance

Schneier on Security
JUNE 27, 2022
I did not attend WEIS this year , but Ross Anderson was there and liveblogged all the talks. Uncategorized conferences security conferences
Dark Reading
JUNE 28, 2022
Google Analytics has been found to be in violation of GDPR privacy laws by Italy — the third country to ban it

Security Affairs
JUNE 26, 2022
Russian threat actors may be behind the explosion at a liquefied natural gas plant in Texas, the incident took place on June 8. A Russian hacking group may be responsible for a cyber attack against a liquefied natural gas plant in Texas that led to its explosion on June 8.

The Last Watchdog
JUNE 27, 2022
Vulnerabilities in web applications are the leading cause of high-profile breaches. Related: Log4J’s big lesson. Log4j, a widely publicized zero day vulnerability, was first identified in late 2021, yet security teams are still racing to patch and protect their enterprise apps and services. This notorious incident highlights the security risks associated with open-source software, and the challenges of protecting web applications against zero day attacks.

Speaker: Mike Cramer, Director of HIPAA & Data Security at The Word & Brown Companies
Now that companies are slowly allowing employees to return to work at the office, it's time to re-evaluate your company’s posture towards privacy and security. Join Mike Cramer, Director of HIPAA & Data Security at The Word & Brown Companies, for a discussion that will focus on compliance and the types of privacy and security measures your company should be aware of, as well as tips and methods for implementing these measures.

IT Security Guru
JUNE 28, 2022
The past decade has seen cybersecurity barge its way into the mainstream.

Schneier on Security
JUNE 29, 2022
Someone hacked the Ecuadorian embassy in Moscow and found a document related to Ecuador’s 2013 efforts to bring Edward Snowden there. If you remember, Snowden was traveling from Hong Kong to somewhere when the US revoked his passport, stranding him in Russia.

The Hacker News
JUNE 28, 2022
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) this week moved to add a Linux vulnerability dubbed PwnKit to its Known Exploited Vulnerabilities Catalog, citing evidence of active exploitation.

Security Affairs
JUNE 28, 2022
The LockBit ransomware operators released LockBit 3.0 with important novelties, including a bug bounty program and Zcash payments. The Lockbit ransomware operation has released LockBit 3.0, which has important noveòties such as a bug bounty program, Zcash payment, and new extortion tactics.

We Live Security
JUNE 27, 2022
Here are some of the most common ways hackers can get hold of other people’s credit card data – and how you can keep yours safe. The post 5 ways cybercriminals steal credit card details appeared first on WeLiveSecurity. Cybercrime

Security Boulevard
JUNE 28, 2022
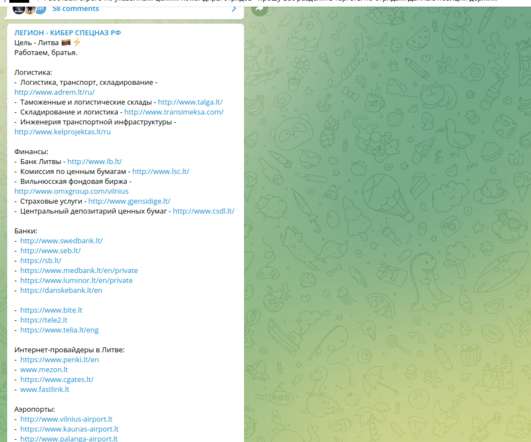
NATO member Lithuania is under attack from Russian hacking group Killnet. It raises serious concerns over Russia’s use of cyber warfare against NATO states. The post Russian Hackers Declare War on Lithuania — Killnet DDoS Panic appeared first on Security Boulevard.

Tech Republic Security
JUNE 28, 2022
A new report reveals that blockchain is neither decentralized nor updated. The post Pentagon finds concerning vulnerabilities on blockchain appeared first on TechRepublic. Big Data Security

CyberSecurity Insiders
JUNE 26, 2022
All these days, we have seen companies sharing their cyber attack experiences and intelligence with government and monitoring groups. But now, here’s a new platform where victims like businesses, activists and institutions can directly speak or share their digital assault experiences with the world.
Security Affairs
JUNE 27, 2022
The Ukrainian CERT-UA warns of attacks against Ukrainian telecommunications operators involving the DarkCrystal RAT. The Governmental Computer Emergency Response Team of Ukraine (CERT-UA) is warning of a malware campaign targeting Ukrainian telecommunications operators with the DarkCrystal RAT.
Cisco CSR
JUNE 28, 2022
Cisco Talos has a long-standing relationship with Ukraine, so when Russia invaded the country earlier this year, things hit close to home.

Security Boulevard
JUNE 28, 2022
Man in the Middle (MitM) is a term used to describe a cyber-attack where the cybercriminal comes between with user and their application. In these attacks, a hacker will inject code to hijack the application to steal credentials or open a backdoor to their network.

Tech Republic Security
JUNE 28, 2022
Conti, Quantum and Mountlocker were all linked to having used the new piece of software to inject systems with ransomware. The post New Bumblebee malware loader increasingly adopted by cyber threat groups appeared first on TechRepublic. Security
Naked Security
JUNE 27, 2022
The crooks needed at least two private keys, each stored in two parts. but they got them anyway. Cryptocurrency Data loss crypto ether hack Harmony
Security Affairs
JUNE 27, 2022
Lithuania confirmed it had been hit by an “intense” cyberattack, after Vilnius imposed restrictions on the rail transit of certain goods to Kaliningrad.

Dark Reading
JULY 1, 2022
OpenSea warns users that they are likely to be targeted in phishing attacks after a vendor employee accessed and downloaded its email list
Let's personalize your content