Forrester: CISO Budgets Not Immune to Cuts
Security Boulevard
AUGUST 30, 2022
Still, a new report from Forrester Research warned that CISOs mustn’t. The post Forrester: CISO Budgets Not Immune to Cuts appeared first on Security Boulevard.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Security Boulevard
AUGUST 30, 2022
Still, a new report from Forrester Research warned that CISOs mustn’t. The post Forrester: CISO Budgets Not Immune to Cuts appeared first on Security Boulevard.

CSO Magazine
MARCH 28, 2023
As the role of the CISO continues to grow in importance and gain more responsibility, many cybersecurity practitioners may wonder if they have what it takes to be successful in the role. Technical expertise and experience are obviously huge assets. They know how to make quick decisions and drive change in the organization.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

The Last Watchdog
OCTOBER 23, 2023
Splunk’s inability to migrate to a modern cloud-native architecture makes it difficult to take advantage of these cost-saving benefits or implement advanced data science use cases critical for threat detection. Influxes of data ingestion and the flat architecture of data lakes have led to difficulties in extracting value from repositories.

CyberSecurity Insiders
JUNE 11, 2023
Zero Trust is a cybersecurity framework that can greatly support Chief Information Security Officers (CISOs) and Chief Technology Officers (CTOs) in their roles of securing organizational systems and data. Simplified Compliance: Compliance with industry regulations and data protection laws is a significant concern for CISOs and CTOs.
Notice Bored
AUGUST 5, 2022
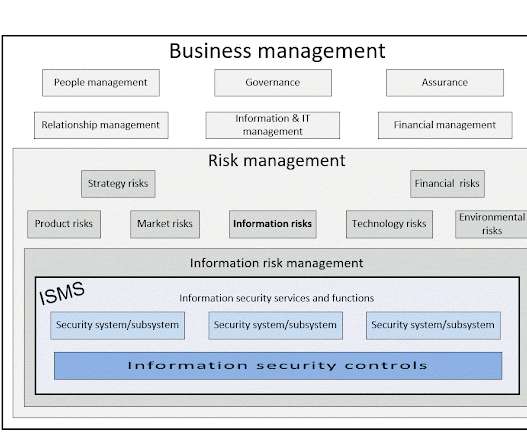
The title ' CISO Workshop: Security Program and Strategy ' with ' Your Name Here ' suggests it might be a template for use in a workshop/course bringing CISOs up to speed on the governance, strategic and architectural aspects of information security, but in fact given the amount of technical detail, it appears to be aimed at informing IT/technology (..)

SecureWorld News
OCTOBER 5, 2023
Michael Gregg, the CISO for the State of North Dakota, speaks across the country, including keynoting at SecureWorld Detroit on Sep. A recent blog by Frank Domizio titled " The CISO Role: Beyond Technology " explores exactly what I am talking about. That's a soft skill that even the most adept CISOs are still trying to master.

Jane Frankland
OCTOBER 31, 2023
However, new research from e2e-assure has revealed that few organisations are taking full advantage of security technologies available today. Having surveyed over 500 CISOs and ITDMs responsible for cybersecurity on the challenges faced with SOCs, their insights are not to be missed. You know about tech complexities and optimisation.
NetSpi Executives
FEBRUARY 21, 2024
Like many technologies that came before it, AI is advancing faster than security standards can keep up with. For a comprehensive view of security in ML models, access our white paper, “ The CISO’s Guide to Securing AI/ML Models.” How transparent is the model architecture?
Security Boulevard
JANUARY 9, 2024
Many next-generation technologies became deployed parallel to existing solutions, including zero-trust architecture ( ZTNA ), extended detection and response ( XDR ), and cloud-based multi-factor authentication. Assessing Duplication of Security Controls. Importance of Assessing Duplication of Security Controls.

CyberSecurity Insiders
OCTOBER 7, 2021
. & HYDERABAD, India–( BUSINESS WIRE )–Analytics Insight has named ‘ The 10 Most Influential CISOs to Watch in 2021 ’ in its October magazine issue. The magazine issue recognizes ten futuristic CISOs who are reimagining the business world and adopting new ways of working. He holds a Ph.D

CyberSecurity Insiders
FEBRUARY 28, 2023
John Masserini, of Tag Cyber, will explore practical approaches to advancing zero trust along with his fellow panelists: Kevin Dana, VP of Information Technology for World Wide Technology; Marcos Christodonte II, Global CISO for CDW; and Allen Jeter, Director of IT for Chainalysis.

SC Magazine
MAY 18, 2021
A visitor photographs a symbol of a cloud at the Deutsche Telekom stand the day before the CeBIT technology trade fair. It’s about how you can do your business mission” in a different environment, with its own requirements for protecting data, Vickers said during his talk at the RSA Show’s Cloud Security Alliance CISO Summit.

SC Magazine
APRIL 30, 2021
We’ve been trying to do that for years and as new technologies come into play, that modernization and optimization is critically important. That includes the architectures, the computing platforms, the algorithms and the people and the process as well. In 1988 we had the Morris Worm , if you remember from the history books. I lived it.
Cisco Security
JANUARY 12, 2022
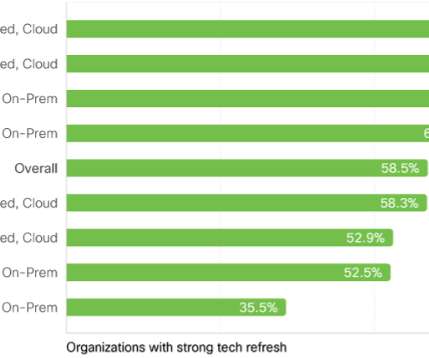
One of the five main findings in our newly published Security Outcomes Study, Volume 2 , was the clear benefit in having a proactive strategy of refreshing business-critical technologies. How often should a technology refresh take place? As you could guess, this level of technology debt is a drag on security teams.

IT Security Guru
SEPTEMBER 25, 2023
The IT Security Guru caught up with Tarnveer Singh a CISO and finalist in the Security Serious Unsung Heroes Awards 2023 for his thoughts on how to get more professionals involved in the cybersecurity industry: There are many ways we can inspire new cybersecurity professionals to join our industry. We must reduce barriers to entry.

SC Magazine
FEBRUARY 11, 2021
The new partnership with Silicon Valley CISO Investments will include an additional $250,000, but perhaps more importantly, support and guidance from the more than 55 practicing chief information security officers that make up SVCI. The post Startup Traceable turns to CISO investors for next phase of growth appeared first on SC Media.

The Last Watchdog
JANUARY 8, 2023
Business initiatives demand faster, more efficient outcomes and technology responds. When it comes down to it, C-level goals and CISO initiatives are not all that misaligned. The complexity that has abounded in the past few years has left us more connected and data-driven than ever before. Managed solutions can help.

Cisco Security
JULY 21, 2021
Today, the Cisco Investments team released their 2021 CISO Survival Guide to Emerging Trends in the Startup Ecosystem. There is a wealth of insightful information for CISOs in this report. Because Zero Trust and XDR are integrated architectural outcomes, the majority of CISOs are anchoring their SASE strategies here.
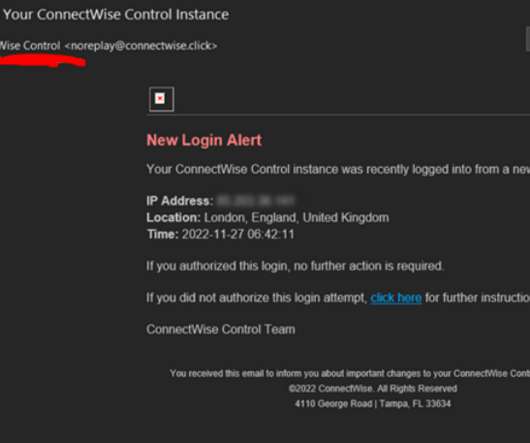
Krebs on Security
DECEMBER 1, 2022
ConnectWise’s warnings come amid breach reports from another major provider of remote support technologies: GoTo disclosed on Nov. ” However, LastPass maintains that its “customer passwords remain safely encrypted due to LastPass’s Zero Knowledge architecture.” Update, 7:25 p.m.

The Last Watchdog
AUGUST 1, 2023
“Nile is in a strong position to take advantage of several paradigm shifts occurring across the technology ecosystem,” said Pankaj Patel, CEO and co-founder of Nile. ” In the era of rapid transformation, CIOs and CISOs are increasingly concerned about the integrity of their business data and digital assets.

NetSpi Executives
FEBRUARY 21, 2024
Like many technologies that came before it, AI is advancing faster than security standards can keep up with. For a comprehensive view of security in ML models, access our white paper, “ The CISO’s Guide to Securing AI/ML Models.” How transparent is the model architecture?

McAfee
NOVEMBER 3, 2020
Forrester also predicts that the number of women CISOs at Fortune 500 companies will rise to 20 percent in 2019 , compared with 13 percent in 2017. During her first few years at Booz Allen, she supported technology, innovation and risk analysis initiatives across U.S. in Communication, Culture and Technology from Georgetown University.

NopSec
SEPTEMBER 23, 2022
Lisa has a passion for connecting business with technology and thrives in transforming disruptive technology into leading solutions. In this episode, Lisa talks with Tim Brown, the CISO at SolarWinds. Tim drives the creation, architecture, strategy, and external visibility for products and solutions.

Security Boulevard
SEPTEMBER 19, 2022
The cost of sunsetting security products, legacy applications, and legacy technology imposes a financial strain on every organization. Before considering sunsetting technology products, most SecOps and DevOps teams focus on evaluating and updating, if possible, legacy processes, including developing a legacy-system modernization workflow.

CyberSecurity Insiders
JANUARY 17, 2022
By Tyler Farrar, CISO, Exabeam. In almost every case, technology has played a vital role in facilitating and supporting these changes. It makes sense that security budgets should follow to help protect these increasingly diverse and flexible architectures. Unfortunately, so were cyber adversaries. Leaving The Legacy.

SecureWorld News
SEPTEMBER 7, 2023
As for the panel presentation at SecureWorld Denver , it features Edgar Acosta, Experienced Cybersecurity Professional (former CISO at DCP Midstream ); Craig Hurter, Sr. Director of Information Security, State of Colorado Governor's Office of Information Technology; and Toby Zimmerer, Sr. Demand and Delivery Director, Optiv.

McAfee
JULY 1, 2020
Hybrid and multi-cloud architectures can offer government agencies the flexibility, enhanced security and capacity needed to achieve what they need for modernizing now and into the future. Yet many questions remain surrounding the implementation of multi- and hybrid-cloud architectures.

CyberSecurity Insiders
NOVEMBER 8, 2021
As organizations strive for excellence in digital transformation and face the realities of an accelerated push to remote work, they’ve been called to rethink their networking and cybersecurity architecture. SASE helps future-proof cybersecurity architecture by decoupling security control from the data center.

SecureWorld News
APRIL 8, 2021
And the developers say this chip could end the "patch and pray" strategy that keeps security teams running in circles and lower the stress level of CISOs in the process. Undefined semantics are nooks and crannies of the computing architecture—for example the location, format, and content of program code.

SC Magazine
MAY 19, 2021
With its tailored controls, micro-perimeters and trust-nothing approach to access, Zero Trust gives CISOs confidence that their security program can secure their remote workforce and meet regulatory compliance requirements. Thanks to a rapid shift to remote work, Zero Trust is finally garnering the attention it deserves. What is Zero Trust?
Security Boulevard
APRIL 12, 2022
CISOs know technology change is constant and never-ending – just like taxes. In fact, if you look back in history, technology began its evolution well before taxes. Like taxes, technology change can cause FUD – fear, uncertainty, and doubt. Why can’t zero trust architecture protect my APIs? You never know.

McAfee
AUGUST 23, 2021
Now that we’ve officially kicked off our journey as McAfee Enterprise , a pure-play enterprise cybersecurity company under the new ownership of Symphony Technology Group (STG), we’re celebrating a lot of new firsts and changes. I found that I had a passion for information security and have been the CISO at two different Fortune 500 companies.

ForAllSecure
APRIL 3, 2019
This doesn’t allow the IT administrator, the end-user, or the CISO to independently verify the security, safety, and resiliency of the software they buy and use. That’s true today because we do not have the right technology. We began our research in a university lab, where a brand new technology was born.

Security Boulevard
SEPTEMBER 9, 2022
But hiring a full-time chief information security officer (CISO) is not always possible for organizations – nor is it always needed. Read on to learn why you might want to consider a virtual CISO (vCISO), and the benefits that come with that decision. As we mentioned, hiring a full-time CISO is not always possible – or necessary.

SecureWorld News
OCTOBER 19, 2023
I think it requires taking a step back and assessing what you can do with less," said Chris Roberts, CISO and Senior Director at Boom Supersonic. Too many folks focus on the technology as opposed to the people or process. Andrew Smeaton, CISO at Afiniti, says reassessment of cybersecurity programs and plans is necessary.

Duo's Security Blog
OCTOBER 25, 2022
Tired: Zero Trust is a Journey Wired: Zero Trust is a Transformation Inspired: Zero Trust is About Relationships So many CIOs and CISOs I engage with are over it. Adopting a zero-trust architecture across your enterprise is transformational. It requires a change in mindset, not just in toolset. Integrations drive zero trust maturity.

CyberSecurity Insiders
JANUARY 5, 2022
SAN FRANCISCO–( BUSINESS WIRE )–Tetrate, the leading company providing a zero-trust application connectivity platform, announced their third annual conference on Zero Trust Architecture (ZTA) and DevSecOps for Cloud Native Applications in partnership with the U.S. security standards for a distributed architecture: About Tetrate.

The Last Watchdog
JULY 30, 2018
The painful impact of cyber attacks on businesses is worsening despite advances in technology aimed at protecting enterprises from malicious network traffic, insider threats, malware, denial of service attacks and phishing campaigns. This has left many CISOs questioning if today’s incumbent cybersecurity solutions are enough.

ForAllSecure
APRIL 3, 2019
This doesn’t allow the IT administrator, the end-user, or the CISO to independently verify the security, safety, and resiliency of the software they buy and use. That’s true today because we do not have the right technology. We began our research in a university lab, where a brand new technology was born.

ForAllSecure
APRIL 3, 2019
This doesn’t allow the IT administrator, the end-user, or the CISO to independently verify the security, safety, and resiliency of the software they buy and use. That’s true today because we do not have the right technology. We began our research in a university lab, where a brand new technology was born.

SecureWorld News
APRIL 7, 2021
There are a lot of lingering questions: What do organizations do to transform their infrastructure to where it needs to be from a technology standpoint? Sol Cates, Principal Technologist and Chief Technology Officer at Thales Group, explained why strategy and groundwork are essential to DX. We're going where the technology is going.

Security Boulevard
JANUARY 24, 2023
Fortifying Data Behind the Blockchain Technologies The Blockchain security model is a significant leap in the progress of transactional protection. Suppose individuals and organizations own the right their place their data anywhere within the decentralized realm along with holding the permissions.

The Last Watchdog
JULY 19, 2023
I had the chance to discuss this with Shinichi Yokohama, NTT Global CISO and John Petrie, Counselor to the NTT Global CISO, at RSA Conference 2023. Towards zero-trust So how should CISOs steer their organizations? the architecture must come first, and then they can decide which product choices they would prefer.”

SecureWorld News
JUNE 2, 2022
Glenn Kapetansky, Chief Security Officer and Technology Capability Lead for Trexin Consulting, has a passion for building systems, organizations, and teams, and has done so across a number of business sectors, technologies, and roles. Glenn's certifications and memberships include IEEE, (ISC)2 (CISSP), ISACA (CISA), and ITIL (SM).
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content