Most Popular Cybersecurity Blogs from 2023
Lohrman on Security
JANUARY 14, 2024
What were the top government technology and security blogs in 2023? The metrics tell us what cybersecurity and technology infrastructure topics were most popular.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Lohrman on Security
JANUARY 14, 2024
What were the top government technology and security blogs in 2023? The metrics tell us what cybersecurity and technology infrastructure topics were most popular.
Anton on Security
APRIL 11, 2024
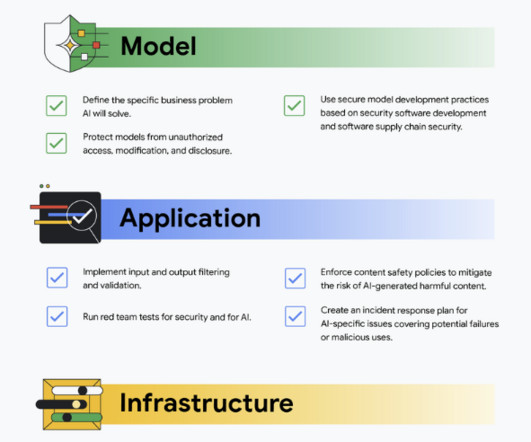
Recently our team has written several papers and blogs focused on securing AI. Here are 5 gen AI security terms busy business leaders should know” defines five key generative AI security terms that busy business leaders should understand to navigate the potential risks and benefits of this technology.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Lohrman on Security
JANUARY 15, 2023
What were the top government technology and security blogs in 2022? The metrics don’t lie, and they tell us what cybersecurity and technology infrastructure topics were most popular.

Security Boulevard
JANUARY 14, 2024
What were the top government technology and security blogs in 2023? The metrics tell us what cybersecurity and technology infrastructure topics were most popular. The post Most Popular Cybersecurity Blogs from 2023 appeared first on Security Boulevard.

Heimadal Security
JULY 12, 2023
Over the past couple of years, increasingly more sysadmins have abandoned the more “traditional”, hands-on, approach to access and identity management in favor of IAG (Identity and Access Governance).

Lohrman on Security
JANUARY 9, 2022
What were the top government security blog posts in 2021? These metrics tell us what cybersecurity and technology infrastructure topics were most popular in the past year.

Security Boulevard
APRIL 25, 2024
Gone are the days of delegating technology and cybersecurity concerns to be solved solely by. The post Why Zero Trust is a Must for Strong Corporate Governance appeared first on Entrust Blog. The post Why Zero Trust is a Must for Strong Corporate Governance appeared first on Security Boulevard.
Security Boulevard
APRIL 11, 2024
Recently our team has written several papers and blogs focused on securing AI. Here are 5 gen AI security terms busy business leaders should know” defines five key generative AI security terms that busy business leaders should understand to navigate the potential risks and benefits of this technology.

Schneier on Security
NOVEMBER 14, 2019
Technology is now deeply intertwined with policy. It's all changing fast; technology is literally creating the world we all live in, and policymakers can't keep up. Or, more specifically, where and how should government step in and regulate what is largely a market-driven industry? Today, it's a crisis.

Heimadal Security
JANUARY 4, 2023
Following a recent cyberattack on the Queensland University of Technology, the Royal ransomware gang has begun leaking data they allegedly stole during the intrusion. Queensland University of Technology (QUT) has 52,672 students and operates on a budget exceeding one billion Australian dollars.

Heimadal Security
MARCH 2, 2023
Starting March 1st, the Russian law ”On Information, Information Technologies and Information Protection” forbids state organizations to use foreign messenger platforms. This happened as a consequence of […] The post WhatsApp, Teams, and Telegram – Banned in Russian Government Organizations appeared first on Heimdal Security Blog.

Anton on Security
OCTOBER 21, 2020
From Google Cloud Blog: “Improving security, compliance, and governance with cloud-based DLP data discovery” So, I’ve been doing some blogging at Google Cloud blog with most posts connected to products, launches, etc. However, I am also doing a fun blog series on DLP in the cloud.
Security Affairs
MAY 31, 2022
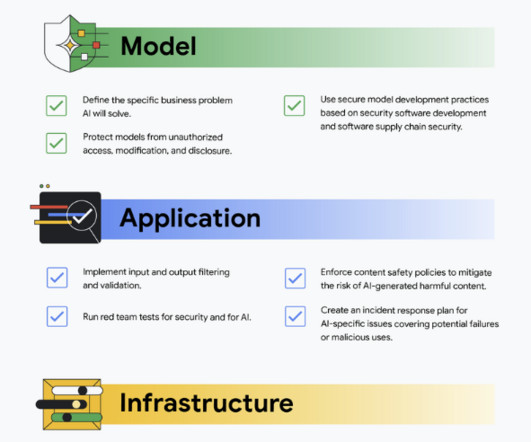
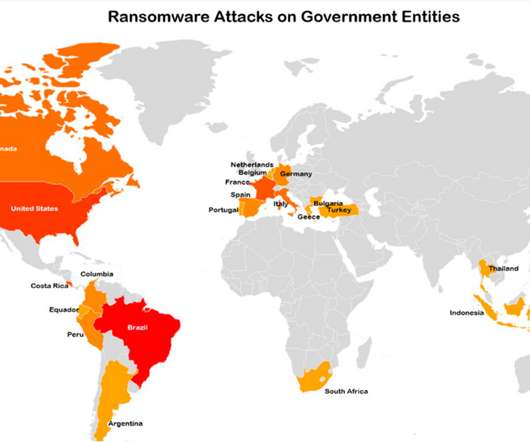
Cyber Research Labs observed a rise in ransomware attacks in the second quarter of 2022, some of them with a severe impact on the victims, such as the attack that hit the Costa Rican government that caused a nationwide crisis. The experts warn of ransomware attacks against government organizations. ” continues Cyble. .

Centraleyes
MARCH 6, 2024
Breakthroughs in machine learning, advanced computing, and cognitive reasoning are revolutionizing industries and reshaping how we envision the future of technology. We must remain aware of the ethical dimensions inherent in technological innovation.

Heimadal Security
MARCH 30, 2023
The use of technology to access health and care services and information is on the rise – over 40 million people now have […] The post The UK Government Shares New Strategy to Boost NHS Cybersecurity by 2030 appeared first on Heimdal Security Blog.

Schneier on Security
MARCH 8, 2019
Government Needs You : Travis Moore, TechCongress; Hashim Mteuzi, Senior Manager, Network Talent Initiative, Code for America; Gigi Sohn, Distinguished Fellow, Georgetown Law Institute for Technology, Law and Policy; and Ashkan Soltani, Independent Consultant. Here is my blog post about the event. Video here.). Video here.).

Security Boulevard
MARCH 21, 2024
Healthcare organizations increasingly rely on technology to store, manage, and transmit sensitive patient information. The post Safeguarding Patient Data with HITRUST Compliance: A Comprehensive Guide for Healthcare Technology Companies appeared first on Hyperproof.

Schneier on Security
APRIL 9, 2024
It was a serious attack by the Chinese government that accessed the emails of senior U.S. government officials. US Cyber Safety Review Board released a report on the summer 2023 hack of Microsoft Exchange by China. From the executive summary: The Board finds that this intrusion was preventable and should never have occurred.

Thales Cloud Protection & Licensing
NOVEMBER 27, 2023
How better key management can close cloud security gaps troubling US government (Part 1 of 2) sparsh Tue, 11/28/2023 - 05:20 Bruce Schneier recently blogged : A bunch of networks, including US Government networks , have been hacked by the Chinese. But “negligent security practices” are not a new concern for the US Government.

Cisco Security
APRIL 1, 2024
Blockchain technology has experienced remarkable adoption in recent years, driven by its use across a broad spectrum of institutions, governments, retail investors, and users. However, this surge in… Read more on Cisco Blogs Blockchain adoption and crypto investments are peaking, along with scams.

Heimadal Security
OCTOBER 21, 2021
The Bureau of Industry and Security (BIS) supports the US national security, foreign policy, and economic objectives by maintaining an effective export control and treaty compliance system and encouraging continuing US leadership in key technology. firms from […].
Security Boulevard
DECEMBER 20, 2021
Sometimes great old blog posts are hard to find (especially on Medium ) , so I decided to do a periodic list blog with my favorite posts of the past quarter or so. This covers both Anton on Security and my posts from Google Cloud blog , and our Cloud Security Podcast too ( subscribe ). Anton’s Security Blog Quarterly Q2 2021.

Security Affairs
MAY 24, 2023
The US Department of the Treasury’s Office of Foreign Assets Control (OFAC) announced sanctions against four entities and one individual for their role in malicious cyber operations conducted to support the government of North Korea. ” reads the announcement. “As a result of today’s action, pursuant to E.O. 13687 and E.O.

Thales Cloud Protection & Licensing
OCTOBER 25, 2018
In this blog post, I’ll discuss: Our current perimeter defense; The need to shift to a data-centric security approach; and, The need to educate the public to strengthen our critical infrastructure security posture. For more information about Thales eSecurity’s federal government security solutions, visit here.

Jane Frankland
APRIL 17, 2024
As technology weaves deeper into our lives, the swift exchange of information has become our reality. I invite you to join me on a journey to understand the intricacies of secure transactions in our digitised world, where trust and technological innovation converge for a safer, more resilient digital future.

Thales Cloud Protection & Licensing
APRIL 21, 2020
federal government contends with a tidal wave of demands in the COVID-19 battle, agencies are pushed to unprecedented limits. government is excelling with digital transformation (DX) which is critical in this time of crisis as the cloud becomes a crucial dynamic with the world working remotely. As the U.S. Some good news: the U.S.

Thales Cloud Protection & Licensing
JULY 3, 2019
With details from our report, I also highlighted how demand for modernization, mobile payments, IoT, cloud migration and cost savings is driving the push for new technologies while increasing opportunities for threats. The post The Changing Face of Data Security in Federal Government appeared first on Data Security Blog | Thales eSecurity.

Thales Cloud Protection & Licensing
SEPTEMBER 17, 2019
As government agencies get back to work after summer barbeques, family vacations and once-in-a-lifetime getaways, the focus is on the priorities for the rest of 2019. Cybersecurity remains one of the top concerns and priorities for our government. Quantum Computing is Coming-Is the Federal Government Ready? In fact, the U.S.

Security Boulevard
APRIL 29, 2024
The rise of digital technology has provided great convenience to the banking sector, but it has also opened up the doors to cyber attacks. The incident was mentioned in the Reserve Bank of India’s […] The post Ensuring RBI Compliance: Crucial Cybersecurity Measures to Protect Financial Standing appeared first on Kratikal Blogs.

Schneier on Security
DECEMBER 19, 2023
” Willison expands this in a blog post , which I strongly recommend reading in its entirety. A key role of government is to prevent this from happening. This isn’t helped by the fact that AI technology means the scope of what’s possible is changing at a rate that’s hard to appreciate even if you’re deeply aware of the space.

McAfee
JULY 1, 2020
Between January and April of this year, the government sector saw a 45% increase in enterprise cloud use, and as the work-from-home norm continues, socially distanced teamwork will require even more cloud-based collaboration services. Organizations have adopted various capabilities that have unique gaps that must be filled.

Anton on Security
DECEMBER 20, 2021
Sometimes great old blog posts are hard to find (especially on Medium ) , so I decided to do a periodic list blog with my favorite posts of the past quarter or so. This covers both Anton on Security and my posts from Google Cloud blog , and our Cloud Security Podcast too ( subscribe ). “A Here is the next one. Do They Matter?”

CyberSecurity Insiders
JUNE 30, 2023
Given this is a technology blog, we wanted to share some of the best tech-related podcasts out there right now. Published by MIT Technology Review, it has explored everything from digital twins, breakthroughs in AI and computing history, to how AI is helping test and train pilots.

McAfee
AUGUST 11, 2021
As outlined in Executive Order on Improving the Nation’s Cybersecurity (EO 14028), Section 3: Modernizing Federal Government Cybersecurity, CISA has been tasked with developing a Federal cloud-security strategy to aid agencies in the adoption of a Zero Trust Architecture to meet the EO Requirements.

The Last Watchdog
OCTOBER 3, 2022
Government policymakers decided in the 1990s to promote inherently insecure, nascent Internet technology to be the world’s primary global information infrastructure for all the world’s communications, content, and commerce. Government policymakers decided in the 1990s to de facto nationally abdicate governing online.

The Last Watchdog
MARCH 25, 2024
The National Institute of Standards and Technology (NIST) has updated their widely used Cybersecurity Framework (CSF) — a free respected landmark guidance document for reducing cybersecurity risk. It also introduces a new focus on governance, highlighting cybersecurity as a critical enterprise risk with many dependencies.
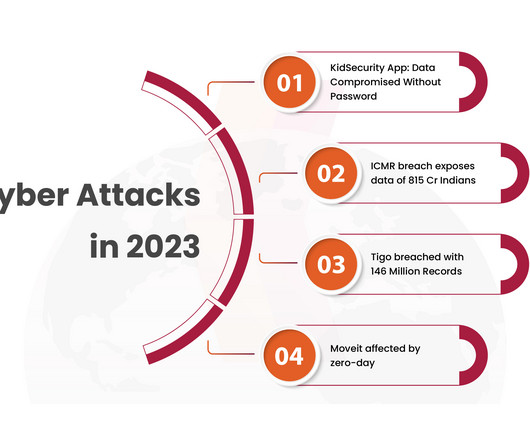
Security Boulevard
DECEMBER 18, 2023
They underscore a stark truth: no entity is immune – not even governments. Amidst unprecedented technological leaps forward, 2023 has […] The post Top 5 Cyber Attacks in 2023 appeared first on Kratikal Blogs. The number is more than figures; it reflects the deep-seated impact of cyber threats on the global economy.

Security Affairs
APRIL 26, 2023
German government warns that technology to regulate power consumption in Huawei network appliances could be used for sabotage purposes. government officials as well as European security authorities, which have warned of the risks associated with Chinese telecoms equipment.” In November 2019, the U.S.

The Last Watchdog
SEPTEMBER 25, 2023
Taking an active role Your cybersecurity policy should address your employees and technology systems. Taurins It’s also essential your business evaluates its technology and keeps it regularly updated to the latest security standards. Security places a crucial role in your technology. Employee training is crucial.

CyberSecurity Insiders
OCTOBER 1, 2021
This allows government organizations to fully leverage an increasingly remote and globally distributed workforce. The addition of PCoIP® technology, a highly secure no data transfer multi-codec display protocol, allows for the highest performance CPU or GPU throughput regardless of bandwidth, connection, or locale.

Security Boulevard
APRIL 10, 2024
In today’s fast-paced business landscape, integrating Artificial Intelligence (AI), particularly Generative AI, encompassing technologies like ChatGPT, Bard, and DALL-E 2, presents unprecedented opportunities and multifaceted risks.

Heimadal Security
JULY 20, 2023
The United Kingdom’s public sector is undergoing a digital transformation, relying increasingly on technology to enhance service delivery, streamline operations, and foster improved engagement with citizens.

Security Boulevard
JANUARY 27, 2023
Department of Health and Human Services (HHS) has issued clarification on obligations for HIPAA-covered entities and business associates (regulated entities) under the HIPAA Privacy, Security, and Breach Notification Rules (HIPAA Rules) when using online tracking technologies. By definition, tracking technologies are apps used to collect and.

The Last Watchdog
MARCH 20, 2023
As technology has rapidly exceeded all historical imaginings, opportunities for fraudsters to exploit their victims abound. Digital exploitation refers to the abuse and manipulation of technology and the internet for illegal and unethical purposes, including identity theft, sextortion, cyberbullying, online scams, and data breaches.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content