When cryptography attacks – how TLS helps malware hide in plain sight
Naked Security
APRIL 21, 2021
No IT technology feels quite as much of a double-edged sword as encryption.

Naked Security
APRIL 21, 2021
No IT technology feels quite as much of a double-edged sword as encryption.

Security Affairs
APRIL 22, 2021
The importance of carrying out a careful risk and impact assessment in order to safeguard the security of the information and the data privacy. In order to reduce as much as possible the vulnerabilities and programming errors that can affect not only the quality of the product itself but can also be exploited to launch increasingly sophisticated and growing computer attacks, it’s necessary to guarantee the protection parameters of computer security in terms of integrity, confidentiality and auth
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Daniel Miessler
APRIL 20, 2021
Casey Ellis (of Bugcrowd fame) had a great post on Twitter today about security terminology. Casey also added that Acceptable Risk would be being willing to get punched in the face. threat actor = someone who wants to punch you in the face threat = the punch being thrown vulnerability = your inability to defend against the punch risk = the likelihood of getting punched in the face — cje (@caseyjohnellis) April 19, 2021.

Schneier on Security
APRIL 21, 2021
Developers have discovered a backdoor in the Codecov bash uploader. It’s been there for four months. We don’t know who put it there. Codecov said the breach allowed the attackers to export information stored in its users’ continuous integration (CI) environments. This information was then sent to a third-party server outside of Codecov’s infrastructure,” the company warned.

Advertisement
How many people would you trust with your house keys? Chances are, you have a handful of trusted friends and family members who have an emergency copy, but you definitely wouldn’t hand those out too freely. You have stuff that’s worth protecting—and the more people that have access to your belongings, the higher the odds that something will go missing.
Troy Hunt
APRIL 17, 2021
Geez I'm glad the Facebook stuff was the week before this one! With that (mostly) out of the way, we headed off to Thredbo for a couple of days of mountain biking, hitting trails I've only ever snowboarded down before (yes, we get snow in Australia). Back to normality (I think we can start calling it that now), Rob and I did our book editing session, the Facebook scraping incident (let's stop calling it a "data breach") continued to consume time and in a case of very fortuitous timing, they're c

Tech Republic Security
APRIL 20, 2021
As the use of cryptocurrency increases, so does the risk of being a target for scammers. Tom Merritt offers five tips for defending against cryptocurrency scams.
Cyber Security Informer brings together the best content for cyber security professionals from the widest variety of industry thought leaders.

Schneier on Security
APRIL 20, 2021
On April 15, the Biden administration both formally attributed the SolarWinds espionage campaign to the Russian Foreign Intelligence Service (SVR), and imposed a series of sanctions designed to punish the country for the attack and deter future attacks. I will leave it to those with experience in foreign relations to convince me that the response is sufficient to deter future operations.

We Live Security
APRIL 20, 2021
The malware sends automated replies to messages on WhatsApp and other major chat apps. The post WhatsApp in pink? Watch out for this fake update appeared first on WeLiveSecurity.
Tech Republic Security
APRIL 20, 2021
A former pro baseball player and coach turned sports psychologist believes there is much cybersecurity pros can learn from sports mental conditioning. He wants to help them hit more home runs.

Bleeping Computer
APRIL 22, 2021
A Microsoft 365 outage is preventing Exchange Online users from sending and receiving emails, with messages being stuck in transit and not reaching the recipients' inboxes. [.].

Advertiser: Revenera
In a recent study, IDC found that 64% of organizations said they were already using open source in software development with a further 25% planning to in the next year. Most organizations are unaware of just how much open-source code is used and underestimate their dependency on it. As enterprises grow the use of open-source software, they face a new challenge: understanding the scope of open-source software that's being used throughout the organization and the corresponding exposure.

Schneier on Security
APRIL 19, 2021
The Washington Post has published a long story on the unlocking of the San Bernardino Terrorist’s iPhone 5C in 2016. We all thought it was an Israeli company called Cellebrite. It was actually an Australian company called Azimuth Security. Azimuth specialized in finding significant vulnerabilities. Dowd, a former IBM X-Force researcher whom one peer called “the Mozart of exploit design,” had found one in open-source code from Mozilla that Apple used to permit accessories to be

Trend Micro
APRIL 19, 2021
What happens in Carbanak and FIN7 attacks? Here are some techniques used by these financially motivated threat groups that target banks, retail stores, and other establishments.

Tech Republic Security
APRIL 23, 2021
Organizations are increasing investments in cybersecurity and their dependence on third parties—even in light of disruptions, according to PwC's Cyber Trust report.

Bleeping Computer
APRIL 23, 2021
Open-source software tools and Vault maker HashiCorp disclosed a security incident yesterday that occurred due to the recent Codecov attack. HashiCorp, a Codecov customer, has stated that the recent Codecov supply-chain attack aimed at collecting developer credentials led to the exposure of HashiCorp's GPG signing key. [.].

Advertisement
The healthcare industry has massively adopted web tracking tools, including pixels and trackers. Tracking tools on user-authenticated and unauthenticated web pages can access personal health information (PHI) such as IP addresses, medical record numbers, home and email addresses, appointment dates, or other info provided by users on pages and thus can violate HIPAA Rules that govern the Use of Online Tracking Technologies by HIPAA Covered Entities and Business Associates.

Schneier on Security
APRIL 22, 2021
Excellent New Yorker article on North Korea’s offensive cyber capabilities.

CyberSecurity Insiders
APRIL 23, 2021
Microsoft Exchange Server Cyber Attack- Cyber Threat actors somehow infiltrated the email servers of Microsoft Exchange operating across the world through a vulnerability and accessed data of many government and private companies. Later, the Satya Nadella led company issued a statement that it could be the work of a Chinese Hacking group named Hafinium.

Tech Republic Security
APRIL 22, 2021
Security professionals would be well-served with this Linux distribution that offers a wide range of penetration and vulnerability testing tools.

Bleeping Computer
APRIL 23, 2021
Click Studios, the company behind the Passwordstate password manager, notified customers that attackers compromised the app's update mechanism to deliver malware in a supply-chain attack after breaching its networks. [.].

Speaker: Blackberry, OSS Consultants, & Revenera
Software is complex, which makes threats to the software supply chain more real every day. 64% of organizations have been impacted by a software supply chain attack and 60% of data breaches are due to unpatched software vulnerabilities. In the U.S. alone, cyber losses totaled $10.3 billion in 2022. All of these stats beg the question, “Do you know what’s in your software?

Security Boulevard
APRIL 22, 2021
If cybersecurity leaders and teams think this year will be quieter and easier than 2020, they are mistaken. The remote work trend launched by COVID-19 is morphing into a new hybrid environment that has some employees working at home full time, others at corporate facilities and many working at either location depending on the day. The post Navigating Cybersecurity Gaps in Uncertain Times appeared first on Security Boulevard.

Hot for Security
APRIL 22, 2021
The bad news. Attackers are exploiting the COVID-19 vaccine apps to deploy malware to Android devices. Since the outburst of the pandemic, they haven’t missed any opportunity to spread malware via Covid19-themed emails, apps, websites and social media. But now, Bitdefender researchers have found multiple apps taking advantage of mobile users looking for information about the vaccines or seeking an appointment to get the jab.

Tech Republic Security
APRIL 22, 2021
While the software solutions have made it easier to work from home, they've also made it easier to launch malware.

Bleeping Computer
APRIL 22, 2021
The "external sender" warnings shown to email recipients by clients like Microsoft Outlook can be hidden by the sender, as demonstrated by a researcher. Turns out, all it takes for attackers to alter the "external sender" warning, or remove it altogether from emails is just a few lines of HTML and CSS code. [.].

Advertisement
Within the past few years, ransomware attacks have turned to critical infrastructure, healthcare, and government entities. Attackers have taken advantage of the rapid shift to remote work and new technologies. Add to that hacktivism due to global conflicts and U.S. elections, and an increased focus on AI, and you have the perfect recipe for a knotty and turbulent 2024.

Security Boulevard
APRIL 19, 2021
Here at Tripwire, we, like many others, recently surpassed the one-year anniversary of working from home due to the COVID-19 pandemic. Since March of 2020, we have converted kitchens, spare bedrooms and garages into office spaces. Our pets and children have become our coworkers, and companies are reporting a sudden increase in shirt sales as […]… Read More.
The Hacker News
APRIL 20, 2021
An ongoing malvertising campaign tracked as "Tag Barnakle" has been behind the breach of more than 120 ad servers over the past year to sneakily inject code in an attempt to serve malicious advertisements that redirect users to rogue websites, thus exposing victims to scamware or malware.
Tech Republic Security
APRIL 21, 2021
Hackers claim to have infiltrated the networks of Quanta Computer Inc., which makes Macbooks and hardware for HP, Facebook and Google.

Bleeping Computer
APRIL 21, 2021
Linux kernel project maintainers have imposed a ban on the University of Minnesota (UMN) from contributing to the open-source Linux project after a group of UMN researchers were caught submitting a series of malicious code commits, or patches that deliberately introduced security vulnerabilities in the official Linux project. [.].

Speaker: Erika R. Bales, Esq.
When we talk about “compliance and security," most companies want to ensure that steps are being taken to protect what they value most – people, data, real or personal property, intellectual property, digital assets, or any other number of other things - and it’s more important than ever that safeguards are in place. Let’s step back and focus on the idea that no matter how complicated the compliance and security regime, it should be able to be distilled down to a checklist.
Security Boulevard
APRIL 18, 2021
Like most technology workforce segments, the cybersecurity diversity issue is a very acute problem: there simply isn’t nearly enough representation of diverse backgrounds in cybersecurity roles, from security operations center (SOC) analysts all the way up through enterprise-level CISOs and board members. Erkang Zheng, founder and CEO of JupiterOne, said the primary issue that comes.
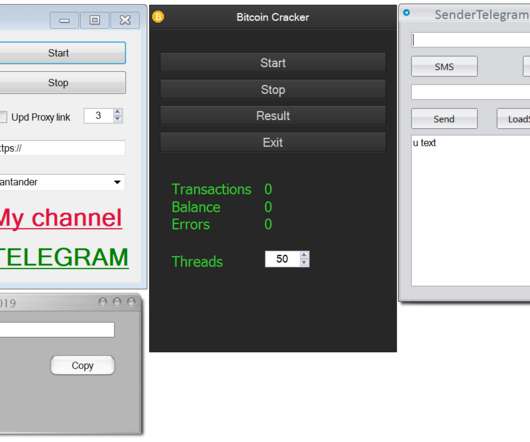
Security Affairs
APRIL 19, 2021
Avast researchers analyzed the activity of a simple cryptocurrency malware dubbed HackBoss that allowed its operators to earn over $560K. While the value of major cryptocurrencies continues to increase, cybercriminals and malware authors focus their efforts on cryptocurrency miners and malicious code that could empty the wallets of the victims. The antivirus company Avast analyzed the case of a simple malware dubbed HackBoss and how it allowed its operators to earn more $560K worth of cryptocurr
Tech Republic Security
APRIL 19, 2021
Using Washington State's proposed law as a guide, New York, Texas and many other states are inching their way toward a data privacy law.
Bleeping Computer
APRIL 21, 2021
The US Cybersecurity and Infrastructure Security Agency (CISA) has issued a new emergency directive ordering federal agencies to mitigate an actively exploited vulnerability in Pulse Connect Secure (PCS) VPN appliances on their networks by Friday. [.].

Speaker: William Hord, Vice President of ERM Services
A well-defined change management process is critical to minimizing the impact that change has on your organization. Leveraging the data that your ERM program already contains is an effective way to help create and manage the overall change management process within your organization. Your ERM program generally assesses and maintains detailed information related to strategy, operations, and the remediation plans needed to mitigate the impact on the organization.
Let's personalize your content