Don’t feed the trolls and other tips for avoiding online drama
We Live Security
MAY 31, 2021
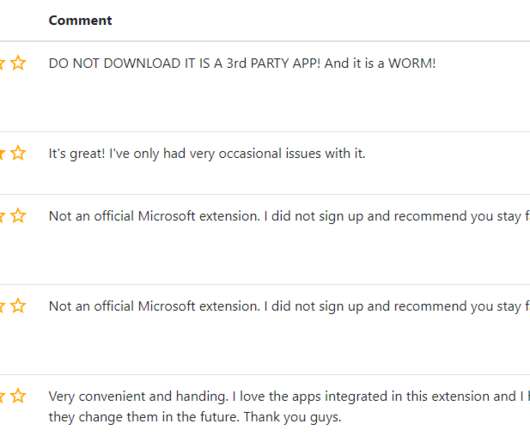
You may not be able to escape internet trolls, but you have a choice about how you will deal with them – here’s how you can handle trolls without losing your cool. The post Don’t feed the trolls and other tips for avoiding online drama appeared first on WeLiveSecurity.









































Let's personalize your content