Bug in Google Maps Opened Door to Cross-Site Scripting Attacks
Threatpost
SEPTEMBER 8, 2020
A researcher discovered a cross-site scripting flaw in Google Map's export function, which earned him $10,000 in bug bounty rewards.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 site-map
site-map 
Threatpost
SEPTEMBER 8, 2020
A researcher discovered a cross-site scripting flaw in Google Map's export function, which earned him $10,000 in bug bounty rewards.
Krebs on Security
MARCH 12, 2020
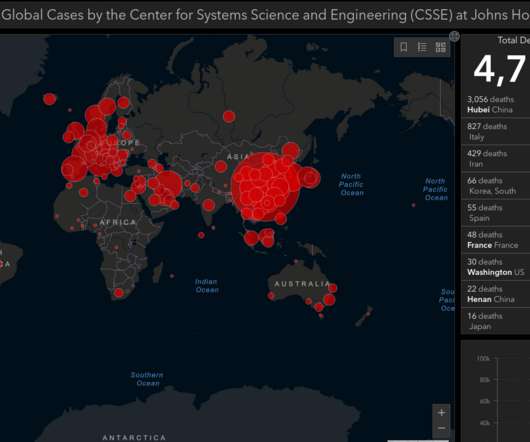
A recent snapshot of the Johns Hopkins Coronavirus data map, available at coronavirus.jhu.edu. In one scheme, an interactive dashboard of Coronavirus infections and deaths produced by John Hopkins University is being used in malicious Web sites (and possibly spam emails) to spread password-stealing malware.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Troy Hunt
AUGUST 12, 2021
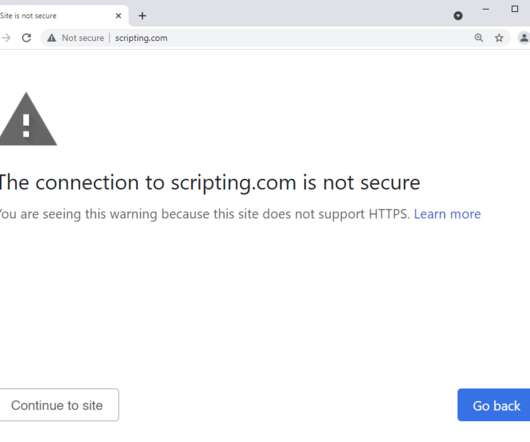
He crawls the sites from a US IP address using request headers that emulate a common browser. The top million is defined by Tranco and Scott uses it to produce 2 other lists which drive this little project: The top sites that redirect to HTTPS The top sites that don't redirect to HTTPS These lists don't add up to 1 million.

The Security Ledger
APRIL 22, 2021
Software vulnerabilities in web sites operated by John Deere could allow a remote attacker to harvest information on the company’s customers including their names, physical addresses and the equipment they own. The revelation suggests the U.S. agriculture sector is woefully unprepared for disruptive cyber attacks, experts warn.

Graham Cluley
JULY 24, 2023
Some employees at Google will have internet access from their desktop PCs significantly restricted, with only internal web-based tools and Google-owned sites such as Google Drive, Google Maps, and Gmail accessible. But will such an approach protect the tech giant from attacks? Read more in my article on the Hot for Security blog.
Krebs on Security
MARCH 20, 2024
Responding to a reader inquiry concerning the trustworthiness of a site called TruePeopleSearch[.]net The site offers to sell a report containing photos, police records, background checks, civil judgments, contact information “and much more! Scouring multiple image search sites reveals Ms. 03-12 15, Singapore).

Security Affairs
FEBRUARY 29, 2020
Threat actors are launching a hacking campaign aimed at taking over tens of thousands of WordPress sites by exploiting critical vulnerabilities. One of the issues exploited in the attacks is a zero-day vulnerability that affects several plugins and that could allow hackers to create admin accounts and take over the sites.

Security Affairs
SEPTEMBER 6, 2023
A Reddit user with the handle ‘Educational-Map-8145’ published a proof of concept exploit for a zero-day flaw in the Linux client of Atlas VPN. ” reads the post published by ‘Educational-Map-8145’ “A malicious javascript on ANY website can therefore craft a request to that port and disconnect the VPN.

Security Affairs
FEBRUARY 4, 2020
A German artist demonstrated how using a simple trick it is possible to deceive Google Maps and create a virtual traffic jam. The German artist Simon Weckert conducted a simple experiment to demonstrat e how to deceive Google Maps and create a virtual traffic jam. Copyright (C) 2014 Media.net Advertising FZ-LLC All Rights Reserved -->.
Troy Hunt
NOVEMBER 13, 2021
Beg bounties are a terrible practice that should die a fiery death (although I'm a little tempted to mess with them a little more.

Krebs on Security
JANUARY 13, 2020
While maps-icloud[.]com icloud.com-site-log[.]in. Case in point: Targets of the phishing domains above who are undecided on whether the link refers to a legitimate Apple site might seek to load the base domain into a Web browser (minus the customization in the remainder of the link after the first forward slash).

SiteLock
AUGUST 27, 2021
core was susceptible to a Cross-site Request Forgery (CSRF) vulnerability inside of the com_templates override view. Cross-site Request Forgery is a vulnerability that allows an attacker to trick a valid user into performing an action they did not intend. Missing access checking in the mphputf8 mapping files made versions 3.6.0 – 3.9.12
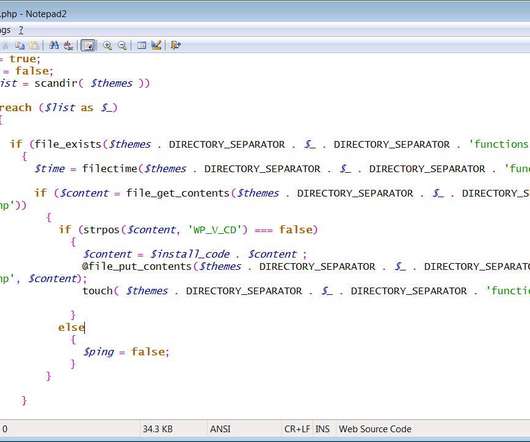
Security Affairs
MARCH 26, 2020
In November 2019, experts reported a highly active malicious campaign that was infecting WordPress sites with a malware dubbed WP-VCD that injects a backdoor into any themes that are installed on the site as well as various PHP files. The WP-VCD malware also attempt to compromise other sites on the same shared host.

Veracode Security
JUNE 21, 2022
Much like last year, we created an interactive heat map that lists out the most prevalent flaws by language along with an explanation of the flaw, supporting SOSS data, and tips for preventing the flaw. ? Take cross-site scripting (XSS), for example. For those of you familiar with last year’s heat map, you’…
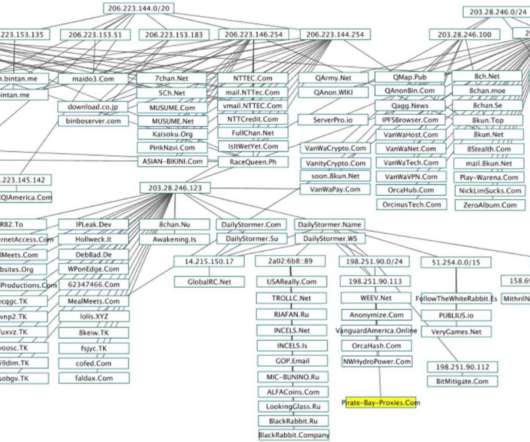
Krebs on Security
OCTOBER 22, 2020
The IP address ranges in the upper-left portion of this map of QAnon and 8kun-related sites — some 21,000 IP addresses beginning in “206.” ” and “207.” ” — are assigned to N.T. Technology Inc. Image source: twitter.com/Redrum_of_Crows. Petersburg, Russia).

Krebs on Security
DECEMBER 6, 2023
Meanwhile, security experts argue that even in cases where online abusers provide intentionally misleading or false information in WHOIS records, that information is still extremely useful in mapping the extent of their malware, phishing and scamming operations.
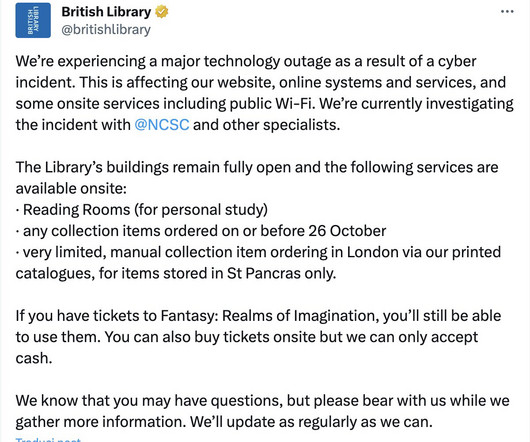
Security Affairs
NOVEMBER 1, 2023
It is located in London and houses a collection of over 150 million items, including books, manuscripts, maps, newspapers, magazines, music recordings, and films. The outage also affects some on-site services, including the public Wi-Fi. “We’re experiencing a major technology outage as a result of a cyber incident.

Malwarebytes
MARCH 15, 2023
OFFICIAL (@stalker_thegame) March 12, 2023 According to GSC, the hacktivists accessed an employee's image app account and stole STALKER 2's full story, cut scenes, various concept art, global maps, and more. Nick Frost", a Vestnik TSS administrator, posted the group's demands on the Russian social media site VK.com.

Troy Hunt
JUNE 21, 2019
Check out how much HIBP trended in searches in January (yes, that's a direct map to my stress levels and yes, I will send stickers to anyone who creates that site I mentioned!) References Scott wrote about maintaining state in a Cloudflare worker (this is a fundamental part of how we're able to process 670M reports a day!
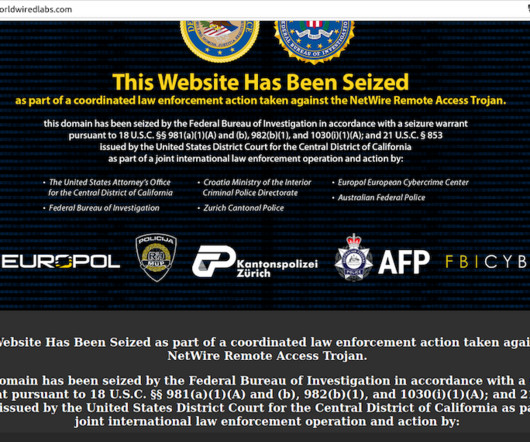
Krebs on Security
MARCH 9, 2023
The site’s true WHOIS registration records have always been hidden by privacy protection services, but there are plenty of clues in historical Domain Name System (DNS) records for WorldWiredLabs that point in the same direction. com also show the site forwarded incoming email to the address tommaloney@ruggedinbox.com.

The Security Ledger
MAY 27, 2021
Rethinking Common Approaches To Cybersecurity Deere John: Researcher Warns Ag Giant’s Site Provides a Map to Customers, Equipment Can Blockchain Solve Data’s Integrity Problem? The post The SOC Hop Needs to be a Relic of the Past appeared first on The Security Ledger with Paul F. Related Stories Futility or Fruition?Rethinking

Krebs on Security
NOVEMBER 21, 2020
In March, a voice phishing scam targeting GoDaddy support employees allowed attackers to assume control over at least a half-dozen domain names, including transaction brokering site escrow.com. Limit the amount of personal information you post on social networking sites. 2019 that wasn’t discovered until April 2020. .”

The Security Ledger
JULY 11, 2021
Related Stories Episode 214: Darkside Down: What The Colonial Attack Means For The Future of Ransomware Episode 218: Denial of Sustenance Attacks -The Cyber Risk To Agriculture Deere John: Researcher Warns Ag Giant’s Site Provides a Map to Customers, Equipment.

Krebs on Security
APRIL 26, 2019
A map showing the distribution of some 2 million iLinkP2P-enabled devices that are vulnerable to eavesdropping, password theft and possibly remote compromise, according to new research. Marrapese said a proof-of-concept script he built identified more than two million vulnerable devices around the globe (see map above).

Malwarebytes
JANUARY 11, 2024
Authentication cookies are in essence pieces of data that the browser sends to a site to identify the user and check whether they are logged in. A Google account provides access to Google services like Gmail, Google Calendar, and Google Maps, but also Google Ads and YouTube.
Malwarebytes
SEPTEMBER 19, 2022
Sniffies identifies itself as a “modern, map-based, meetup app for gay, bi, and curious guys.” In essence it relies on users making typing errors (typos) when entering a site or domain name. Lead the users to bogus technical 'support' scam sites. Lead the users to fake job posting sites". Typosquatting.

SiteLock
AUGUST 27, 2021
Have you ever visited a website — only to be greeted by an alarming red screen that reads: “The site ahead contains malware”? You may not know that your website has been infected with malware — but you’ll figure it out when Google or another search engine detects it and marks your site with the warning label.

SiteLock
AUGUST 27, 2021
Start by mapping out your defenses with the appropriate security solutions, such as a web application firewall or malware scanning and remediation solutions. Many of today’s sites feature forms to collect customers’ contact information and store it in a database. Cross-Site Scripting. SQL Injection Vulnerabilities.

The Security Ledger
AUGUST 8, 2021
» Related Stories Deere John: Researcher Warns Ag Giant’s Site Provides a Map to Customers, Equipment Episode 218: Denial of Sustenance Attacks -The Cyber Risk To Agriculture Exclusive: Flaws in Zoom’s Keybase App Kept Chat Images From Being Deleted. Read the whole entry. »

Malwarebytes
JULY 12, 2021
The very common name of the watch in this case (“Dust watch”) means the results are filled with YouTube videos and gaming articles about the popular CounterStrike map “Dust”. Now, we can’t say which site is tied to the spam messages on Twitter. The site responsible may already be offline. What do offers really cost online?

Malwarebytes
MARCH 13, 2023
At the time it was impossible to confirm this claim, but after two earlier victims, Community Health Systems (CHS) and Hatch Bank disclosed that data was stolen in the GoAnywhere MFT attacks, the Clop leak site now shows seven new companies. At least two of them reportedly have been breached using the GoAnywhere MFT vulnerability.

The Security Ledger
MAY 13, 2021
» Related Stories Exclusive: Flaws in Zoom’s Keybase App Kept Chat Images From Being Deleted Deere John: Researcher Warns Ag Giant’s Site Provides a Map to Customers, Equipment Episode 210: Moving The Goal Posts On Vendor Transparency: A Conversation With Intel’s Suzy Greenberg. Read the whole entry. »

Security Affairs
APRIL 16, 2019
Expert discovered an exploit that could allow ad blocking filter list maintainers for the Adblock Plus, AdBlock, and uBlocker browser extensions to craft filters to inject remote scripts into web sites. Armin Sebastian used Google Maps for his test: /^[link]. With the release of Adblocker Plus 3.2 ” Armin wrote.
Security Affairs
JUNE 3, 2023
blacksuit extension to the name of the encrypted files, drops a ransom note into each directory containing the encrypted files, and adds the reference to its TOR chat site in the ransom note along with a unique ID for each of its victims. BlackSuit ransomware operators also set up a data leak site. BlackSuit appends the .

Adam Levin
SEPTEMBER 27, 2019
” “We’re the #1 result,” Basecamp’s ad copy continued, “but this site lets companies advertise against us using our brand. iOS, Apple Maps, and Bing) do exist. Not too long ago, the same search resulted in a first hit featuring Basecamp, but it was an ad. So here we are. A small, independent co.
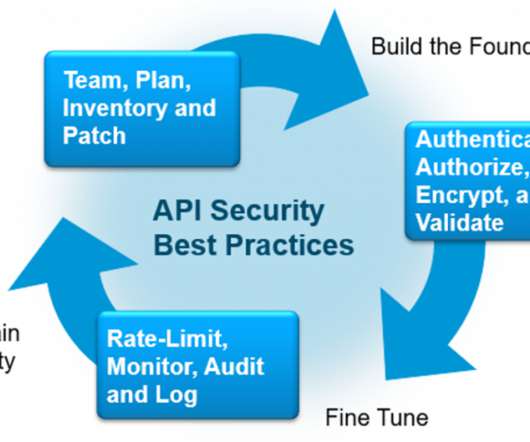
Cisco Security
AUGUST 30, 2021
Maps to API1-API10. Maps to API1-API10. Maps to API1,API2,API5, and API6. Maps API1 and API5. Maps to API7. Maps to API3 and API7. This plan document is the perfect addition to an existing governance policy. Ensure the plan covers public, private, and partner APIs. Inventory and patch your APIs.
Security Affairs
OCTOBER 22, 2021
One of the companies created by the cyber criminal organizations with this purpose is Combi Security, but researchers from Gemini Advisory discovered other similar organizations by analyzing the site of another fake cybersecurity company named Bastion Security. ” concludes the report. ” concludes the report. Pierluigi Paganini.

SiteLock
AUGUST 27, 2021
It leverages the SiteLock threat database, which is built from more than 12 million protected sites. According to our research, sites with a higher risk are 12 times more likely to be exploited than those with low risk. Given that fact, many sites are more likely to be compromised than many people realize.

SiteLock
AUGUST 27, 2021
This link might look like your website’s URL, but it will actually lead users to a malicious site that includes forms with input fields that request personal information. In addition, search engines also perform regular site scans and will blacklist websites if they detect an infection.

SiteLock
AUGUST 27, 2021
And although security is rarely top-of-mind when you are working away on your WordPress blog, e-commerce site or client websites, the fact is, if your website isn’t secure, you have a 1-in-3 chance of being hacked at some point. Check out this mesmerizing attack map that shows hacking in real-time. Don’t believe it?
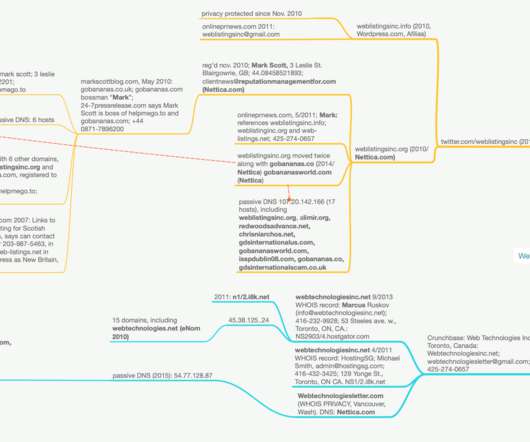
Krebs on Security
MARCH 23, 2020
Cached versions of weblistingsinc.org at archive.org show logos similar to the one featured on the Web Listings mailer, and early versions of the site reference a number of “business partners” in India that also perform SEO services. Cached versions of this site from 2011 show it naming Web Listings Inc.
SiteLock
AUGUST 27, 2021
In carrying out this type of attack, cybercriminals typically replace existing content on your site with their own messages — whether those messages are intended to be political, religious, or simply shocking. First, prospective customers will abandon your site if they don’t feel it’s secure.

Malwarebytes
FEBRUARY 19, 2024
CISA (the Cybersecurity & Infrastructure Security Agency) has issued a cybersecurity advisory after the discovery of documents containing host and user information of a state government organization’s network environment—including metadata—on a dark web brokerage site.

Krebs on Security
FEBRUARY 14, 2022
Later that same day, the @fuck_maze account posted a link to a Pastebin-like site that included working exploit code for a recently patched security hole in SonicWall VPN appliances ( CVE-2021-20028 ). As usual, I put together a rough mind map on how all these data points indicate a connection between Wazawaka, Orange, and Boriselcin.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content