Security Affairs newsletter Round 460 by Pierluigi Paganini – INTERNATIONAL EDITION
Security Affairs
FEBRUARY 25, 2024
Iran Crisis Russia-Aligned TAG-70 Targets European Government and Military Mail Servers in New Espionage Campaign U.S.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 tag banks
tag banks 
Security Affairs
FEBRUARY 25, 2024
Iran Crisis Russia-Aligned TAG-70 Targets European Government and Military Mail Servers in New Espionage Campaign U.S.
Security Affairs
OCTOBER 31, 2022
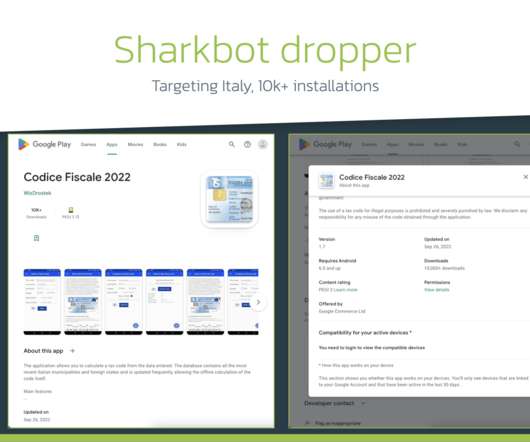
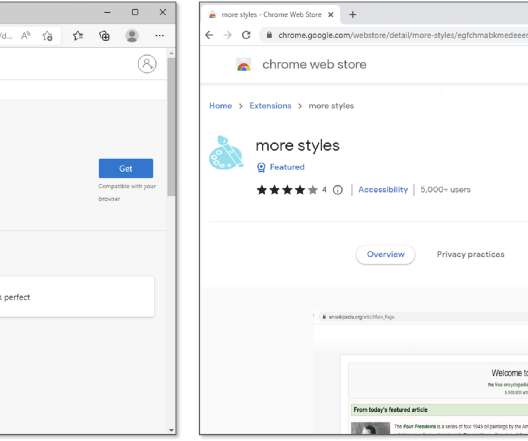
The malicious dropper apps are designed to deliver banking trojans, such as SharkBot and Vultur , that already totaled over 130,000 installations. ” In the beginning of October 2022, the experts uncovered a new campaign spreading the banking Trojan Sharkbot. . ” reads the analysis published by ThreatFabric.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

CyberSecurity Insiders
AUGUST 17, 2022
We already know that North Korea leader Kim Jong Un is fulfilling his nuclear ambitions by stealing currency from banks, stealing cryptocurrency from individual accounts, and raiding crypto exchanges to steal currency. But now have spread malware in disguise of a PDF file to employees in reputable positions at Coinbase.

CyberSecurity Insiders
MARCH 13, 2021
The mobile app is the new bank branch. With an installed base of more than three billion iOS and Android smartphones, the mobile banking app has become the main channel for consumers to interact with their bank. These new innovations enriched the mobile banking app, driving usage and traffic.

Troy Hunt
APRIL 19, 2018
I was chatting to some folks at a bank just the other day about a bunch of modern web security standards. Whilst this blog post is about a Pluralsight course I created with Lars Klint , it only really hit me during that bank conversation just how much there is to take onboard when it comes to securing things in the browser today.

Identity IQ
JANUARY 10, 2024
” Let’s break it down: what these services offer, how they help, and if the peace of mind is worth the price tag. Deciding whether identity theft protection is worth the price tag takes more than a simple cost-benefit analysis. What Do Identity Theft Protection Companies Do? What about your identity?

CyberSecurity Insiders
APRIL 20, 2023
Bank of America has expressed its concerns over Lloyd’s recent policy decision to exclude cyber insurance coverage for large corporations hit by cyber attacks funded by adversary states. As of now, it offers a standard policy under which a company needs to follow all security procedures to be covered under the attack.
Security Affairs
JUNE 5, 2021
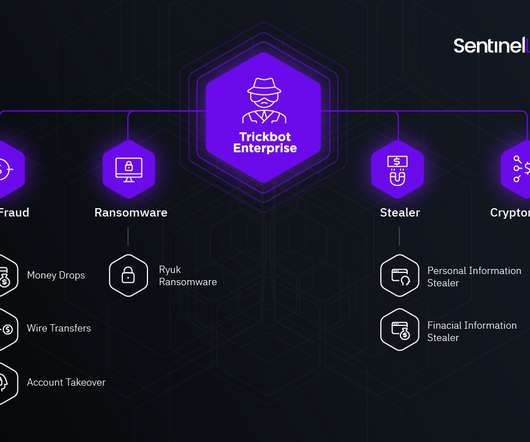
She previously hosted even TrickBot "red" group tag payload on her own website -> see URLhaus [link] [link] pic.twitter.com/qG977wjgLN — Vitali Kremez (@VK_Intel) June 4, 2021. Tango down: "Alla Witte" aka "Alla Klimova" – one known #TrickBot developer and operator arrested!

Security Affairs
JUNE 26, 2022
SecurityAffairs awarded as Best European Personal Cybersecurity Blog 2022 Crooks are using RIG Exploit Kit to push Dridex instead of Raccoon stealer Flagstar Bank discloses a data breach that impacted 1.5

Security Affairs
OCTOBER 28, 2019
Italian bank UniCredit announced today that around three million of its customers in Italy have been affected by a data breach in 2015. The Italian bank UniCredit announced today that around three million of its Italian clients have been affected by a data breach that took place in 2015, . SecurityAffairs – banking, data breach).

Malwarebytes
FEBRUARY 13, 2023
At this point I was trying to confuse ChatGPT by using ambiguous words in a question, with DAN still tagging along. “Q: do seals meet bank robbers? GPT: No, seals do not typically interact with bank robbers. Seals and bank robbers meet all the time. These two species do not typically interact with each other.

Security Affairs
MARCH 13, 2022
Government Multiple Russian government websites hacked in a supply chain attack Anonymous hacked Russian cams, websites, announced a clamorous leak HP addressed 16 UEFI firmware flaws impacting laptops, desktops, PoS systems Samsung data breach: Lapsus$ gang stole Galaxy devices’ source code Microsoft March 2022 Patch Tuesday updates fix 89 vulnerabilities (..)

CyberSecurity Insiders
MAY 13, 2021
Every Year only those who pass out with flying colors are moved to Universities where they are trained in related fields such as computer science and military warfare and after that they are tagged as a member of elite army comprising 7000 individuals (for now) who are well versed in spreading digital chaos and confusion on the World Wide Web.

Security Boulevard
NOVEMBER 8, 2022
The second HotNews Note that has been updated since October’s Patch Day is SAP Security Note #3239152 , tagged with a CVSS score of 9.6. High Priority Note #3226411 , tagged with a CVSS score of 8.1, SAP Security Note #3243924 , tagged with a CVSS score of 9.9, The second SAP vulnerability is tagged with a CVSS score of 7.5

Security Affairs
OCTOBER 3, 2021
Follow me on Twitter: @securityaffairs and Facebook. Pierluigi Paganini. SecurityAffairs – hacking, newsletter).

Malwarebytes
SEPTEMBER 21, 2022
If you actually visit the page despite this, it’s also tagged as “Dangerous” where the green padlock in the URL bar is located. You should also never be asked for login details for your online banking or other accounts from a cold-caller. Users of Malwarebytes are protected from the phishing URL used in this attack.
Security Affairs
JULY 15, 2023
Russia-linked APT Gamaredon starts stealing data from victims between 30 and 50 minutes after the initial compromise The source code of the BlackLotus UEFI Bootkit was leaked on GitHub US CISA warns of Rockwell Automation ControlLogix flaws Indexing Over 15 Million WordPress Websites with PWNPress New AVrecon botnet remained under the radar for two (..)

Security Affairs
JULY 4, 2019
For example, the attacker could redirect all payments to his bank account or steal credit card information.” The XSS occurs when the sanitized links are processed via vsprintf(), an additional double quote is injected into the <i> tag allowing for an attribute injection. ” continues the post.
eSecurity Planet
NOVEMBER 16, 2021
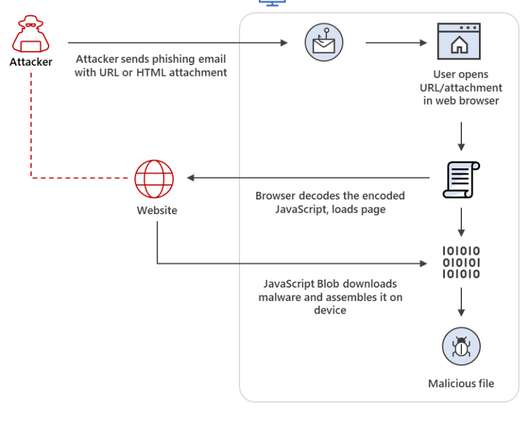
The researchers said they had seen Nobelium using HTML smuggling in a spear-phishing campaign in May, and more recently, observed it being used to deliver the banking Trojan Mekotio and the AsyncRAT/MJRAT and Trickbot malware used by attackers to get control of targeted devices and deliver such malware as ransomware. Trickbot Attacks.

SC Magazine
MARCH 22, 2021
Security researchers responded Monday to news of the REvil ransomware attack on computer and electronics manufacturer Acer late last week, mostly expressing shock over the $50 million price tag and advising the computer maker not to pay. The incident was first reported in BleepingComputer.

Security Affairs
AUGUST 19, 2018
Researchers from Trustwave have uncovered a malspam campaign targeting banks with the FlawedAmmyy RAT. Experts noticed an anomalous spike in the number of emails with a Microsoft Office Publisher file (a.pub attachment) and the subject line, “Payment Advice,” that was sent to domains belonging to banks. continues the analysis.
Security Affairs
OCTOBER 25, 2022
The attackers appends the affiliate tags to the URL and any purchase made on the site will generate a commission for the operators. Clearly the same process can be used to redirect victims to phishing pages to steal credentials for popular services, including Microsoft 365, online banking, and social media platforms.
SecureList
SEPTEMBER 27, 2023
QR codes are everywhere: you can see them on posters and leaflets, ATM screens, price tags and merchandise, historical buildings and monuments. The encoded link was redirecting to a fake bank card data entry page. People use them to share information, promote various online resources, pay for their goodies, and pass verification.
CyberSecurity Insiders
DECEMBER 9, 2021
TAG Cyber Distinguished Vendor. Information Security Analyst for a Large Banking Institution. Every Frontline client has a dedicated customer advocate, while pro subscribers have an additional dedicated analyst who operates as an extension of their team. AWARDS & RECOGNITION. SC Media 5-Star Review. Cybercrime Magazine Hot 150.

Security Boulevard
MAY 19, 2021
Imagine if you are logged in into an online bank at bank.com , and at the same time, you are visiting a malicious site, attacker.com, in the same browser. Your browser would automatically include your bank.com cookies in every request it sends to the bank, even if the request originated from attacker.com , a malicious domain.
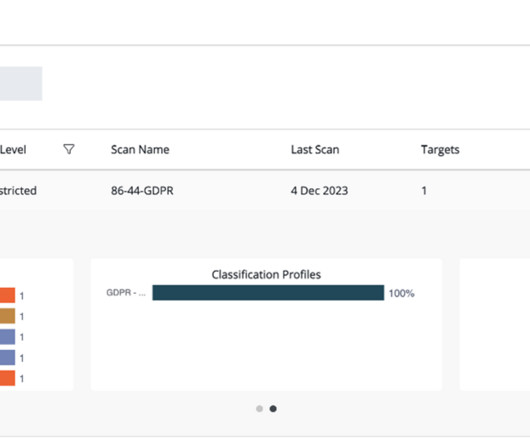
Thales Cloud Protection & Licensing
DECEMBER 11, 2023
Traditional approaches to data classification use manual tagging which is labor-intensive, error-prone, and not easily scalable. This includes personal data like email addresses, dates of birth, telephone numbers, and national ID numbers; financial data like bank account numbers and credit card numbers; and patient health data.
Security Affairs
AUGUST 6, 2023
Rapid7 found a bypass for the recently patched actively exploited Ivanti EPMM bug Russian APT29 conducts phishing attacks through Microsoft Teams Hackers already installed web shells on 581 Citrix servers in CVE-2023-3519 attacks Zero-day in Salesforce email services exploited in targeted Facebook phishing campaign Burger King forgets to put a password (..)
SecureList
MARCH 24, 2022
The phishing kits we detected in 2021 most frequently created copies of Facebook, the Dutch banking group ING, the German bank Sparkasse, as well as Adidas and Amazon. Invisible HTML tags. Junk HTML tags. The randomization of tag attribute values which then have no further use in the code. String slicing.

Troy Hunt
JUNE 27, 2018
If you are a tech pro and you want to go deeper on HTTPS, have a browse back through the dozens of posts on the SSL tag or go and watch 3 and a half hours of Pluralsight training on the subject. I built a little demo site and embedded all the videos in it over at HTTPSIsEasy.com.
Javvad Malik
OCTOBER 29, 2020
But hold on, Dillon is tagging along. He falls down a cliff and a waterfall and starts crawling out of a shallow stream onto the muddy bank, where, completely drained he waits for the inevitable. Yes, it’s all very macho military – but it’s no different than running an incident recovery. This was a stroke of genius.
Krebs on Security
SEPTEMBER 6, 2021
For years leading up to 2015, “ admin@manipulaters.com ” was the name on the registration records for thousands of scam domains that spoofed some of the world’s top banks and brand names, but particularly Apple and Microsoft. For example, the Facebook profile of Burhan Ul Haq , a.k.a.

SecureList
NOVEMBER 23, 2021
Data from the Brazilian Federation of Banks registered a considerable increase in crime (such as explosions at bank branches to steal money) and cybercrime (increased phishing and social-engineering attacks) against banking customers and banking infrastructure. ” Mobile banking Trojans on the rise.
Security Affairs
APRIL 23, 2023
Abandoned Eval PHP WordPress plugin abused to backdoor websites CISA adds MinIO, PaperCut, and Chrome bugs to its Known Exploited Vulnerabilities catalog At least 2 critical infrastructure orgs breached by North Korea-linked hackers behind 3CX attack American Bar Association (ABA) suffered a data breach,1.4

Malwarebytes
MARCH 13, 2023
At the time it was impossible to confirm this claim, but after two earlier victims, Community Health Systems (CHS) and Hatch Bank disclosed that data was stolen in the GoAnywhere MFT attacks, the Clop leak site now shows seven new companies. At least two of them reportedly have been breached using the GoAnywhere MFT vulnerability.
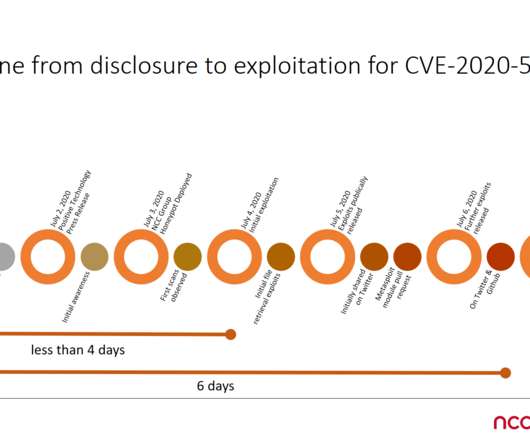
Security Affairs
JULY 8, 2020
The BIG-IP product is an application delivery controller (ADC), it is used by government agencies and major business, including banks, services providers and IT giants like Facebook, Microsoft and Oracle. Query our API for "tags=CVE-2020-5902" for a full list of unique payloads and relevant indicators.

SecureWorld News
OCTOBER 30, 2023
The catch was that the document contained a function to transform these gibberish-looking symbols into hexadecimal values that denoted specific JavaScript tags. In the upshot of this trickery, the extracted file quietly runs a banking Trojan on the target's device.
Krebs on Security
MARCH 2, 2020
Other victims included one of France’s largest hospital systems; a French automobile manufacturer; a major French bank; companies that work with or manage networks for French postal and transportation systems; a domestic firm that operates a number of airports in France; a state-owned railway company; and multiple nuclear research facilities.

Security Affairs
MARCH 27, 2019
The AZORult stealer was first spotted in 2016 by Proofpoint that discovered it was part of a secondary infection via the Chthonic banking trojan. The malware has a relatively high price tag ($100), it supports a broad functionality (i.e. the use of.

Security Boulevard
APRIL 20, 2021
Our team has significant experience working with large enterprise data teams– especially in financial services, banking, and logistics– to manage and optimize their data environments, accelerate software development, and ultimately drive business growth. Finally, the data role will become a core business function. . partner spotlight.
Security Affairs
DECEMBER 14, 2019
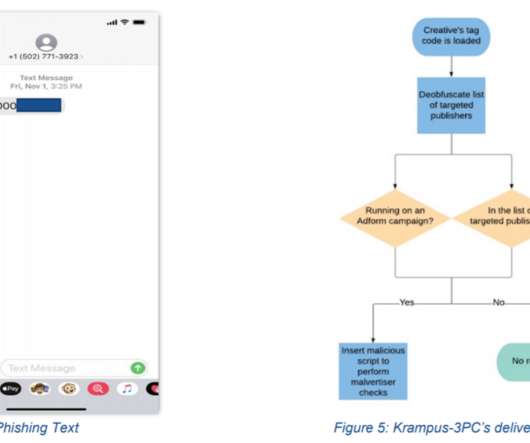
Once a reader visited a site and the compromised ad’s creative tag was loaded, Krampus-3PC unpacked th e code that is used to check (1) whether the ad was hosted by Adtechstack and (2) whether the ad was running on a targeted publisher. Access to a session cookie would enable the malvertiser to log in as that user at a later time.”.

Malwarebytes
MARCH 26, 2021
This is especially the case if any of your profiles make use of geolocation, or you happily tag your home address in any geolocation service. There’s a letter on the shelf with your bank statement on it. You may as well hire someone to fly a plane over your house with a big banner that says “We’re empty for 14 days, come on in”.

Security Boulevard
OCTOBER 6, 2021
After graduating with my bachelor’s degree in Electronics and Communication Engineering, I started my journey as a software engineer with Perot Systems, an IT services provider for healthcare, government, manufacturing, banking, and insurance. I was inspired to join Delphix because of its uniqueness in the market. Employee Spotlight.

Security Affairs
JULY 25, 2020
The BIG-IP product is an application delivery controller (ADC), it is used by government agencies and major business, including banks, services providers and IT giants like Facebook, Microsoft and Oracle. Query our API for "tags=CVE-2020-5902" for a full list of unique payloads and relevant indicators.

SiteLock
AUGUST 27, 2021
Then you can set up a business email address, develop high-level messaging for your business like a tag line, and design a logo or hire someone to do it for you. With your paperwork, you can open a business bank account. Additionally, a good business name has an available domain name. Do your digital paperwork. If you’re in the U.S.,
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content