Designing Contact-Tracing Apps
Schneier on Security
SEPTEMBER 13, 2021
Susan Landau wrote an essay on the privacy, efficacy, and equity of contract-tracing smartphone apps. Also see her excellent book on the topic.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 topic smartphones
topic smartphones 
Schneier on Security
SEPTEMBER 13, 2021
Susan Landau wrote an essay on the privacy, efficacy, and equity of contract-tracing smartphone apps. Also see her excellent book on the topic.

Schneier on Security
DECEMBER 15, 2023
It was connected to your smartphone. ChatGPT both surprised and amazed the world with its ability to understand human language and generate credible, on-topic, humanlike responses. In 2016, I wrote about an Internet that affected the world in a direct, physical manner. It had sensors like cameras and thermostats.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Schneier on Security
JANUARY 8, 2019
This is why your computer and smartphone software is constantly being patched; software vendors are fixing bugs that are also vulnerabilities that have been discovered and are being used. There are challenges with that, of course, but there is already a healthy amount of academic literature on the topic -- and research is continuing.

Hot for Security
APRIL 5, 2021
Cybersecurity can often seem like a topic for the business sector. With most smartphone owners using an Android device, we noticed an unusual trend where a relatively large number of users started installing Zoom apps from non-official sources. But regular consumers are equally affected by cybercrime, directly or indirectly.

CyberSecurity Insiders
APRIL 8, 2021
In case you didn’t read it, the topic was data fatigue. Remember when you received your first smartphone (can anyone say Palm Treo)? Recently we wrote on open extended detection and response (XDR) platform and the problems it helps solve. There is a solution to the pain of multiple panes of glass. Open XDR is the answer.

SecureList
MARCH 13, 2024
Stalkerware is commercially available software that can be discreetly installed on smartphone devices, enabling a perpetrator to monitor an individual’s private life without their knowledge. Once installed, stalkerware makes it possible to access the smartphone from anywhere.

Schneier on Security
SEPTEMBER 26, 2019
This is a complicated topic. You have little choice but to rely on the companies that build your computers and write your software, whether in your smartphones, your 5G wireless infrastructure, or your subway cars. There is definitely a national security risk in buying computer infrastructure from a country you don't trust.
eSecurity Planet
MARCH 15, 2024
It provides extensive insights into cybersecurity topics to guide users through offensive strategies like Wi-Fi network attacks using specialized tools. Mobile hacking: This feature allows users to investigate vulnerabilities particular to mobile devices, such as smartphones and tablets.

Thales Cloud Protection & Licensing
JULY 12, 2023
The following statistics highlight the need to reach out to kids: 73% of teenagers can’t imagine life without a smartphone, and half take their phones to bed. This is when children start participating in cyber and digital activities and develop disciplinary preferences and career aspirations.

Malwarebytes
SEPTEMBER 16, 2022
The user has to approve the login by pressing a button on a smartphone app. It allows direct messages between individuals, and conversations among groups of people take place in channels dedicated to specific topics or areas of concern. This type of MFA sends a notification to a user whenever their username and password are used.

SecureWorld News
OCTOBER 21, 2021
Smartphone usage has been linked to many terrible things in a study by Harvard : depression, anxiety, poor sleep, increased odds of dying in a car accident. SecureWorld's panel of cybersecurity professionals tackle this topic in our Remote Sessions webcast, It's 2 AM. RESOURCE] Data is generating across more devices than ever before.
Notice Bored
OCTOBER 19, 2021
when I read the recommendation for a topic-specific policy on backup. We don't always take the trouble to consult with colleagues, research the topic, explore the risks and controls, and think both broadly and deeply about the subject area - the topic of the policy. Why do data need to be backed up? What's the purpose?

SecureList
JANUARY 31, 2023
For any requests on this topic, please contact crimewareintel@kaspersky.com. This blog post covers the NFC-related capabilities of recent Prilex modifications. The Prilex family is detected by all Kaspersky products as HEUR:Trojan.Win32.Prilex Prilex and HEUR:Trojan.Win64.Prilex.

Security Affairs
JUNE 8, 2021
Criminals were using secure smartphones configured to run only the An0m app that was able to communicate only with peers with the same configuration. Below my interview on the topic made with TRT World: Follow me on Twitter: @securityaffairs and Facebook. Pierluigi Paganini. SecurityAffairs – hacking, Trojan Shield).

Herjavec Group
OCTOBER 27, 2020
Fast forward to now: cybersecurity is a consistent topic amongst the C-Suite and CSAM is a must-mention, internationally recognized campaign. Department of Homeland Security (DHS) in October 2004. Not long ago CSAM was a niche concept that only the security team knew about. The world needs to cyber protect 300 billion passwords this year.
Hacker Combat
DECEMBER 6, 2021
The Loop software for smartphones and desktops includes a workspace, pages, and components. Nothing is more aggravating than wasting your team’s time on the wrong topics. Microsoft Loop, a development of their Fluid Framework technology, is a solution for project communication and coordination.

Security Boulevard
FEBRUARY 19, 2021
They might be reading your article on a tiny smartphone screen. If you already have a topic in mind, a good way to combat writer's block is to start with an outline. When people read your blog posts, they might scan the entire article before committing time to reading it. Divide your article up into easily digestible chunks.

Malwarebytes
JANUARY 24, 2023
The Chinese owned TikTok app has been under a lot of scrutiny, and a few US states have officially banned TikTok from state-owned or state-leased smartphones, laptops, and other internet-enabled devices. Spying Scraping data by and for advertisers is not the only concern about social media.

Malwarebytes
SEPTEMBER 21, 2021
Whether you’re looking for a smartphone, a laptop, a gaming device or something else, or even just signing up for an account online, you want to make sure your kids are protected. Do this on all the devices they use, including their smartphones. Thanks to smartphones, we’ve found in ourselves our inner shutterbug.

Duo's Security Blog
JANUARY 9, 2023
In previous years, we’ve seen research groups like Pew Research Center report that 28% of smartphone owners say they do not use a screen lock or other security features to access their device. It is difficult to determine an exact number of jailbroken devices. However, Pingdom reports a rough estimate of as many as 8.5%

CyberSecurity Insiders
JUNE 18, 2021
The first is the digital version of an official physical identity document – such as a digital driving license that lives in a mobile wallet on your smartphone. We have also published a whitepaper on the topic which you can download for free here. Broadly speaking, Digital Identities can take two forms.

Security Affairs
APRIL 8, 2022
Endpoints are the devices that connect to your networks, such as laptops, smartphones, and printers. Cloud security is an important and complex topic, and there are considerations beyond the scope of this article. This way, you only have to remember one master password to access all of your other passwords. Secure your endpoints.

CyberSecurity Insiders
FEBRUARY 12, 2021
Finally, users would be able to use their FIDO token on their smartphone to unlock their room and access hotel facilities, all these actions embodying the concept of truly portable authentication. .
Joseph Steinberg
JANUARY 22, 2024
As the publisher of the original English version of Hacking for Dummies explained when the seventh edition of the book was released in 2022: Your smartphone, laptop, and desktop computer are more important to your life and business than ever before.

Security Affairs
JANUARY 14, 2021
The ads usually offer cameras, game consoles, laptops, smartphones, and similar items for sale at deliberately low prices. The hierarchy of the scammer groups represents a pyramid, with the topic starters on top. The topic starters’ share is about 20-30 percent of the stolen sum.

Security Affairs
OCTOBER 13, 2020
The cybersecurity issues related to IoT are a brand-new topic in the niche. It’s up to the end-users to update their IoT devices, and that is a potential problem because people are still reluctant to update their smartphones and computers. Once they found backdoors, they released updates and patches to deliver necessary security fixes.
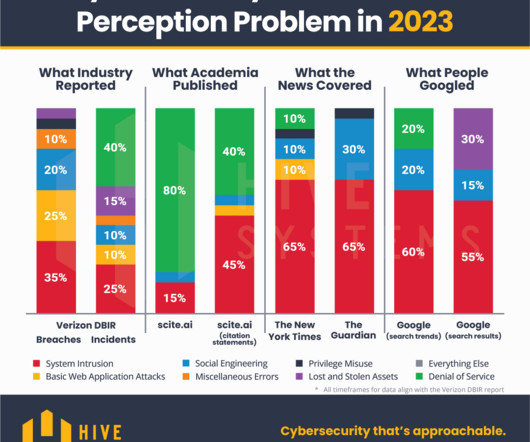
Approachable Cyber Threats
DECEMBER 6, 2023
If the news media and the internet are leading us astray, maybe we can pinpoint what those influences are and systematically reduce our bias on those topics. Academic publications aligned most closely with DBIR in terms of coverage proportion across topics in the past but not so much this time around.

Hacker Combat
AUGUST 7, 2020
Since many people carry smartphones, they find it easier to use mobile devices to make payments. Lou is a respected expert on the topics of customer service, payments and fintech, Internet technology, and entrepreneurship. The use of mobile devices is on the rise and mobile commerce accounts for about 48 percent of digital sales.

Spinone
NOVEMBER 19, 2018
It covers such topics as suspicious files and links, password creation, 2-step verification , software, antivirus, OS, backup , mobile security , physical security and so on. Do not insert these links in the browser and do not scan QR-codes with your smartphone if you are not sure about their contents or origin.
SecureList
JUNE 1, 2021
We will see what children were engrossed in during their leisure time when they were fixated on their smartphones, how and where they tapped into their creativity, what they were listening to and who their favorite YouTube blogger was. The popularity of a topic is determined by its share of related queries. YouTube bloggers.

SecureList
MARCH 1, 2021
Therefore, attackers constantly monitor the situation in the world, collecting the most interesting topics for potential victims, and then use these for infection or cheating users out of their money. It just so happened that the year 2020 gave hackers a large number of powerful news topics, with the COVID-19 pandemic as the biggest of these.
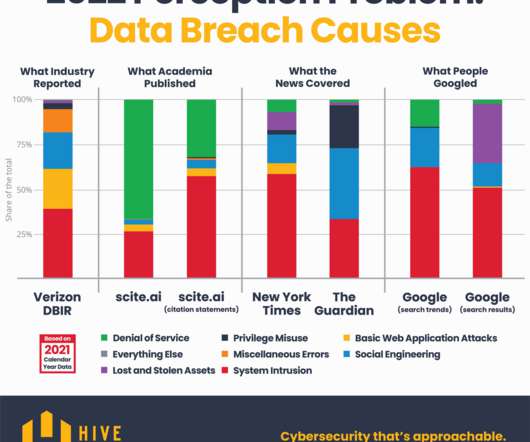
Approachable Cyber Threats
DECEMBER 13, 2022
If the news media and the internet are leading us astray, maybe we can pinpoint what those influences are and systematically reduce our bias on those topics. Academic publications aligned most closely with DBIR in terms of coverage proportion across topics in 2020 but not so much in 2021. Do those perceptions reflect reality?
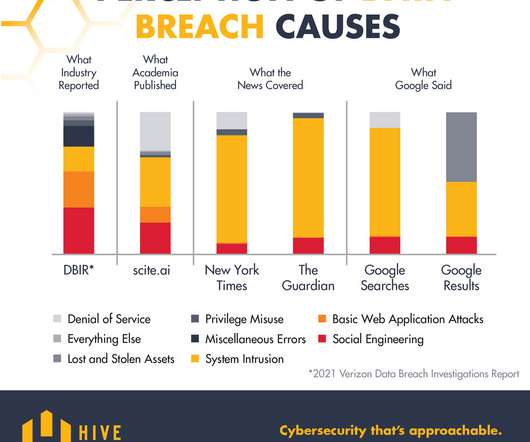
Approachable Cyber Threats
SEPTEMBER 14, 2021
If the news media and the internet are leading us astray, maybe we can pinpoint what those influences are and systematically reduce our bias on those topics. A curious discrepancy is that The Guardian covered relatively little (1%) on the topic of denial of service attacks compared to the New York Times (12%). Try it out!

The Last Watchdog
JUNE 6, 2022
It was only a few short years ago that BYOD and Shadow IT exposures were the hot topics at RSA. Employees using their personally-owned smartphones to upload cool new apps presented a nightmare for security teams. For a full drill down on our discussion, please give the accompanying podcast a listen. Here are key takeaways.

Spinone
AUGUST 20, 2018
In the previous post we have covered the cyber security topics of suspicious files and links, password creation and 2-step verification. Do not root your smartphone. Let’s discuss OS and software, antivirus, backup, mobile security, physical security and so on. Operating System and Software Do not use pirate software.
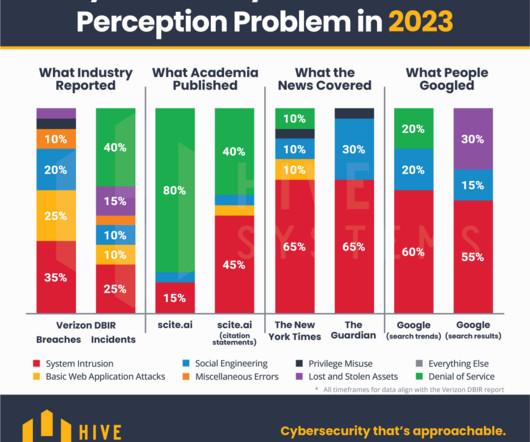
Approachable Cyber Threats
DECEMBER 7, 2023
If the news media and the internet are leading us astray, maybe we can pinpoint what those influences are and systematically reduce our bias on those topics. Academic publications aligned most closely with DBIR in terms of coverage proportion across topics in the past but not so much this time around.
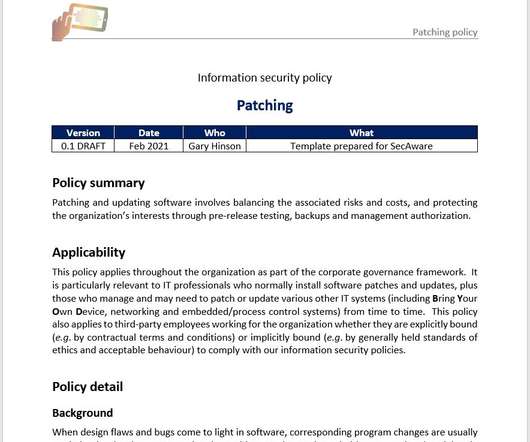
Notice Bored
OCTOBER 22, 2021
With respect to whoever crafted the wording of the 10th topic-specific example policy for ISO/IEC 27002:2022 , "management of technical vulnerabilities" is the kind of phrase that speaks volumes to [some, switched-on, security-aware] IT pro's. The organization may name these topic-specific policies standards, directives, policies or others."
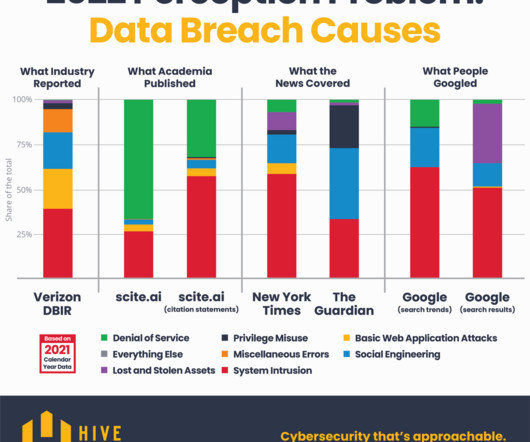
Approachable Cyber Threats
DECEMBER 13, 2022
If the news media and the internet are leading us astray, maybe we can pinpoint what those influences are and systematically reduce our bias on those topics. Academic publications aligned most closely with DBIR in terms of coverage proportion across topics in 2020 but not so much in 2021. Do those perceptions reflect reality?

SecureList
DECEMBER 22, 2021
Filtering targets six potentially dangerous topics: Adult content, Alcohol, Narcotics, Tobacco, Racism and Profanity. The popularity of a topic is determined by its share of related queries. These days, most children are actively using not only computers but also smartphones and tablets. Yandex), as well as on YouTube.
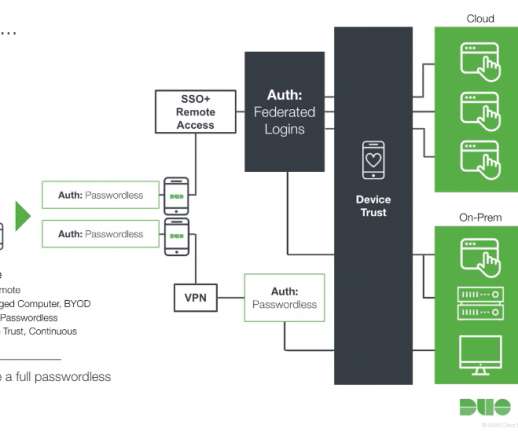
Cisco Security
MAY 21, 2021
Securing user identities was another popular topic this year that many vendors covered. At the same time, the ubiquity of smartphones and biometric capable devices and the emergence of WebAuthn, a FIDO2 standard for modern strong authentication, promises to put an end to the crisis of compromised credentials.

The Last Watchdog
MAY 20, 2021
One of the hottest topics at RSA Conference 2021 taking place virtually this week is the Secure Access Services Edge ( SASE ) security framework. Related: Cybersecurity experts react to Biden’s EO. In this dynamic, software-driven environment, the bolt-on approach to protecting company datacenters has become obsolete.

SecureList
DECEMBER 6, 2022
By the early 2000s, charity had become a common scam topic: for example, after the massive Indian Ocean earthquake and tsunami of 2004, users received messages from fake charities pleading for donations. Instagram account “giving away” free smartphones. Form for collecting personal data to send the bogus prize.

Cisco Security
FEBRUARY 14, 2022
Josh Green: Thankfully technology has advanced so that suddenly everyone has a fingerprint reader or face recognition scanner in their pocket through biometric technology in their smartphones. Where can your readers go to find out more about these topics? Thank you for sharing those insights.
Cisco Security
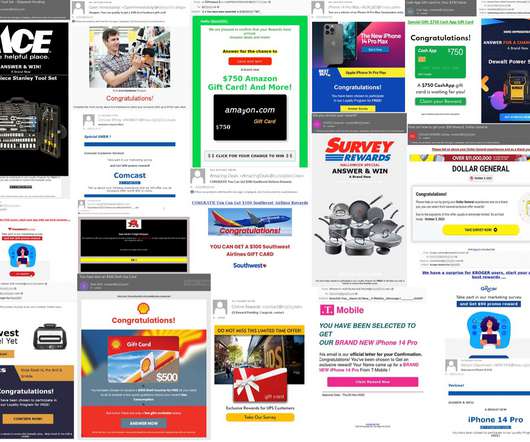
DECEMBER 8, 2022
According to these emails, if you fill out a simple survey you’ll receive “exclusive offers” such as gift cards, smartphones, smart watches, power drills, or even pots and pans. Another topic that we covered the last time we explored these types of scams was package delivery spam. Image 1 – Survey scam emails.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content