
AnyDesk confirmed today that it suffered a recent cyberattack that allowed hackers to gain access to the company's production systems. BleepingComputer has learned that source code and private code signing keys were stolen during the attack.
AnyDesk is a remote access solution that allows users to remotely access computers over a network or the internet. The program is very popular with the enterprise, which use it for remote support or to access colocated servers.
The software is also popular among threat actors who use it for persistent access to breached devices and networks.
The company reports having 170,000 customers, including 7-Eleven, Comcast, Samsung, MIT, NVIDIA, SIEMENS, and the United Nations.
AnyDesk hacked
In a statement shared with BleepingComputer late Friday afternoon, AnyDesk says they first learned of the attack after detecting indications of an incident on their production servers.
After conducting a security audit, they determined their systems were compromised and activated a response plan with the help of cybersecurity firm CrowdStrike.
AnyDesk did not share details on whether data was stolen during the attack. However, BleepingComputer has learned that the threat actors stole source code and code signing certificates.
The company also confirmed ransomware was not involved but didn't share too much information about the attack other than saying their servers were breached, with the advisory mainly focusing on how they responded to the incident.
As part of their response, AnyDesk says they have revoked security-related certificates and remediated or replaced systems as necessary. They also reassured customers that AnyDesk was safe to use and that there was no evidence of end-user devices being affected by the incident.
"We can confirm that the situation is under control and it is safe to use AnyDesk. Please ensure that you are using the latest version, with the new code signing certificate," AnyDesk said in a public statement.
While the company says that no authentication tokens were stolen, out of caution, AnyDesk is revoking all passwords to their web portal and suggests changing the password if it's used on other sites.
"AnyDesk is designed in a way which session authentication tokens cannot be stolen. They only exist on the end user's device and are associated with the device fingerprint. These tokens never touch our systems, "AnyDesk told BleepingComputer in response to our questions about the attack.
"We have no indication of session hijacking as to our knowledge this is not possible."
The company has already begun replacing stolen code signing certificates, with Günter Born of BornCity first reporting that they are using a new certificate in AnyDesk version 8.0.8, released on January 29th. The only listed change in the new version is that the company switched to a new code signing certificate and will revoke the old one soon.
BleepingComputer looked at previous versions of the software, and the older executables were signed under the name 'philandro Software GmbH' with serial number 0dbf152deaf0b981a8a938d53f769db8. The new version is now signed under 'AnyDesk Software GmbH,' with a serial number of 0a8177fcd8936a91b5e0eddf995b0ba5, as shown below.
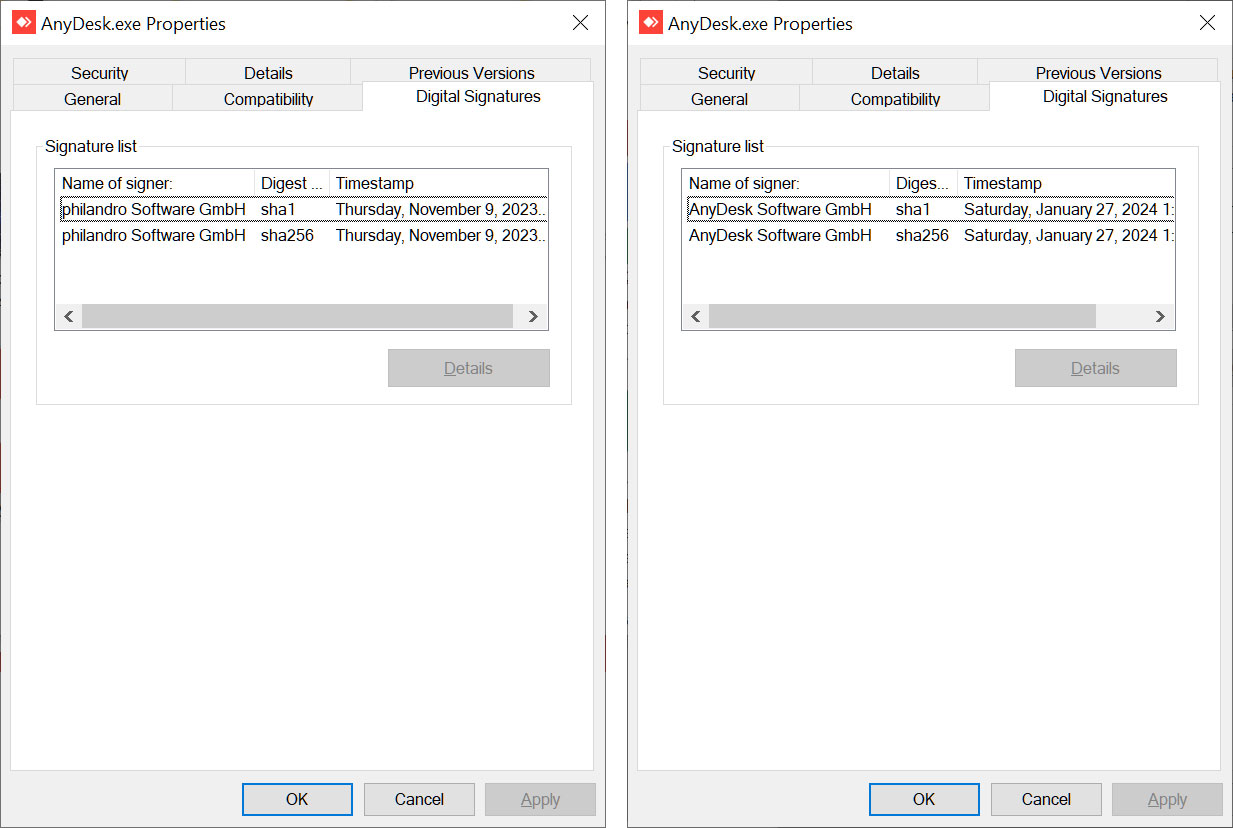
Source: BleepingComputer
Certificates are usually not invalidated unless they have been compromised, such as being stolen in attacks or publicly exposed.
While AnyDesk had not shared when the breach occurred, Born reported that AnyDesk suffered a four-day outage starting on January 29th, during which the company disabled the ability to log in to the AnyDesk client.
"my.anydesk II is currently undergoing maintenance, which is expected to last for the next 48 hours or less," reads the AnyDesk status message page.
"You can still access and use your account normally. Logging in to the AnyDesk client will be restored once the maintenance is complete."
Yesterday, access was restored, allowing users to log in to their accounts, but AnyDesk did not provide any reason for the maintenance in the status updates.
However, AnyDesk has confirmed to BleepingComputer that this maintenance is related to the cybersecurity incident.
It is strongly recommended that all users switch to the new version of the software, as the old code signing certificate will soon be revoked.
Furthermore, while AnyDesk says that passwords were not stolen in the attack, the threat actors did gain access to production systems, so it is strongly advised that all AnyDesk users change their passwords. Furthermore, if they use their AnyDesk password at other sites, they should be changed there as well.
Every week, it feels like we learn of a new breach against well-known companies.
Last night, Cloudflare disclosed that they were hacked on Thanksgiving using authentication keys stolen during last years Okta cyberattack.
Last week, Microsoft also revealed that they were hacked by Russian state-sponsored hackers named Midnight Blizzard, who also attacked HPE in May.


Comments
Moonrider626 - 3 months ago
Boo hoo. This company hasn't done much to protect the people being scammed by it. Millions of dollars have been taken from our elderly citizens simply because this company allows anyone to use it, allowing them to manipulate victims computers and infinitely harass people into giving away everything they have in their bank accounts. Get rid of that distinction, my good friend, maybe I'll feel sorry for the people behind this company. But for now, I say: boo hoo.
Moonrider626 - 3 months ago
Perhaps I should be more exact. This software allows anyone to go on your computer and pose as anything they want over the phone through virus scam pop-ups. If you recieve a virus warning from the internet asking you to call a phone number. Simply close the browser window and start over, don't call anyone, they aren't text support, they are scammers from outside the country, most likely India or Nigeria. If all else fails, simply turn off your computer by holding down the power button until it shuts off, wait 5 seconds and turn it back on.
Moonrider626 - 3 months ago
The other way these guys get phone calls are from miss spelled google searches and searching for support from non official software, windows and hardware (such as printer) support. If you need support in this area I suggest researching reddit and find the answers you seek or finding their official websites and contacting them directly.
nickutis - 3 months ago
readers of this blog never call tech support scams so not sure why you explain us how to avoid grandma scams or fix computer by hard reboot lol
ftcm207 - 3 months ago
Can’t resist feeling schadenfreude about this story.
AnyDesk is FSF: full stack fubar — support, billing, web portal, security, management, executives, the software itself.
When TeamViewer raised my annual subscription rate by about 30% around 2 years ago, probably to pay for its insane sponsorship of soccer/football jerseys of Manchester United, I switched to Anydesk, another German company.
A few months ago, I ended my paid subscription with Anydesk after one year. It was a living hell of AnyDesk’s pathetic parade of negligence and gross incompetence on a scale I hadn’t seen for years. The app had bugs that prevented clicking default buttons on customer computers, but Anydesk finally fixed it, mostly.
As a new customer, I was forced by AnyDesk to use their beta customer portal, which was more like pre-alpha. It was missing lots of info and had wrong info for other things, and it wouldn’t let me disable autorenew within 30 days of renewal!!!, showed no payment method but AnyDesk still charged my original credit card when autorenew happened. They had unreachable billing support that required selecting one of 3 reasons, each of which led to info-only pages without a way to submit, and they had unreachable tech support that required using the old customer portal, which I couldn’t use because they forced me to use their new portal. They changed my license features without notice then I could no longer connect to more than one device simultaneously. I finally got my renewal refund after asking an Anydesk employee in the US who handles sales to relay info to his german bosses, who finally emailed me claiming they issued a refund, but after 16+ days they still hadn’t credited my card, so I complained to my state attorney general, which contacted AnyDesk legal, which suddenly responded but claimed I didn’t have standing because the state attorney dept handles consumer complaints but I’m a business, not a consumer. My US-based anydesk sales contact pushed his bosses again and got them to refund my money.
The CEO of anydesk is a move fast and break things kinda guy but that mantra isn’t appropriate for infrastructure and software tools, unlike social media nonsense that made that phrase famous.
One good thing about the experience is I stopped believing the stereotype of German efficiency and quality. Stereotypes aren’t good proxies for evaluating quality.
Splashtop SOS continues to be a stellar replacement. Thank goodness!
toughdude - 3 months ago
Remote Utilities is a viable alternative for me. It lacks any online (SaaS) account, essentially leaving nothing to be hacked. How can you hack a user database that doesn't exist?
However, the media will continue to laud TeamViewer and AnyDesk. Even now, some antivirus programs remain conspicuously silent about the outdated AnyDesk version signed with the compromised Philandro Software certificate.
Well, this speaks volumes about the current state of the 'security industry'. When remote software goes by names like 'TeamViewer' or 'AnyDesk', don't hold your breath for antivirus programs to take action, even if the software is an outright Trojan masquerading under these brands.
toughdude - 3 months ago
Quote:
"Certificates are usually not invalidated unless they have been compromised, such as being stolen in attacks or publicly exposed."
So it's been 2 days that AnyDesk issued this statement and NOT ONE of the so called 'antivirus software companies' did anything to prevent their customers from being hacked by malware which could possibly be signed with a stolen certificate. Here's virustotal report results for a file signed with Philandro Software certificate:
https://www.virustotal.com/gui/file/ec33d8ee9c3881b8fcea18f9f862d5926d994553aec1b65081d925afd3e8b028?nocache=1
Now this is all you need to know about the effectiveness of the 'antivirus solutions' that charge companies millions of dollars in license costs.
Once again:
1. A code signing certificate is compromised.
2. The company who owns it acknolwedged the fact but not yet revoked it (hmm, why?).
3. Two days are past.
4. Not a single 'antivirus software' marks the files as at least potentially dangerous.
NoneRain - 3 months ago
Uh, AV usually don't detect unsafe software as malicious. Imagine they did, and all piece of software with known vuls would be blocked on spot.... Some software wouldn't even be able to update to the patched version, since they would be blocked.
That said, VirusTotal scans are command-line scans, and don't represent the AV capabilities that might as well include vul scans, certs verification and such.
toughdude - 3 months ago
Quite the contrary, overall VirusTotal is more aggressive the off-the-shelf products. Quote from VirusTotal.com website:
"In VirusTotal, desktop-oriented solutions coexist with perimeter-oriented solutions; heuristics in this latter group may be more aggressive and paranoid, since the impact of false positives is less visible in the perimeter."
It is normal to see even a benign program with a lot of false positive detections when checked on VirusTotal. Just google 'virustotal false positive' and you'll see the scale of the problem.
megakotaro - 3 months ago
If the software get supply chain attack like solarwinds, which hacker change normal code to malicious code, the software will be flag as detected. If the code doesn’t change, it is still a clean file but has vulnerabilities.
toughdude - 3 months ago
The problem is - we don't know exactly when the breach occured. AnyDesk didn't give any information about that, they only acknolwedged the very fact of the breach taking place.
No one can guarantee now that there's no dormant backdoor now in their 'clean files', even those signed with the recently issued certificates. I may sound a bit alarmist/paranoid, maybe.
deltasierra - 3 months ago
No need to make this article about nationalism but anyone thinking any one country is significantly better than another at almost anything is a fool. Yes, Germans are known for efficiency, but people that love efficiency and execute it really well come from and work all around the world. Same with quality, same with engineering, and so on.
Anyways, we also abandoned TeamViewer when prices went up, and AnyDesk was already an obvious no-go at that time. So far, no complaints with Splashtop. Of course, everyone has their weaknesses, company culture problems or other organization softspots, etc. It's just surprising how strong the underdogs can be while market leaders get to hold on to that just by being there (it takes many years to upset that sort of thing in multi-billion dollar market spaces).
AnyDesk's old cert should be revoked NOW; when something is compromised, you don't wait, even if it does affect customers. Have mechanisms to force an update along with the message on why it's absolutely necessary... I mean, c'mon, this isn't 2017... haven't we learned anything??
toughdude - 3 months ago
The certificate has been already revoked by AnyDesk but the majority of "security industry" is still unaware except two engines (as of Feb 08, 2024):
https://www.virustotal.com/gui/file/ec33d8ee9c3881b8fcea18f9f862d5926d994553aec1b65081d925afd3e8b028?nocache=1
As one commentator noted earlier, they might be considering the file clean by just analyzing it for malicious code. But not doing anything about a file signed with a compromised and revoked certificate? Are you serious?