
A recently uncovered ransomware operation named 'Kasseika' has joined the club of threat actors that employs Bring Your Own Vulnerable Driver (BYOVD) tactics to disable antivirus software before encrypting files.
Kasseika abuses the Martini driver (Martini.sys/viragt64.sys), part of TG Soft's VirtIT Agent System, to disable antivirus products protecting the targeted system.
According to Trend Micro, whose analysts first discovered and examined Kasseika in December 2023, the new ransomware strain features many attack chains and source code similarities with BlackMatter.
As BlackMatter's source code has never been leaked publicly since its shutdown in late 2021, Kasseika was likely built by former members of the threat group or experienced ransomware actors who purchased its code.
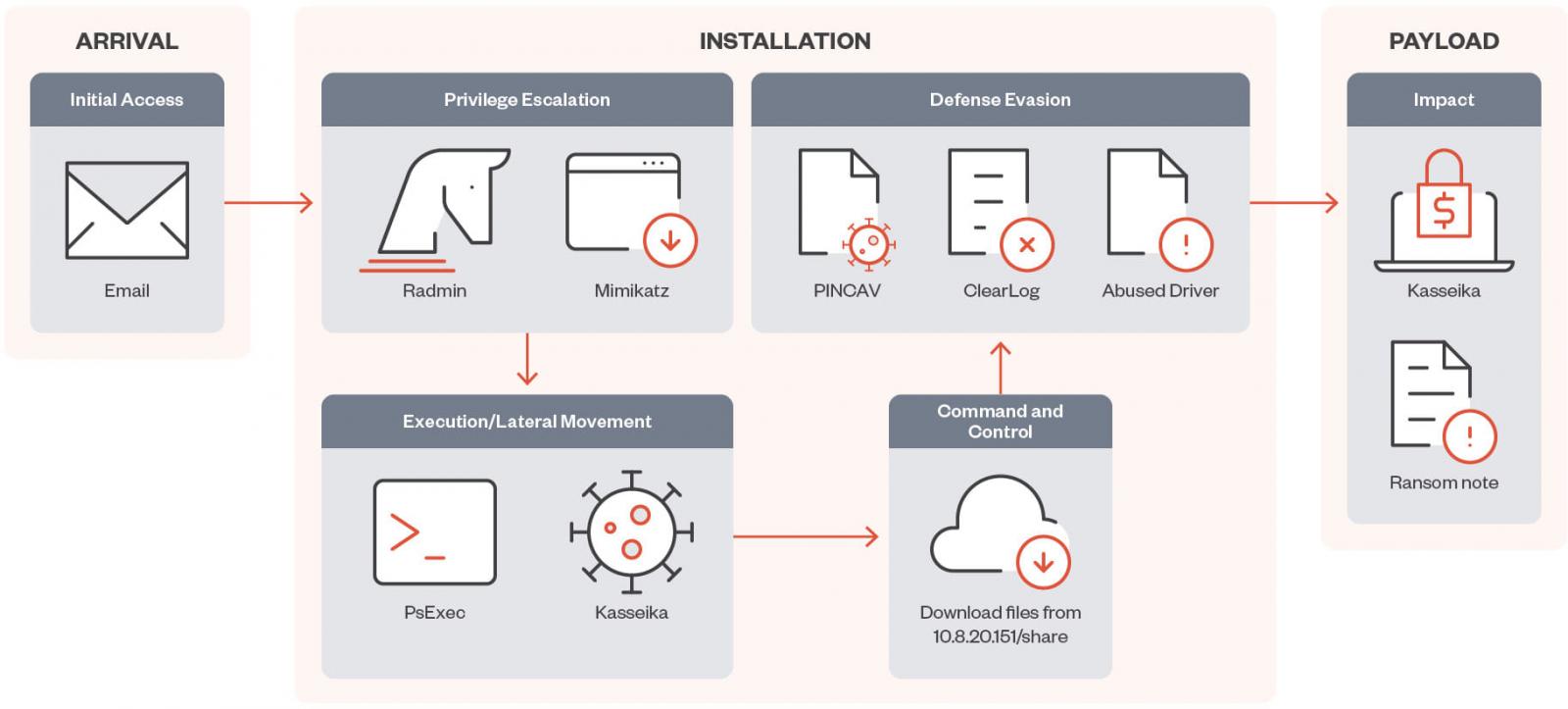
Kasseika attack chain
Kasseika attacks start with a phishing email sent to employees of the targeted organization, attempting to steal their account credentials, which will then be used for initial access to the corporate network.
Next, Kasseika operators abuse the Windows PsExec tool to execute malicious .bat files on the infected system and others they have accessed through lateral movement.
The batch file checks for the presence of a process named 'Martini.exe' and terminates it to avoid interference. Next, it downloads the vulnerable 'Martini.sys' driver on the machine.
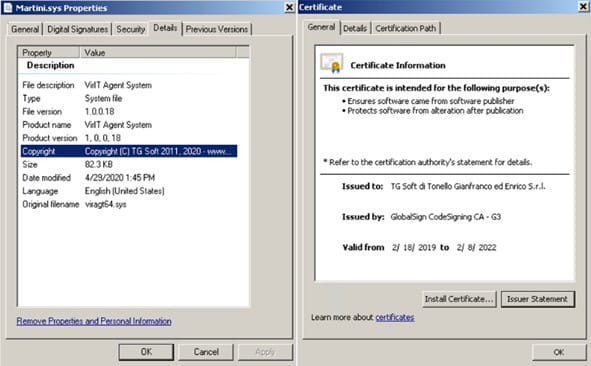
Source: Trend Micro
The presence of that driver is crucial in the attack chain, as Kasseika will not proceed further if the 'Martini' service creation fails or if 'Martini.sys' isn't found on the system.
By using BYOVD attacks, aka exploiting flaws in the loaded driver, the malware gains the privileges to terminate 991 processes from a hardcoded list, many of which correspond to antivirus products, security tools, analysis tools, and system utilities.
Kasseika eventually executes Martini.exe to terminate AV processes and then launches the main ransomware binary (smartscreen_protected.exe). After this, it runs a 'clear.bat' script to remove attack traces.
The ransomware utilizes the ChaCha20 and RSA encryption algorithms to encrypt target files, appending a pseudo-random string to the filenames, similar to BlackMatter.
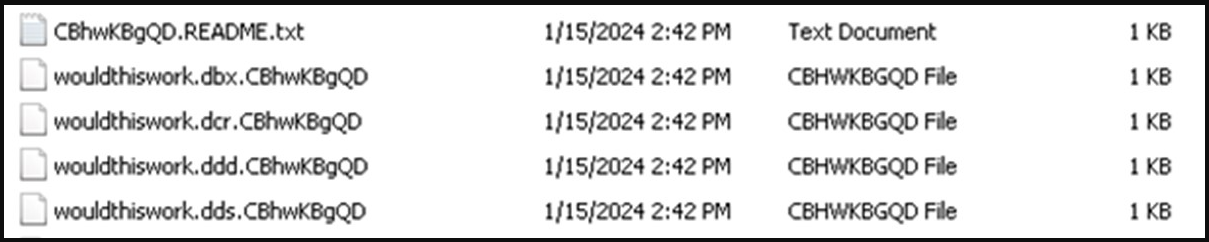
Source: Trend Micro
Kasseika drops a ransom note in every directory that it has encrypted and also changes the computer's wallpaper to display a note about the attack.
Source: Trend Micro
Finally, Kasseika clears system event logs post-encryption, using commands like 'wevutil.exe' to erase traces of its activities and make security analysis harder.
In the attacks seen by Trend Micro, victims were given 72 hours to deposit 50 Bitcoins ($2,000,000), with another $500,000 added every 24 hours of delay in resolution.
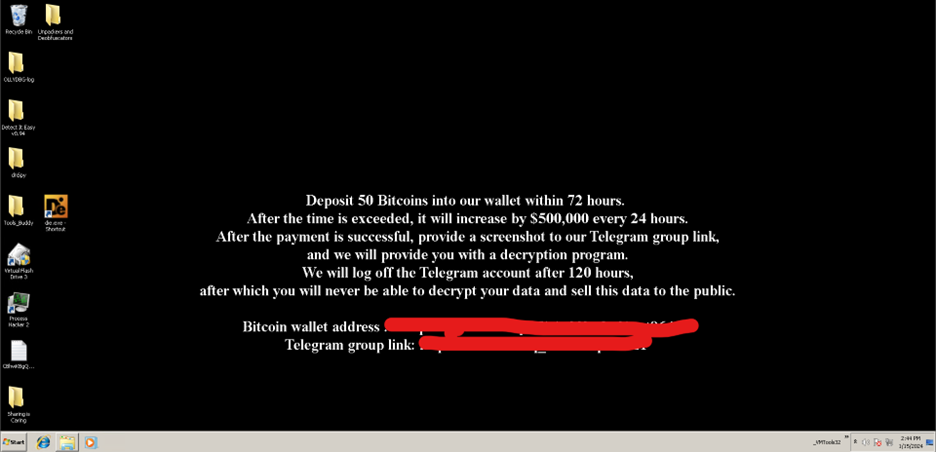
Source: Trend Micro
The victims are expected to post a screenshot of payment proof on a private Telegram group to receive a decrypter, with the maximum deadline for doing so set to 120 hours (5 days).
Trend Micro has published indicators of compromise (IoCs) related to the Kasseika threat separately in this text file.



Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now