
Anonfiles, a popular service for sharing files anonymously, has shut down after saying it can no longer deal with the overwhelming abuse by its users.
Anonfiles is an anonymous file-sharing site that allows people to share files anonymously without their activity being logged.
However, it soon became one of the most popular file-sharing services used by threat actors to share samples of stolen data, stolen credentials, and copyrighted material.
Five days ago, Anonfiles users began reporting that the service would time out when attempting to upload files.
As spotted by cybersecurity researcher g0njxa, the Anonfiles operators have now shut down the service, stating that their proxy provider recently shut them down and that they can no longer deal with the overwhelming amount of abusive material uploaded to the site.
The statement shown on Anonfiles site is reproduced in its entirety below:
"After trying endlessly for two years to run a file sharing site with user anonymity we have been tired of handling the extreme volumes of people abusing it and the headaches it has created for us.
Maybe it is hard to understand but after tens of million uploads and many petabytes later all work of handling abuse was automated through all available channels to be fast as possible.
We have auto banned contents of hundreds of thousands files.
Banned file names and also banned specific usage patterns connected to abusive material to the point where we did not care if we accidental delete thousands of false positive in this process.
Even after all this the high volume of abuse will not stop.
This is not the kind of work we imagine when acquiring it and recently our proxy provider shut us down.
This can not continue.
Domain 4sale.
domain@anonfiles.com"
While Anonfiles was a useful file-sharing site for many, other users reported [1, 2, 3] that the site used shady advertisers that commonly redirected malware, tech support scams, and unwanted Google Chrome and Firefox browser extensions.
For example, when attempting to download a file from Anonfiles, users said you would often be first redirected to a site that downloaded an ISO file using the same name as the file you thought you were downloading.
However, these ISO files contained various malware, including information-stealing malware, remote access trojans, and ad clickers.
In 2021, CronUp researcher Germán Fernández warned that Anonfiles malvertising was pushing the RedLine Stealer malware, a notorious information-stealing malware that steals your credentials and cryptocurrency wallets.
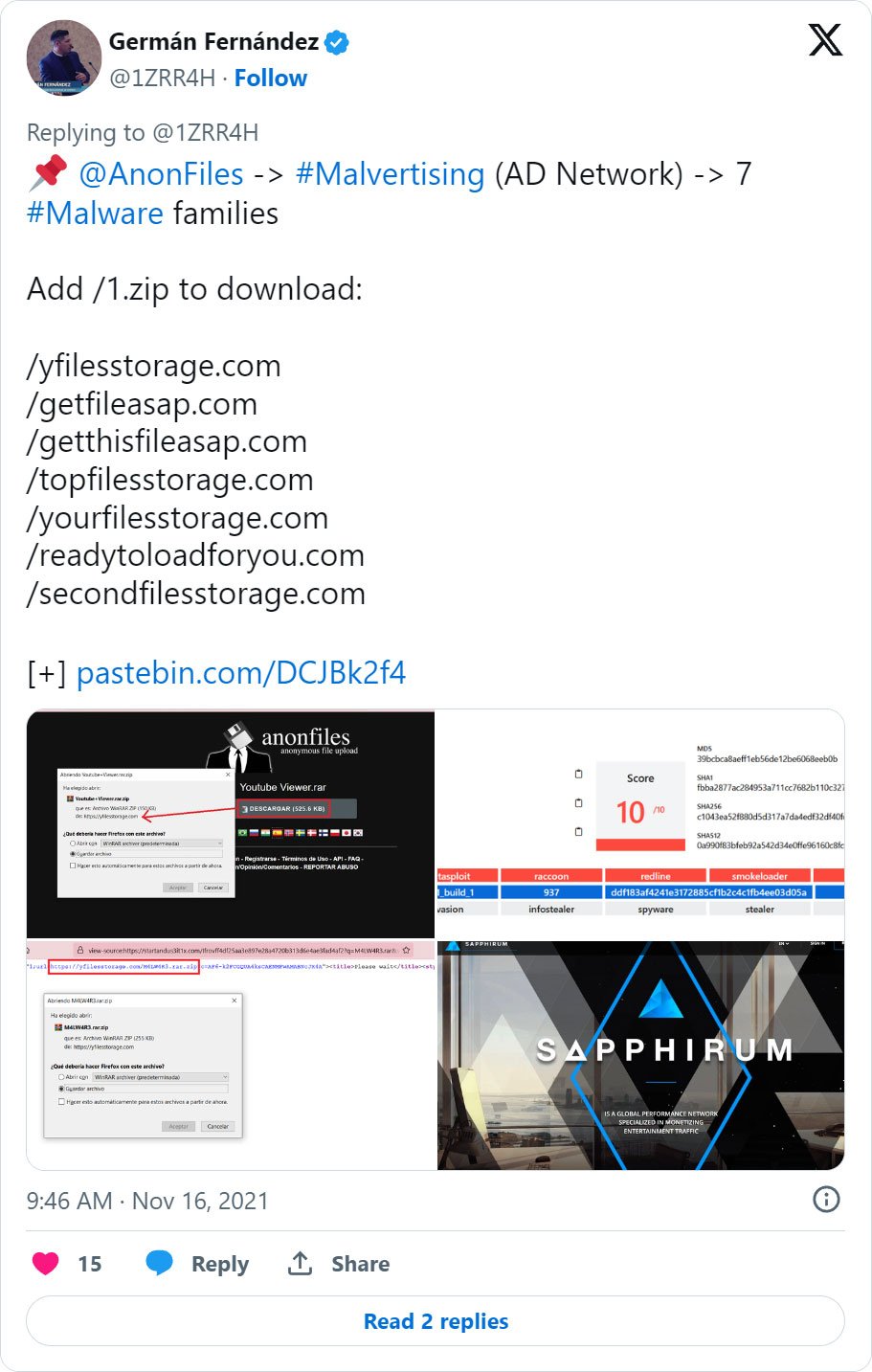
Other malvertising campaigns seen by Fernández and Malwarebytes on Anonfiles pushed search hijacking extensions, Amadey botnet, Vidar stealer, and even STOP ransomware.
The Anonfiles operators are now looking for someone to purchase their domain, likely to launch their own file sharing service.
However, in the interim, the shutdown will cause many files used by cybersecurity researchers and threat actors alike to no longer be available.

Comments
nauip - 9 months ago
Well, that was unexpected!
NoneRain - 9 months ago
Anon stuff is a double-edged sword. In recent years, it has being cutting more in the bad side.
The same goes for red-team tools made public.
EndangeredPootisBird - 9 months ago
Penetration testing was a mistake.
GT500 - 9 months ago
Penetration testing is never a mistake. It's an attempt to catch security vulnerabilities before they can be exploited by criminals.
EndangeredPootisBird - 9 months ago
Tell that to the thousands of companies and enterprises who got breached using open source penetration testing tools. They have done more harm than good.
GT500 - 9 months ago
Criminals can make their own tools. Without those tools, those companies would never know about security vulnerabilities and would never be able to close them. Those tools are vital to security, and so is penetration testing.
The reason these companies are being breached isn't because penetration testing tools exist, it's because they refuse to listen to their security people and actually properly secure their systems. Many companies will refuse to purchase the necessary hardware to block and detect network intrusions, and will refuse to make the necessary changes to their network. Many IT administrators also seem to think that obvious things (like not opening ports globally) aren't important, and leave company networks open to attack by sheer incompetence.
Blaming penetration testing tools for breaches of corporate networks is like blaming a screwdriver when someone gets stabbed in the eye with one. It's ludicrous.
h_b_s - 9 months ago
Not only can, they do make their own tools. But if they can just download a tool that does what they want, they will, just like a carpenter or cabinet maker will buy a hammer at the local hardware store rather than forging his own. It's just as absurd to force a tester to make all their own tools to test the integrity of their own, or their client's infrastructure as it is to force a carpenter to forge his own claw hammer before he can hammer a nail.
The vast majority of network intrusions don't include traditional penetration tools so outlawing penetration tools is foolish - nor will it stop their proliferation of such tools as the US discovered when they tried the same thing with classifying encryption as a weapon technology in the 90s. Attackers use social engineering and insider threats to harness naive workers, weak and reused credentials, and disgruntled workers to gain entry. Once that's accomplished the initial access is often sold to those buying off-the-shelf malware kits (note, not open source penetration tools) to create a monetization. Do you people even bother to read AND UNDERSTAND the articles on this website or are you just using them to shore up your preconceptions of how things should be according to yourself? Anyone that can write a Python script with a testing harness can trivially write their own credential brute force program. Since that's quite literally basic Python, even script kiddies can do it. So it doesn't matter if you can just download the program or write it yourself. Someone will, and then you have a penetration tool that's not a known quantity. In security terms, surprise is a bad thing.