
Threat actors behind the relatively new Venus Ransomware are hacking into publicly-exposed Remote Desktop services to encrypt Windows devices.
Venus Ransomware appears to have begun operating in the middle of August 2022 and has since encrypted victims worldwide. However, there was another ransomware using the same encrypted file extension since 2021, but it is unclear if they are related.
BleepingComputer first learned of the ransomware from MalwareHunterTeam, who was contacted by security analyst linuxct looking for information on it.
Linuxct told BleepingComputer that the threat actors gained access to a victim's corporate network through the Windows Remote Desktop protocol.
Another victim in the BleepingComputer forums also reported RDP being used for initial access to their network, even when using a non-standard port number for the service.
How Venus encrypts Windows devices
When executed, the Venus ransomware will attempt to terminate thirty-nine processes associated with database servers and Microsoft Office applications.
taskkill, msftesql.exe, sqlagent.exe, sqlbrowser.exe, sqlservr.exe, sqlwriter.exe, oracle.exe, ocssd.exe, dbsnmp.exe, synctime.exe, mydesktopqos.exe, agntsvc.exe, isqlplussvc.exe, xfssvccon.exe, mydesktopservice.exe, ocautoupds.exe, agntsvc.exe, agntsvc.exe, agntsvc.exe, encsvc.exe, firefoxconfig.exe, tbirdconfig.exe, ocomm.exe, mysqld.exe, mysqld-nt.exe, mysqld-opt.exe, dbeng50.exe, sqbcoreservice.exe, excel.exe, infopath.exe, msaccess.exe, mspub.exe, onenote.exe, outlook.exe, powerpnt.exe, sqlservr.exe, thebat64.exe, thunderbird.exe, winword.exe, wordpad.exe
The ransomware will also delete event logs, Shadow Copy Volumes, and disable Data Execution Prevention using the following command:
wbadmin delete catalog -quiet && vssadmin.exe delete shadows /all /quiet && bcdedit.exe /set {current} nx AlwaysOff && wmic SHADOWCOPY DELETE
When encrypting files, the ransomware will append the .venus extension, as shown below. For example, a file called test.jpg would be encrypted and renamed test.jpg.venus.
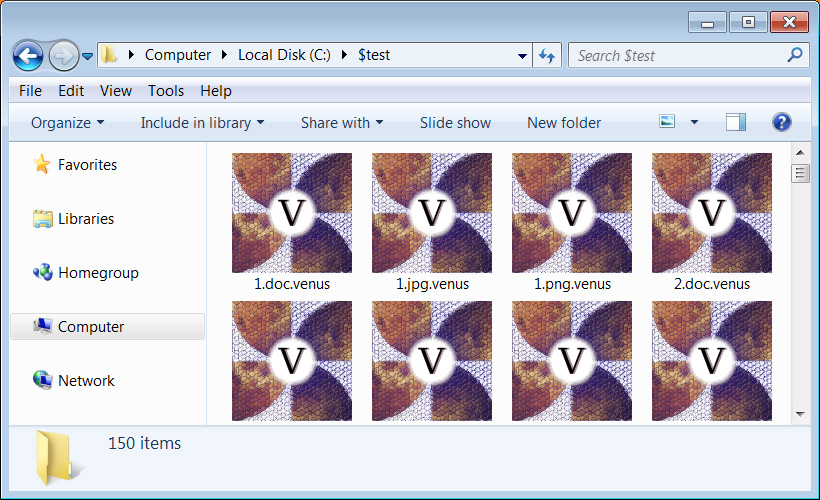
Source: BleepingComputer
In each encrypted file, the ransomware will add a 'goodgamer' filemarker and other information to the end of the file. It is unclear what this additional information is at this time.
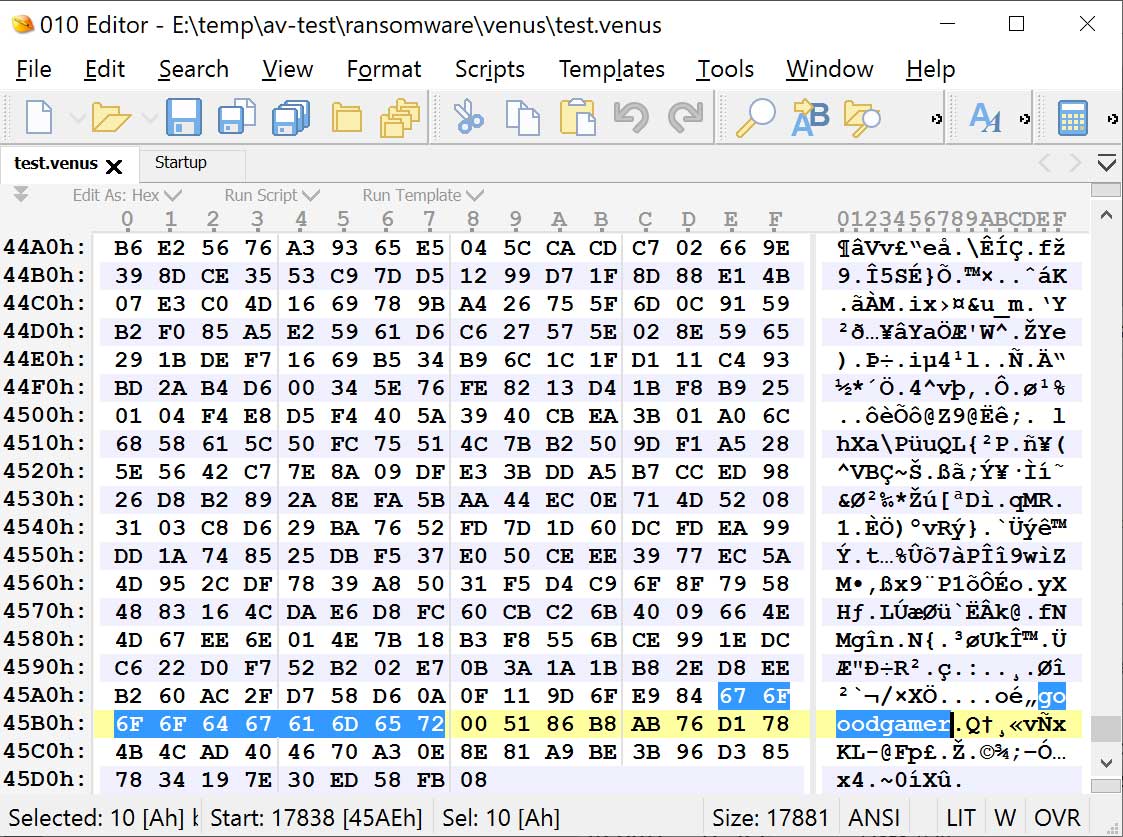
Source: BleepingComputer
The ransomware will create an HTA ransom note in the %Temp% folder that will automatically be displayed when the ransomware is finished encrypting the device.
As you can see below, this ransomware calls itself "Venus" and shares a TOX address and email address that can be used to contact the attacker to negotiate a ransom payment. At the end of the ransom note is a base64 encoded blob, which is likely the encrypted decryption key.
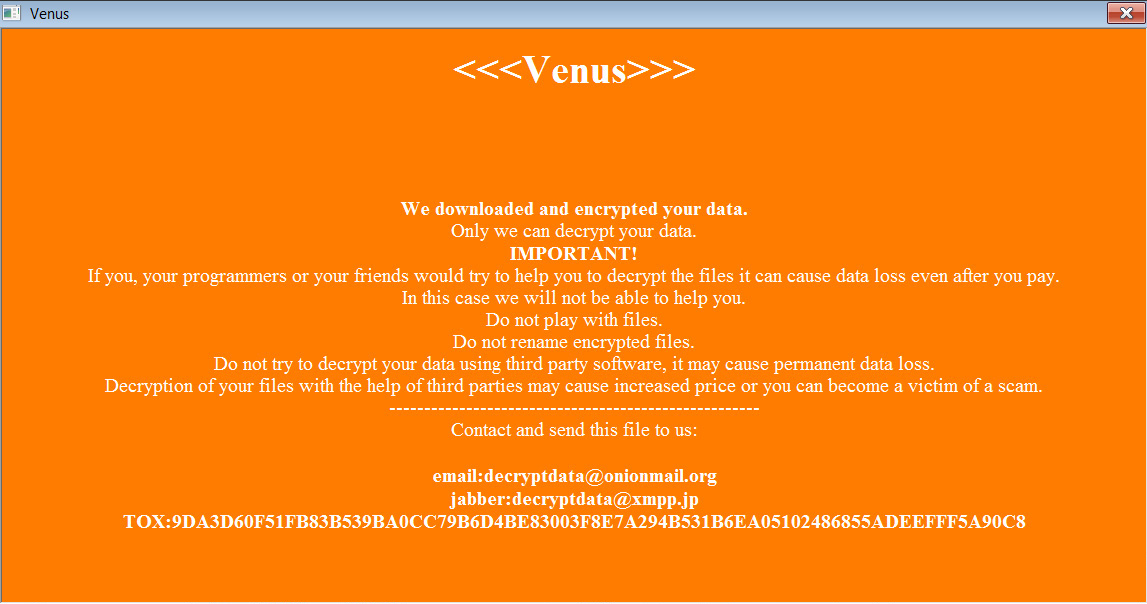
Source: BleepingComputer
At this time, the Venus ransomware is fairly active, with new submissions uploaded to ID Ransomware daily.
As the ransomware appears to be targeting publicly-exposed Remote Desktop services, even those running on non-standard TCP ports, it is vital to put these services behind a firewall.
Ideally, no Remote Desktop Services should be publicly exposed on the Internet and only be accessible via a VPN



Comments
Amigo-A - 1 year ago
This ransomware is spreading and has been known since May 2021.
https://id-ransomware.blogspot.com/2021/05/venus-ransomware.html
horsedoggs - 1 year ago
How is publicly exposed rdp still a thing? have people not heard of rd gateway, mfa and country based firewall rules…
EndangeredPootisBird - 1 year ago
Another example:
Why are large multi-national companies still employing device-based MFA despite having been inadequate for years and easy to bypass (like how we saw LAPSUS breaching their targets with MFA fatigue.)?
Litteraly every company is able to defend itself from all known attack vectors, they just choose not to for some strange reason, opting for ineffiecent security practices like VPN's, endpoint and identity security and ignoring all other attack vectors, while Zero Trust and hardware based MFA/Security Keys not only offer superiour security, but are also easier and cheaper to maintain.
The only proof you need is the time an group attempted to breach Cloudflare, only finding out its impossible as they employ security keys for authentication https://www.bleepingcomputer.com/news/security/cloudflare-employees-also-hit-by-hackers-behind-twilio-breach/
While Twilio, who were employing device-based MFA, were breached by the same group
https://www.bleepingcomputer.com/news/security/twilio-discloses-data-breach-after-sms-phishing-attack-on-employees/
TsVk! - 1 year ago
Another day, another RDP attack...
It's like the bad old days with Flash Player. :P