MetaMask has published a warning for their iOS users about the seeds of cryptocurrency wallets being stored in Apple's iCloud if app data backup is active.
MetaMask is a “hot” cryptocurrency wallet used by over 21 million investors to store their wallet tokens and manage their digital assets.
In cryptocurrency lingo, a seed is a secret recovery phrase consisting of 12 words that protect access to the wallet's content.
Storing the wallet seed in iCloud practically means that if an owner has their Apple account compromised, their digital assets are also at risk.
If you have enabled iCloud backup for app data, this will include your password-encrypted MetaMask vault. If your password isn’t strong enough, and someone phishes your iCloud credentials, this can mean stolen funds. (Read on ) 1/3
— MetaMask (@MetaMask) April 17, 2022
Real phishing case
Unfortunately, the scenario above was already used against at least one MetaMask user who has lost over $655k as a result of a well-crafted phishing attack.
1/ On April 15th, @revive_dom received multiple text messages asking to reset his Apple ID password and at 6:32 PM he received a call from "Apple Inc." which was a spoofed caller ID.
— Serpent (@Serpent) April 17, 2022
They claimed that there was suspicious activity on his Apple ID and they asked for a one-time pic.twitter.com/fc8lSntgyP
The target received multiple text messages asking to reset his Apple account and the attacker then followed up with a call from a spoofed Apple Inc. number pretending to be the firm’s support agents investigating suspicious activity on his account.
The victim followed the instructions and provided the fake support agents the six-digit verification code received from Apple. Soon, his MetaMask wallet was emptied.
The hackers had already requested one final Apple account password reset and all they needed was the additional verification to access the victim's iCloud data where the MetaMask seed was backed up. This allowed them to steal $655,388 worth of crypto.
What to do
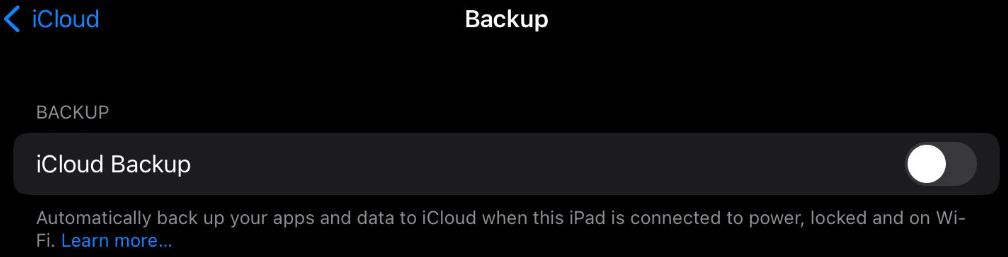
To keep your digital assets safe from such tricky attacks, make sure to exclude MetaMask from iCloud backups via Settings > Profile > iCloud > Manage Storage > Backups.
The two-factor authentication code is a temporary secret that should not be shared with anyone, regardless how convincing a call, email, or SMS may appear. Official representatives would never ask for it.
Additionally, cryptocurrency users can keep their assets safer in a cold wallet if they're not actively trading them instead of the MetaMask hot wallet.
Finally, keeping your investments out of social media and other public channels make you less of a target as hackers are keeping an eye for fresh, high-value victims.



Comments
tcallaha - 2 years ago
I can’t believe how many of these stories where the headlines sound like the hackers actually broke into something actually turn out to be entirely preventable social engineering attacks where a little common sense would have prevented it. The headline makes it sound like MetaMask and/or Apple did something wrong or the hackers broke into a system somewhere, but there is absolutely nothing “hacky” about this. The fault here lies entirely with the gullibility and lack of skepticism on the part of the user.
This was like if someone walked up to you and said “Hey I think your car is broken can I have your keys to check?” And then you gave them the keys and they drive off with it.
If you’re technically savvy enough to invest in crypto, you should be able to recognize this kind of thing!
yawnshard - 2 years ago
Quote: "iCloud content, as it exists in the customer's account, may be provided in response to a search warrant issued upon a showing of probable cause, or customer ..."
Besides a dumbphone where any cop can force your finger or face in front of the unlock sensors is nothing for crypto. "tech savvy" don't use phones, they use desktops with dm-crypt/LUKS.
And given the amount of unlawful search warrants I'm siding with the innocents here.
diligiant - 2 years ago
MetaMask is trying to cover its tracks as the keychain offer ways to flag data as only restorable to the same device (using 1 of 3 kSecAttrAccessible_ThisDeviceOnly).
They should fix their security design flaw instead of blaming others!
https://developer.apple.com/documentation/security/ksecattraccessibleafterfirstunlockthisdeviceonly