Threat actors are using stolen NVIDIA code signing certificates to sign malware to appear trustworthy and allow malicious drivers to be loaded in Windows.
This week, NVIDIA confirmed that they suffered a cyberattack that allowed threat actors to steal employee credentials and proprietary data.
The extortion group, known as Lapsus$, states that they stole 1TB of data during the attack and began leaking the data online after NVIDIA refused to negotiate with them.
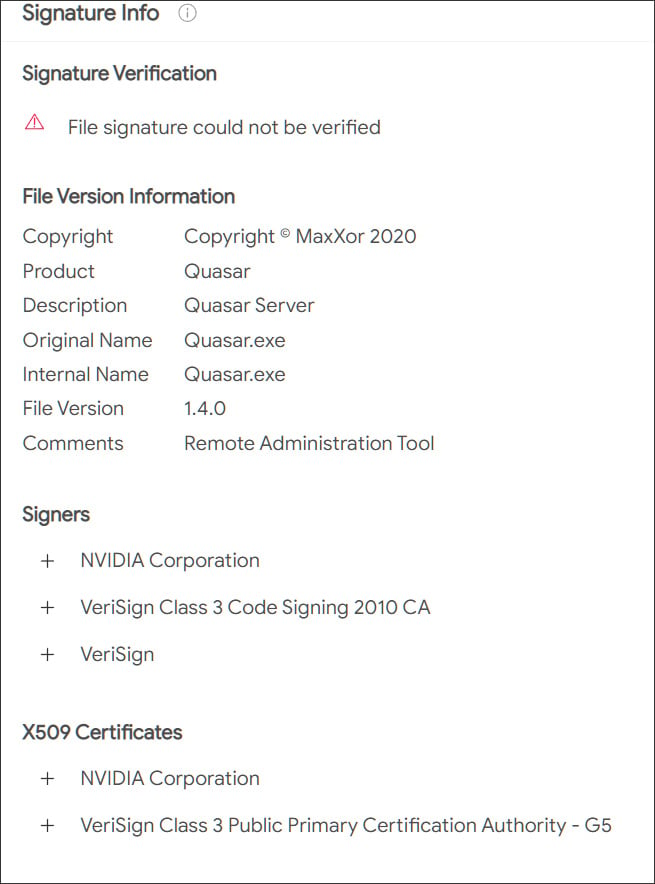
The leak includes two stolen code-signing certificates used by NVIDIA developers to sign their drivers and executables.
As part of the #NvidiaLeaks, two code signing certificates have been compromised. Although they have expired, Windows still allows them to be used for driver signing purposes. See the talk I gave at BH/DC for more context on leaked certificates: https://t.co/UWu3AzHc66 pic.twitter.com/gCrol0BxHd
— Bill Demirkapi (@BillDemirkapi) March 3, 2022
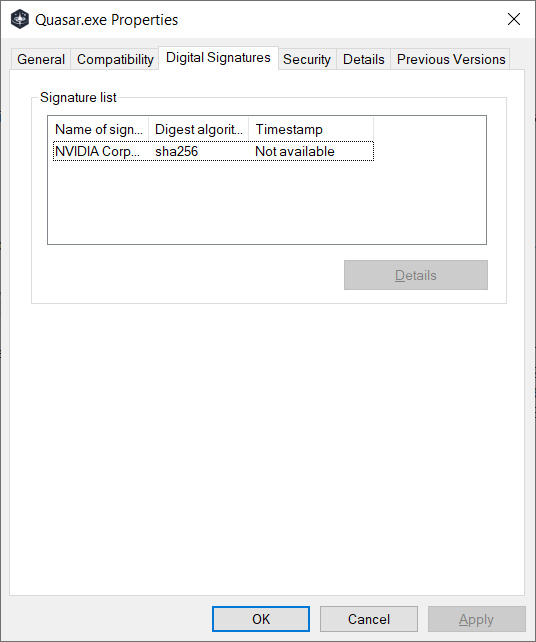
A code-signing certificate allows developers to digitally sign executables and drivers so that Windows and end-users can verify the file's owner and whether they have been tampered with by a third party.
To increase security in Windows, Microsoft also requires kernel-mode drivers to be code signed before the operating system will load them.
NVIDIA certificates used to sign malware
After Lapsus$ leaked NVIDIA's code-signing certificates, security researchers quickly found that the certificates were being used to sign malware and other tools used by threat actors.
According to samples uploaded to the VirusTotal malware scanning service, the stolen certificates were used to sign various malware and hacking tools, such as Cobalt Strike beacons, Mimikatz, backdoors, and remote access trojans.
For example, one threat actor used the certificate to sign a Quasar remote access trojan [VirusTotal], while someone else used the certificate to sign a Windows driver [VirusTotal].
Security researchers Kevin Beaumont and Will Dormann shared that the stolen certificates utilize the following serial numbers:
43BB437D609866286DD839E1D00309F5
14781bc862e8dc503a559346f5dcc518
Some of the files were likely uploaded to VirusTotal by security researchers but others appear to be used by threat actors for malware campaigns [1, 2].
While both stolen NVIDIA certificates are expired, Windows will still allow a driver signed with the certificates to be loaded in the operating system.
Therefore, using these stolen certificates, threat actors gain the advantage of making their programs look like legitimate NVIDIA programs and allowing malicious drivers to be loaded by Windows.
To prevent known vulnerable drivers from being loaded in Windows, David Weston, director of enterprise and OS security at Microsoft, tweeted that admins can configure Windows Defender Application Control policies to control what NVIDIA drivers can be loaded.
WDAC policies work on both 10-11 with no hardware requirements down to the home SKU despite some FUD misinformation i have seen so it should be your first choice. Create a policy with the Wizard and then add a deny rule or allow specific versions of Nvidia if you need
— David Weston (DWIZZZLE) (@dwizzzleMSFT) March 3, 2022
However, using WDAC is not an easy task, especially for non-IT Windows users.
Due to the potential for abuse, it is hoped that the stolen certificates will be added to Microsoft's certificate revocation list in the future to prevent malicious drivers from loading in Windows.
However, doing so will cause legitimate NVIDIA drivers to be blocked as well, so we will likely not see this happening soon.



Comments
yawnshard - 2 years ago
1) Hard: If the higher up CA in the chain would check if someone is trying to sign with an expired or revoked cert this wouldn't happen.
2) Easy: If companies kept their certs on a dedicated HSM or smart card this wouldn't happen.
Security policies exist for a reason. Why does a 300 people company manage to pull it off, but a 500 billion USD one fails to do so?
Edit, one more rant:
Malware scanners that skip signed files obviously never heard of supply chain attacks.
buzzword - 2 years ago
My guess would be that they're waiting until they can push newly signed drivers via Windows update before revoking the stolen certificates. If not, then welcome to Microsoft security theater, where the entire driver signing process is a useless joke.
Kevanstech - 2 years ago
As always there are issues with signed drivers.
1. If you have a graphics card that is deemed as "Obsolete" the certificate will be an old certificate and revoking the certificate will effectively stop lots of working graphics cards.
2. if a company goes out of business then no new certificate and no working device.
If the certificate was counter signed by a microsoft certificate or other software verification service (if there is one), then you could work out which driver is more likely to be fraudulent because only the good one will be signed twice. This service is likely to charge and so it is also likely not to be used by everyone.
vijoj89688 - 2 years ago
Both the certificates have not been revoked, at least as on 23rd Mar 2022!! You can recheck here:
43BB437D609866286DD839E1D00309F5 = https://crt.sh/?id=369243575&opt=ocsp
14781bc862e8dc503a559346f5dcc518 = https://crt.sh/?id=158868919&opt=ocsp
Welcome to the Jungle ...