
The Hive ransomware gang is more active and aggressive than its leak site shows, with affiliates attacking an average of three companies every day since the operation became known in late June.
Security researchers gleaning information straight from Hive’s administrator panel found that affiliates had breached more than 350 organizations over four months.
The gang’s data leak site currently lists only 55 companies that did not pay the ransom, suggesting that a large number of Hive ransomware victims paid the ransom.
A conservative estimation places Hive ransomware gang’s profits into millions of U.S. Dollars between October and November alone.
Recruiting partners
Hive ransomware emerged in late June targeting companies in various sectors. While most of the non-paying victims on their leak site are small to medium-sized businesses, the gang also published files from larger companies with revenues assessed to be in the hundreds of millions.
A source has told BleepingComputer that Hive ransomware is also behind the recent attack on Virginia’s Division of Legislative Automated Systems (DLAS). However, we could not independently verify the information.
Analysts at cybersecurity company Group-IB investigating the Hive ransomware-as-a-service (RaaS) operation discovered that the group is “one of the most aggressive ones,” its affiliates hitting at least 355 companies by October 16.
The first publicly known attack from this gang was on June 23, against Canadian IT company Altus Group. At that time, it was unclear if Hive was a RaaS operation open to other cybercriminals.
Things became clear in early September when the group, through a user known as “kkk,” replied in a thread on “reputable” ransomware programs that they were looking for partners that already had access to company networks.
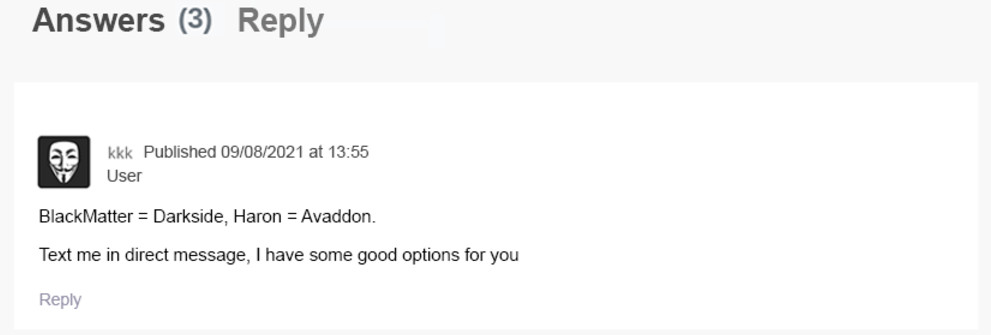
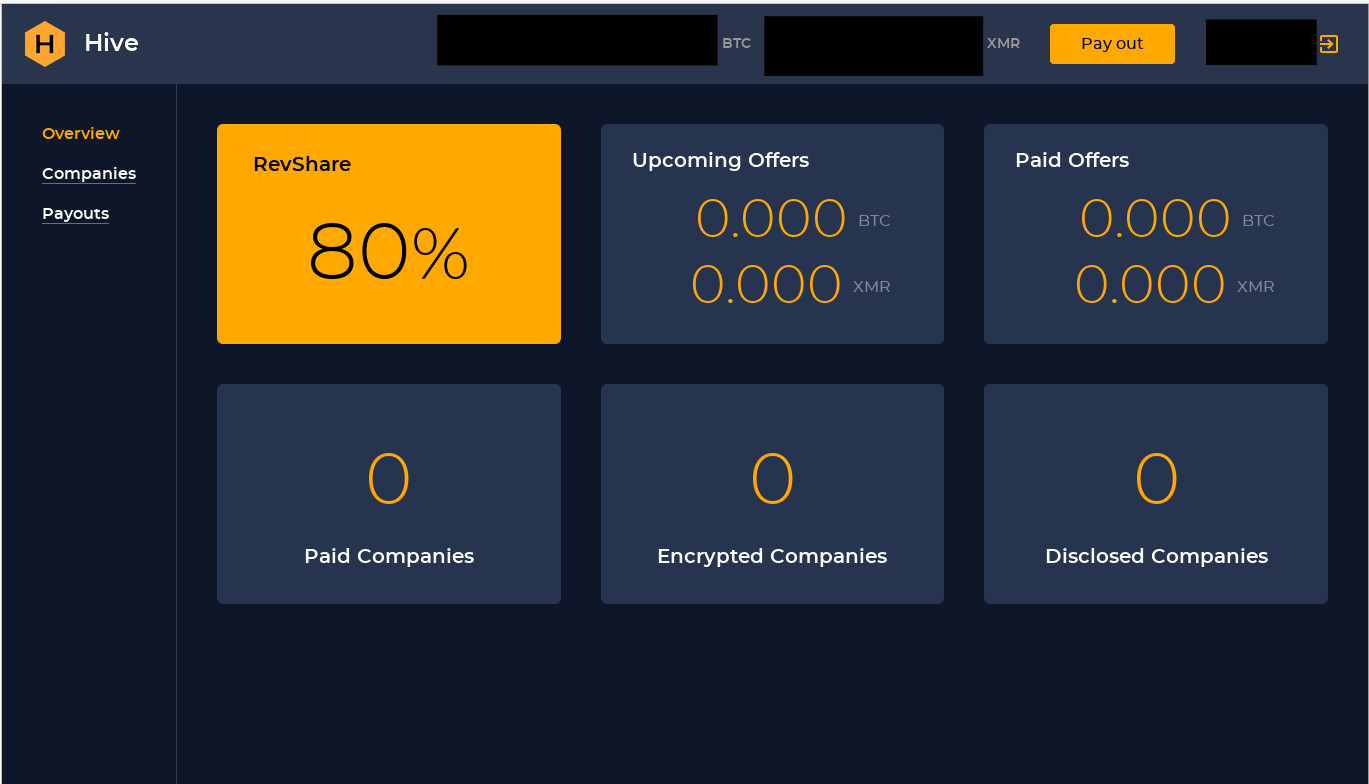
The message also included details about splitting the ransom money: 80% for affiliates, 20% for the developers.
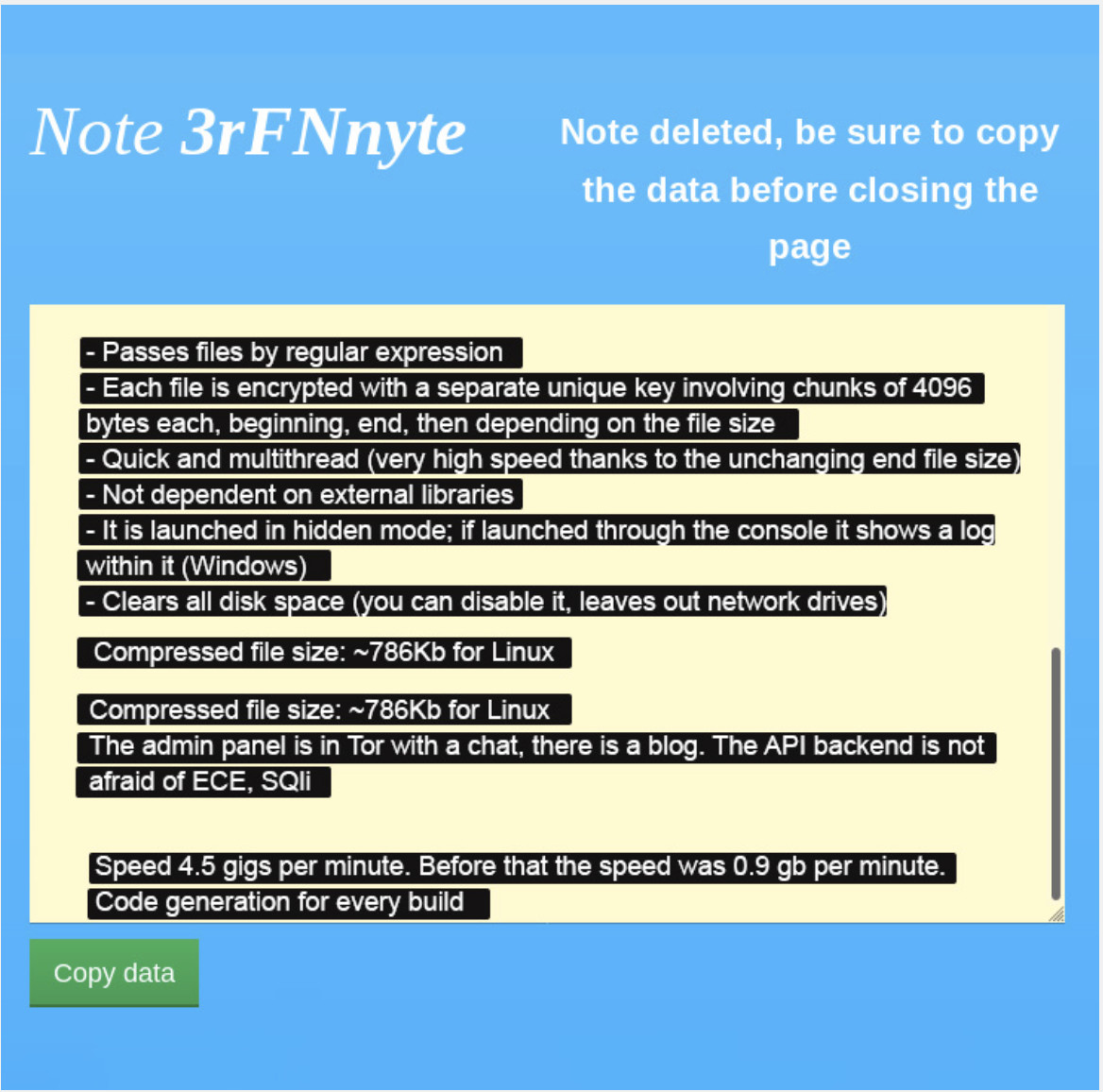
The same user also provided technical information about the file-encrypting malware in a self-destructing note captured by Group-IB researchers.
Although “kkk” did not name the RaaS they were representing, the researchers say that the technical details provided made it clear that the actor was referring to Hive ransomware.
Behind the Hive ransomware curtains
Group-IB obtained access to the Hive ransomware admin panel and started to collect information about the operation and how it worked.
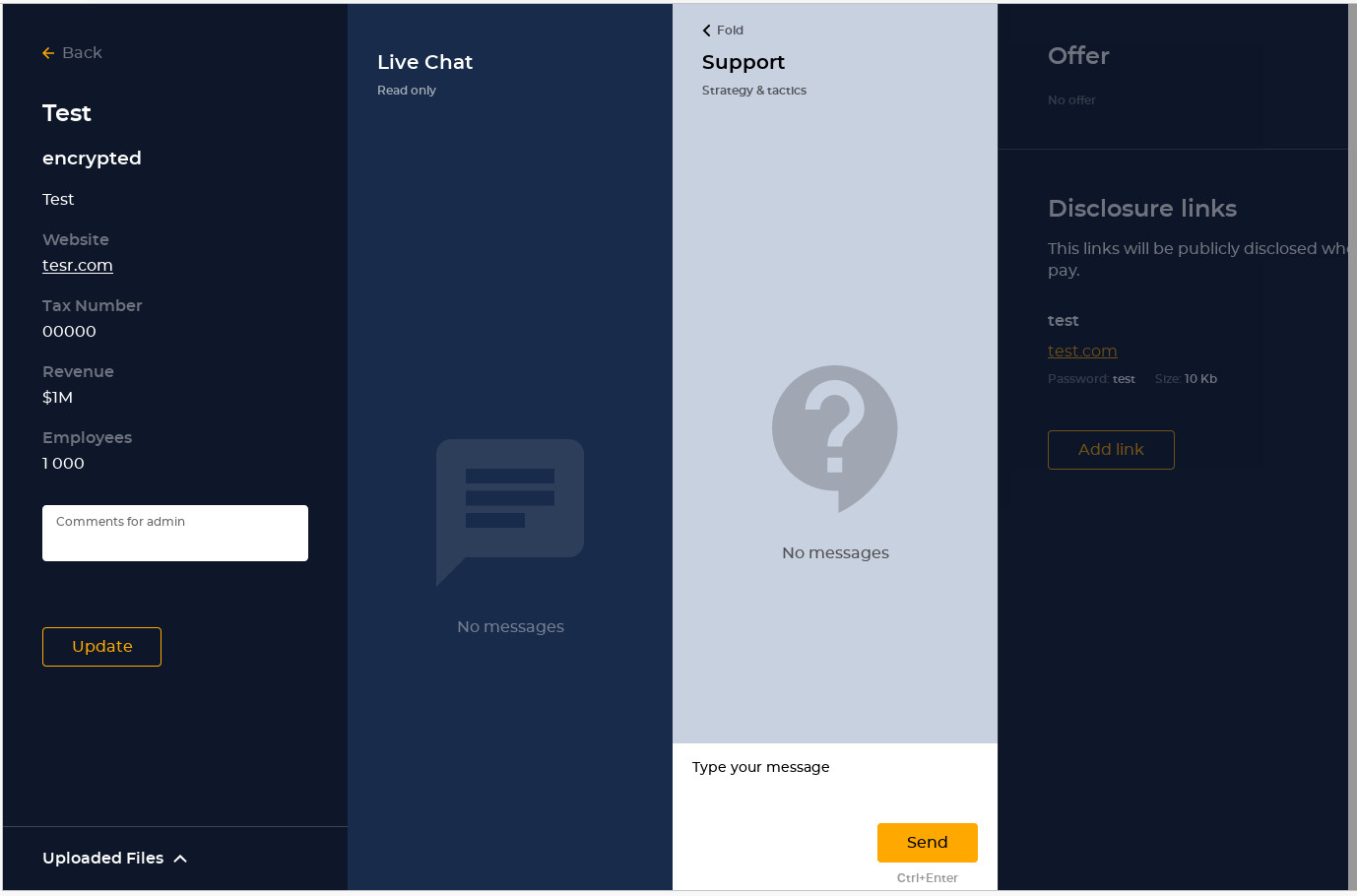
It appears that the developers set everything up to make ransomware deployment and negotiations with the victims as easy and transparent as possible.
Affiliates can generate a malware version in up to 15 minutes and negotiations run via Hive ransomware admins, who pass the message to the victim in a chat window also visible to affiliates.
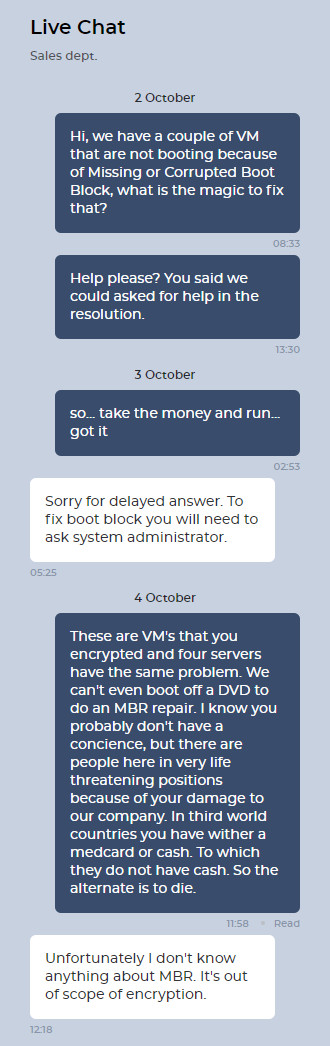
Although the decryption software is provided after paying the ransom, some companies complained that the tool was not working properly and corrupted the Master Boot Record of virtual machines, making them non-bootable.
In a report shared with BleepingComputer, Group-IB notes that the Hive ransomware administration panel shows affiliates how much money they made, the companies that paid and those that had their data leaked, and lets them store profiles for targeted businesses.
The researchers found that all affiliates have access to the company IDs in the Hive ransomware database, which is rather unusual.
Furthermore, the admin panels and the leak site are running through an API (Application Programming Interface), which Group-IB says has been seen with only two other ransomware groups: Grief and DoppelPaymer.
Looking closer at the API, the researchers found an error that allowed them to glean information about all Hive ransomware attacks, which also let them gauge how many companies paid these attackers.
According to their assessment, the threat actor hit 355 organizations by October 16; 104 victims negotiated with the attackers.
“Based on the analysis of company data obtained through API, the number of victims grew by 72% in less than one month. On September 16, the total number of records related to victim companies was 181. Just one month later, on October 16, the number increased to 312. Notably, 43 companies listed as victims in September disappeared from API in October, most likely after paying the ransom” - Group-IB
As for the money extorted from victims, Group-IB told BleepingComputer that they estimate the gang made at least $6.5 million from October to November.
Group-IB’s research into the ransomware business, recently published in the company’s recent report called “Corporansom: threat number one,” shows that about 30% of the victims choose to pay the threat actor.
Despite being more active than initially believed, Hive ransomware relies on common initial compromise methods, which include the following:
- vulnerable RDP servers
- compromised VPN credentials
- phishing emails with malicious attachments
The attackers also deploy the encryption stage of the attack during non-working hours or over the weekend, which is typical for most ransomware attacks.



Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now