
The complete source code for the Paradise Ransomware has been released on a hacking forum allowing any would-be cyber criminal to develop their own customized ransomware operation.
Released on the hacking forum XSS, the link to the source code is only accessible to active users on the site who have previously replied to or reacted to other posts on the site.
Security Joes researcher Tom Malka, who shared the source code with BleepingComputer, compiled the package and found it creates three executables - a ransomware configuration builder, the encryptor, and a decryptor.
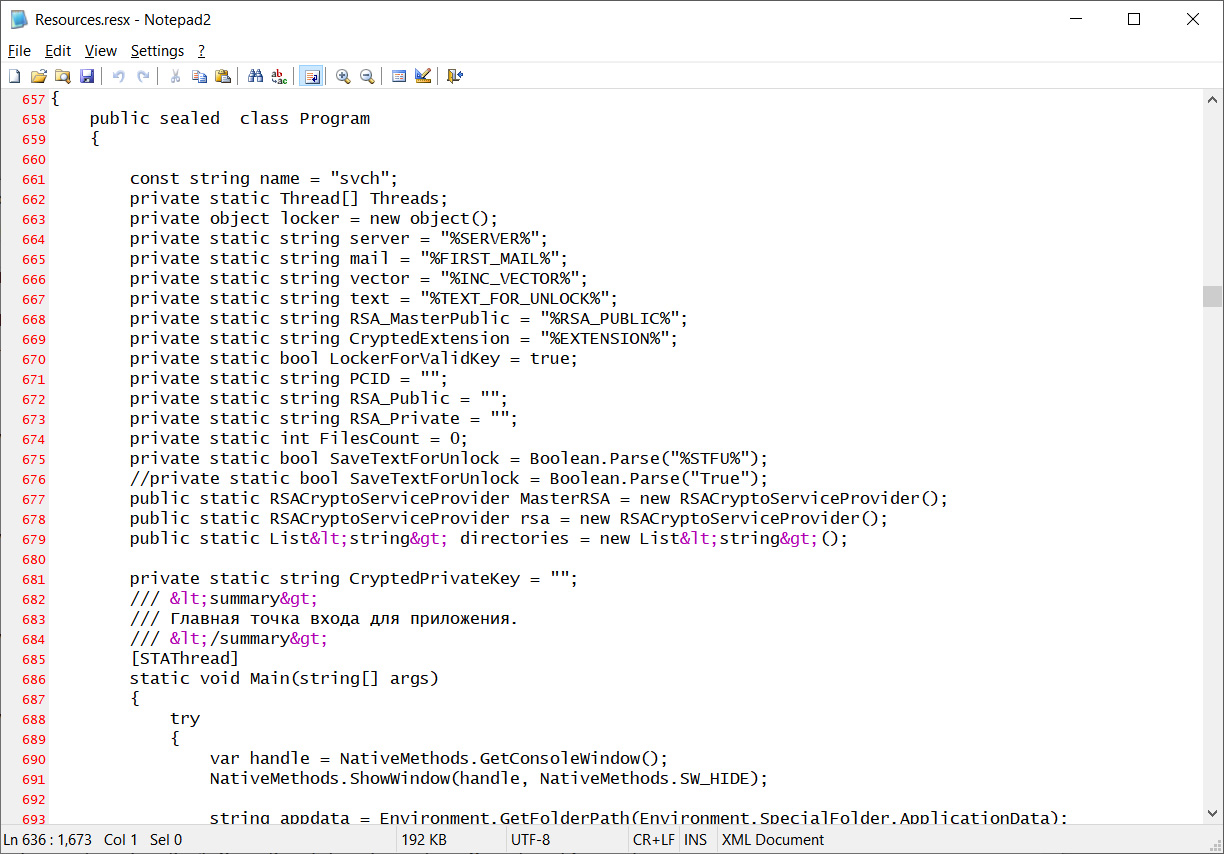
Sprinkled throughout the source code are Russian comments, shown above, that clearly demonstrate the native language of the developer.
A Paradise ransomware affiliate can use the builder to customize their own version of the ransomware to include a custom command and control server, encrypted file extension, and contact email address.
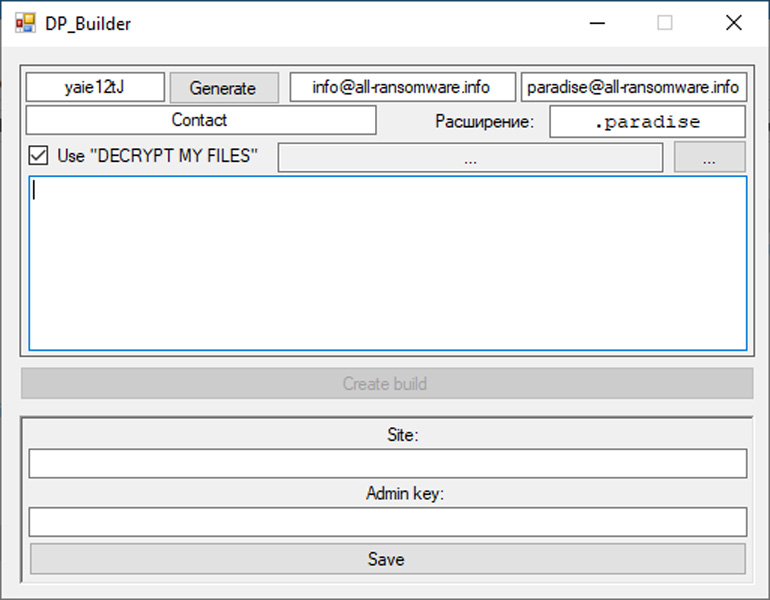
Once the customized ransomware is created, affiliates can distribute the malware in their campaigns to target victims.
Welcome to Paradise
The Paradise Ransomware operation first launched in September 2017 through phishing emails containing malicious IQY attachments that downloaded and installed the ransomware.
Over time, multiple versions of the ransomware were released, with initial versions containing flaws that led to the release of a Paradise Ransomware decryptor.
However, the new versions switched the encryption method to RSA, which prevented the free decryption of files.
Michael Gillespie, who created the original Paradise Ransomware decryptor, told BleepingComputer that the versions of Paradise that were released include:
- Paradise - Native version that had the flaws allowing decryption.
- Paradise .NET - A secure .NET version that switched encryption algorithms to use RSA encryption.
- Paradise B29 - A "Team" variant that only encrypted the end of a file.
Gillespie said that it is not clear if they were all developed by the same group as they were all circulating at around the same time with thousands of different extensions, as threat actors flocked to the growing Ransomware-as-a-Service.
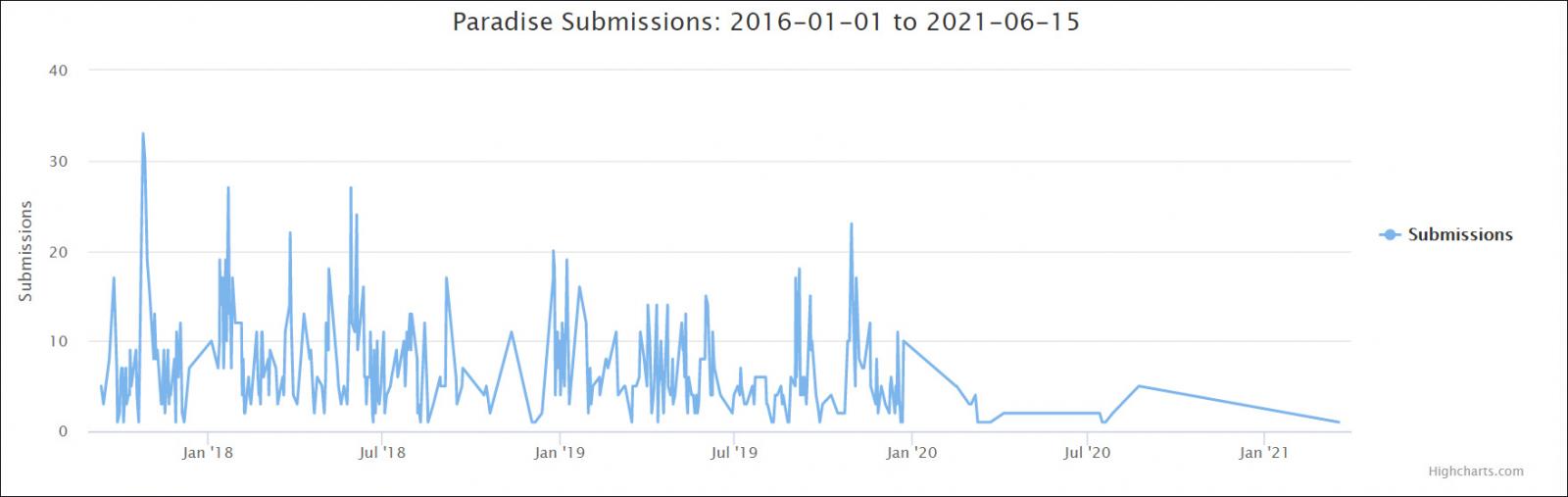
Based on submissions statistics to ID Ransomware, the Paradise Ransomware was heavily distributed between September 2017 and January 2020, when it suddenly tapered off until now, where it is rarely seen.
Unfortunately, Gillespie tells BleepingComputer that the source code is for the secure version of Paradise Ransomware that utilizes RSA encryption to encrypt files.
Using this source code, other threat actors can easily modify it to release their own customized version of the ransomware, allowing an easy entry point into creating a new ransomware operation.



Comments
Without_A_Monitor - 2 years ago
just to ask, when the article reads as "...clearly demonstrate the native language of the developer," is it not possible for one language to be used to appear like the "native language" when it isn't in order to deceive and further hide the identities of the developer(s)? With that said, if there is more info on the developer(s) and his/her identities (e.g. nationality, ethnicity,) that is helpful and different, but as is, any language can be used in order to feign like it's someone's "native language."
Amigo-A - 2 years ago
Distribution source: Ukraine. Ransomware Team: Paradise Ransomware Team.
This is known from the very beginning of distribution.
After a time, actors from any country can join. And so it was done.
Without_A_Monitor - 2 years ago
much obliged for the reply and info. so, when you type, "the distribution source" is that the exact same as the "developer?" My (mis)understanding is that it is not. One provides while the other creates, but perhaps, I am misunderstanding. Also, Ukraine is not Russia, nor Russia is Ukraine, not that you aren't already aware. There is much history between the two countries and ethnicities that consists of conflict and tension.
Amigo-A - 2 years ago
There was another public option in January 2021.
Dominique1 - 2 years ago
I agree that program comments are not an indication of the developer's origin. It's more an indication of who the operators are. As for the variable style, I would assume that the developer speaks English fluently.
Lawrence Abrams - 2 years ago
Why would Russian comments in source code be an indication of who the operators are rather than the developer?
Amigo-A - 2 years ago
Operators can be recruited legally, even through public announcements. They may not know who they are serving. If they get paid on time, they won't even try to figure out what their employer is doing.
There are many such firms in some European countries. They hire people from different countries, they may even know Russian. They can be from any country in Eastern Europe, Kazakhstan, Belarus, Ukraine and other countries of the former USSR.
At the request of the boss, they can pretend to be Russians, so that everyone thinks that it is Russia that attacks all computers in the world. The media, willingly or unwillingly, will help spread this lie. In fact, the share of Russian extortions is very, very small, especially if they often work in an international group.