
A Razer Synapse zero-day vulnerability has been disclosed on Twitter, allowing you to gain Windows admin privileges simply by plugging in a Razer mouse or keyboard.
Razer is a very popular computer peripherals manufacturer known for its gaming mouses and keyboards.
When plugging in a Razer device into Windows 10 or Windows 11, the operating system will automatically download and begin installing the Razer Synapse software on the computer. Razer Synapse is software that allows users to configure their hardware devices, set up macros, or map buttons.
Razer claims that that their Razer Synapse software is used by over 100 million users worldwide.
Security researcher jonhat discovered a zero-day vulnerability in the plug-and-play Razer Synapse installation that allows users to gain SYSTEM privileges on a Windows device quickly.
SYSTEM privileges are the highest user rights available in Windows and allow someone to perform any command on the operating system. Essentially, if a user gains SYSTEM privileges in Windows, they attain complete control over the system and can install whatever they want, including malware.
After not receiving a response from Razer, jonhat disclosed the zero-day vulnerability on Twitter yesterday and explained how the bug works with a short video.
Need local admin and have physical access?
— jonhat (@j0nh4t) August 21, 2021
- Plug a Razer mouse (or the dongle)
- Windows Update will download and execute RazerInstaller as SYSTEM
- Abuse elevated Explorer to open Powershell with Shift+Right click
Tried contacting @Razer, but no answers. So here's a freebie pic.twitter.com/xDkl87RCmz
Getting SYSTEM privileges by plugging in a mouse
As BleepingComputer has a Razer mouse available, we decided to test out the vulnerability and have confirmed that it took us about two minutes to gain SYSTEM privileges in Windows 10 after plugging in our mouse.
It should be noted that this is a local privilege escalation (LPE) vulnerability, which means that you need to have a Razer devices and physical access to a computer. With that said, the bug is so easy to exploit as you just need to spend $20 on Amazon for Razer mouse and plug it into Windows 10 to become an admin.
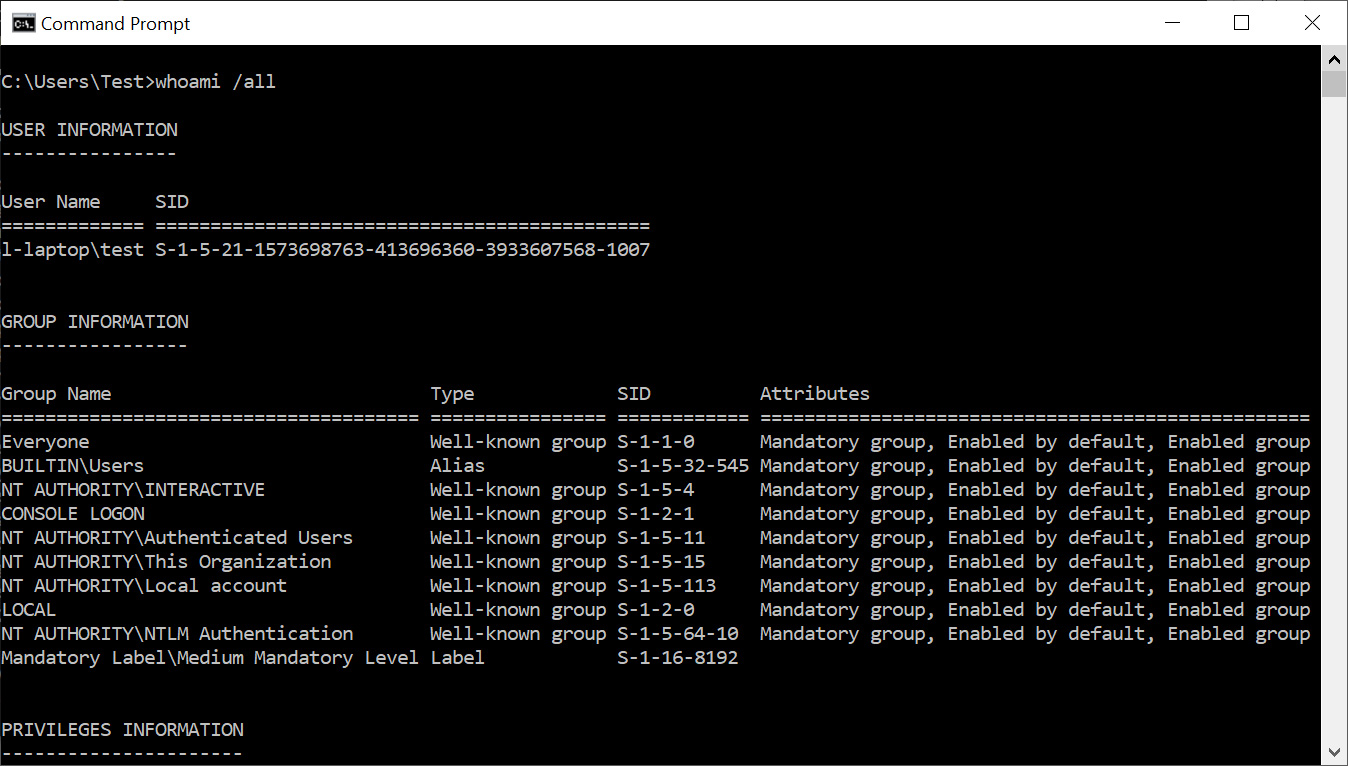
To test this bug, we created a temporary 'Test' user on one of our Windows 10 computers with standard, non-administrator privileges, as shown below.
When we plugged the Razer device into Windows 10, the operating system automatically downloaded and installed the driver and the Razer Synapse software.
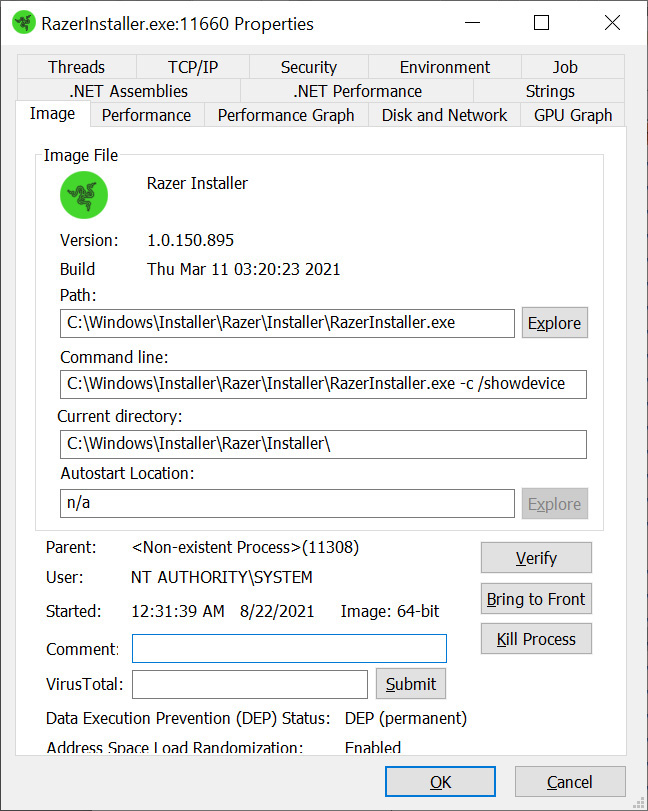
Since the RazerInstaller.exe executable was launched via a Windows process running with SYSTEM privileges, the Razer installation program also gained SYSTEM privileges, as shown below.
When the Razer Synapse software is installed, the setup wizard allows you to specify the folder where you wish to install it. The ability to select your installation folder is where everything goes wrong.
When you change the location of your folder, a 'Choose a Folder' dialog will appear. If you press Shift and right-click on the dialog, you will be prompted to open 'Open PowerShell window here,' which will open a PowerShell prompt in the folder shown in the dialog.
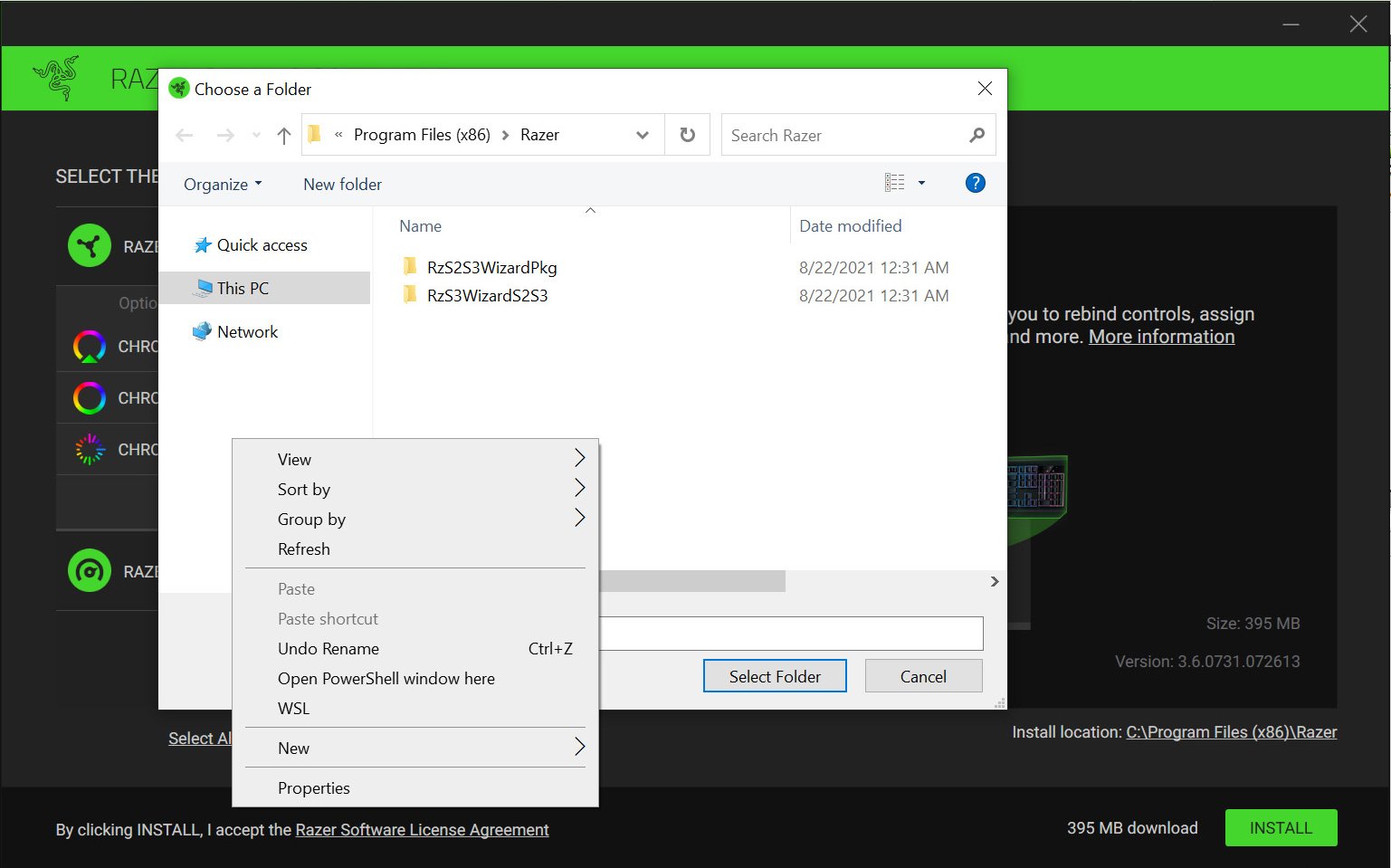
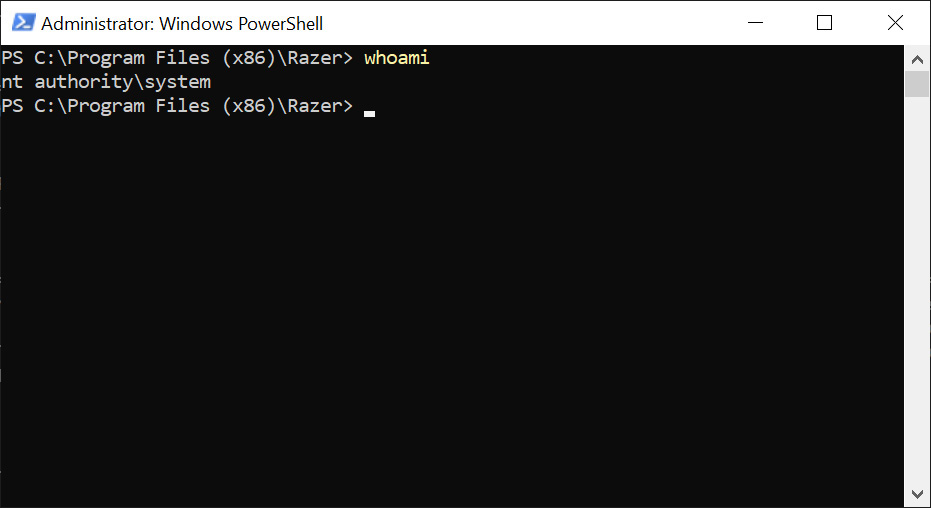
As this PowerShell prompt is being launched by a process with SYSTEM privileges, the PowerShell prompt will also inherit those same privileges.
As you can see below, once we opened the PowerShell prompt and typed the 'whoami' command, it showed that the console has SYSTEM privileges allowing us to issue any command we want.
As explained by Will Dormann, a Vulnerability Analyst at the CERT/CC, similar bugs are likely to be found in other software installed by the Windows plug-and-play process.
Many vulnerabilities fall into the class of "How has nobody realized this before now?"
— Will Dormann (@wdormann) August 22, 2021
If you combine the facts of "connecting USB automatically loads software" and "software installation happens with privileges", I'll wager that there are other exploitable packages out there...
Razer to fix the vulnerability
After this zero-day vulnerability gained wide attention on Twitter, Razer has contacted the security researcher to let them know that they will be issuing a fix.
I would like to update that I have been reached out by @Razer and ensured that their security team is working on a fix ASAP.
— jonhat (@j0nh4t) August 22, 2021
Their manner of communication has been professional and I have even been offered a bounty even though publicly disclosing this issue.
Razer also told the researcher that he would be receiving a bug bounty reward even though the vulnerability was publicly disclosed.



Comments
fromFirefoxToVivaldi - 2 years ago
Easy solution for this and all future issues like this: Windows should stop installing/upgrading drivers without prompting the user for credentials and permission first.
h_b_s - 2 years ago
That's been the proper solution all along, but neither users nor administrators who would have to administrate printer drivers for thousands of users wanted it. Hence, PrintNightmare.
crownkingcharles - 2 years ago
I used this technique with a printer driver when I was using a computer inside a jail I was being held at. They wouldn't allow a browser to launch for the non-privileged user, but SYSTEM has no such limitation.
chilinux - 2 years ago
If you honor the Windows 11 requirements for Secure Boot and TPM 2.0, does it automatically mitigate this exploit?
ken_smon - 2 years ago
This does not sound like a Razor issue at all. Although the installer could be modified to not allow this, it is a fundamental problem with Plug and Play in particular and the Windows "security" ecosystem being deeply flawed.
Lawrence Abrams - 2 years ago
Personally, I think it's a problem on both ends.
Windows should not allow user mode programs and only install drivers.
Since it is allowed, vendors should security their products so they can't be abused in this manner.
68616c - 2 years ago
There is a motivation for Razer, or any other OEM, to force the driver install. When drivers are not installed, the user does not have access to extra controls like resolution, programmable buttons, and LED lighting.
Trying to push a driver reduces support issues, and stops bad review scores due to devices not working out-of-the box. Imagine creating Christmas chat-bots that keep barking: "Please download and install drivers."
And, people who whine and give 1-star product reviews will not take the blame for not RTM. They'll blame the product for not holding their hand.
fromFirefoxToVivaldi - 2 years ago
Windows had been installing only basic drivers for decades. Windows 10 changed that.
>"Please download and install drivers." had always been the norm. There's nothing wrong with requiring the user to click a few buttons.
The current approach only leads to outdated drivers being forced on everyone who uses Windows 10 Home and can't disable automatic driver installations.
chadf - 2 years ago
... "the bug is so easy to exploit as you just need to spend $20 on Amazon for Razer mouse" ...
Maybe even less, if one has/can find a cheap usb + microcontroller which can fake the Razer device enough to trigger windows into installing the software.
Dominique1 - 2 years ago
:facepalm:
63kk01 - 2 years ago
Okay, wow, I guess sharing with people here that there has been proven exploitation of this without even having to use an actual Razer device was TMI!? Post removed? Here I thought BleepingComputer was a security-focused site, which also sometimes means seeing that a way has been made to more easily execute a (still unpatached) zero-day exploit.
I apologize if my post was too uncomfortable for the crowd here.