Fake Windows 10 updates are being used to distribute the Magniber ransomware in a massive campaign that started earlier this month.
Over the past few days, BleepingComputer has received a surge of requests for help regarding a ransomware infection targeting users worldwide.
While researching the campaign, we discovered a topic in our forums where readers report becoming infected by the Magniber ransomware after installing what is believed to be Windows 10 cumulative or security update.
These updates are distributed under various names, with Win10.0_System_Upgrade_Software.msi [VirusTotal] and Security_Upgrade_Software_Win10.0.msi being the most common.
Other downloads pretend to be Windows 10 cumulative updates, using fake knowledge base articles, as shown below.
System.Upgrade.Win10.0-KB47287134.msi
System.Upgrade.Win10.0-KB82260712.msi
System.Upgrade.Win10.0-KB18062410.msi
System.Upgrade.Win10.0-KB66846525.msi
Based on the submissions to VirusTotal, this campaign appears to have started on April 8th, 2022 and has seen massive distribution worldwide since then.
While it's not 100% clear how the fake Windows 10 updates are being promoted, the downloads are distributed from fake warez and crack sites.
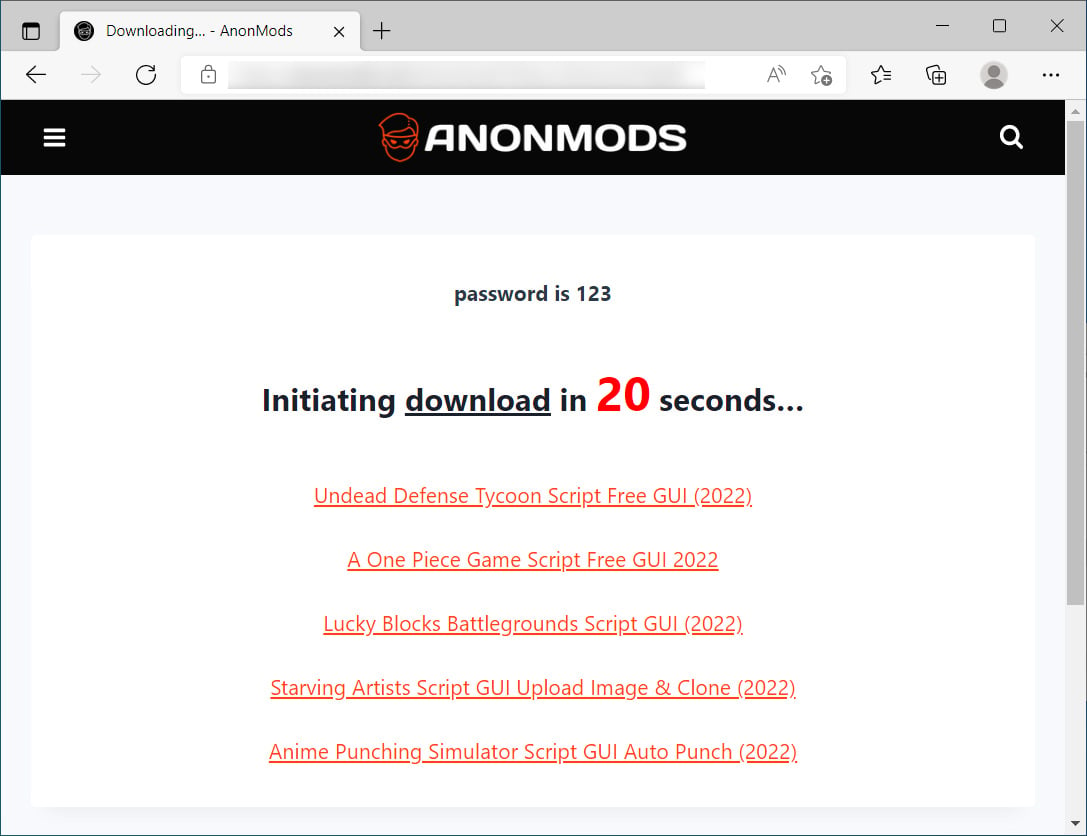
Source: BleepingComputer
Once installed, the ransomware will delete shadow volume copies and then encrypt files. When encrypting files, the ransomware will append a random 8-character extension, such as .gtearevf, as shown below.
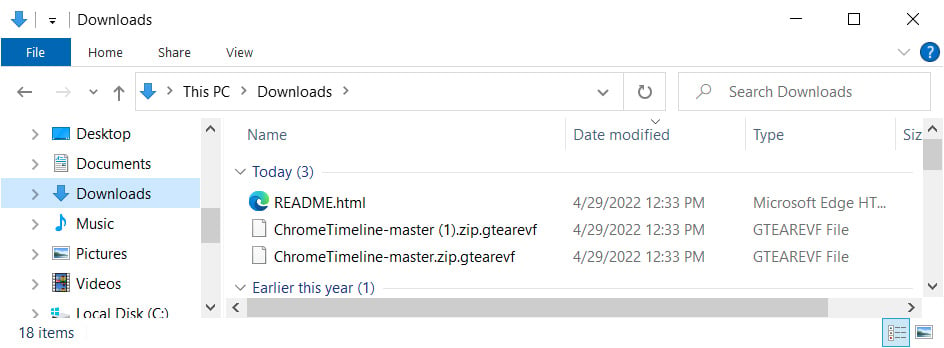
Source: BleepingComputer
The ransomware also creates ransom notes named README.html in each folder that contains instructions on how to access the Magniber Tor payment site to pay a ransom.
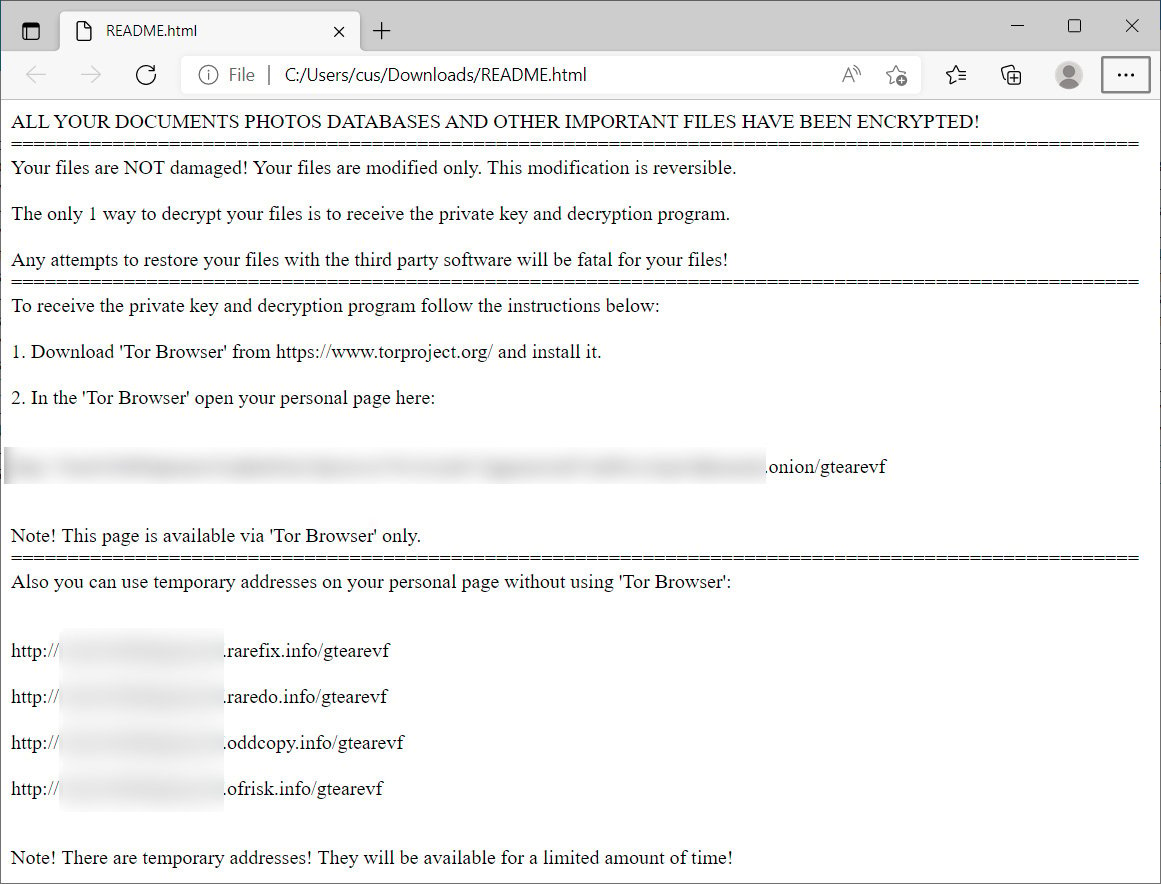
Source: BleepingComputer
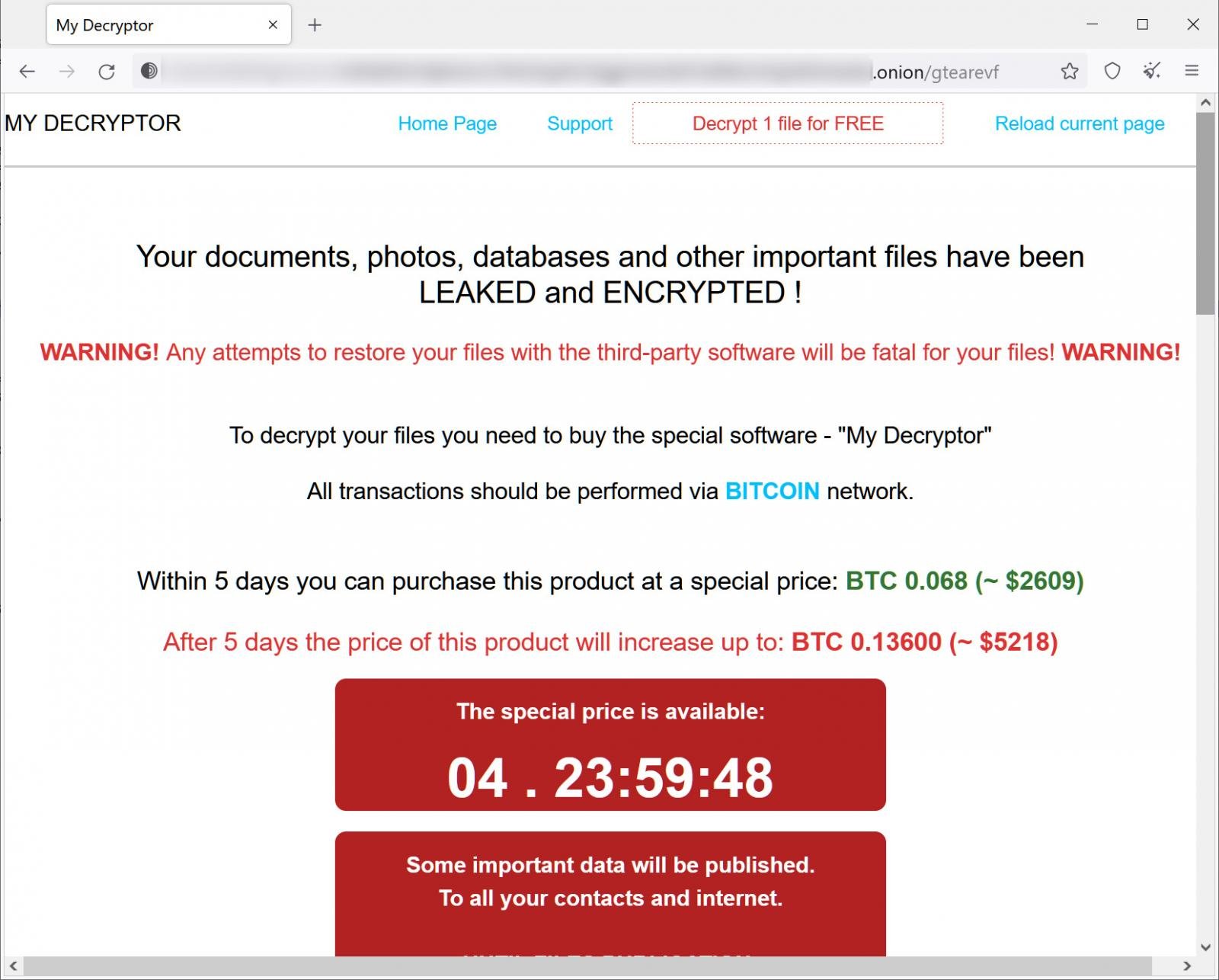
The Magniber payment site is titled 'My Decryptor' and will allow a victim to decrypt one file for free, contact 'support,' or determine the ransom amount and bitcoin address victims should make a payment.
Source: BleepingComputer
From payment pages seen by BleepingComputer, most ransom demands have been approximately $2,500 or 0.068 bitcoins.
Magniber is considered secure, meaning that it does not contain any weaknesses that can be exploited to recover files for free.
Unfortunately, this campaign primarily targets students and consumers rather than enterprise victims, causing the ransom demand to be too expensive for many victims.



Comments
jmwoods - 2 years ago
One of the main reasons to do frequent disk image backups and store them offline...
An investment of around $60 U.S. for a 2 TB external USB drive, and free disk imaging software like Macrium Reflect (Free) are must-have tools for anyone...and the answer to "how do I get my files back".
Kennethcc11 - 2 years ago
I was very happy to see this report, my efforts have worked, and I was about to collapse the first two days.
andy_3_913 - 2 years ago
Why would anybody get their Windows Updates from anywhere other than within the OS from Microsoft?
Lawrence Abrams - 2 years ago
I don't think they are searching for these updates, but rather they are promoted by sites, likely using dialogs to look like Windows update prompts.
bob3160 - 2 years ago
It's your computer. You control it's updates. We all know how to reach Updates and Security on our computers. Never do updates via a suggested link regardless of how genuine it looks.
yawnshard - 2 years ago
Unless you are a pro and know how to check and verify a digitally signed binary or microsoft installer. At least a company like MS doesn't lose their keys, unlike a certain hardware manufacturer, hahaha.
Sxionaut - 2 years ago
Moral of the story: invest in a proven anti-virus solution. Just don't use the anti-virus that Austin - Peay University uses: https://govstech.apsu.edu/TDClient/2071/Portal/KB/ArticleDet?ID=15476 As that's not proven.