
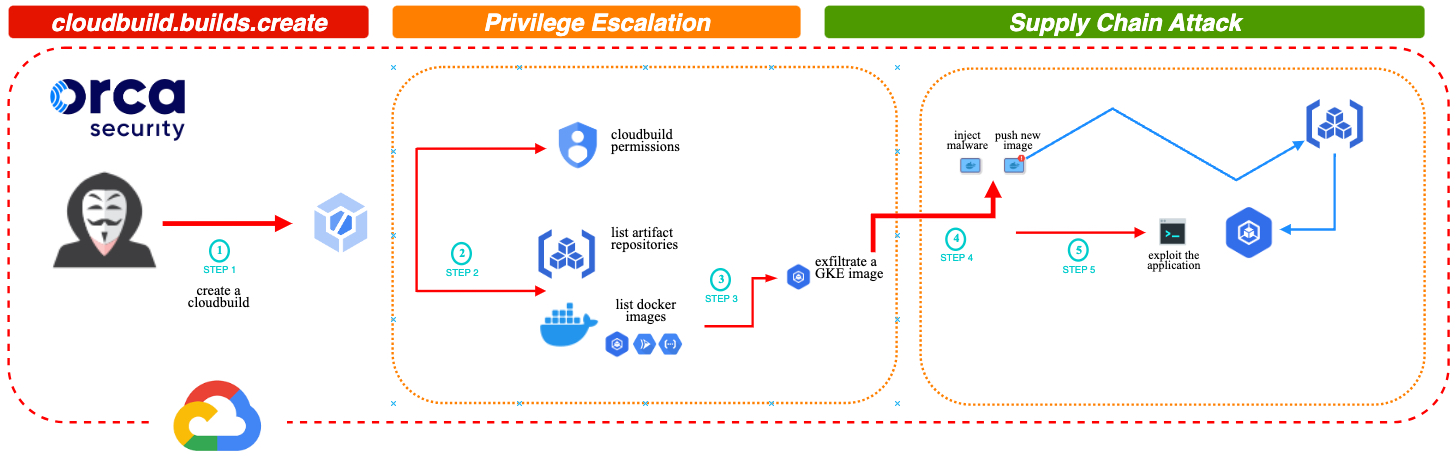
A critical design flaw in the Google Cloud Build service discovered by cloud security firm Orca Security can let attackers escalate privileges, providing them with almost nearly-full and unauthorized access to Google Artifact Registry code repositories.
Dubbed Bad.Build, this flaw could enable the threat actors to impersonate the service account for the Google Cloud Build managed continuous integration and delivery (CI/CD) service to run API calls against the artifact registry and take control over application images.
This allows them to inject malicious code, resulting in vulnerable applications and potential supply chain attacks after deploying the malicious applications within customers' environments.
"The potential impact can be diverse, and applies to all organizations that are using the Artifact Registry as their main or secondary image repository," said Orca security researcher Roi Nisimi.
"The first and immediate impact is disrupting the applications relying on these images. This can lead to DOS, data theft and spreading malware to users.
"As we have seen with the SolarWinds and recent 3CX and MOVEit supply chain attacks, this can have far reaching consequences."
The same vulnerability was observed and reported by Rhino Security Lab here. Still, their method to exploit this privilege escalation flaw was more complex, involving the use of the GCP API and exfiltrated Cloud Build Service Account access tokens.
Orca Security's attack takes advantage of the cloudbuild.builds.create permission to escalate privileges and allow attackers to tamper with Google Kubernetes Engine (GKE) docker images using artifactregistry permissions and run code inside the docker container as root.
After Orca Security reported the issue, the Google Security Team implemented a partial fix revoking the logging.privateLogEntries.list permission from the default Cloud Build Service Account, unrelated to Artifact Registry.
It is important to note that this measure did not directly address the underlying vulnerability in the Artifact Registry, leaving the privilege escalation vector and the risk of a supply chain attack intact.
"However, Google's fix doesn't revoke the discovered Privilege Escalation (PE) vector. It only limits it - turning it into a design flaw that still leaves organizations vulnerable to the larger supply chain risk," Nisimi said.
"It's therefore important that organizations pay close attention to the behavior of the default Google Cloud Build service account. Applying the Principle of Least Privilege and implementing cloud detection and response capabilities to identify anomalies are some of the recommendations for reducing risk."
Google Cloud Build customers are advised to modify the default Cloud Build Service Account permissions to match their needs and remove entitlement credentials that go against the Principle of Least Privilege (PoLP) to mitigate the privilege escalation risks.
In April, Google also addressed a Google Cloud Platform (GCP) security vulnerability dubbed GhostToken that let attackers backdoor any Google account using malicious OAuth applications.
Update July 18, 14:22 EDT: A Google spokesperson shared the following statement after the article was published.
We created our Vulnerability Rewards Program specifically to identify and fix vulnerabilities like this one. We are appreciative of Orca and the broader security community’s participation in these programs. We appreciate the work of the researchers and have incorporated a fix based on their report as outlined in a security bulletin issued in early June. — Google spokesperson

Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now