
The development team behind the open-source password management software KeePass is disputing what is described as a newly found vulnerability that allows attackers to stealthily export the entire database in plain text.
KeePass is a very popular open-source password manager that allows you to manage your passwords using a locally stored database, rather than a cloud-hosted one, such as LastPass or Bitwarden.
To secure these local databases, users can encrypt them using a master password so that malware or a threat actor can't just steal the database and automatically gain access to the passwords stored within it.
The new vulnerability is now tracked as CVE-2023-24055, and it enables threat actors with write access to a target's system to alter the KeePass XML configuration file and inject a malicious trigger that would export the database, including all usernames and passwords in cleartext.
The next time the target launches KeePass and enters the master password to open and decrypt the database, the export rule will be triggered, and the contents of the database will be saved to a file the attackers can later exfiltrate to a system under their control.
However, this export process launches in the background without the user being notified or KeePass requesting the master password to be entered as confirmation before exporting, allowing the threat actor to quietly gain access to all of the stored passwords.
After this was reported and assigned a CVE-ID, users asked the development team behind KeePass to add a confirmation prompt before silent database exports like the one triggered via a maliciously modified configuration file or provide a version of the app that comes without the export feature.
Another request is to add a configurable flag to disable exporting inside the actual KeePass database, which could then only be changed by knowing the master password.
Since CVE-2023-24055 was assigned, a proof-of-concept exploit has already been shared online, likely making it easier for malware developers to upgrade information stealers with the ability to dump and steal the contents of KeePass databases on compromised devices.
Vulnerability disputed by KeePass devs
While the CERT teams of Netherlands and Belgium have also issued security advisories regarding CVE-2023-24055, the KeePass development team is arguing that this shouldn't be classified as a vulnerability given that attackers with write access to a target's device can also obtain the information contained within the KeePass database through other means.
In fact, a "Security Issues" page on the KeePass Help Center has been describing the "Write Access to Configuration File" issue since at least April 2019 as "not really a security vulnerability of KeePass."
If the user has installed KeePass as a regular program and the attackers have write access, they can also "perform various kinds of attacks." Threat actors can also replace the KeePass executable with malware if the user runs the portable version.
"In both cases, having write access to the KeePass configuration file typically implies that an attacker can actually perform much more powerful attacks than modifying the configuration file (and these attacks in the end can also affect KeePass, independent of a configuration file protection)," the KeePass developers explain.
"These attacks can only be prevented by keeping the environment secure (by using an anti-virus software, a firewall, not opening unknown e-mail attachments, etc.). KeePass cannot magically run securely in an insecure environment."
However, even if the KeePass developers will not provide users with a version of the app that addresses the export to cleartext via triggers issue, you could still secure your database by logging in as a system admin and creating an enforced configuration file.
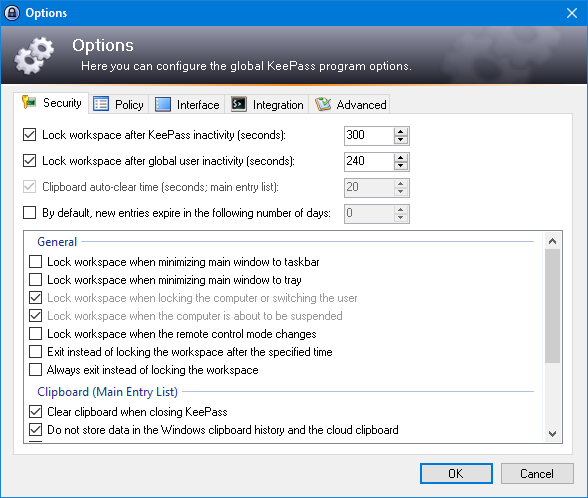
This type of config file takes precedence over settings described in global and local configuration files, including new triggers added by malicious actors, thus mitigating the CVE-2023-24055 issue.
Before using an enforced config file, you must also ensure that regular system users do not have write access to any files/folders in KeePass' app directory.
And there's also one more thing that could allow attackers to work around enforced configurations: using a KeePass executable launched from another folder than the one where your enforced config file was saved.
"Please note that an enforced configuration file only applies to the KeePass program in the same directory," the KeePass development team says,
"If the user runs another copy of KeePass without an enforced configuration file, this copy does not know the enforced configuration file that is stored elsewhere, i.e. no settings are enforced."


Comments
fromFirefoxToVivaldi - 1 year ago
What about KeepassXC? It has some quirks, but if it's not vulnerable, it could be a good alternative to recommend if for some reason people do not want to simply use Bitwarden.
Edit: Ok, I see that it would be enough for someone to drop a portable keepass installation. So it looks like there's no alternative.
If I understand this correctly, even if this gets patched, unless databases are made unreadable to older versions, nothing will change. All attackers would have to do is drop an older version.
Just switch to bitwarden.
hikari15 - 1 year ago
Not vulnerable as per the devs response.
github.com/keepassxreboot/keepassxc/issues/9041
Cheers!
SoftwareEngineer248 - 1 year ago
This is not a security vulnerability. Basically, if can modify a user's files, you can also do a lot of other things which will allow you to steal passwords from ANY password manager. Here are some examples:
1) Malware can wait for the user to enter passwords into a website and then copy them.
2) Malware can modify ANY password manager or web browser, so it exports the password database the next time the master password is used.
3) The malware can copy the database, store it in the cloud and then wait for the user to enter the master password. Once it gets the master password, it sends it to the cloud and the attacker decrypts all of the passwords.
There are a lot more things malware can do. Basically, once malware is running as a user on a computer, it will steal your passwords. No password manager can protect you from this attack.
fromFirefoxToVivaldi - 1 year ago
1) This gives malware just one password at a time, instead of the whole database.
2) It can't do so without circumventing UAC, programs need elevated permission to modify their files. This vulnerability is just about running a portable keepass in userspace and hoping the user will enter their password when prompted.
3) You can not copy the master password in userspace if user enabled secure desktop in keepass. This would require compromising UAC.
This is an issue because it lets attackers gain access to user's password without having to first circumvent UAC.
h_b_s - 1 year ago
UAC is trivially bypassed. Changing the defaults to something more secure leads to a muscle memory response in just clicking through every prompt in frustration already discovered in the Windows Vista days. This is a vulnerability, even though the KeePass team is correct in their facts on what can also happen should a user account be breached, their opinion on whether it should be fixed or not is dubious.
There are alternatives that use the same database format and, KeePass is itself open source. If you don't like the way the team is handling their responsibilities there are options, with or without coding skills.
SoftwareEngineer248 - 1 year ago
First, UAC is not going to save you because UAC is far from perfect. All an attacker needs to get around UAC is one local privilege elevation bug.
Second, malware does not need to get around UAC to get someone's master password. I looked at KeePass's code and it looks like the encrypted password file's decryption key and master password are stored in memory. For more information, please see KeePass\Forms\KeyPromptForm.cs (https://sourceforge.net/projects/keepass/files/KeePass%202.x/2.53/KeePass-2.53-Source.zip/download).
Once something is in memory, it's very easy to get it. All malware has to do is connect to the process and read the process's memory. On Windows, you would use OpenProcess() and ReadProcessMemory(). I am sure there are similar functions on Linux and Mac OS. Once malware has read KneePass's (or any password manager's) the memory, finding the master password and the derived encryption key is trivial.
The secure desktop does not stop this attack because the secure desktop does not stop program A (the malware) from reading program B's (the password manager's) memory.
At the end of the day, there is nothing you can do to stop malware from stealing your passwords if it is already running as your user on your computer (i.e. it's running under your account on your computer). The reason is the malware has the same rights as the person running the password manager and this means the malware can do whatever the password manager can do).
BTW, DRM and anti-cheat software has the same problem. It wants to prevent the user from doing something (copying or modifying a program). It can't because the user can study how the DRM or anti-cheat software works and then create a hack to break it.
Wannabetech1 - 1 year ago
Can you explain in a "for dummies" manner how Bitwarden is better since it's cloud based? BTW, I'm a former Lastpass user who recently migrated to B.W.
kvh - 1 year ago
2 reasons Bitwarden doesn't have this particular issue:
1. BitWarden does not store configuration in an unecrypted local file, at least as far as I can find. Nor, on Windows, in the Registry. This means there is no file that can be secretly updated with new configuration options.
2. Bitwarden doesn't have a way to automatically export the database to a plain text file. All exports require going through the UI.
Neither of those reasons are "because it's cloud based", Bitwarden could add the functionality at any time, although I doubt they would.
The reason this particular vulnerability isn't worse than LastPass's is because they have to break into each machine individually, modify the config file, wait for the user to open the database to get the unencrypted database. With LastPass they got all the databases in one go, now they have to unencrypt them. It's a question of which security is better: Security protecting your computer from file changes for KeePass, or encryption on the database.
SoftwareEngineer248 - 1 year ago
I guarantee you Bitwarden has similar vulnerabilities. Basically, if malware is running on a machine, it can copy the master password when the user enters it and once it has that, it can get the rest of the passwords.
fromFirefoxToVivaldi - 1 year ago
Malware gains nothing by copying the master password from Bitwarden. To log in you also need 2fa token and unless someone is naive enough to use e-mail for that purpose, compromising the pc will not be enough.
On keepass this is also not that easy. If you enable secure desktop, master password entry form is unavailable to userspace software.
AdvancedSetup - 1 year ago
2FA is not the panacea you may think it is and there are ways to bypass it. I have to agree with SoftwareEngineer248 that if you have admin rights on a system you cannot stop them from accessing what they're after sooner or later. You can code a specific tool to copy every single bit of all datastreams, etc. If hackers can break UEFI code I'm sure none of the password managers are safe from such an attack. You must keep the computer secure or you've lost.
fromFirefoxToVivaldi - 1 year ago
How about you stick to the premise? This vulnerability doesn't require admin rights.
SoftwareEngineer248 - 1 year ago
RE: "Malware gains nothing by copying the master password from Bitwarden. To log in you also need 2fa token and unless someone is naive enough to use e-mail for that purpose, compromising the pc will not be enough."
2 Factor Authentication (2FA) will not help you in this situation. The reason is all the malware has to do is wait for you to sign in. Once you are signed in, you will decrypt your password file and then the malware steals the passwords.
Basically, no password manager or software is going to save you if you are already infected with malware.
fromFirefoxToVivaldi - 1 year ago
They would first need to break aes memory encryption, even when the database is open. Impossible on a normal PC.
Passwords are never in plain text, even in RAM, unless the user copies them or chooses to reveal password contents globally in the application.
deltasierra - 1 year ago
"You must keep the computer secure or you've lost." Secure is relative, not absolute. The average end user can't be expected to maintain a [relatively] secure computing environment, otherwise social engineering and malware wouldn't be as successful as it is. Not that any software can remain 100% defensible either; the best strategy remains: defense-in-depth to slow down or best-case, make the target not worth the time and effort.
On the other hand, software claiming to secure every password a user has is expected to take every precaution possible to secure its castle walls. Write access at the user's privilege level isn't necessarily admin compromise. Regardless of this CVE, it IS a flaw to allow a database export to plain text without entering the master password. Silent or UI, that doesn't even matter.
Hopefully KeePass will turn down the cynicism and work towards some mitigations/additional safeguards. It's still being actively developed, is it not? Indeed, a flimsy, half-baked patch isn't as important as a long-term slight redesign/rearchitecting that better protects the config file and adds the silent export password prompts.
SoftwareEngineer248 - 1 year ago
Defense in depth is a good thing but it will not really help you here.
Even if KneePass fixed this "vulnerability", all an attacker (malware author) would have to do is figure out how KneePass works and write software which steals the passwords while KneePass runs.
deltasierra - 1 year ago
KeePass is open-source software, so it's trivial for attackers or security researchers to understand how it works. Thus, they aren't afforded the fog-of-war to their code that proprietary password managers have. At the same time, secure development can still assume that even if [proprietary] source code is stolen, it doesn't [completely] compromise the security of the software. Microsoft employs this and I"m sure many others to as well.
Not that weaknesses can't and won't be found, but of course one of the "promises" of open-source is that enough eyes on and testing is done that weaknesses are rather thoroughly weeded out. That's the hope, anyways. Unfortunately, weaknesses always will exist and vary in terms of severity, release time of fixes by the developer(s), and time-to-patch by consumers of the software.
Yes, something we can all agree on is that security is hard. For starters though, it takes a positive, can-do attitude. Almost anyone is guilty of these cynical shortcomings -- Apple, Microsoft, and others saying "that's not a flaw -- that's by design and we don't see it as an issue." That's fine and dandy in some cases, and it's fair and true to say that not all risk can and will ever be eliminated. Circling back again though, it does require significant collaboration and sharing, determination, and even some humility to really stay on the upside of the curve, because by golly, plenty of threat actors have all the time in the world, resources, and motivation & determination to steal our money, identity... all the way to breaching our corporate networks!
KeePass seems to excuse themself here: "KeePass cannot magically run securely in an insecure environment." That's an over-the-top statement there. We're not asking for perfection, just for additional hardening. User ideas are already floating.
Just would rather hear "we'll consider this and research further." That's what cyber citizens need more of, not less.
SoftwareEngineer248 - 1 year ago
Unfortunately, users are going to have to learn how to keep their PCs or Macs secure. There are no quick and easy solutions.
Here are the best answers I have come up with:
1. For people who just do not want to learn, they should stick to an iPhone and iPad. The reason is iOS/iPadOS prevent apps from interfering from each other. All a user has to do to keep themselves safe is do the following:
- Only use supported devices (i.e. devices still receiving security patches)
- Apply security updates promptly
- Turn on automatic updates
- Use secure (truly random) passwords
- Do not reuse passwords
For PC, Mac OS and Linux users, it's going to be harder. Here are some suggestions:
- Only use software which still receives security updates
- Limit the amount of software installed on a machine. The more software you install, the higher the chance you either install malware or install something you forget to update.
- Install all security updates promptly
- Learn how to get security updates for all software installed on the machine.
- DO NOT INSTALL PIRATED SOFTWARE - It may contain viruses.
- Only install software from large well-known organizations. For each program you install, ask why you trust its authors.
- Use secure (truly random) passwords
- Do not reuse passwords
- Use a firewall to block all incoming connections (this breaks some software)
- Consider using two computers. One is for general purpose work and one is for sensative work (visiting financial web sites, doing taxes, etc.).
The bottom line is there are no easy answers. Security is hard.
JohnC_21 - 1 year ago
What are your thoughts on using a stock Chromebook with only a very few apps installed for doing sensitive work?
deltasierra - 1 year ago
A stock Chromebook with minimal app usage and some browser hardening would be a fairly strong posture. Not fool proof though, especially if managed; news just came out recently of an attack that unenrolls managed Chromebooks. Stand-alones wouldn't have to worry about this.
SoftwareEngineer248 - 1 year ago
RE: JohnC_21 - What are your thoughts on using a stock Chromebook with only a very few apps installed for doing sensitive work?
This sounds like a good idea. My advice would be to only go to essential web sites and only use apps from trusted sources. Also, remember to replace the Chrome Book when Google or the Manufacture stop releasing security patches for it.