
Cisco has released a security advisory to warn about a critical vulnerability (CVSS v3 score: 10.0), tracked as CVE-2022-20695, impacting the Wireless LAN Controller (WLC) software.
The security flaw allows remote attackers to log in to target devices through the management interface without using a valid password.
The bug involves the improper implementation of the password validation algorithm, making it possible to bypass the standard authentication procedure on non-default device configurations.
If this prerequisite is present, the attacker may use crafted credentials to gain varying levels of privilege, potentially going all the way up to an administrative user.
Impact and remediation
According to Cisco's advisory, the products affected by this flaw are those that run Cisco WLC Software 8.10.151.0 or Release 8.10.162.0 and have "macfilter radius compatibility" configured as "Other."
The affected products are:
- 3504 Wireless Controller
- 5520 Wireless Controller
- 8540 Wireless Controller
- Mobility Express
- Virtual Wireless Controller (vWLC)
In addition to the above, some customers using the following builds not available through the Software Center should also consider themselves vulnerable: 8.10.151.4 to 8.10.151.10 and 8.10.162.1 to 8.10.162.14.
Finally, Cisco has confirmed the following as not vulnerable to CVE-2022-20695:
- Catalyst 9800 Embedded Wireless Controller for Catalyst 9300, 9400, and 9500 Series Switches
- Catalyst 9800 Series Wireless Controllers
- Catalyst 9800 Wireless Controller for Cloud
- Embedded Wireless Controller on Catalyst Access Points
- Wireless LAN Controller (WLC) AireOS products not listed in the Vulnerable Products section
To determine if your configuration is vulnerable, issue the "show macfilter summary" command. If the RADIUS compatibility mode returns "Other," you're vulnerable to attacks.
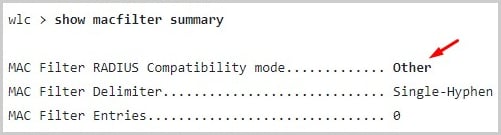
(Cisco)
Applying the latest available security updates (8.10.171.0 or later) released by Cisco addresses this vulnerability no matter what configuration you're using.
Possible workarounds
Cisco has provided two possible workarounds for those who can't update the Wireless LAN Controller.
The first option is to reset the "macfilter radius compatibility" mode to the default value by issuing the following command: "config macfilter radius-compat cisco".
The second option would be to change the configuration to other safe modes, such as "free", using this command: "config macfilter radius-compat free".
At the time of writing this, Cisco is not aware of the vulnerability being under active exploitation, and Bleeping Computer has seen no reports about scanning attempts either.



Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now