
An international law enforcement operation has seized the servers, data, and customer logs for DoubleVPN, a double-encryption service commonly used by threat actors to evade detection while performing malicious activities.
DoubleVPN is a Russian-based VPN service that double, triple, and even quadruple-encrypts data sent through their service.
When using the service, requests are encrypted and transmitted to one VPN server, which sends it to further VPN servers, who finally connect to the final destination, as shown below.
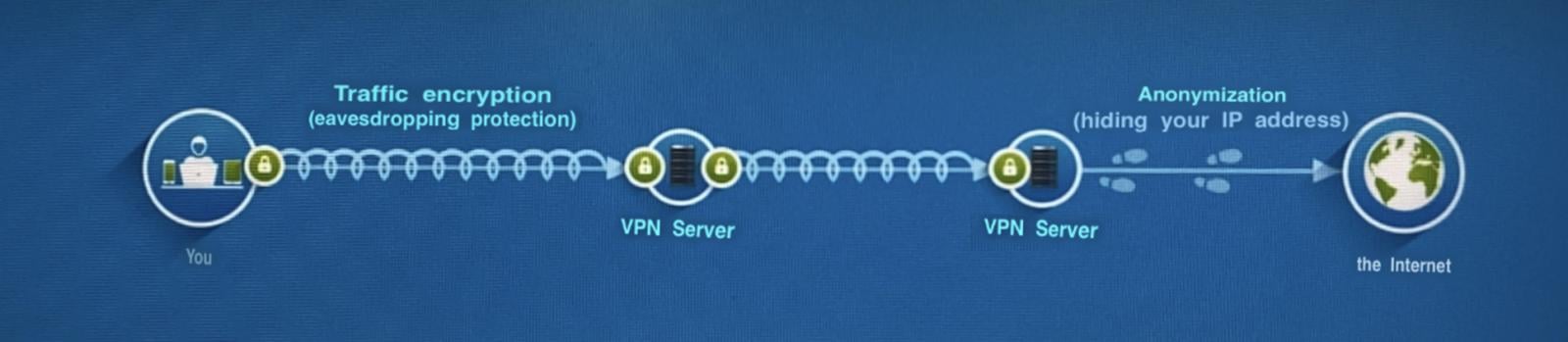
Translated from Doublevpn.com
Threat actors commonly used this service to obfuscate their locations and originating IP addresses when performing cyberattacks.
Servers and data seized by law enforcement
The doublevpn.com [archive.org] website was seized on June 29th by law enforcement, who stated in a seizure notice that they gained access to the servers for DoubleVPN and took personal information, logs, and statistics for the service's customers.
"On 29th of June 2021, law enforcement took down DoubleVPN. Law enforcement gained access to the servers of DoubleVPN and seized personal information, logs and statistics kept by DoubleVPN about all of its customers. DoubleVPN’s owners failed to provide the services they promised," says the now-seized doublevpn.com website.
"International law enforcement continues to work collectively against facilitators of cybercrime, wherever and however it is committed. The investigation regarding customer data of this network will continue."
In a press statement issued today, Europol states that the coordinated takedown of the DoubleVPN service was conducted by the Dutch National Police (Politie), with international support coordinated by Europol and Eurojust.
"DoubleVPN was heavily advertised on both Russian and English-speaking underground cybercrime forums as a means to mask the location and identities of ransomware operators and phishing fraudsters," said the press statement.
"The service claimed to provide a high level of anonymity by offering single, double, triple and even quadruple VPN-connections to its clients."
As part of this operation, law enforcement seized servers worldwide and replaced associated web domains with a law enforcement splash page.
The splash page states that the operation was conducted by Germany's BKA, Netherland's Politie, the FBI, the UK National Crime Agency, the United States Secret Service, the Royal Canadian Mounted Police, Eurojust, Switzerland's Polizia Cantonale, Europol, Bulgaria's GDBOP, and the Swedish National Police.
Europol told BleepingComputer that they could not share further details as there are ongoing parallel investigations related to this takedown.
6/30/21: Updated with information from Europol press release.



Comments
No1gr8 - 2 years ago
I'm glad to see agencies starting to take these threats seriously.
EmanuelJacobsson - 2 years ago
Its too little, too late, im afriad.
h_b_s - 2 years ago
"Its too little, too late, im afriad."
It's not too late. This signals a ramp up in cooperation. Putin is feeling the heat, I assume. The Russian political and military elite will only tolerate him so long as he keeps the graft flowing. Sanctions puts a crimp in the flow of western luxury goods and the sales of arms. If the military turns on him, he will last about as long as any other corrupt politician in that situation.
Echo64 - 2 years ago
I like how much time and effort they put into their seize notices, it literally looks like something you'd see on an episode of NCIS.