
Researchers have found half a dozen high-risk vulnerabilities in the latest firmware version for the Netgear Nighthawk R6700v3 router. At publishing time the flaws remain unpatched.
Nighthawk R6700 is a popular dual-bank WiFi router advertised with gaming-focused features, smart parental controls, and internal hardware that is sufficiently powerful to accommodate the needs of home power users.
The six flaws were discovered by researchers at cybersecurity company Tenable and could allow an attacker on the network to take complete control of the device:
- CVE-2021-20173: A post-authentication command injection flaw in the update functionality of the device, making it susceptible to command injection.
- CVE-2021-20174: HTTP is used by default on all communications of the device’s web interface, risking username and password interception in cleartext form.
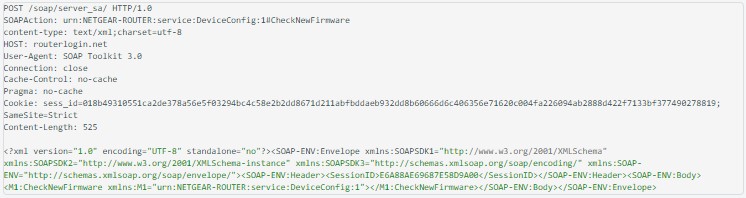
- CVE-2021-20175: SOAP Interface (port 5000) uses HTTP to communicate by default, risking username and password interception in cleartext form.
- CVE-2021-23147: Command execution as root without authentication via a UART port connection. Exploiting this flaw requires physical access to the device.
- CVE-2021-45732: Configuration manipulation via hardcoded encryption routines, allowing the changing of settings that are locked for reasons of security.
- CVE-2021-45077: All usernames and passwords for the device’s services are stored in plaintext form in the configuration file.
On top of the aforementioned security issues, Tenable found several instances of jQuery libraries relying on version 1.4.2, which is known to contain vulnerabilities. The researechers also note that the device uses a MiniDLNA is server version with publicly known flaws.
Source: Tenable
The recently disclosed flaws affect firmware version 1.0.4.120, which is the latest release for the device.
Users are advised to change the default credentials to something unique and strong and follow recommended security practices for more robust defense against malware infections.
Also, check Netgear’s firmware download portal regularly and install new versions as soon as they become available. Turning on automatic updates on your router is also recommended.
The current security report refers to Netgear R6700 v3, which is still under support, not Netgear R6700 v1 and R6700 v2, which have reached end of life. If you are still using the older models, it is recommended to replace them.
Tenable disclosed the above issues to the vendor on September 30, 2021, and even though some information exchange in the form of clarifications and suggestions took place afterward, the problems remain unaddressed.
We have reached out to Netgear asking for a comment on the above, and we will add an update to this story as soon as we hear back from them.



Comments
fromFirefoxToVivaldi - 2 years ago
This is why people should only be buying routers compatible with Open/DD-WRT. The only issue is finding one that's priced reasonably.
S2K2 - 2 years ago
Most of these require physical access, or already being authenticated. The rest are configuration problems that the admin can resolve. But ya, blow up Netgear.
forum11 - 2 years ago
"...R6700 v3, which is still under support, not Netgear R6700 v1 and R6700 v2, which have reached end of life. If you are still using the older models, it is recommended to replace them."
First, the idea that one should just discard perfectly good hardware is disheartening. I'm not familiar with current Netgear offerings, but I'd hope installing alternative firmware, something like OpenWrt, would be an option. If not, I would steer clear of buying anything else from them given they seem so inclined to abandon units.
Second, the whole versioning of hardware models to the point they are considered entirely different "models" with separate life cycles yet have the same core model number is a pet peeve of mine. You know the planned obsolescence force is strong with a company when they need to outwardly version their models.
CFGC21 - 1 year ago
One reason Netgear Nighthawk Routers are getting hacked is because users are required to get a Netgear account to install the router and that portion of their website has been compromised. My situation: Over a year ago we got the RAX70. Worked great (and still does), but when I logged in the router there were a lot of unrecognized devices. When I changed the SSID and passwords, the log showed that WLAN access was being rejected due to incorrect security. after about 1.5 days, the router started getting hit with DOS attacks to port 443 and then two other ports were attacked a couple of times. Then I started noticing things on my on my android phone, computer and gmail. Fast forward .. they took control of my android phone and my computer. I got a new IPhone14. Using my new phone that I had for maybe 1 day, I contacted Netgear (actual company site) via chat and she changed my email address which change I confirmed by responding to her email. I logged in with my new address using a one time passcode. When I tried to change the password, I could not select it. I logged out and when I tried to log back in the system said the email address did not exist in their system. That happened twice. When I did log in, the section to change your password had been removed. I explored my account a little more and saw about 6-8 routers logged under my account. I deleted all but the one we purchased. So my data has been breached and probably our TVs are infected also. Today I decided just to toss out the router beause there is no way to repair this situation if someone else has control of my Netgear account. Backing up to say, As I was logging into my Netgear account, me account page was taking way to long to open and the buffering circle looked strange. I copied and pasted this from the address bar that shows a redirect. I don’t know if it tells anything. I just wanted to post this information somewhere so people will know about Netgear’s compromised web site. I know we are not the only ones this has happened to, but many people are not aware of what is taking place , as I didn’t for a long time. I found the 6-8 devices attached to the router maybe 2 weeks ago. It was probably those same devices that were listed, in June 2022, under my Netgear account.
https://accounts.netgear.com/login?redirectUrl=https:%2F%2Fmy.netgear.com%2Fcommunity%2Flogin%2Fdefault.aspx%3Freferer%3