
The author of a popular software-defined radio (SDR) project has removed a "backdoor" from radio devices that granted root-level access.
The backdoor had been, according to the author, present in all versions of KiwiSDR devices for the purposes of remote administration and debugging.
Last night, the author pushed out a "bug fix" on the project's GitHub aimed at removing this backdoor silently, which sparked some backlash.
Since then, the author's original forum posts and comments with any mention of "backdoor" have been removed over the last few hours.
Hardcoded password gives root access to all devices
KiwiSDR is a software-defined radio that can be attached to an embedded computer, like Seeed BeagleBone Green (BBG).
It is provided either as a standalone board or a more complete version featuring BBG, a GPS antenna, and an enclosure.
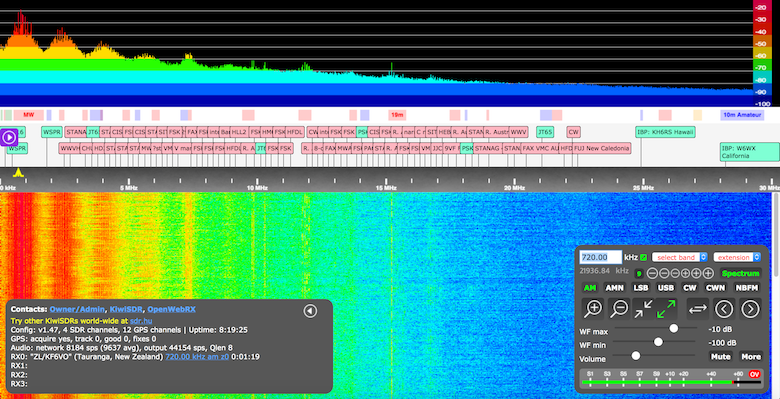
SDRs are aimed at replacing radio frequency (RF) communication hardware with software or firmware for carrying out signal processing activities that would normally require hardware devices.
The concept is analogous to software-defined networking.
Yesterday, Mark Jessop, an RF engineer, and radio operator came across an interesting forum post in which the author of the KiwiSDR project admitted to having remote access to all radio receiver devices running the software.
Interesting post on the KiwiSDR forums. Seems to imply the KiwiSDR author has remote access to all KiwiSDRs? Post has since been modified to remove the last paragraph and the thread locked :-/ https://t.co/cAi5dS7J49 pic.twitter.com/elqSsaUJ65
— Mark Jessop (@vk5qi) July 14, 2021
Another user, M. dug out a 2017 forum thread where KiwiSDR's developer admitted that a backdoor indeed provided them with remote access to all KiwiSDR devices.
Although the entire KiwiSDR forum site has become inaccessible as of today, an archived copy of the forum post seen by BleepingComputer confirms the contents of the tweet:
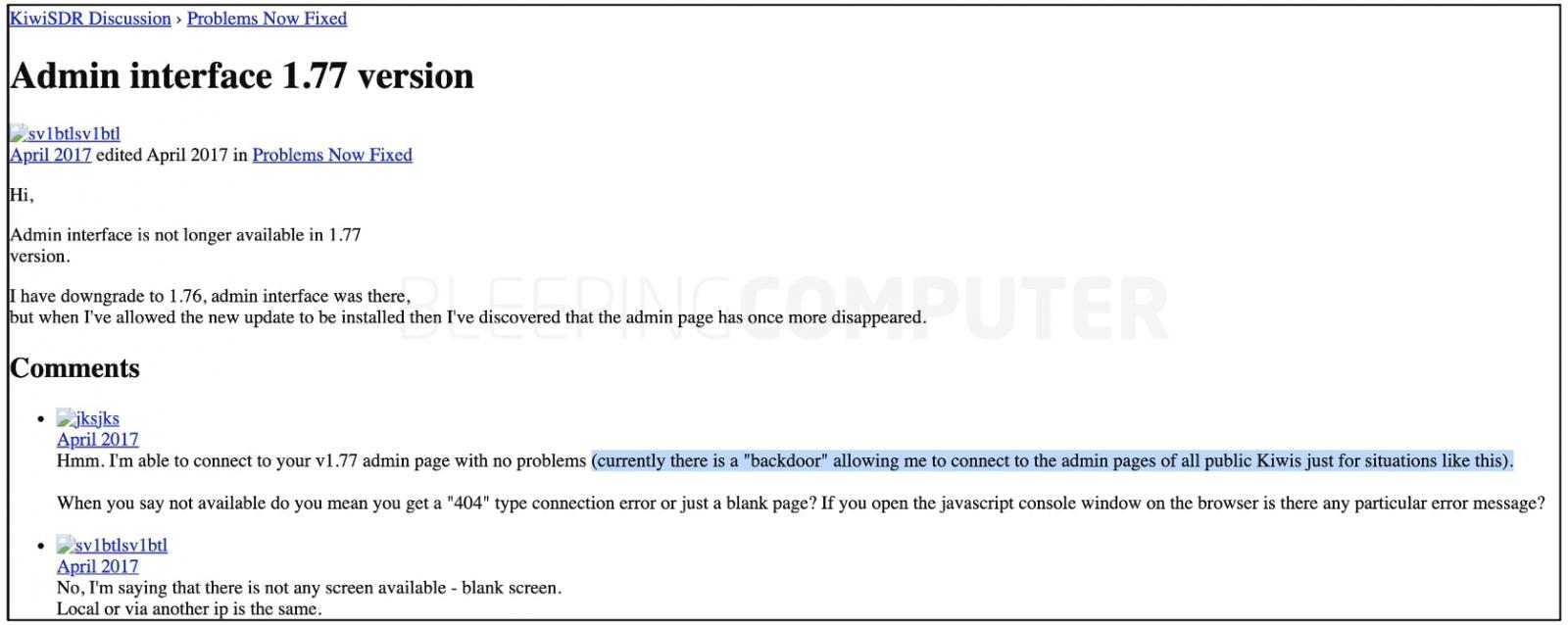
Source: BleepingComputer
Furthermore, as of today, over 600 KiwiSDR devices are online with the backdoor still present in them, as highlighted by Hacker Fantastic.
Although these devices are mainly acting as radio receivers, it is worth noting, any remote actor who logs in using the hardcoded master password is granted root-level access to the device's (Linux-based) console.
This can enable adversaries to probe into the IoT devices, take them over, and begin traversing adjacent networks the radio devices are connected to:
"These KiwiSDRs are used for receiving HF radio stations. The backdoor itself doesn't give an attacker any special SDR access, just that they can access the console of the device (Linux) and start pivoting into networks," ethical hacker xssfox told BleepingComputer.
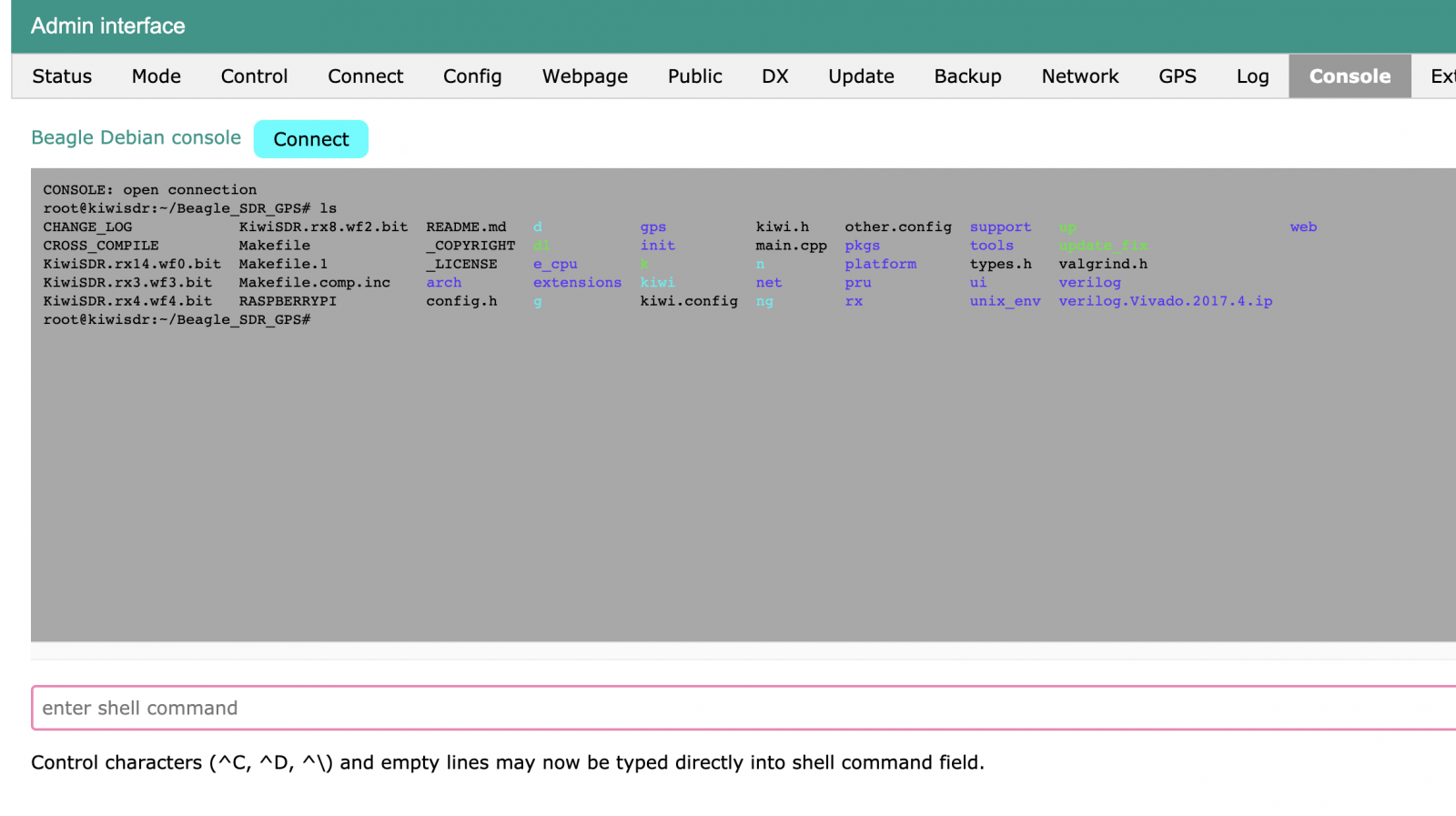
An image of the KiwiSDR administration panel obtained by BleepingComputer shows console level access with root access (notice the #) is possible:
A video created by xssfox demonstrates how the backdoor can be exploited via a simple HTTP GET request, which looks like:
Note: the superuser password (kconbyp) shown above is an older password, SHA256 hash of which used to be present on KiwiSDR devices. The more recent hash (shown below) is different, indicating "kconbyp" won't work on later versions of KiwiSDR and that a newer master password has been present.
Dev pushes out "bug fix" overnight removing the backdoor
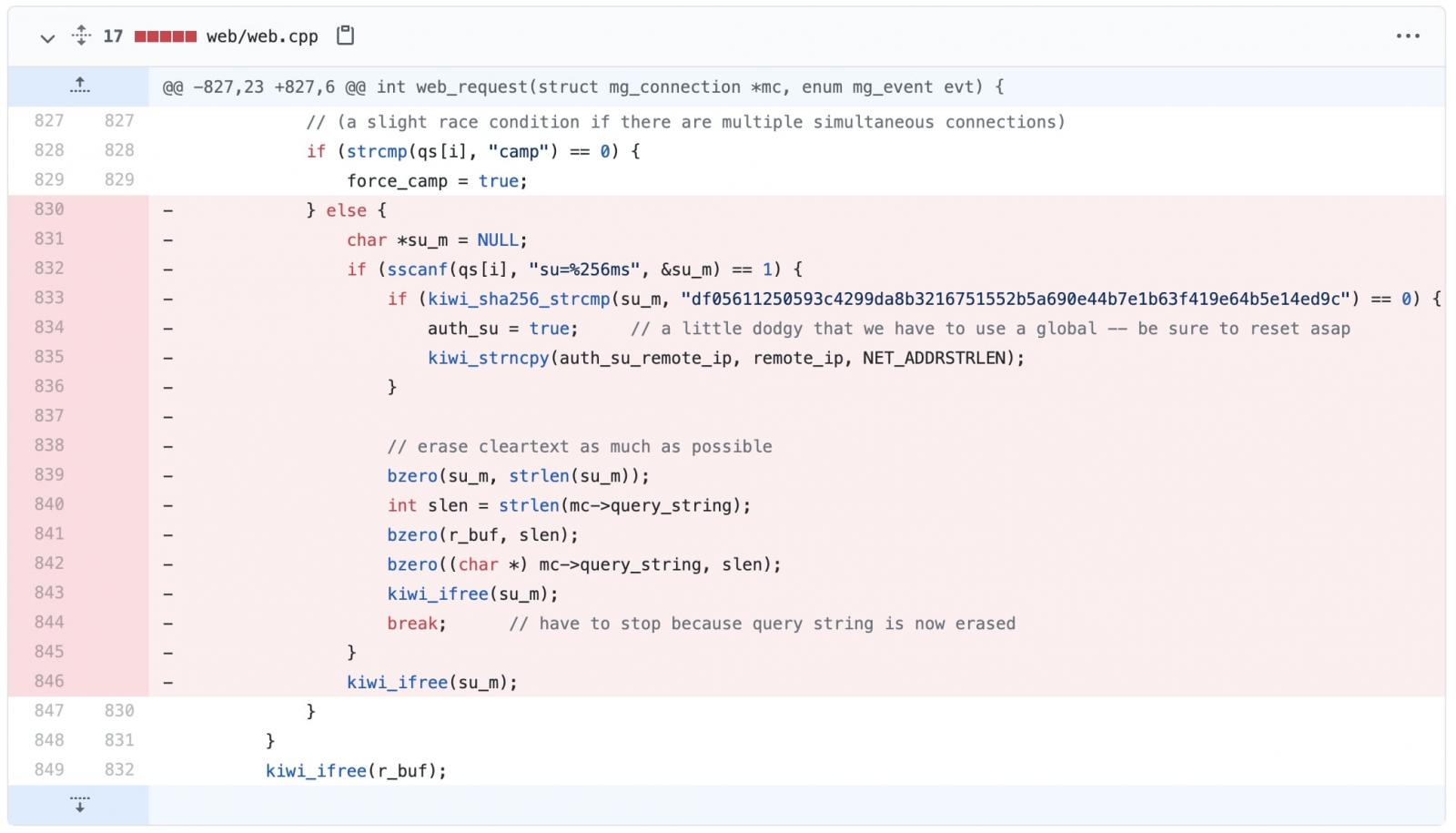
As seen by BleepingComputer, as of a few hours ago a fix has been committed to KiwiSDR's GitHub project removing the backdoor code.
The update removes multiple administrative functions, and specifically the code that compares the provided master password against its SHA256 hash:
Jessop clarified that there is no indication of KiwiSDR's author having misused the backdoor access, which had been introduced with the intention of debugging KiwiSDR devices in good faith.
He further said KiwiSDR developer has been extremely responsive in patching bugs and adding features.
But, like others, the engineer did express concerns, that the master password would transmit over HTTP enabling any Man-in-the-Middle (MitM) threat actor to potentially intercept it and consequently gain remote access to all devices.
However, given the KiwiSDR is HTTP only, sending what is essentially a 'master' password in the clear is a little worrying. KiwiSDR does not support HTTPS, and it's been stated that it will never support it. (Dealing with certs on it would be a PITA too)
— Mark Jessop (@vk5qi) July 14, 2021
Some Redditors also expressed that backdoors were never okay, regardless of whether HTTPS was in use:
"No way. Back doors are never okay. Password was sent in the clear, as HTTPS isn't supported. Eventually someone would have exploited this. Hell, someone might have already exploited this and we just don't know about it," said one of the users in a thread.
KiwiSDR users should upgrade to the latest version v1.461 released today on GitHub that removes the backdoor from their radio devices.



Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now