Digital security giant Entrust has confirmed that it suffered a cyberattack where threat actors breached their network and stole data from internal systems.
Entrust is a security firm focused on online trust and identity management, offering a wide range of services, including encrypted communications, secure digital payments, and ID issuance solutions.
Depending on what data was stolen, this attack could impact a large number of critical, and sensitive, organizations who use Entrust for identity management and authentication.
This includes US government agencies, such as the Department of Energy, Department of Homeland Security, the Department of the Treasury, the Department of Health & Human Services, the Department of Veterans Affairs, the Department of Agriculture, and many more.
Hackers breached Entrust’s network in June
Approximately two weeks ago, a source told BleepingComputer that Entrust was breached on June 18th and that the hackers stole corporate data during the cyberattack.
However, it wasn't until yesterday that the breach was publicly confirmed when security researcher Dominic Alvieri tweeted a screenshot of a security notice sent to Entrust's customers on July 6th.
"I am writing to let you know that on June 18, we learned that an unauthorized party accessed certain of our systems used for internal operations. We have been working tirelessly to remediate this situation since that moment," reads a security notice from Entrust CEO Todd Wilkinson.
"The first thing I want to tell you is that, although our investigation is ongoing, we have found no indication to date that the issue has affected the operation or security of our products and services."
The security notice confirms that data was stolen from Entrust's internal systems. However, it is not known at this time if this is purely corporate data or customers' and vendors' as well.
"We have determined that some files were taken from our internal systems. As we continue to investigate the issue, we will contact you directly if we learn information that we believe would affect the security of the products and services we provide to your organization." - Entrust.
Today, Entrust told BleepingComputer that they are working with a leading cybersecurity firm and law enforcement to investigate the attack but that it has not affected their operations.
"While our investigation is ongoing, we have found no indication to date that the issue has affected the operation or security of our products and services, which are run in separate, air-gapped environments from our internal systems and are fully operational," Entrust told BleepingComputer.
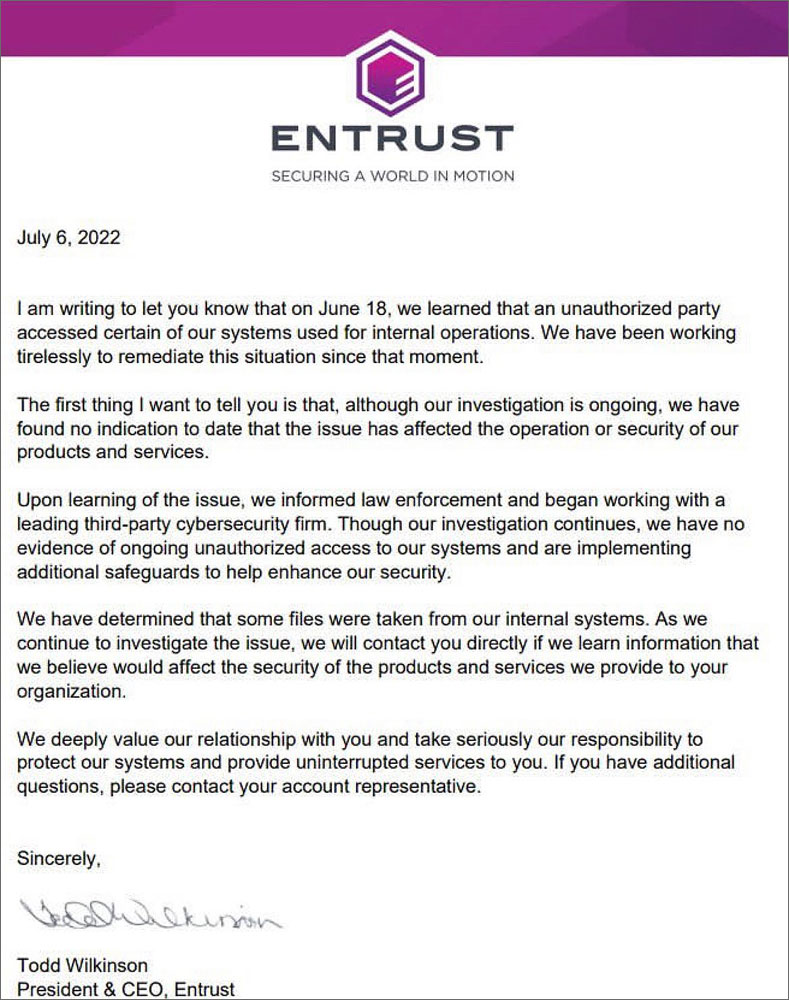
Source: Dominic Alvieri
Hit by a ransomware gang
While the security notices and Entrust's statements to BleepingComputer did not share further details regarding the attack, BleepingComputer has learned that a well-known ransomware gang is behind the attack.
While it is unclear if devices were encrypted during the attack, ransomware gangs commonly steal data before launching their encryptors to be used in double-extortion schemes.
According to AdvIntel CEO Vitali Kremez, a ransomware operation purchased compromised Entrust credentials and used them to breach their internal network.
"The responsible group operation relied on the trusted network of network access sellers to obtain initial access to Entrust environment which led to the subsequent encryption and exfiltration exposure via a known ransomware group," Kremez told BleepingComputer in a conversation about the attack.
Unless Entrust pays a ransom demand, we will likely learn what ransomware operation was behind the attack when they publicly publish the stolen data.
When we reached out to Entrust with questions about the ransomware attack, they told us they could not share any further details about the attack.



Comments
RyanBit - 1 year ago
Yet another reminder that even Cyber Security companies are not immune to intrusions. While some people will judge Entrust and assume they're less capable, no company can prevent ALL breach attempts. It will happen sooner or later and the real test is how they own it, how they learn from it, and how they better protect and benefit their customers from the experience.
EndangeredPootisBird - 1 year ago
You can easily mitigate 100% of cyberattacks, the problem is that no company is covering all the blind spots, be it exposed and out of date RDP and VPN's, weak/default credentials, vulnerable applications, internet-facing IOT devices, etc.
Its the whole reason im stunned to see cyberattacks still being successful, you can easily cover all attack vectors, yet no company are willing to do it and arent learning anything from seeing others getting breached.
Zero Trust alone covers Resource Development, Credential Access and Lateral Movement, and mostly Initial Access, yet most companies still waste millions on endpoint-based protection and VPN's.
plat1098 - 1 year ago
Another likely example of money getting funneled into pockets instead of where it's really needed. Now the threat of customers flocking elsewhere will cost more than the original expenditure on security.
Kind of like the principle of ransomware in general.