
Security researchers discovered a multi-step information stealing campaign where hackers breach the systems of hotels, booking sites, and travel agencies and then use their access to go after financial data belonging to customers.
By using this indirect approach and a fake Booking.com payment page, cybercriminals have found a combination that ensures a significantly better success rate at collecting credit card information.
Next-level phishing
Typically, researchers observed info-stealer campaigns that targeted the hospitality industry (e.g. Hotels, travel agencies) using “advanced social engineering techniques” to deliver info-stealing malware.
It starts with a simple query to make a reservation, or it refers to an existing one, researchers at cybersecurity Perception Point say in a report earlier this month.
After establishing communication with the hotel, the criminals invoke a reason, such as a medical condition or a special request for one of the travelers, to send important documents via a URL.
The URL leads to info-stealing malware that “is designed to operate stealthily” and collects sensitive data like credentials or financial info.
In a new report this week, researchers at internet company Akamai say that the attack goes beyond the step described above and moves to target the customers of the compromised entity.
“After the infostealer is executed on the original target (the hotel), the attacker can access messaging with legitimate customers” - Shiran Guez, information security senior manager at Akamai
Having a direct and trusted communication channel with the final victim, cybercriminals can send their phishing message disguised as a legitimate request from the now-compromised hotel, booking service, or travel agency.
The message asks for an additional credit card verification and relies on the common ingredients of a phishing text: requires immediate action and uses sound rationale to explain it.
Guez notes that the message “is written professionally and modeled after genuine hotel interactions with their guests,” which eliminates all suspicion of a ploy.
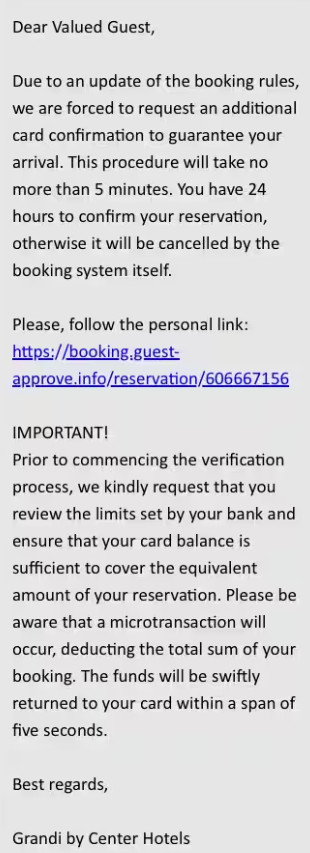
source: Akamai
“It is important to remember that this message comes from within the booking site’s message platform itself,” the researcher highlights.
Since the communication comes from the booking site through the official channel, the target has no reason to doubt its legitimacy.
Fake Booking.com page
Guez says that the victim receives a link for the alleged card verification to keep the reservation. The link triggers on the victim machine an executable that is encoded in a complex JavaScript base64 script.
The researcher stresses that the script’s purpose is to detect information about the browsing environment and it is designed to make analysis significantly more difficult.
The attacker also included multiple security validation and anti-analysis techniques to make sure that only potential victims reach the next stage of the scam, which shows a fake Booking.com payment page.
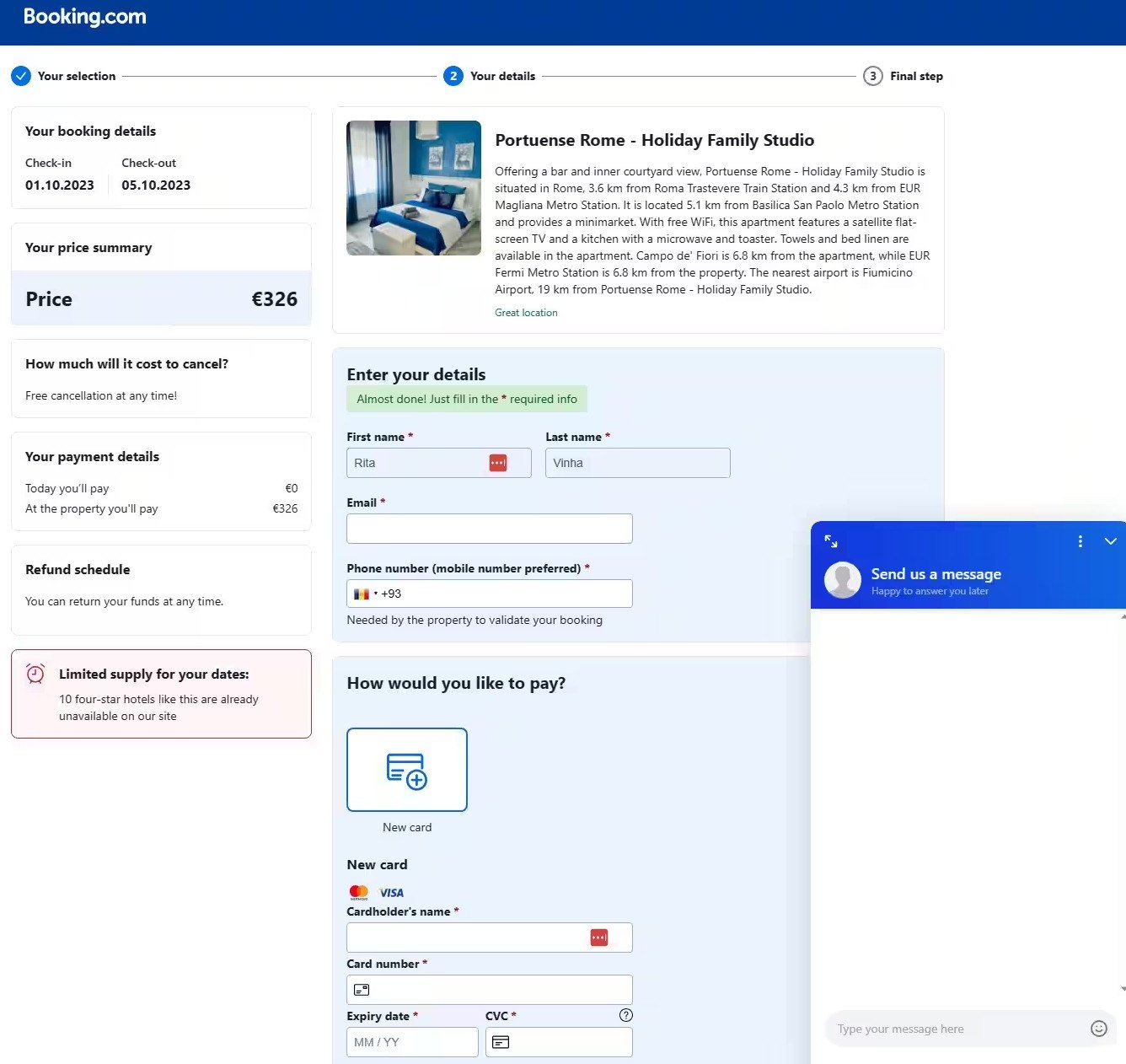
source: Akamai
Despite the more sophisticated approach that makes the trick very difficult to spot, Guez says that the regular signs indicating a potential scam could still reveal the fraud.
Users should avoid clicking on unsolicited links, even if they look legitimate, be suspicious of urgent or threatening messages asking for immediate action, and check URLs for indicators of deception.
However, to ensure you don’t fall victim to more complex phishing campaigns, the recommended action is to contact the company directly at an official email address or phone number and ask for clarifications about the message.


Comments
ukcobra - 7 months ago
This is still happening, I know it has been reported to Booking.com. They do not appear to be doing anything about it. Compromised links to the hackers payment portals are still on their messaging system.
The Booking.com agents have no idea of the timescales and no ability to help impacted customers. Personal data has been accessed and they appear to be slow to contain and eradicate this threat.
boozy1 - 7 months ago
The issue is still going on. Important detail: the scam mails are sent through booking.com's own mailservers!
Sedrick - 6 months ago
Hello, I am having the same issue : I received a weird mail FROM booking.com site (from the hotel) asking me this and I clicked on the link but did not fill any personal information. Should I check for something being installed/hacked/infostealer on my computer ?
"Dear Guest, we regret to inform you that your booking may be canceled as your card has not been automatically verified.
You will need to re-verify your card and confirm your identity.
Attention: To verify, the card must have an amount equal to your reservation, make sure there are no restrictions on online transactions on the card.
"This is not a deposit or payment, you pay upon arrival at the hotel".
This must be done within 6 hours or your reservation will be automatically canceled.
We recommend that you use a Mastercard.
Please follow the link below to confirm your reservation [Copy Link]:
LINK
Regards © Booking 2023 Team"
boozy1 - 6 months ago
Don't do anything that email is trying to get you to do, instead call the hotel and tell them that their booking.com account has been hacked.
As long as you don't follow any links you're safe. The hotel on the other hand... they have a few things hey need to fix.
Sedrick - 6 months ago
Thank you boozy for your reply,
I will not fill any information.
However, I clicked on the URL they provided asking me to fill information. Do you know if that solely could have compromised my computer?
boozy1 - 6 months ago
Nah, the fake site itself doesn't push any malware they just want to steal credit card information. You're safe.
ilaion - 6 months ago
Yeah, it looks like a scam. Card verification doesn't require you to have the full amount because they just want to check that you're using a valid card. Typically, they'll charge a small amount for this and return it after a short time.
techgenie - 6 months ago
Amazingly, this just happened and booking.com is blaming the hotel. The mail looked so legit I almost fell for it. It had my correct itinery down to my reservation number. I only stopped right before clicking submit because I noticed URL of the form is highly irregular.
Mail was routed through booking.com domain server. They haven't gotten it right yet, after more than six weeks!
techgenie - 6 months ago
Man this is of course happening till now!
I reported to both booking.com and the hotel (Shangri-La) and they are blaming each other!
I am sick of this ping-pong'ing. I am done with booking.com and any affiliate and going back to old phone and desk travel agent!
Booking.com app even relayed the said scam message!
edruiop - 6 months ago
It is Still hapening
Message is From Booking messages tools and from the hotel account, most people trust them...
And Booking Still dont care, and their stock options are flying...
"Our messages tools can contains phishing link but we f... dont care what will you do just pay and shut up..". Thats Killing me... Never again Booking
techgenie - 6 months ago
I say they have enormous class action lawsuit heading their way. Amazing thing is that I checked their app after I filed complaint and their messaging app showed exact scam message prominently showing that scam link with unverified domain.
They cannot blame this blatant disregard to their system design and dump blame it on "properties." If I saw that in-app message before I looked at their e-mail, I would have just fell for it!
Who is in charge of their system security?