
A thirty-month international law enforcement operation codenamed 'Operation Cyclone' targeted the Clop ransomware gang, leading to the previously reported arrests of six members in Ukraine.
In June, BleepingComputer reported that Ukrainian law enforcement arrested members of the Clop ransomware gang involved in laundering ransom payments.
This Friday, new information came to light regarding how the operation was conducted and the law enforcement agencies involved.
Interpol's Operation Cyclone
The transcontinental operation named 'Operation Cyclone' was coordinated from INTERPOL's Cyber Fusion Centre in Singapore, with assistance from Ukrainian and US law enforcement authorities.
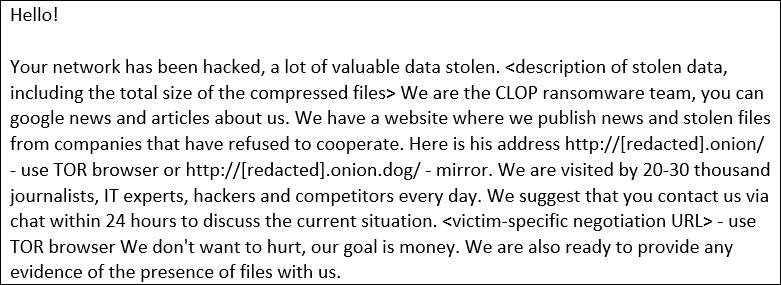
This operation targeted Clop for its numerous attacks against Korean companies and US academic institutions, where the threat actors encrypted devices and extorted organizations to pay a ransom or have their stolen data leaked.
In December 2020, Clop conducted a massive ransomware attack against E-Land Retail, a South Korean conglomerate, and retail giant, causing 23 out of 50 NC Department Store and NewCore Outlet retail stores to temporarily close. They later claimed to have stolen 2,000,000 credit cards from the company using point-of-sale malware.
More recently, Clop used a vulnerability in the Accellion secure file transfer gateway to steal confidential and private files of corporations and universities. When $10 million+ ransom demands were not paid, the threat actors publicly released students' personal information from numerous universities and colleges.
The US education institutions targeted in the Accellion attacks included the University of Colorado, University of Miami, Stanford Medicine, University of Maryland Baltimore (UMB), and the University of California.
Through intelligence sharing between law enforcement agencies and private partners, Operation Cyclone led to the arrest of six suspects in Ukraine, the search of more than 20 houses, businesses, and vehicles, and the seizure of computers and $185,000 in cash assets.
The operation was also assisted by private partners, including Trend Micro, CDI, Kaspersky Lab, Palo Alto Networks, Fortinet, and Group-IB.
“Despite spiralling global ransomware attacks, this police-private sector coalition saw one of global law enforcement’s first online criminal gang arrests, which sends a powerful message to ransomware criminals, that no matter where they hide in cyberspace, we will pursue them relentlessly,” said INTERPOL’s Director of Cybercrime Craig Jones in an announcement.
US cybersecurity firm Intel 471 previously told BleepingComputer that while the arrested members are linked to the Clop ransomware gang, they were primarily involved in the money laundering for the criminal organization. The intelligence firm further said that core members of the Clop operation are likely out of harm's way in Russia.
If convicted, the six suspected Clop members face up to eight years in prison.
A video released by Ukraine's SSU shows investigators conducting raids on the suspect's property and the seizure of evidence.
Targeting ransomware operations
With ransomware attacks escalating against critical infrastructure, healthcare, businesses, and educational institutions, law enforcement has been applying significant pressure on criminal operations this year.
This law enforcement activity has led to numerous arrests and infrastructure takedowns, including:
- The disruption of the Netwalker ransomware operation and the arrest of an affiliate in Canada.
- The arrest of the two Egregor operation members led to the shutting down of the organization.
- The arrest of 12 individuals believed to be linked to ransomware attacks against 1,800 victims in 71 countries.
Law enforcement operations have also led to ransomware gang's shutting down their operations as they feel law enforcement tightening on their activities.
This includes the recent shutdown of the REvil and BlackMatter operations, as well as Avaddon ransomware's shutdown in June.
While ransomware gangs may shut down their operations, it does not mean that law enforcement has given up on bringing them to justice.
This week, the US Department of State announced a $10 million reward for identifying or locating key leaders in the DarkSide/BlackMatter ransomware operation.
Thanks to Douglas Mun for the tip!


Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now