
The Ziggy ransomware operation has shut down and released the victims' decryption keys after concerns about recent law enforcement activity and guilt for encrypting victims.
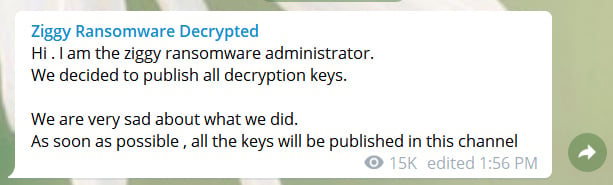
Over the weekend, security researcher M. Shahpasandi told BleepingComputer that the Ziggy Ransomware admin announced on Telegram that they were shutting down their operation and would be releasing all of the decryption keys.
In an interview with BleepingComputer, the ransomware admin said they created the ransomware to generate money as they live in a "third-world country."
After feeling guilty about their actions and concerns over recent law enforcement operations against Emotet and Netwalker ransomware, the admin decided to shut down and release all of the keys.
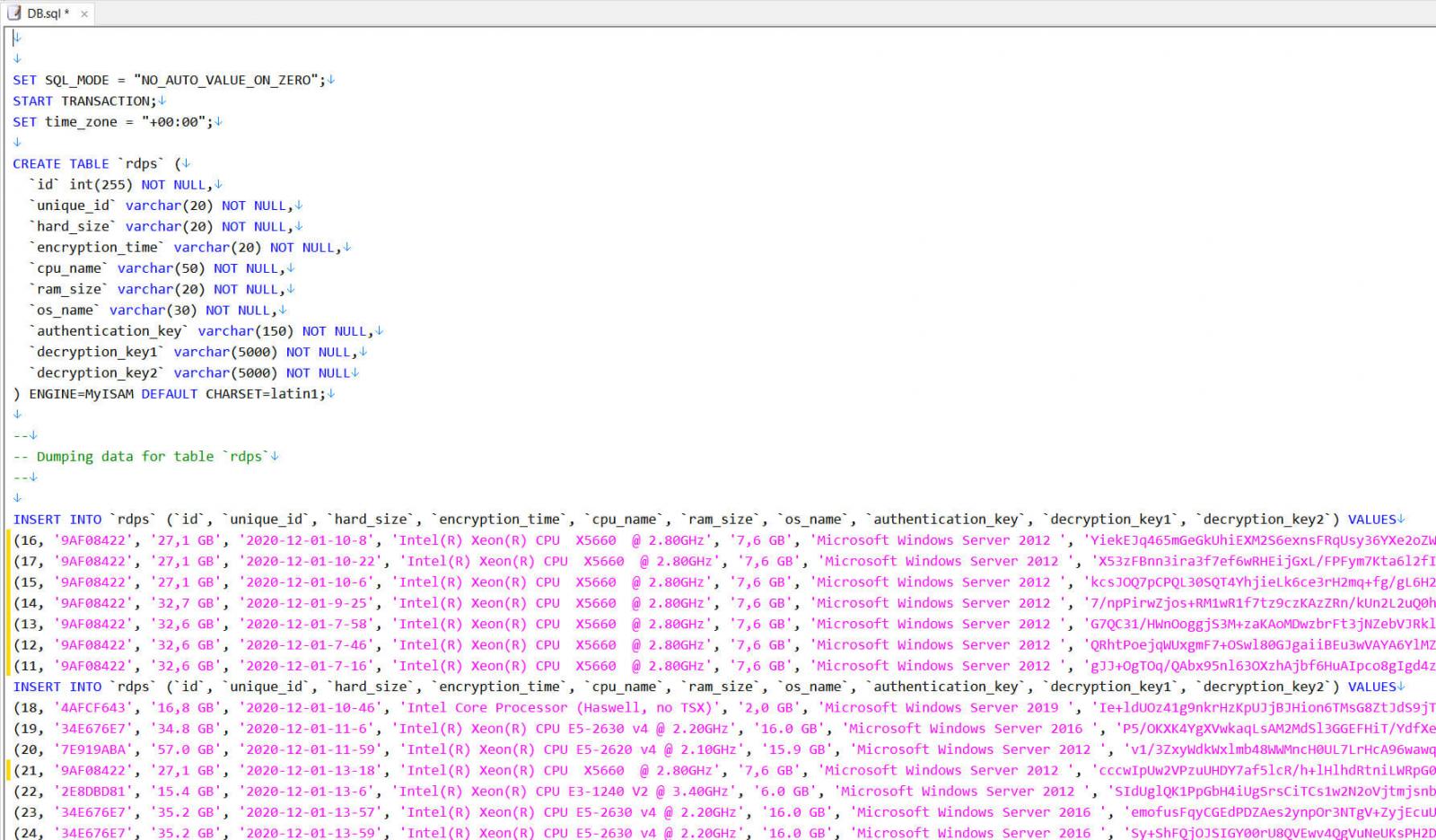
Today, the Ziggy ransomware admin posted a SQL file containing 922 decryption keys for encrypted victims. For each victim, the SQL file lists three keys needed to decrypt their encrypted files.
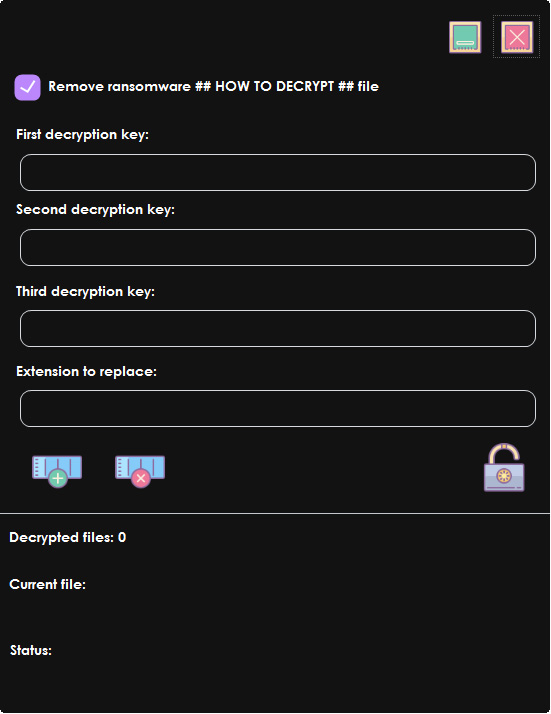
The ransomware admin also posted a decryptor [VirusTotal] that victims can use with the keys listed in the SQL file.
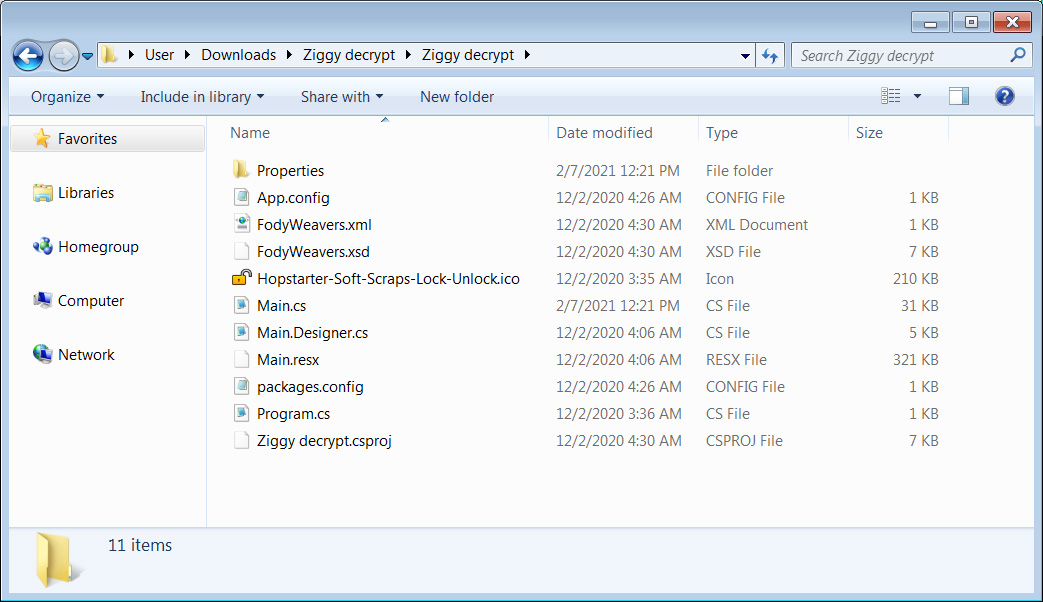
In addition to the decryptor and the SQL file, the ransomware admin shared the source code for a different decryptor with BleepingComputer that contains offline decryption keys.
Ransomware infections use offline decryption keys to decrypt victims infected while not being connected to the Internet or the command and control server was unreachable.
The ransomware admin also shared these files with ransomware expert Michael Gillespie who created a decryptor for the Ziggy Ransomware using the released keys.
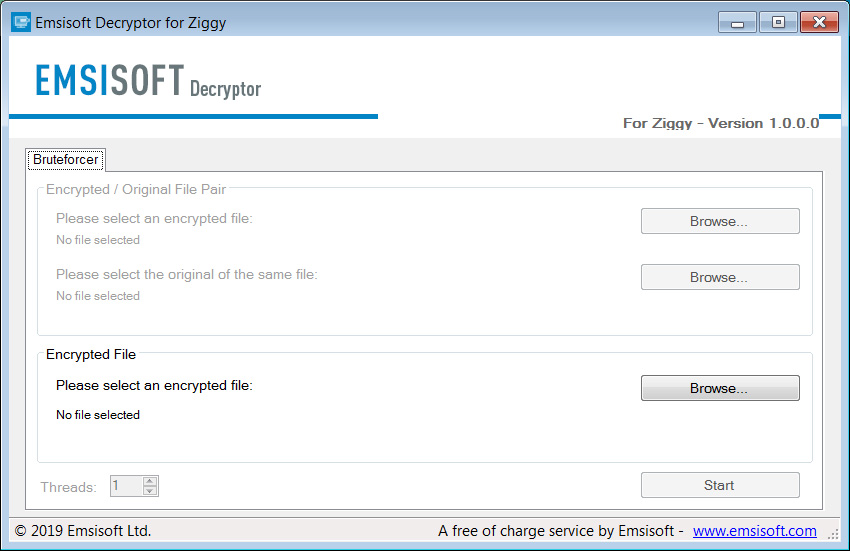
While the ransomware admin appears to be honest in their intent to shut down and release the keys, BleepingComputer always suggests using a security company's decryptor rather than one supplied by a threat actor.
"The release of the keys, whether voluntarily or involuntarily, is the best possible outcome. It means past victims can recover their data without needing to pay the ransom or use the dev’s decryptor, which could contain a backdoor and/or bugs. And, of course, it also means there’s one less ransomware group to worry about."
"The recent arrest of individuals associated with the Emotet and Netwalker operation could be causing some actors to get cold feet. If so, we could well see more groups ceasing operations and handing over the their keys. Fingers crossed," Emsisoft's Brett Callow told BleepingComputer.
Last week, the Fonix ransomware operation also shut down and released keys and decryptor. The Ziggy admin told BleepingComputer that they are friends with the Fonix ransomware group and are from the same country.
Update /2/8/21: Added information about released Ziggy decryptor.


Comments
Word-Warrior - 3 years ago
Taking away all of the embellished reportage fill out we would be left with...
The Numb-Nut thieving scumbags known as 'Ziggy Ransomware' have jumped on the bandwagon of those other Ransomware scum groups who have announced they are closing their illegal theft operations! They and all the groups closing shop are NOT sorry one little bit for what they have done, stolen; or for the sheer misery and pain that they have reaped upon certain individuals. They are running scared and are currently in a scared stiff state of panic that they are close to being the next group arrested.
That's the report in the short and sweet way that people want to really see/know! :)
The Ziggy group ransomware admin said they were sad and felt guilty for what they had done and, that they created the ransomware to generate money as they live in a "third-world country. " Liar, liar, lying toad! You live in a third world country...SO THE FRAK WHAT!? There are plenty of wealthy and well off people in your country that you could have stolen from! I am a hard up disabled person and live from day to day in a country supposedly affluent an full of prosperous people. You B******S think everyone in the West is rich...we are not! Only 1% of a country population is mega wealthy (except where you are from...your country has more per its population than any country in the world!) You did not have to make a member of my family, and other peoples families lives miserable. You probably took peoples money, decrypted them and then immediately passed on their details to your friends, Fonix ransomware group and the likes etc, for them to heap more misery on defenseless individuals.
Well my friends and I (we know a few things about computers...which is bad luck for you lowlifes) will not shut down our operations of looking for you...or your friends! I'm pretty certain that those people arresting other scum groups will carry on looking for you also! You see, now that the good guys have a few of YOU in their possession...shall we say...they'll be squealing and pleading to give information on as many of you as they know of to avoid huge jail sentences etc!
Its good to know that you are having a bunch of NOT NICE days. Buy yourself a good brush as you are going to need it to give your prison cell a good clean out.
Thanks for the report Mr Abrams and stay safe (put a mask on your photo avatar and help promote virus awareness).
Maybe you should write a book for Ransomware groups to read whilst they are in prison. Call it, 'No(soft)ware 2 Run: The Story of Ransomware Dummies'. Volumes 1 - Volume 10 would be a good start! :)